This example deploys a fully ECS Cluster with FARGATE mode. It creates all the necessary infrastructure, such as the VPC, Application Load Balancer and the necessary Roles in 3 availability zones.
It also creates all ECS setup, like cluster, service, tasks, auto scaling and the deploy mode (blue green).
This example creates a Jenkins server on EC2. You should connect to http://<PUBLIC_IP_JENKINS>:8080 and follow the instructions. To get the admin password, you can connect on EC2 via SSM Sessions Manager.
- Create a Pipeline to get configuration via SCM (git). You can use Jenskinsfile on main branch from this Sample Repository
- Replace your values on Jenkinsfile after deployment below.
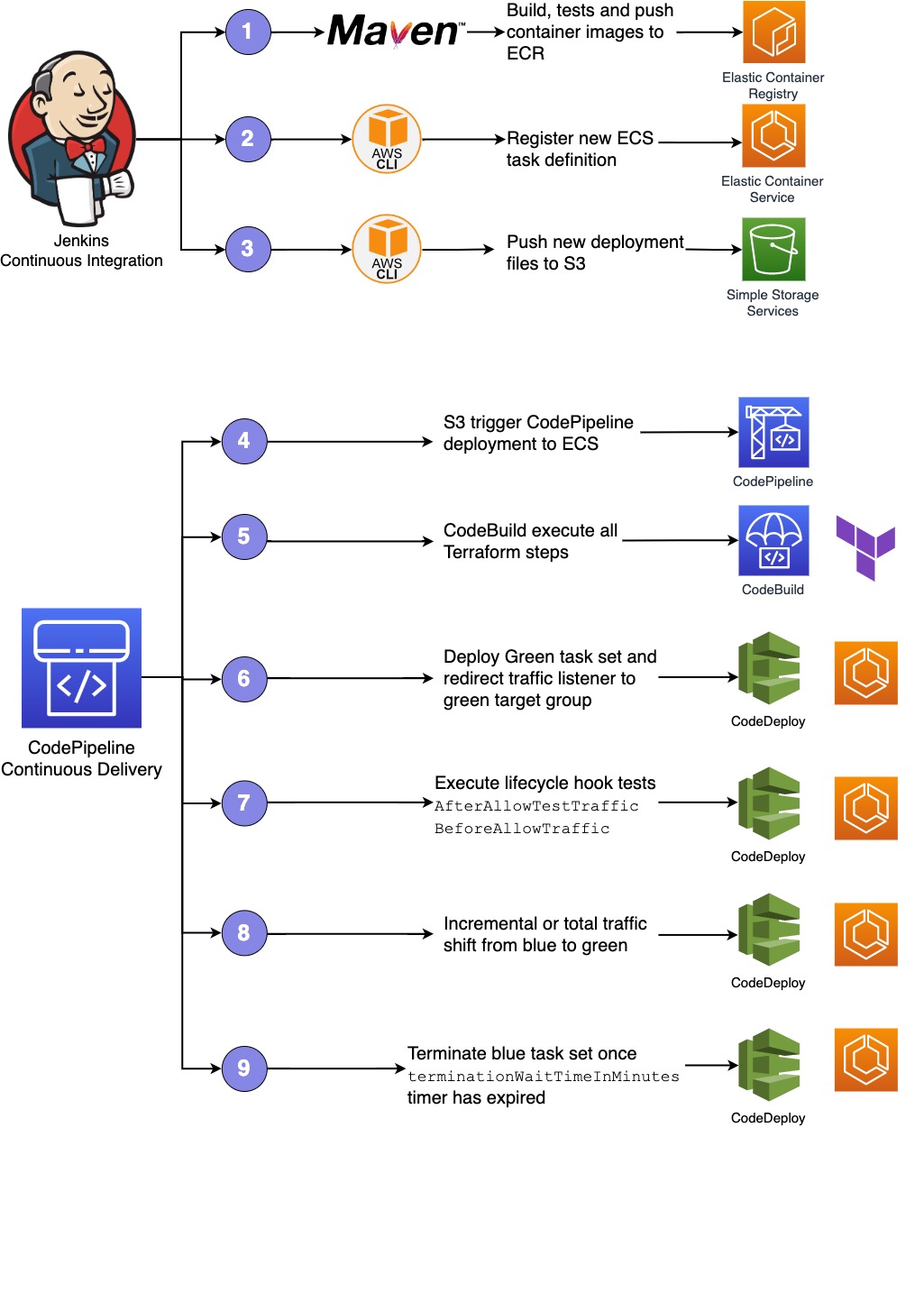
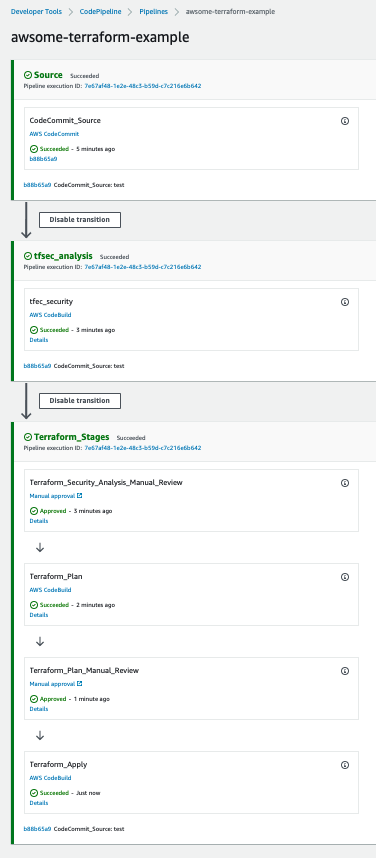
All deployment steps is done through a Pipeline using Jenkins for CI, CodePipeline, CodeBuild and CodeDeploy. In this example, the Terraform flow it's executed via AWS Codebuild before application deployment.
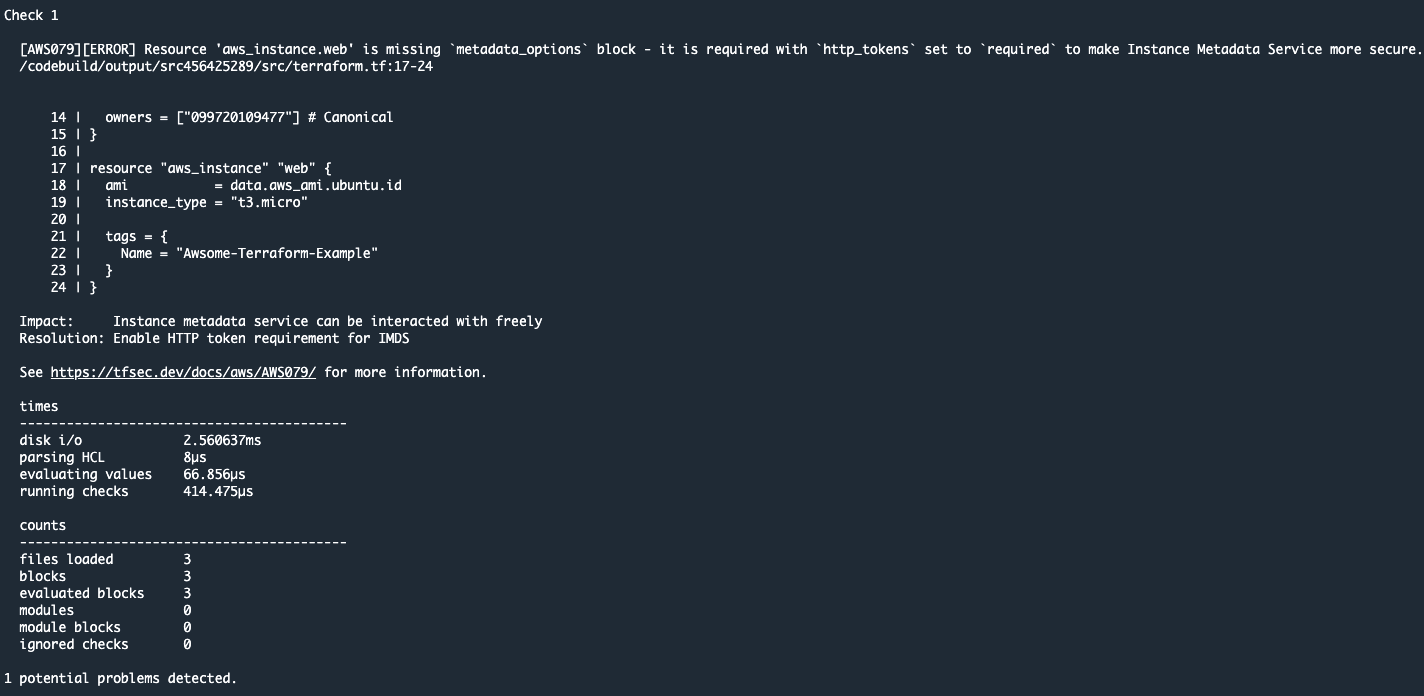
During the pipeline execution, we can check the security checks pased to our tfsec configuration
This configuration is running inside of an AWS Codebuild Container ith the configuration stated at buildspec_tfsec. We highly recommend you to check the tfsec documentation to review the configuration and modify as you need.
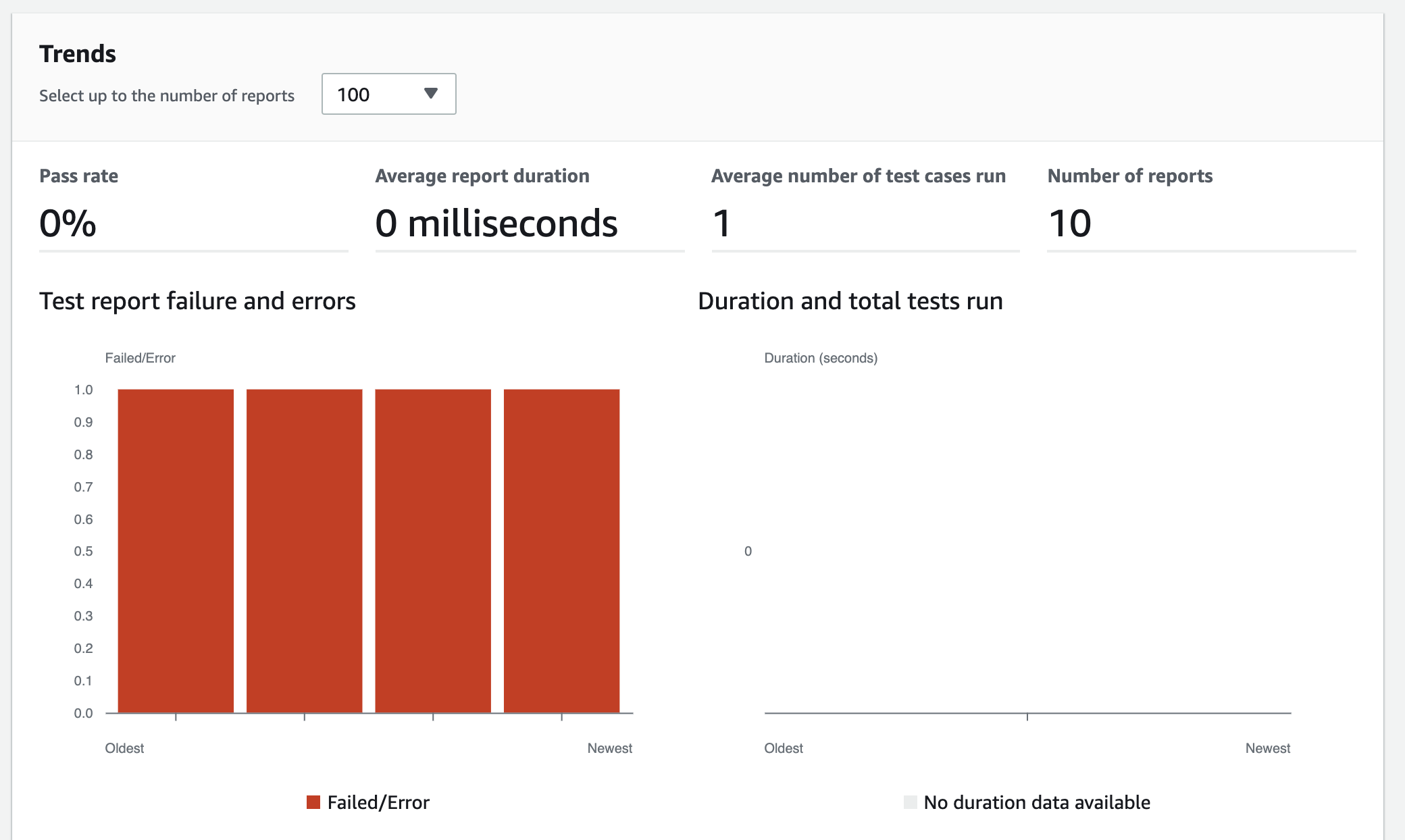
Besides this output, AWS Codebuild also exports the result of tfsec report on the Codebuild reports section
Our pipeline have several manual process:
- Manual process to review the security checks passed via tfsec.
- Manual process to review the Terraform plan output.
- Terraform: IAM policies more restrictive
If you will use remote backend (recommended), please, you have to configure the file below (you have to create the resources before), otherwise, just simple remove this file for local backend
backend.tfIf you want an example about how to create your remote backend infrastructure, go to infra_backend directory and replace variables.tf file with your data and follow the steps below
export AWS_REGION=<ENTER YOUR REGION> # Select your own region
terraform init
terraform plan
terraform applyEnsure that you have installed the following tools in your Mac or Windows Laptop before start working with this module and run Terraform Plan and Apply
git clone '<this repository>'Initialize a working directory with configuration files
cd '<this repository directory>'
terraform initVerify the resources created by this execution
export AWS_REGION=<ENTER YOUR REGION> # Select your own region
terraform planto create resources
terraform applyEnter yes to apply
The following command destroys the resources created by terraform apply
cd '<this repository directory>'
terraform destroy --auto-approve| Name | Version |
|---|---|
| terraform | >= 0.13 |
| aws | ~> 4.0 |
No providers.
| Name | Source | Version |
|---|---|---|
| devops | ./modules/devops | n/a |
| ec2 | ./modules/ec2 | n/a |
| ecs | ./modules/ecs | n/a |
| network | ./modules/network | n/a |
No resources.
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| availability_zones | Define subnets AZs | list(string) |
[ |
no |
| instance_type | Define EC2 instance type | string |
"jenkins-lab" |
no |
| name | Define EC2 TAG name | string |
"t2.medium" |
no |
| object_lock_days | The number of days that you want to specify for the default retention period | number |
365 |
no |
| object_lock_mode | The default Object Lock retention mode you want to apply to new objects placed in the specified bucket | string |
"GOVERNANCE" |
no |
| private_subnet_cidr_block | Define private subnet CIDRs | list(string) |
[ |
no |
| public_subnet_cidr_block | Define public subnet CIDRs | list(string) |
[ |
no |
| scale_max_capacity | Define max containers capacity for ECS Service Autoscale | number |
2 |
no |
| scale_min_capacity | Define min containers capacity for ECS Service Autoscale | number |
1 |
no |
| vpc_cidr_block | Define VPC CIDR block | string |
"10.10.0.0/16" |
no |
| vpc_name | Define the name of the network | string |
"poc-ecs" |
no |
| Name | Description |
|---|---|
| aws_public_security_group_id | n/a |
| private_subnet_ids | n/a |
| public_subnet_ids | n/a |
| vpc_id | n/a |