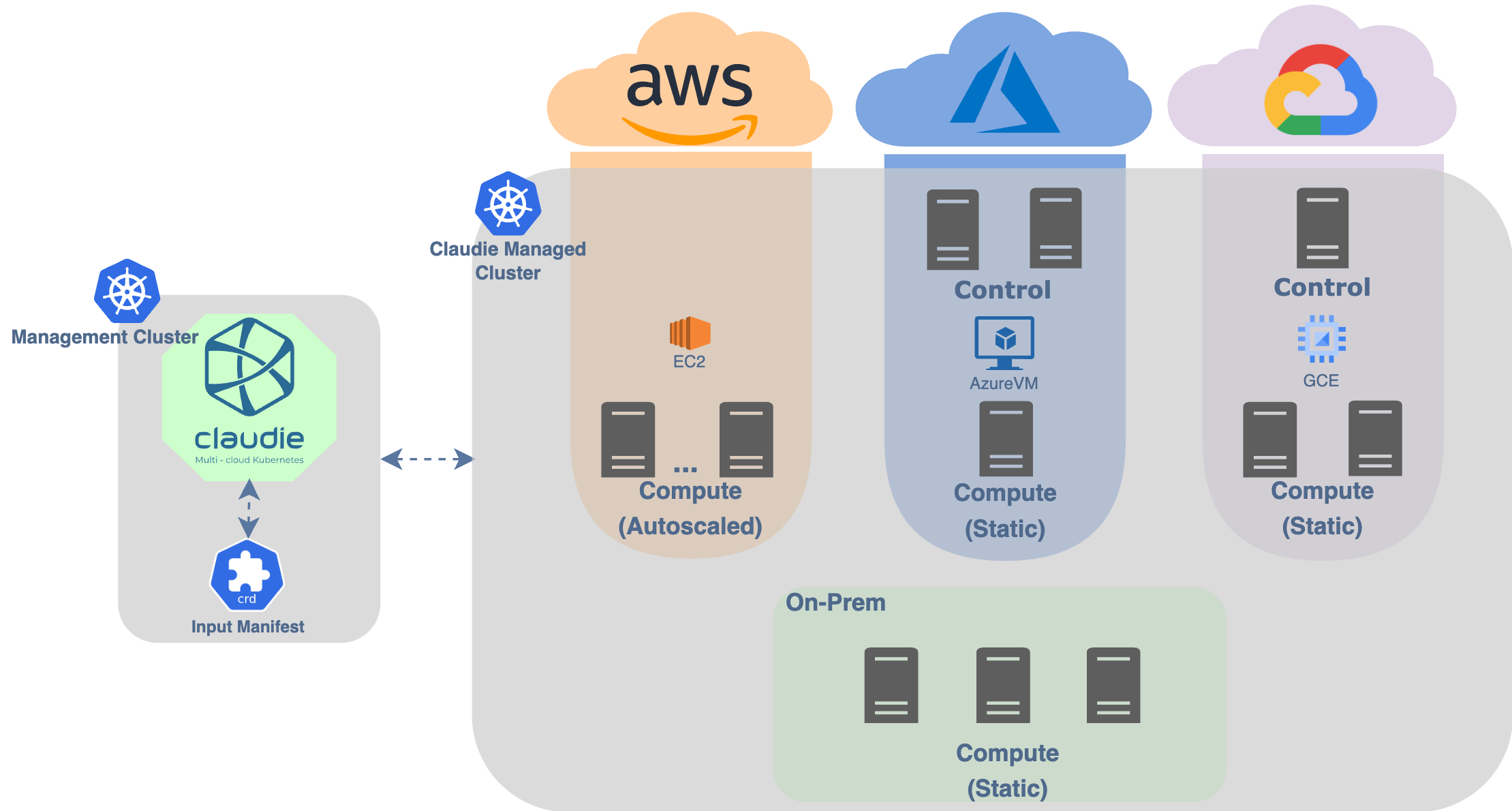
Platform for managing multi-cloud and hybrid-cloud Kubernetes clusters with support for nodepools across different cloud-providers and on-premise data centers
The purpose of Claudie is to become the final Kubernetes engine you'll ever need. It aims to build clusters that leverage features and costs across multiple cloud vendors and on-prem datacenters. A Kubernetes that you won't ever need to migrate away from.
Claudie has been built as an answer to the following Kubernetes challenges.
- Cost savings
- Data locality & compliance (e.g. GDPR)
- Managed Kubernetes for providers that do not offer it
- Cloud bursting
- Service interconnect
Read in more details here.
Create fully-featured Kubernetes clusters composed of multiple different public Cloud providers and on-premise data center in an easy and secure manner. Simply insert credentials to your cloud projects, define your cluster, and watch how the infra spawns right in front of you.
Declaratively define your infrastructure with a simple, easy to understand YAML syntax. See example manifest.
To scale-up or scale-down, simply change a few lines in the input manifest and Claudie will take care of the rest in the matter of minutes.
Claudie has its own managed load-balancing solution, which you can use for Ingresses, the Kubernetes API server, or generally anything. Check out our LB docs.
Claudie comes pre-configured with a storage solution, with ready-to-use Storage Classes. See Storage docs to learn more.
Before you begin, please make sure you have the following prerequisites installed and set up:
-
Claudie needs to be installed on an existing Kubernetes cluster, referred to as the Management Cluster, which it uses to manage the clusters it provisions. For testing, you can use ephemeral clusters like Minikube or Kind. However, for production environments, we recommend using a more resilient solution since Claudie maintains the state of the infrastructure it creates.
-
Claudie requires the installation of cert-manager in your Management Cluster. To install cert-manager, use the following command:
kubectl apply -f https://github.com/cert-manager/cert-manager/releases/download/v1.12.0/cert-manager.yaml
| Supported Provider | Node Pools | DNS |
|---|---|---|
| AWS | ✔️ | ✔️ |
| Azure | ✔️ | ✔️ |
| GCP | ✔️ | ✔️ |
| OCI | ✔️ | ✔️ |
| Hetzner | ✔️ | ✔️ |
| Cloudflare | N/A | ✔️ |
| GenesisCloud | ✔️ | N/A |
For adding support for other cloud providers, open an issue or propose a PR.
-
Deploy Claudie to the Management Cluster:
kubectl apply -f https://github.com/berops/claudie/releases/latest/download/claudie.yaml
To further harden claudie, you may want to deploy our pre-defined network policies:
# for clusters using cilium as their CNI kubectl apply -f https://github.com/berops/claudie/releases/latest/download/network-policy-cilium.yaml# other kubectl apply -f https://github.com/berops/claudie/releases/latest/download/network-policy.yaml
-
Create Kubernetes Secret resource for your provider configuration.
kubectl create secret generic example-aws-secret-1 \ --namespace=mynamespace \ --from-literal=accesskey='myAwsAccessKey' \ --from-literal=secretkey='myAwsSecretKey'
Check the supported providers for input manifest examples. For an input manifest spanning all supported hyperscalers checkout out this example.
-
Deploy InputManifest resource which Claudie uses to create infrastructure, include the created secret in
.spec.providersas follows:kubectl apply -f - <<EOF apiVersion: claudie.io/v1beta1 kind: InputManifest metadata: name: examplemanifest labels: app.kubernetes.io/part-of: claudie spec: providers: - name: aws-1 providerType: aws secretRef: name: example-aws-secret-1 # reference the secret name namespace: mynamespace # reference the secret namespace nodePools: dynamic: - name: control-aws providerSpec: name: aws-1 region: eu-central-1 zone: eu-central-1a count: 1 serverType: t3.medium image: ami-0965bd5ba4d59211c - name: compute-1-aws providerSpec: name: aws-1 region: eu-west-3 zone: eu-west-3a count: 2 serverType: t3.medium image: ami-029c608efaef0b395 storageDiskSize: 50 kubernetes: clusters: - name: aws-cluster version: 1.27.0 network: 192.168.2.0/24 pools: control: - control-aws compute: - compute-1-aws EOF
Deleting existing InputManifest resource deletes provisioned infrastructure!
Claudie outputs base64 encoded kubeconfig secret <cluster-name>-<cluster-hash>-kubeconfig in the namespace where it is deployed:
- Recover kubeconfig of your cluster by running:
kubectl get secrets -n claudie -l claudie.io/output=kubeconfig -o jsonpath='{.items[0].data.kubeconfig}' | base64 -d > your_kubeconfig.yaml
- Use your new kubeconfig:
kubectl get pods -A --kubeconfig=your_kubeconfig.yaml
-
To remove your cluster and its associated infrastructure, delete the cluster definition block from the InputManifest:
kubectl apply -f - <<EOF apiVersion: claudie.io/v1beta1 kind: InputManifest metadata: name: examplemanifest labels: app.kubernetes.io/part-of: claudie spec: providers: - name: aws-1 providerType: aws secretRef: name: example-aws-secret-1 # reference the secret name namespace: mynamespace # reference the secret namespace nodePools: dynamic: - name: control-aws providerSpec: name: aws-1 region: eu-central-1 zone: eu-central-1a count: 1 serverType: t3.medium image: ami-0965bd5ba4d59211c - name: compute-1-aws providerSpec: name: aws-1 region: eu-west-3 zone: eu-west-3a count: 2 serverType: t3.medium image: ami-029c608efaef0b395 storageDiskSize: 50 kubernetes: clusters: # - name: aws-cluster # version: 1.27.0 # network: 192.168.2.0/24 # pools: # control: # - control-aws # compute: # - compute-1-aws EOF
-
To delete all clusters defined in the input manifest, delete the InputManifest. This triggers the deletion process, removing the infrastructure and all data associated with the manifest.
kubectl delete inputmanifest examplemanifest
Everyone is more than welcome to open an issue, a PR or to start a discussion.
For more information about contributing please read the contribution guidelines.
If you want to have a chat with us, feel free to join our channel on kubernetes Slack workspace (get invite here).
While we strive to create secure software, there is always a chance that we miss something. If you've discovered something that requires our attention, see our security policy to learn how to proceed.
To see the vision behind Claudie, please refer to the roadmap document.
Claudie is proudly developed by Berops. Feel free to request a demo here. For information on enterprise support, contact us here.
Apache-2.0 (see LICENSE for details).