This Repository contains CORS misconfiguration related vulnerable codes. One can configure the Vulnerable code on local machine to perform practical exploitation of CORS related misconfiguration issues.
I would like to say Thank You to @albinowax (For his work in CORS exploitation), AKReddy and Vivek Sir (For being great personalities who always supported me) and Andrew Sir - @vanderaj (for his encouraging words)
git clone https://github.com/incredibleindishell/CORS_vulnerable_Lab-Without_Database.git
cd CORS_vulnerable_Lab-Without_Database
docker build . -t <tagname>
docker run -d -p 8000:80 <tagname>
Access it as http://localhost:8000
Following are the pre-requities to configure the vulnerable code on local/remote machine
- Apache web server
- PHP 5/7
Steps to Configure:
- Download and extract the codes in "htdocs" or webroot directory of the web server.
- Access the "CORS Vulnerable Lab" application.
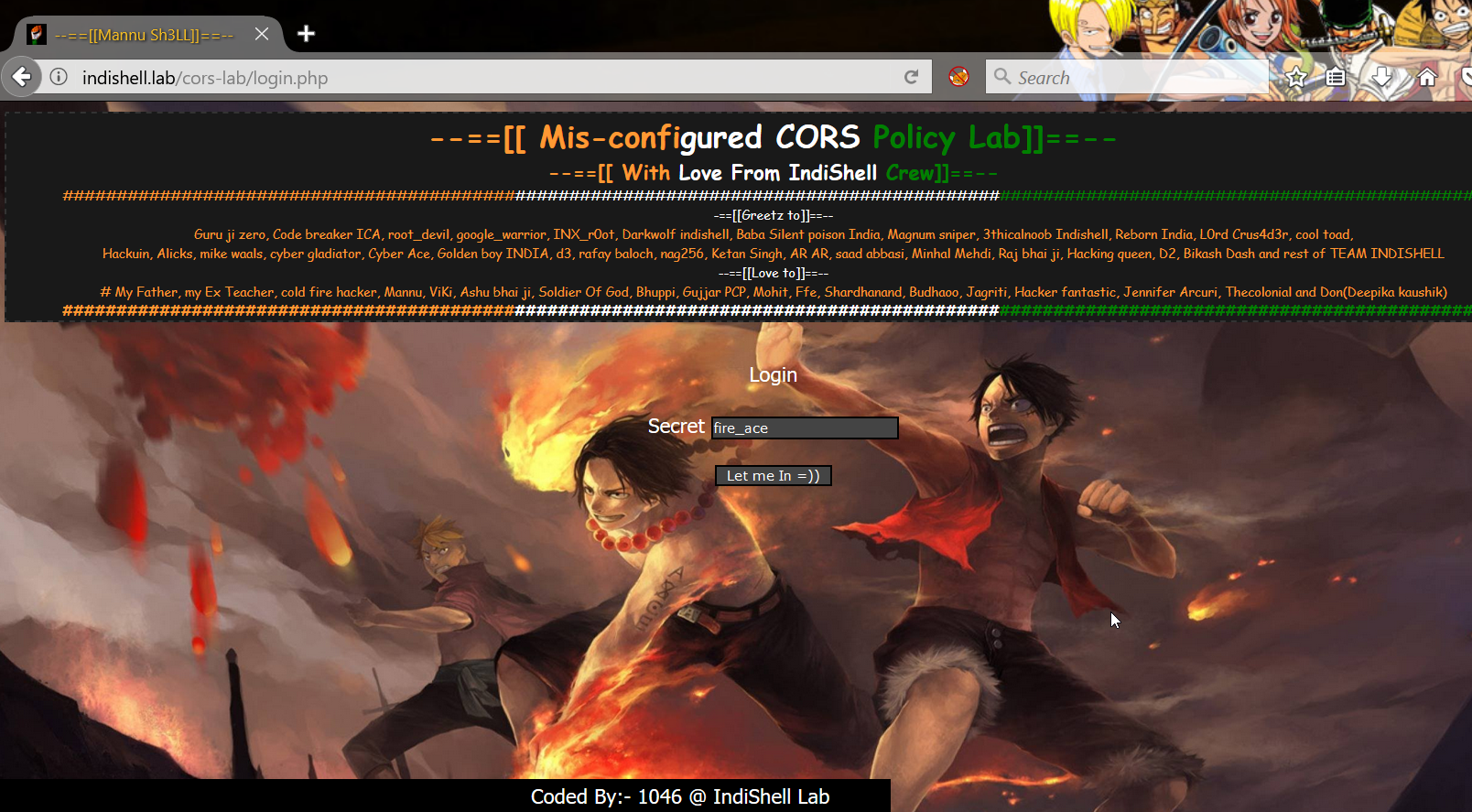
- Login credentials are already specified in input fields, just click "Let Me In" button and you are ready to play with the lab.
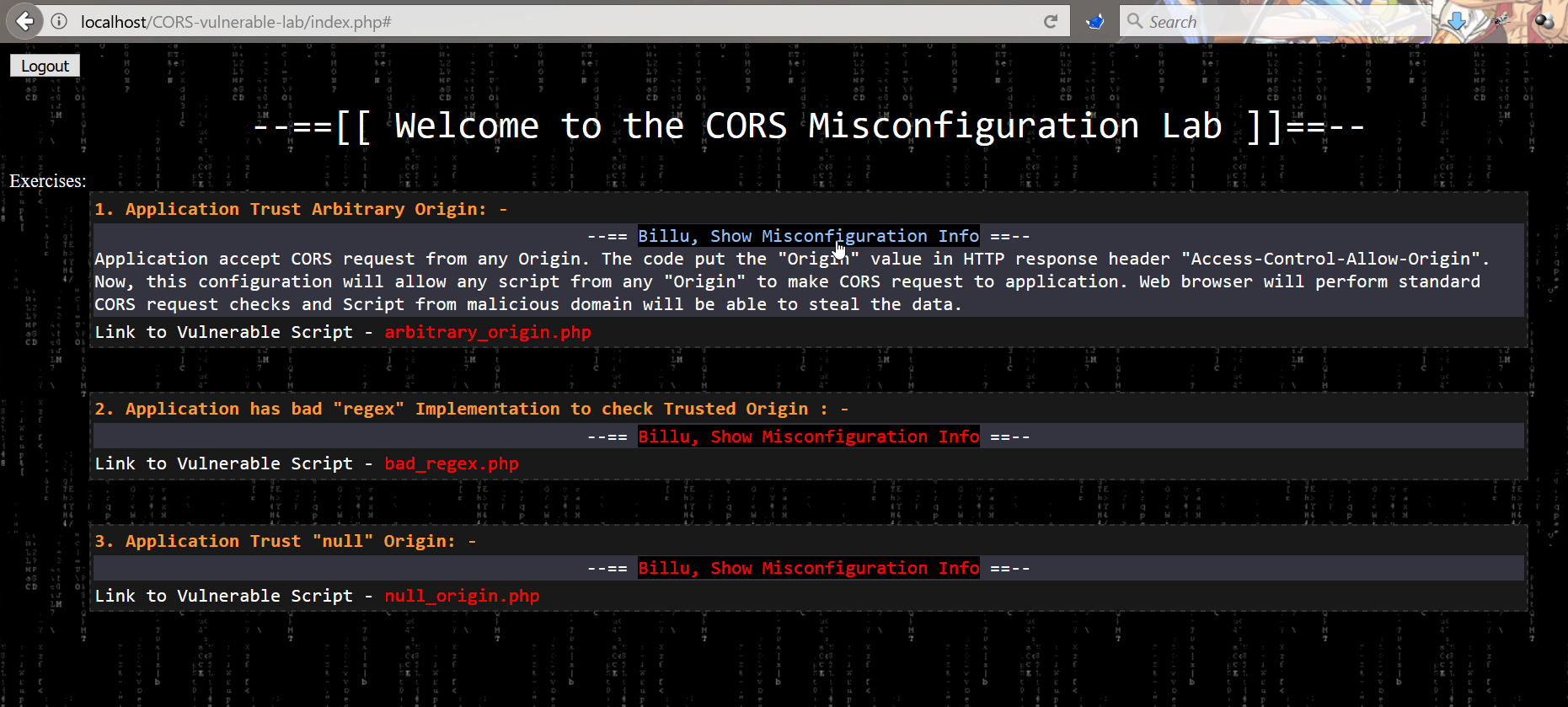
There are 3 misconfiguration which are simulated in this Lab.
Application Trust Arbitrary Origin
Application accept CORS request from any Origin. The code put the "Origin" value in HTTP response header "Access-Control-Allow-Origin". Now, this configuration will allow any script from any "Origin" to make CORS request to application. Web browser will perform standard CORS request checks and Script from malicious domain will be able to steal the data.
Application has bad "regex" Implementation to check Trusted Origin
Application has CORS policy implemented and perform "Regex" check for whitelisted Domain/Sub-domains. In this scenario, application has weak regex implementation in code which just check for presence of domain name "b0x.com" anywhere in HTTP request "Origin" header. If HTTP header "Origin" has value "inb0x.com" or b0x.comlab.com, regex will mark it pass. This misconfiguration will lead to sharing of data over cross origin.
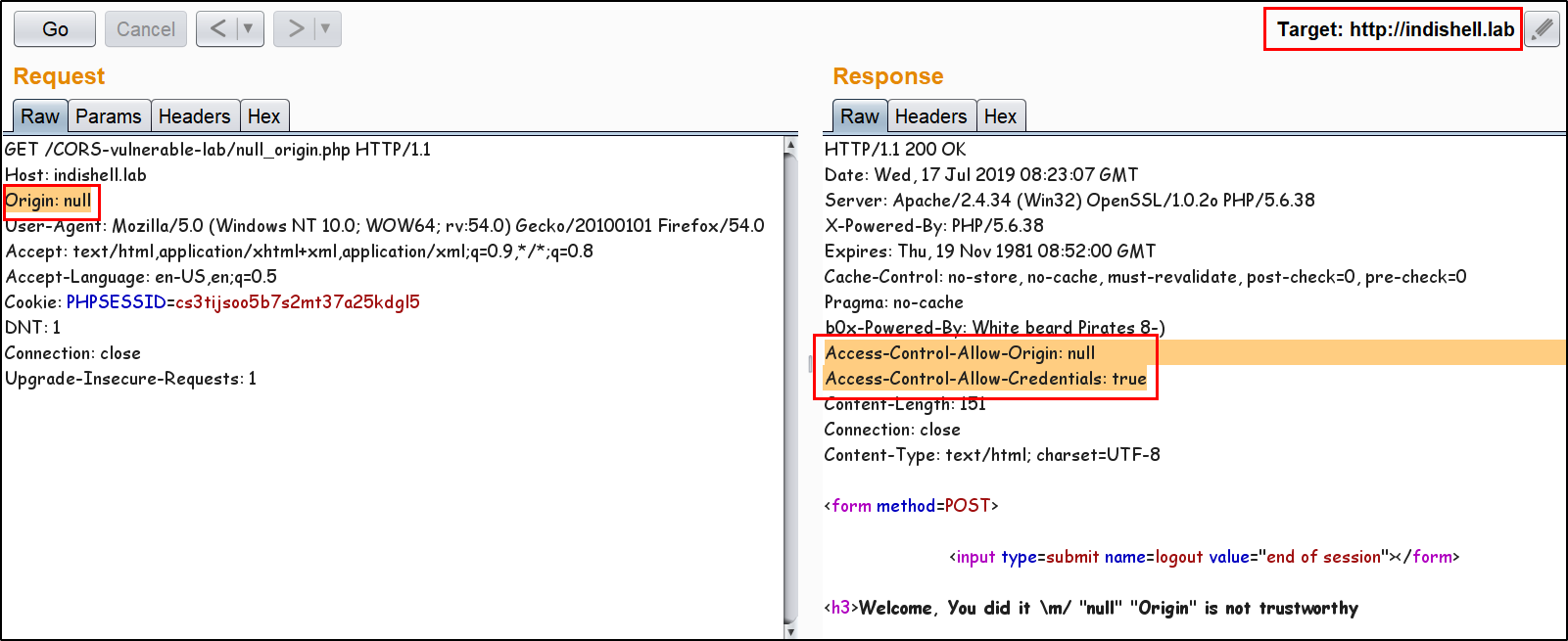
Application Trust "null" Origin
In this scenario, application HTTP response header "Access-Control-Allow-Origin" is always set to "null". When user specify any value other than null, application does not process it and keep reflecting "null" in HTTP response. There are few tricks which allow an attacker to perform exploitation and can ex-filtrate data of victim using CORS request.
Examples:
Application Trust Arbitrary Origin
Application accept any value specified in "Origin" header.
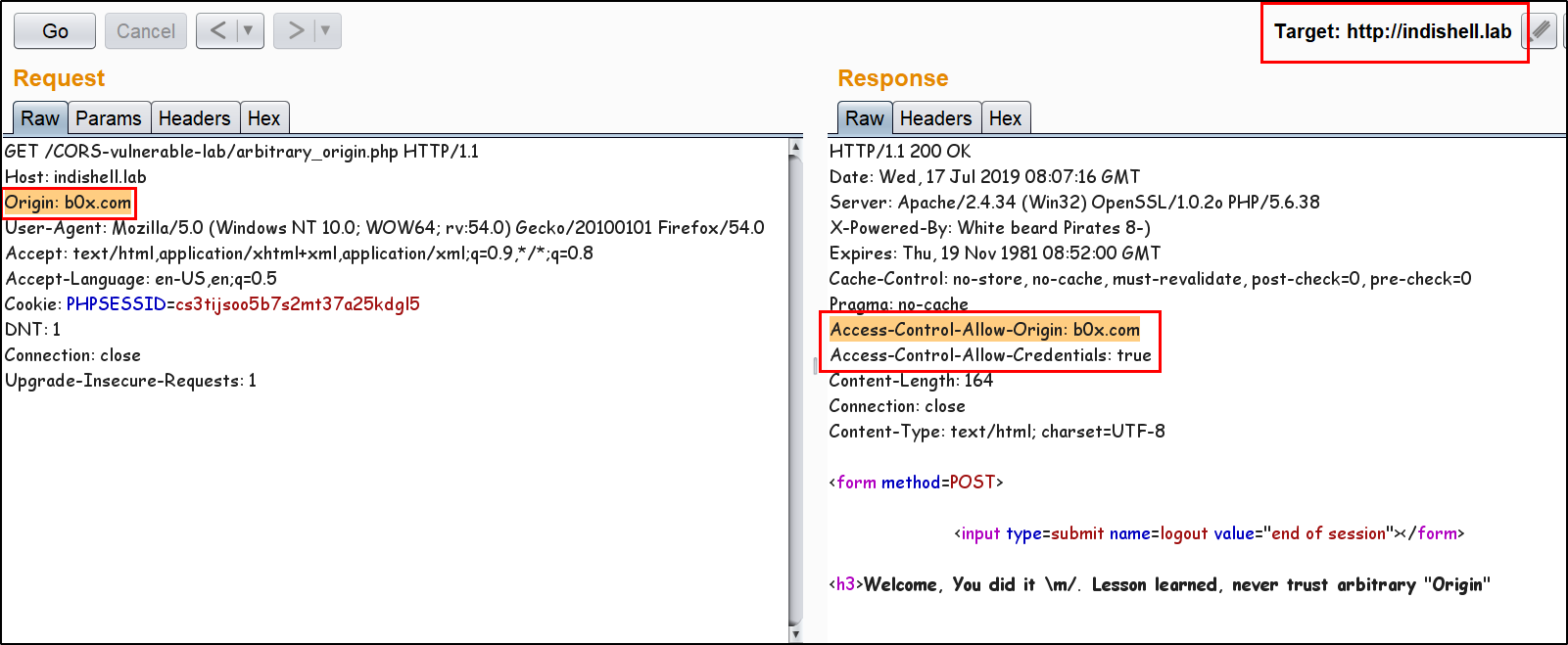
Exploitation Demo
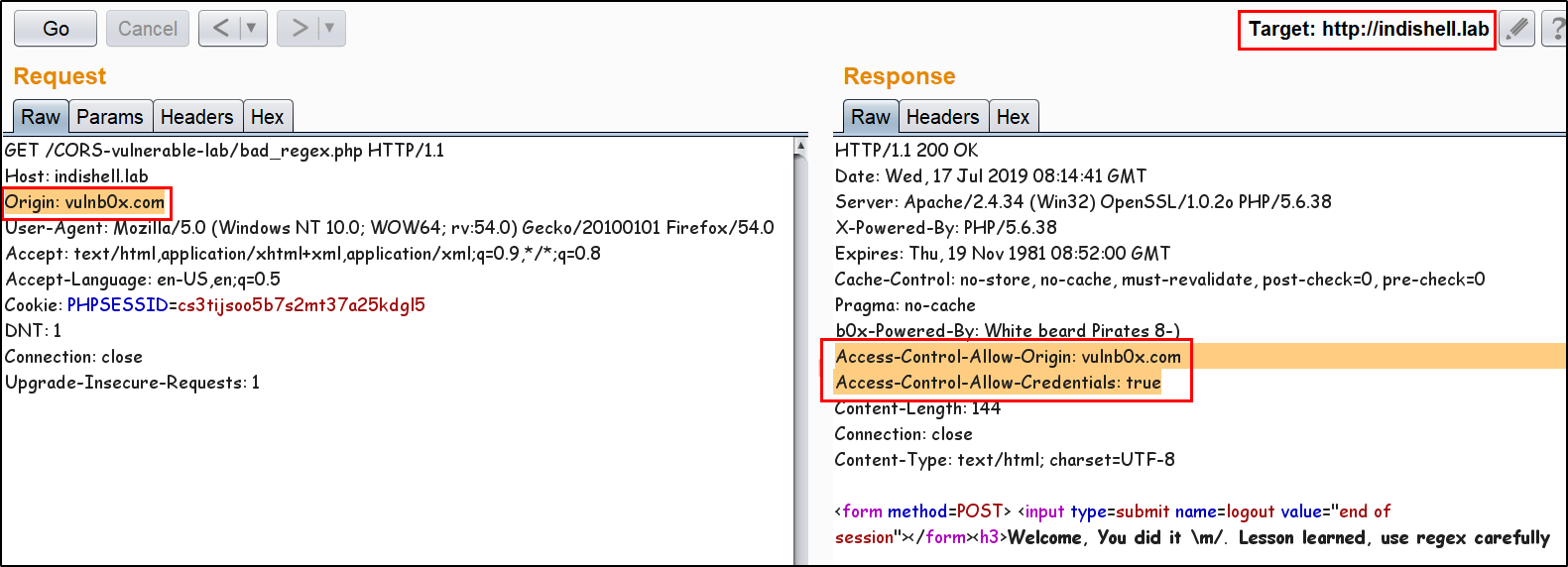
Application has bad "regex" Implementation to check Trusted Origin
Application is trusting whitelisted Origin.
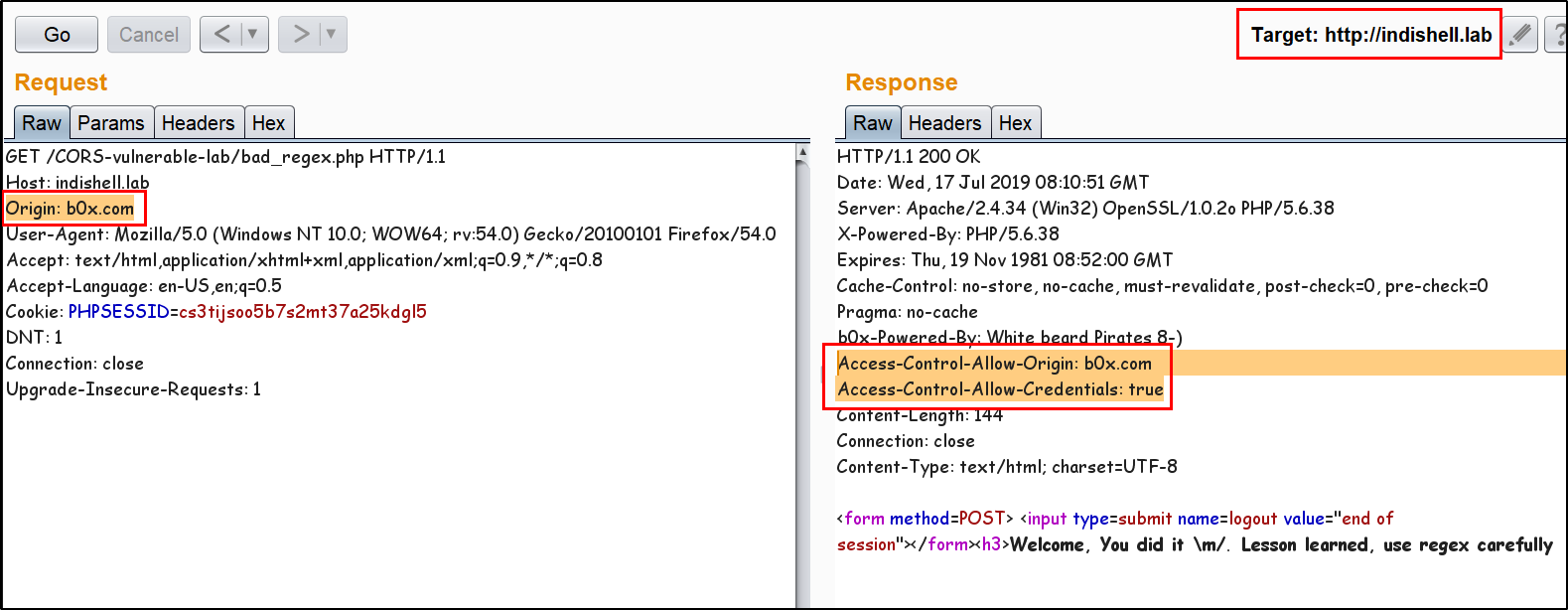
Application is not allowing any arbitrary Origin.
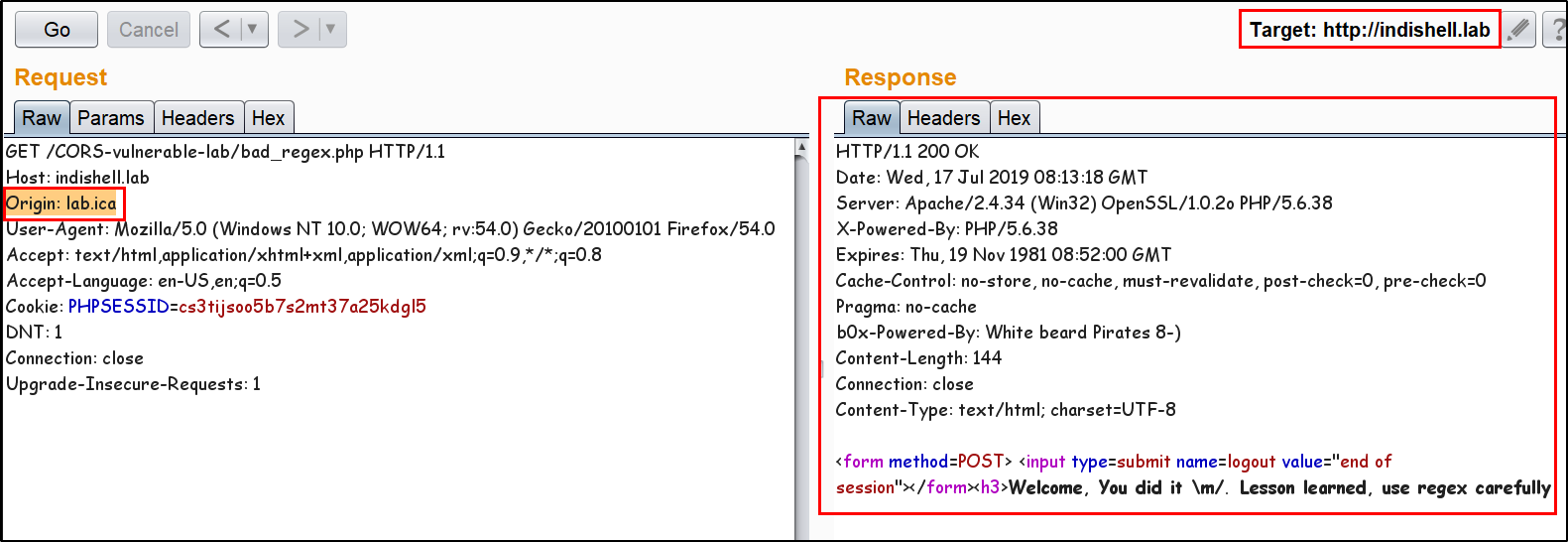
Application weak regex allowing an Origin which has whitelisted domain string in starting of the domain name.
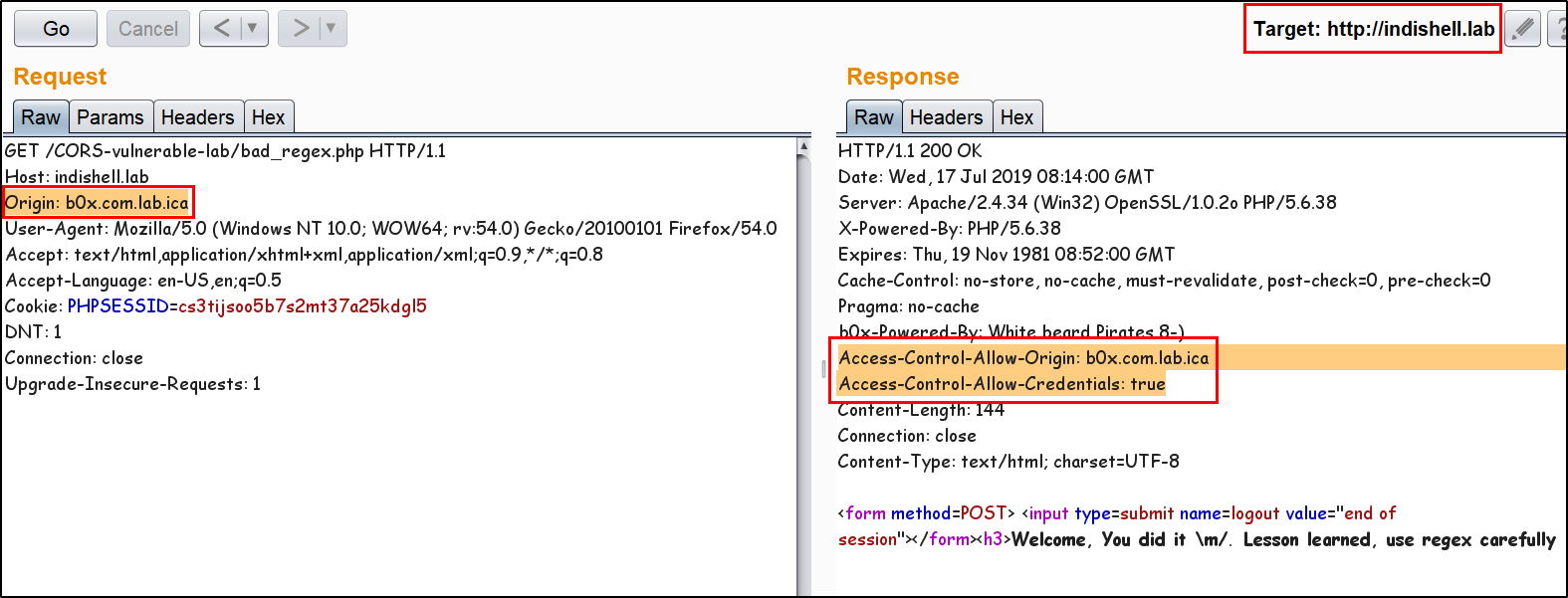
Application weak regex allowing an Origin which has whitelisted domain string in the end of the domain name.
Application Trust "null" Origin
Application accept "null" value specified in "Origin" header.
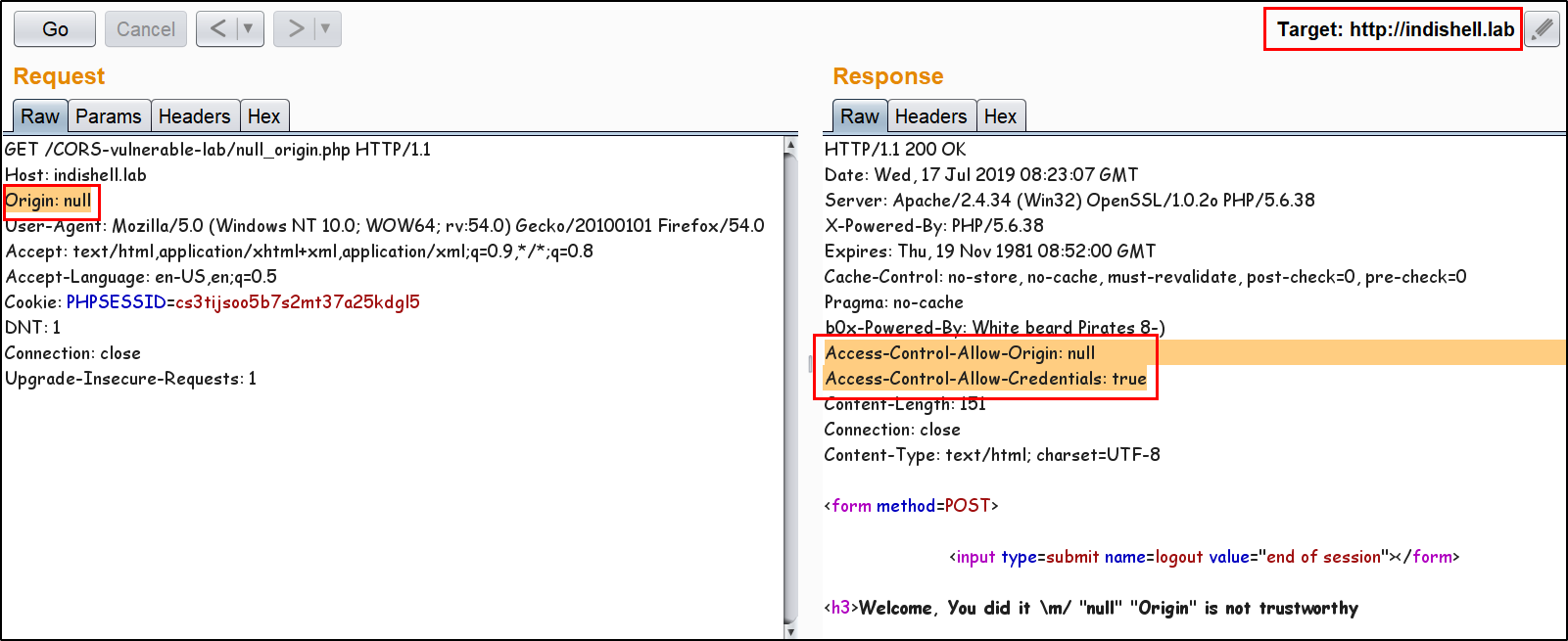
Application is not accepting any value other then "null" "Origin".
Exploitation Demo
Ex-filtrating data to attacker controlled server
Ofcourse,
--==[[ With Love From IndiShell ]]==--
--==[[ Greetz To ]]==--
Guru ji zero, Code breaker ICA, root_devil, google_warrior, INX_r0ot, Darkwolf indishell, Baba,
Silent poison India, Magnum sniper, ethicalnoob Indishell, Reborn India, L0rd Crus4d3r, cool toad,
Hackuin, Alicks, mike waals, cyber gladiator, Cyber Ace, Golden boy INDIA, d3, rafay baloch, nag256
Ketan Singh, AR AR, saad abbasi, Minhal Mehdi, Raj bhai ji, Hacking queen, lovetherisk, D2, Bikash Dash and rest of the Team INDISHELL
--==[[Love to]]==--
My Father, my Ex Teacher, cold fire hacker, Mannu, ViKi, Ashu bhai ji, Soldier Of God, Bhuppi, Gujjar PCP
Mohit, Ffe, Shardhanand, Budhaoo, bohops, Hacker fantastic, Jennifer Arcuri, Thecolonial, S3cur3Th1sSh1t, Ben R
Anurag Bhai ji, Vivek bhai ji and Don(Deepika kaushik)