IMPORTANT:
Vaile Framework has been merged into the original TIDoS Framework. You can find the latest progress here: https://github.com/0xInfection/TIDoS-Framework. This repository is discontinued.


Pentest framework based on TIDoS.
IMPORTANT:
The new Qt5 interface is complete, but has additional dependencies. Take a look at the updated installation instructions.
Here is some light on what the framework is all about:
- A complete versatile framework to cover up everything from Reconnaissance to Vulnerability Analysis.
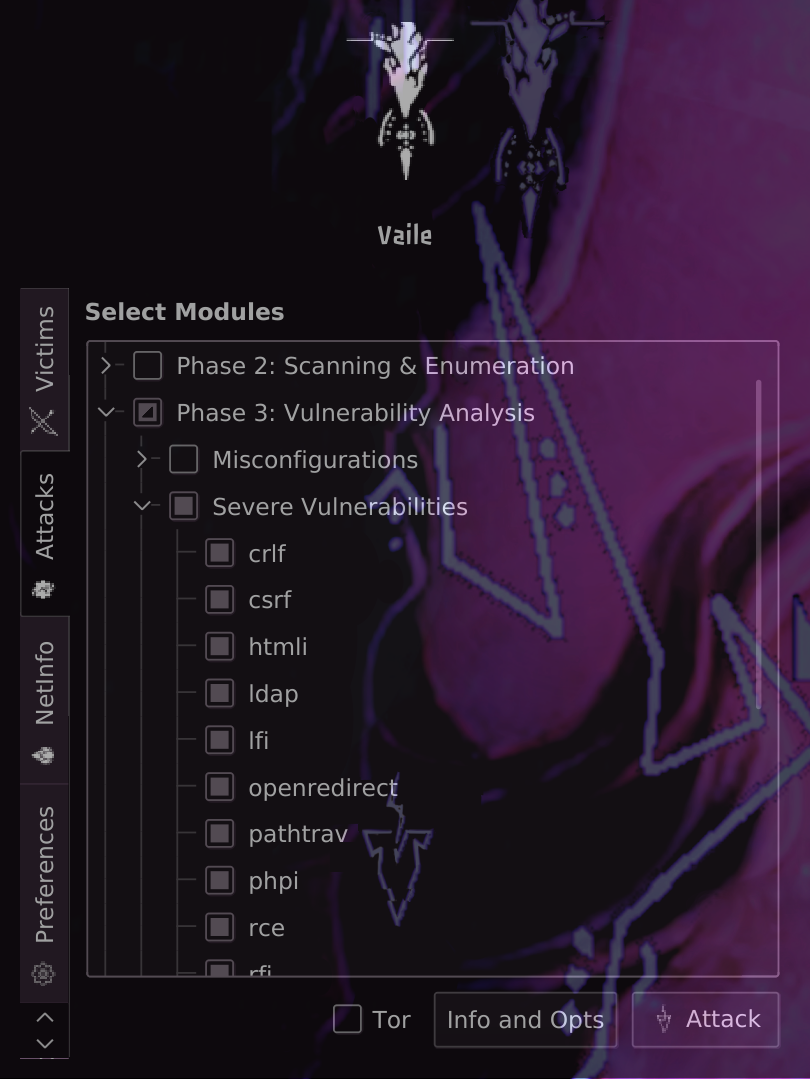
- Has 5 main phases, subdivided into 14 sub-phases consisting a total of 108 modules.
- Reconnaissance Phase has 50 modules of its own (including active and passive recon, information disclosure modules).
- Scanning & Enumeration Phase has got 16 modules (including port scans, WAF analysis, etc)
- Vulnerability Analysis Phase has 37 modules (including most common vulnerabilities in action).
- Exploits Castle has only 1 exploit.
(purely developmental) - And finally, Auxiliaries have got 4 modules.
more under development - All four phases each have an
Auto-Awesomemodule which automates every module for you. - Since 2.1: huge performance boost through parallelisation in various modules
- Piping Attacks through Tor (not implemented everywhere yet)
- You just need the domain, and leave everything is to this tool.
- Vaile has full verbose out support, so you'll know whats going on.
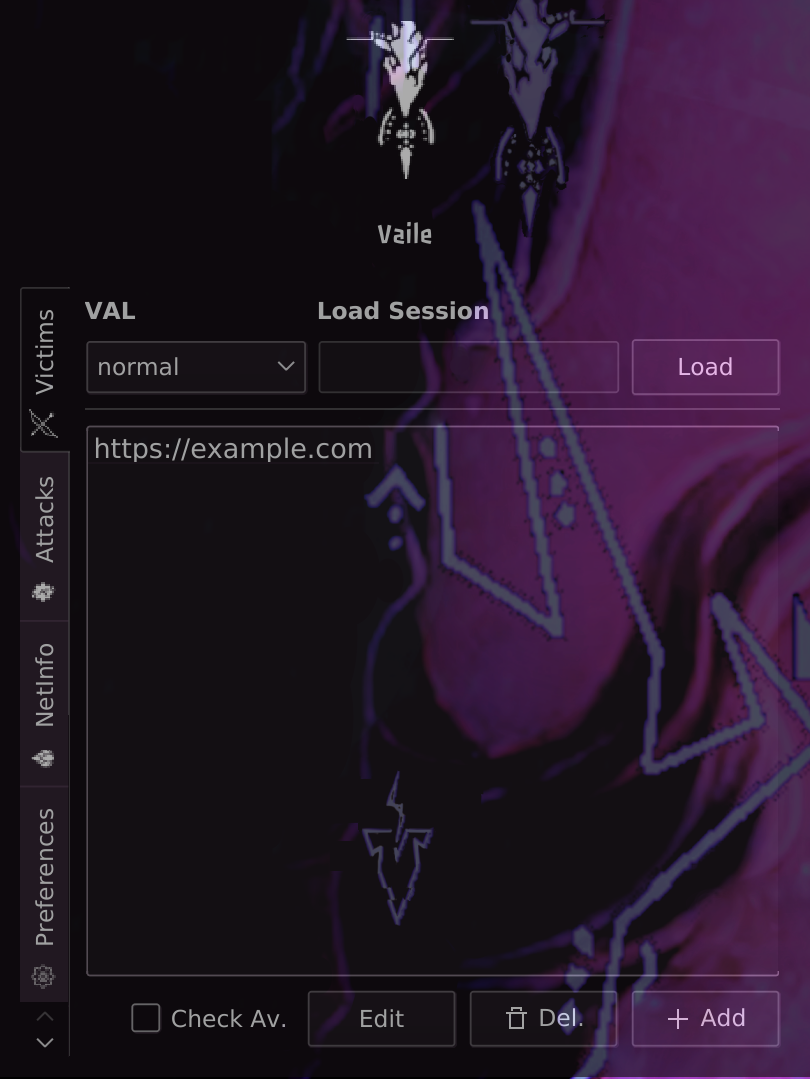
- Since 2.2: Attacking now even easier with a new GUI
The main differences between Vaile and TIDoS are:
- the programming language: Vaile is fully ported to Python3
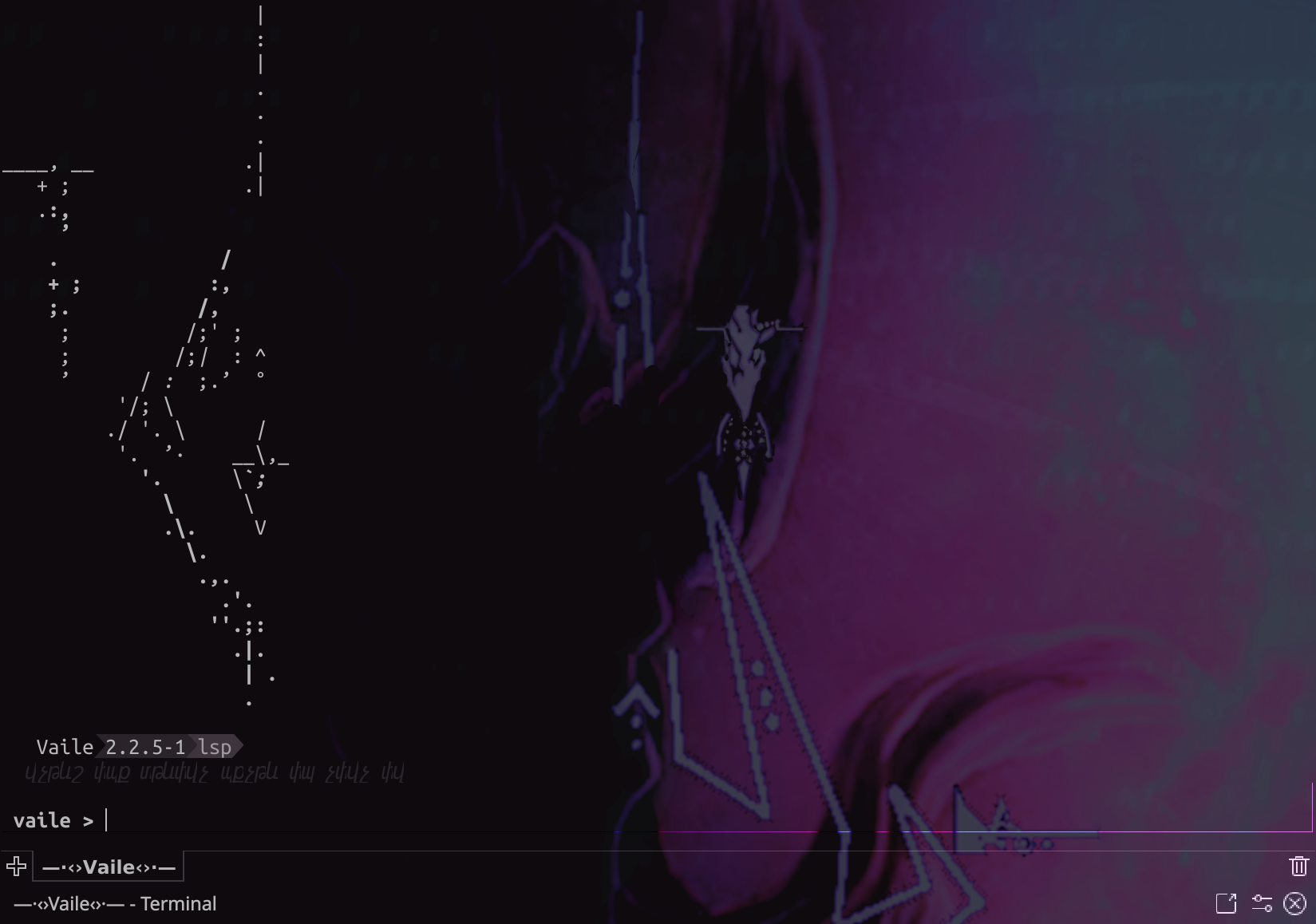
- the interface: Vaile presents a new, Metasploit-like console interface
- Parallelisation: Vaile uses multiprocessing to speed up attacks
- An alternative CLI interface for faster interaction with one specific module
- Anonymity: Attacking through Tor is possible (95% done)
- Module Completion: Some modules have been feature-extended (e.g. more evasion, supporting more than 1 query parameter)
- Some new modules: arpscan
- A Graphical User Interface for easier interaction with the toolkit
To install the framework globally in /opt, run the provided core/install.py script as root. After this, you can launch Vaile simply by typing Vaile on the command line.
- Clone the repository locally and navigate there:
git clone https://github.com/vainlystrain/vaile.git
cd Vaile
Vaile needs some libraries to run, which can be installed via aptitude or dnf Package Managers.
sudo apt-get install libncurses5 libxml2 nmap tcpdump libexiv2-dev build-essential python3-pip libmariadbclient18 libmysqlclient-dev tor konsole
Now after these dependencies are finished installing, we need to install the remaining Python Package dependencies, hence run:
pip3 install -r requirements.txt
Thats it. You now have Vaile at your service. Fire it up using:
python3 Vaile #Qt5 interface
sudo python3 vsconsole.py #console interface
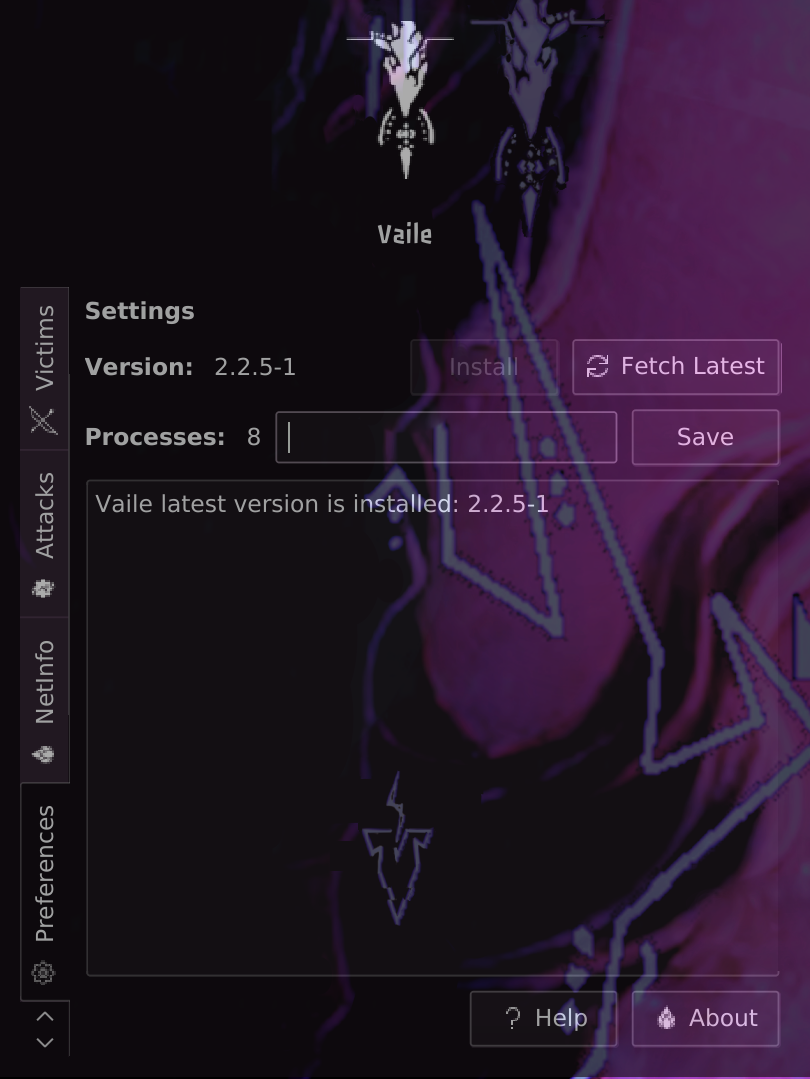
To get the current version of Vaile, move into the installation folder and perform (sudo) git pull #sudo if installed by install.py. Alternatively, you can run the fetch command in vsconsole.
To get started, you need to set your own API KEYS for various OSINT & Scanning and Enumeration purposes. To do so, open up API_KEYS.py under files/ directory and set your own keys and access tokens for SHODAN, CENSYS, FULL CONTACT, GOOGLE and WHATCMS.
GOOD NEWS:
The latest release of Vaile includes all API KEYS and ACCESS TOKENS for
SHODAN,CENSYS,FULL CONTACT,WHATCMSby default. I found these tokens on various repositories on GitHub itself. You can now use all the modules which use the API KEYS. :)
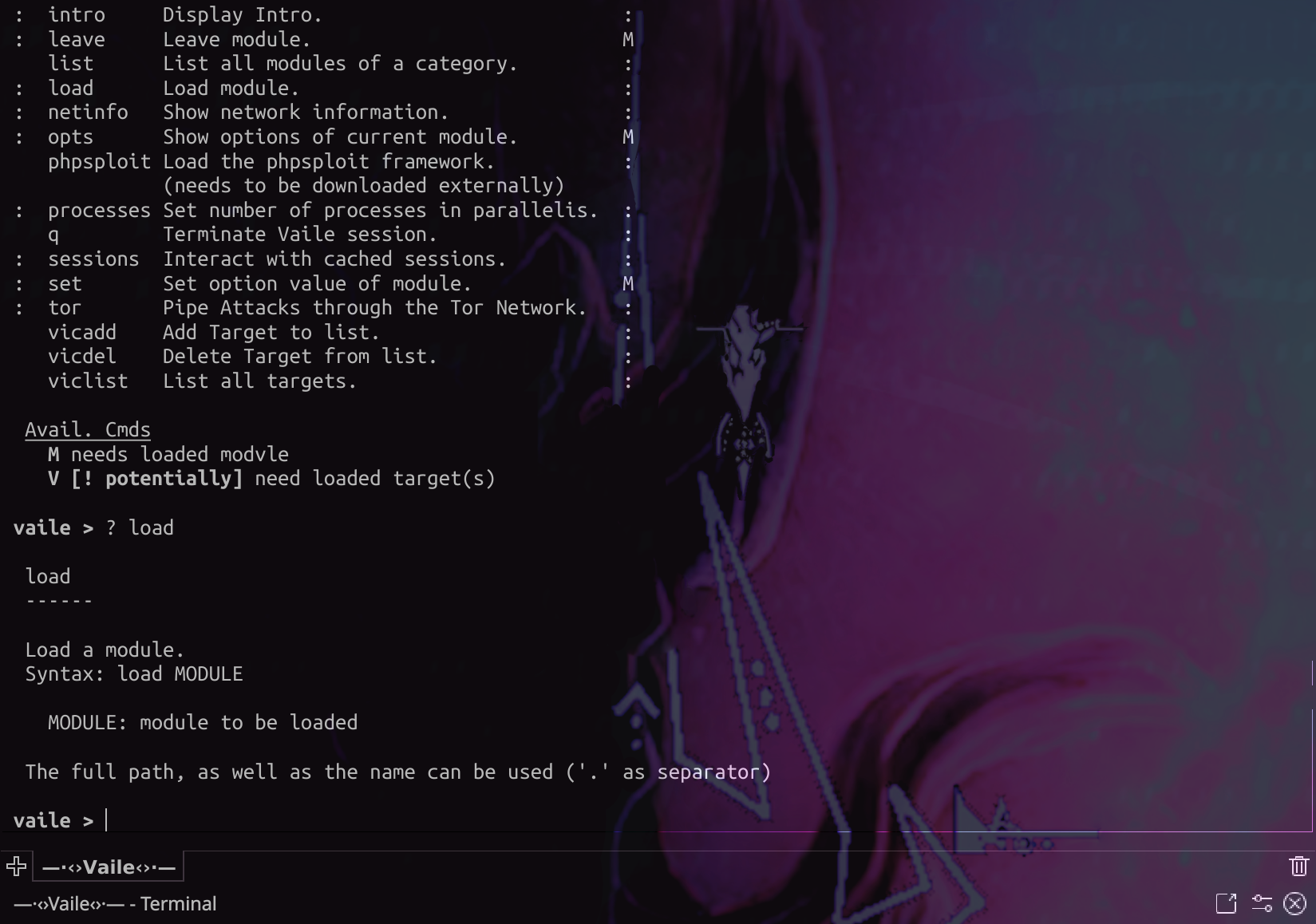
__ __
! attack Attack specified target(s) M
: clear Clear terminal. :
V creds Handle target credentials.
: fetch Check for and install updates. :
: find Search a module. :
help Show help message. :
info Show description of current module. M
: intro Display Intro. :
: leave Leave module. M
list List all modules of a category. :
: load Load module. :
: netinfo Show network information. :
: opts Show options of current module. M
phpsploit Load the phpsploit framework. :
(needs to be downloaded externally)
: processes Set number of processes in parallelis. :
q Terminate Vaile session. :
: sessions Interact with cached sessions. :
: set Set option value of module. M
: tor Pipe Attacks through the Tor Network. :
vicadd Add Target to list. :
vicdel Delete Target from list. :
viclist List all targets. :
Avail. Cmds
M needs loaded modvle
V [! potentially] need loaded target(s)
Vaile Attack presently supports the following: and more modules are under active development
-
Reconnaissance + OSINT
-
Passive Reconnaissance:
- Nping Enumeration
Via external APi - WhoIS Lookup
Domain info gathering - GeoIP Lookup
Pinpoint physical location - DNS Configuration Lookup
DNSDump - Subdomains Lookup
Indexed ones - Reverse DNS Lookup
Host Instances - Reverse IP Lookup
Hosts on same server - Subnets Enumeration
Class Based - Domain IP History
IP Instances - Web Links Gatherer
Indexed ones - Google Search
Manual search - Google Dorking (multiple modules)
Automated - Email to Domain Resolver
Email WhoIs - Wayback Machine Lookups
Find Backups - Breached Email Check
Pwned Email Accounts - Enumeration via Google Groups
Emails Only - Check Alias Availability
Social Networks - Find PasteBin Posts
Domain Based - LinkedIn Gathering
Employees & Company - Google Plus Gathering
Domain Profiles - Public Contact Info Scraping
FULL CONTACT - Censys Intel Gathering
Domain Based - Threat Intelligence Gathering
Bad IPs
- Nping Enumeration
-
Active Reconnaissance:
- Ping Enumeration
Advanced - CMS Detection
(185+ CMSs supported)IMPROVED - Advanced Traceroute
IMPROVED robots.txtandsitemap.xmlChecker- Grab HTTP Headers
Live Capture - Find HTTP Methods Allowed
via OPTIONS - Detect Server Type
IMPROVED - Examine SSL Certificate
Absolute - Apache Status Disclosure Checks
File Based - WebDAV HTTP Enumeration
PROFIND & SEARCH - PHPInfo File Enumeration
via Bruteforce - Comments Scraper
Regex Based - Find Shared DNS Hosts
Name Server Based - Alternate Sites Discovery
User-Agent Based - Discover Interesting Files
via Bruteforce- Common Backdoor Locations
shells, etc. - Common Backup Locations
.bak, .db, etc. - Common Password Locations
.pgp, .skr, etc. - Common Proxy Path Configs.
.pac, etc. - Multiple Index Paths
index, index1, etc. - Common Dot Files
.htaccess, .apache, etc - Common Logfile Locations
.log, .changelog, etc
- Common Backdoor Locations
- Ping Enumeration
-
Information Disclosure:
- Credit Cards Disclosure
If Plaintext - Email Harvester
IMPROVED - Fatal Errors Enumeration
Includes Full Path Disclosure - Internal IP Disclosure
Signature Based - Phone Number Havester
Signature Based - Social Security Number Harvester
US Ones
- Credit Cards Disclosure
-
-
Scanning & Enumeration
- Remote Server WAF Enumeration
Generic54 WAFs - Port Scanning
Ingenious Modules- Simple Port Scanner
via Socket Connections - TCP SYN Scan
Highly reliable - TCP Connect Scan
Highly Reliable - XMAS Flag Scan
Reliable Only in LANs - FIN Flag Scan
Reliable Only in LANs - Port Service Detector
- Simple Port Scanner
- Web Technology Enumeration
Absolute - Complete SSL Enumeration
Absolute - Operating System Fingerprinting
IMPROVED - Banner Grabbing of Services
via Open Ports - Interactive Scanning with NMap
16 preloaded modules - Internet Wide Servers Scan
Using CENSYS Database - Web and Links Crawlers
- Depth 1
Indexed Uri Crawler - Depth 2
Single Page Crawler - Depth 3
Web Link Crawler
- Depth 1
- ARP Scanner
NEW
- Remote Server WAF Enumeration
-
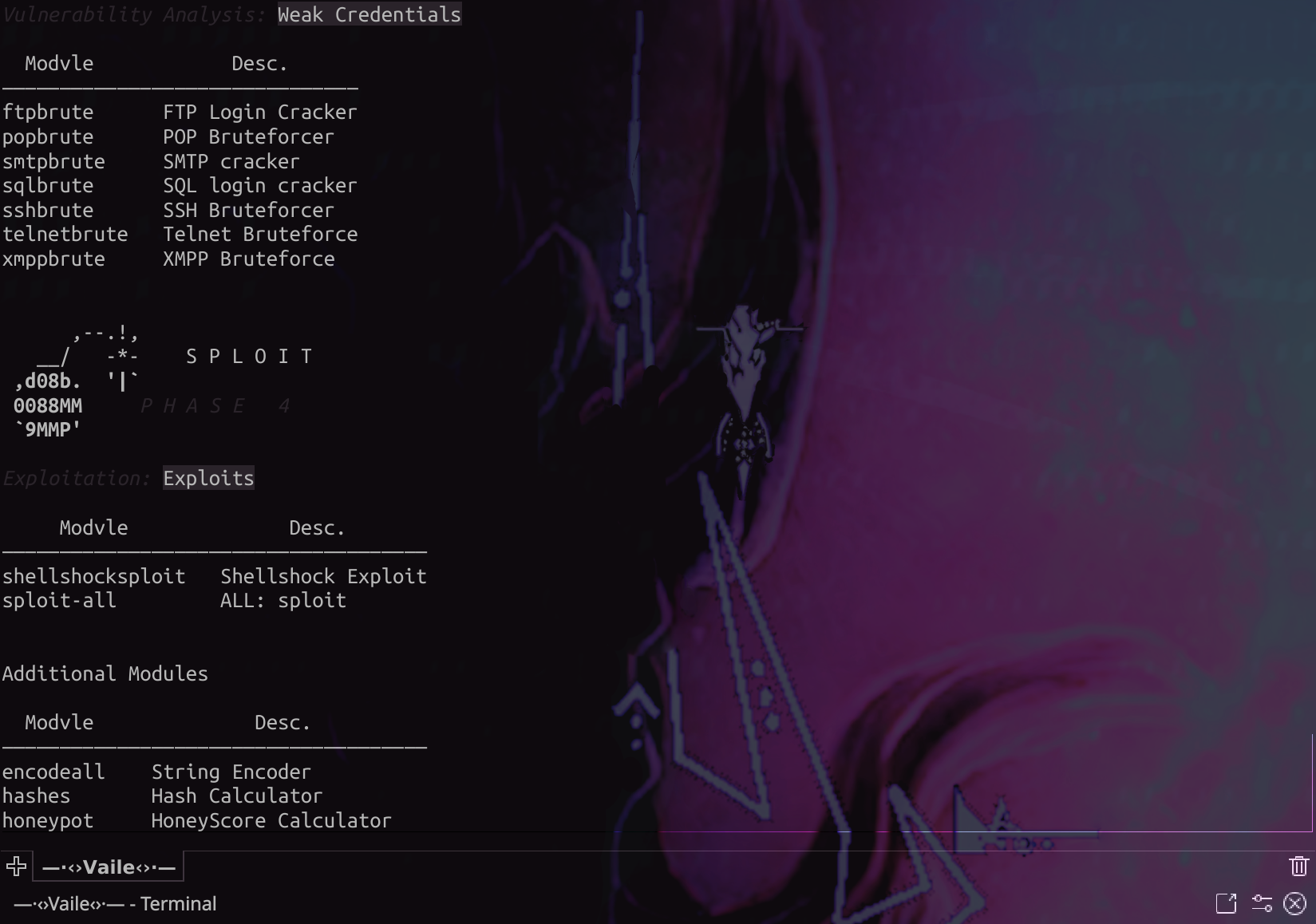
Vulnerability Analysis
Web-Bugs & Server Misconfigurations
- Insecure CORS
Absolute - Same-Site Scripting
Sub-domain based - Zone Transfer
DNS Server based - Clickjacking
- Frame-Busting Checks
X-FRAME-OPTIONSHeader Checks
- Security on Cookies
HTTPOnlyFlagSecureFlag on Cookies
- Cloudflare Misconfiguration Check
- DNS Misconfiguration Checks
- Online Database Lookup
For Breaches
- HTTP Strict Transport Security Usage
- HTTPS Enabled but no HSTS
- Domain Based Email Spoofing
- Missing
SPFRecords - Missing
DMARCRecords
- Missing
- Host Header Injection
- Port Based
Web Socket Based X-Forwarded-ForHeader Injection
- Port Based
- Security Headers Analysis
Live Capture - Cross-Site Tracing
HTTP TRACE Method - Session Fixation
via Cookie Injection - Network Security Misconfig.
- Checks for
TELNETEnabledvia Port 23
- Checks for
Serious Web Vulnerabilities
- File Inclusions
- Local File Inclusion (LFI)
Param based - Remote File Inclusion (RFI)
IMPROVED- Parameter Based
- Pre-loaded Path Based
- Local File Inclusion (LFI)
- OS Command Injection
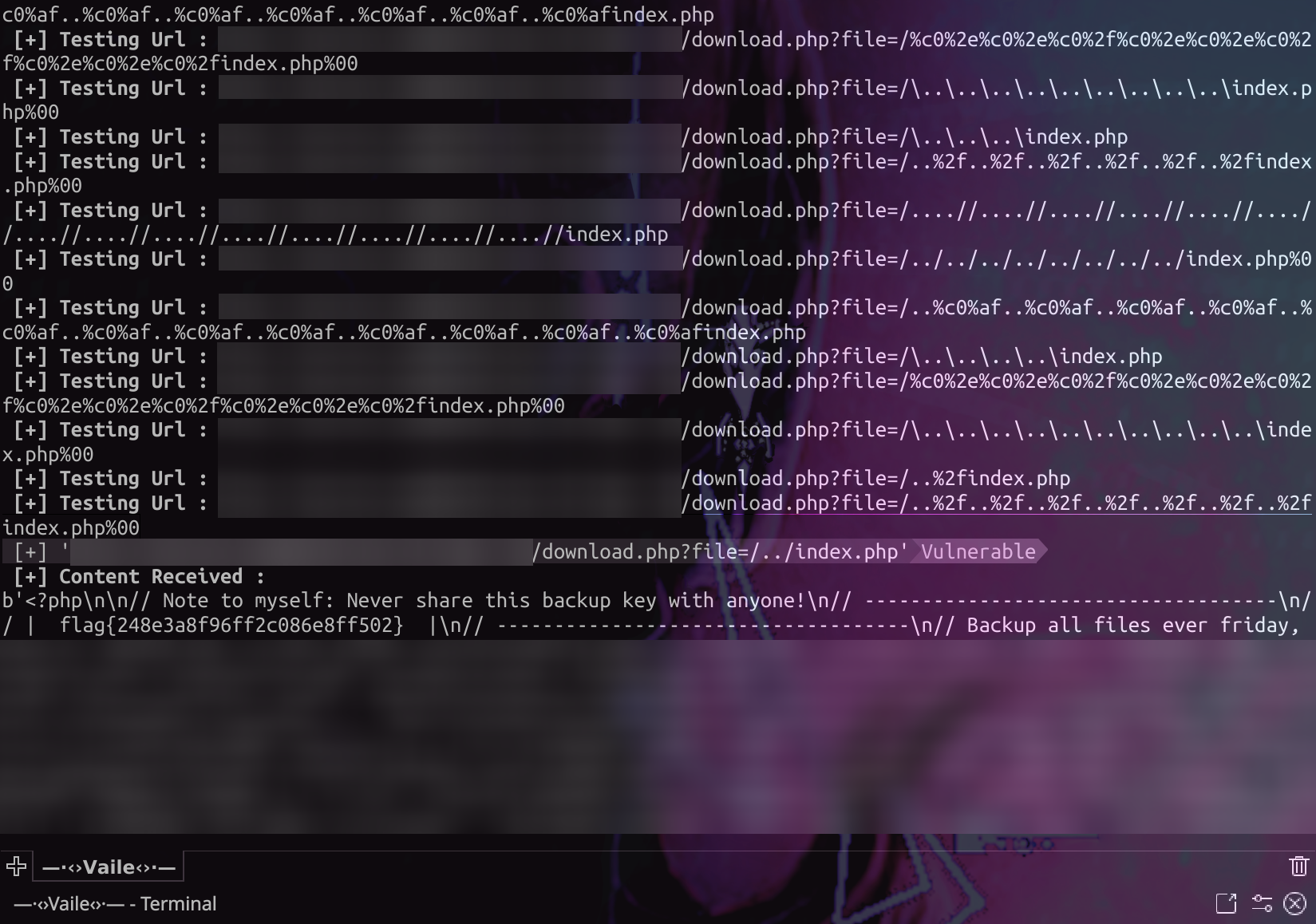
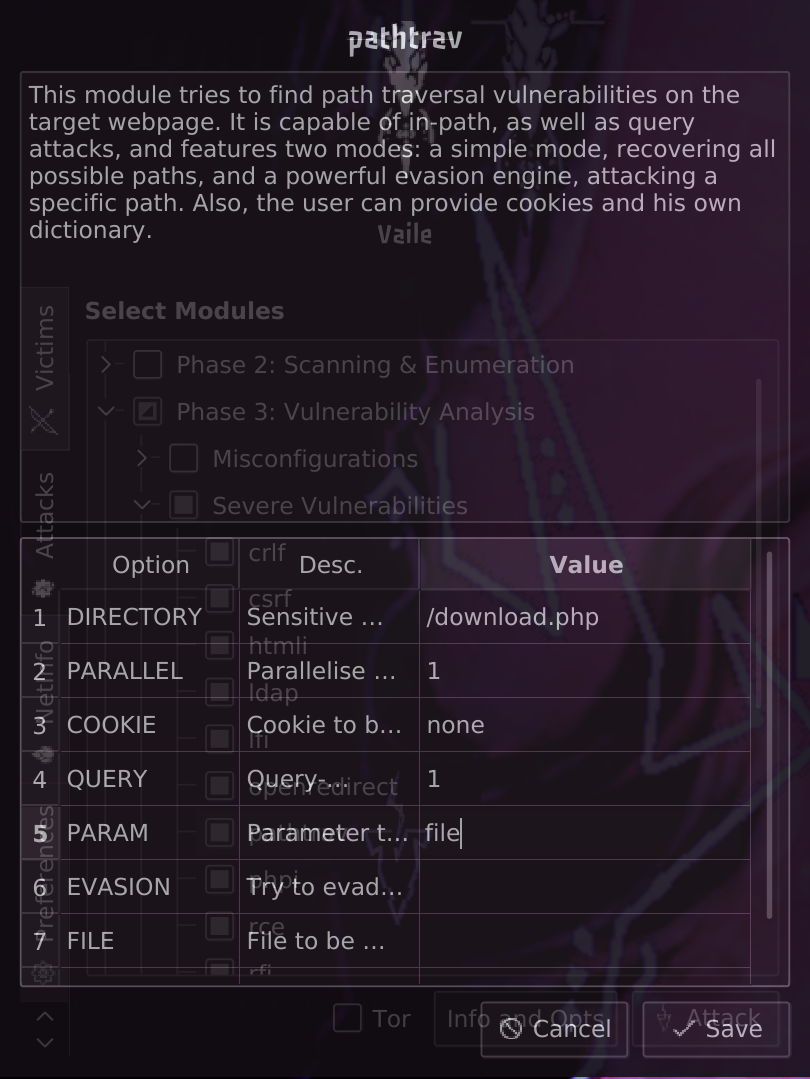
Linux & Windows (RCE) - Path Traversal
ENHANCED - Cross-Site Request Forgery
Absolute - SQL Injection
- Error Based Injection
- Cookie Value Based
- Referer Value Based
- User-Agent Value Based
- Auto-gathering
IMPROVED
- Blind Based Injection
Crafted Payloads- Cookie Value Based
- Referer Value Based
- User-Agent Value Based
- Auto-gathering
IMPROVED
- Error Based Injection
- LDAP Injection
Parameter Based - HTML Injection
Parameter Based - Bash Command Injection
ShellShock - Apache Struts Shock
Apache RCE - XPATH Injection
Parameter Based - Cross-Site Scripting
IMPROVED- Cookie Value Based
- Referer Value Based
- User-Agent Value Based
- Parameter Value Based
Manual
- Unvalidated URL Forwards
Open Redirect - PHP Code Injection
Windows + Linux RCE - CRLF Injection
HTTP Response Splitting- User-Agent Value Based
- Parameter value Based
Manual
- Sub-domain Takeover
50+ Services- Single Sub-domain
Manual - All Subdomains
Automated
- Single Sub-domain
Other
-
PlainText Protocol Default Credential Bruteforce
- FTP Protocol Bruteforce
- SSH Protocol Bruteforce
- POP 2/3 Protocol Bruteforce
- SQL Protocol Bruteforce
- (XMPP Protocol Bruteforce)
BROKEN:DEP - SMTP Protocol Bruteforce
- TELNET Protocol Bruteforce
- Insecure CORS
-
Auxillary Modules
- Hash Generator
MD5, SHA1, SHA256, SHA512 - String & Payload Encoder
7 Categories - Forensic Image Analysis
Metadata Extraction - Web HoneyPot Probability
ShodanLabs HoneyScore
- Hash Generator
-
Exploitation
purely developmental- ShellShock
net_info.py- Displays information about your network. Accessible from 'netinfo' command.
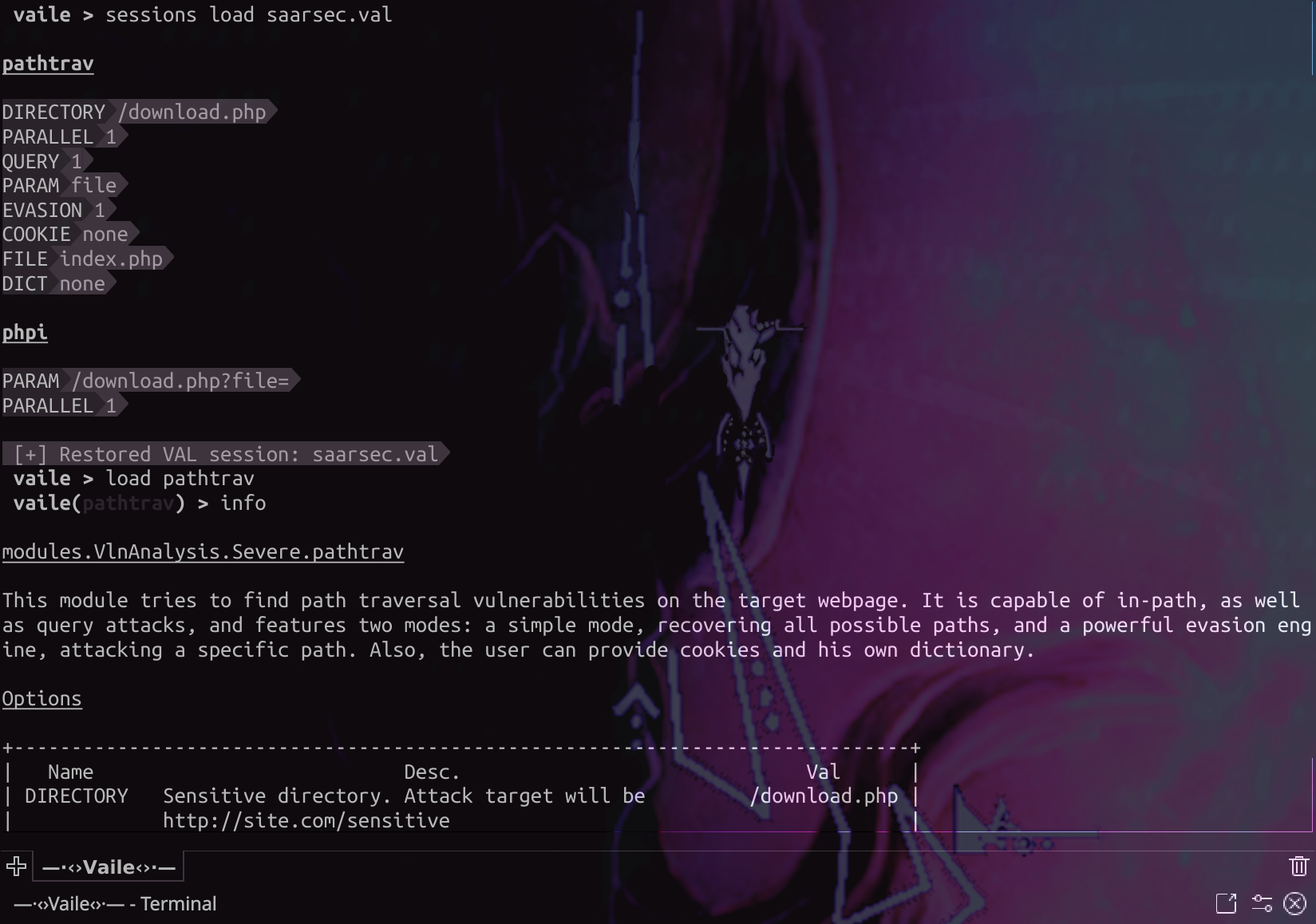
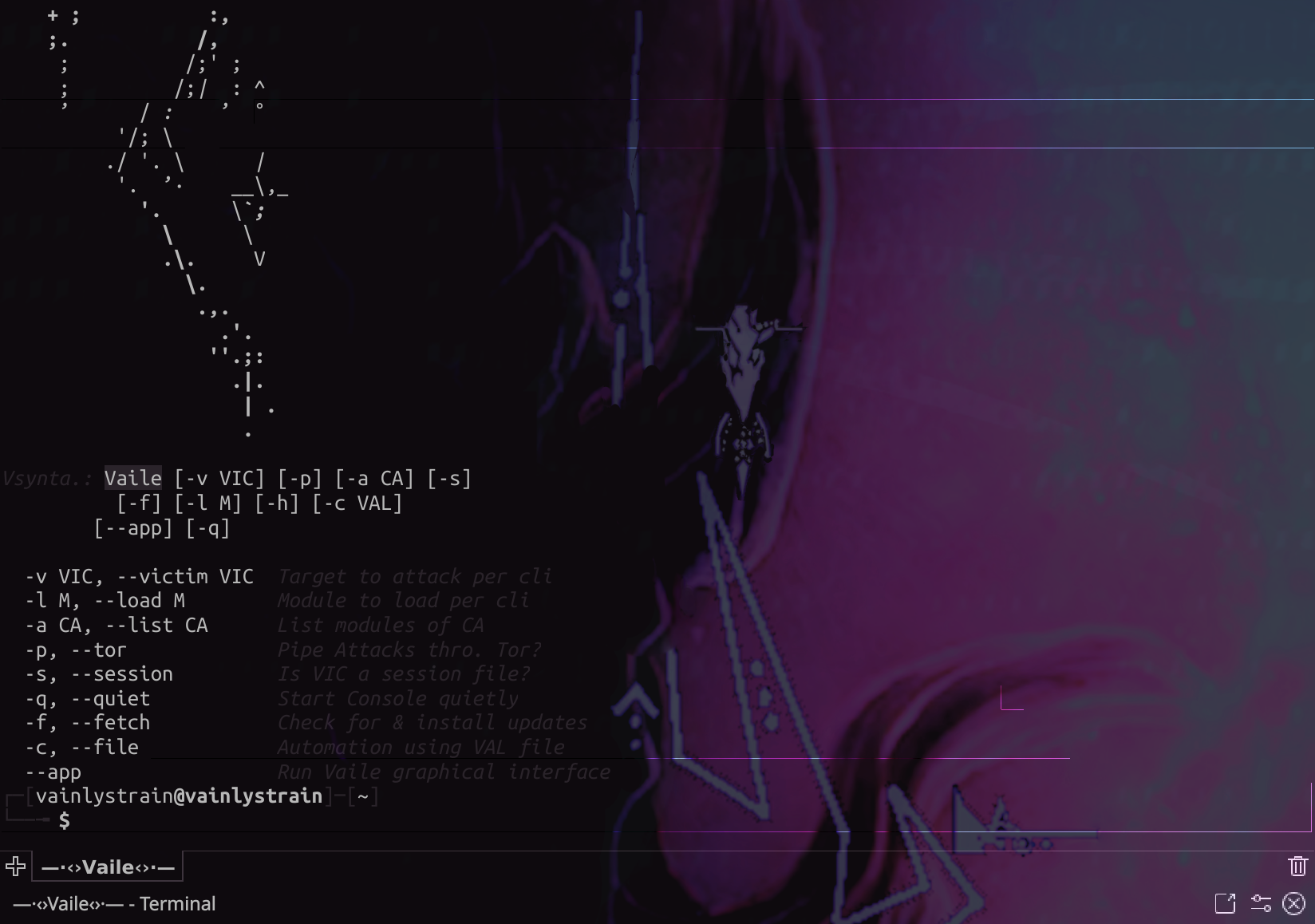
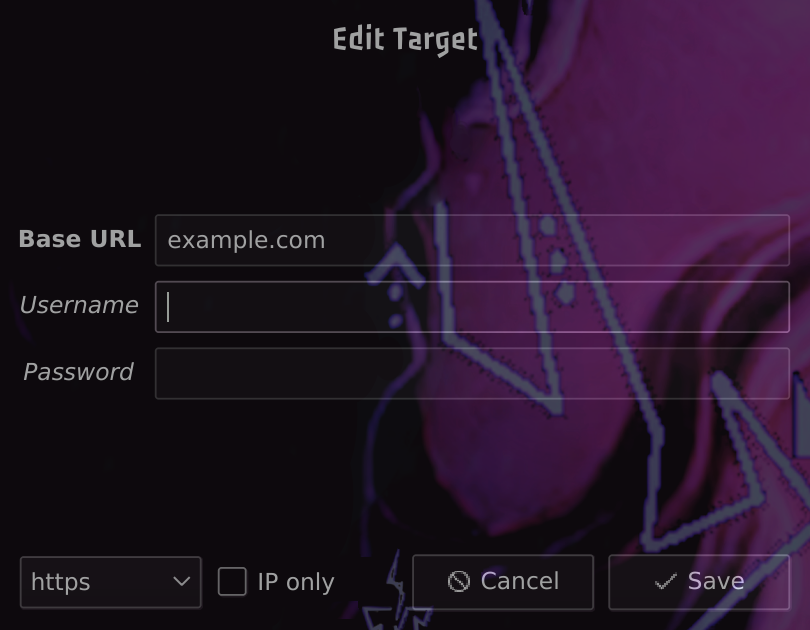
Lets see some screenshots of Vaile in action:
- The core framework:
- The Graphical interface:
v2.2.5-10 [latest release] [#stable]
Vaile is provided as an offensive web application audit framework. It has built-in modules which can reveal potential misconfigurations and vulnerabilties in web applications which could possibly be exploited maliciously.
THEREFORE, NEITHER THE AUTHOR NOR THE CONTRIBUTORS ARE RESPONSIBLE FOR ANY MISUSE OR DAMAGE DUE TO THIS TOOLKIT.