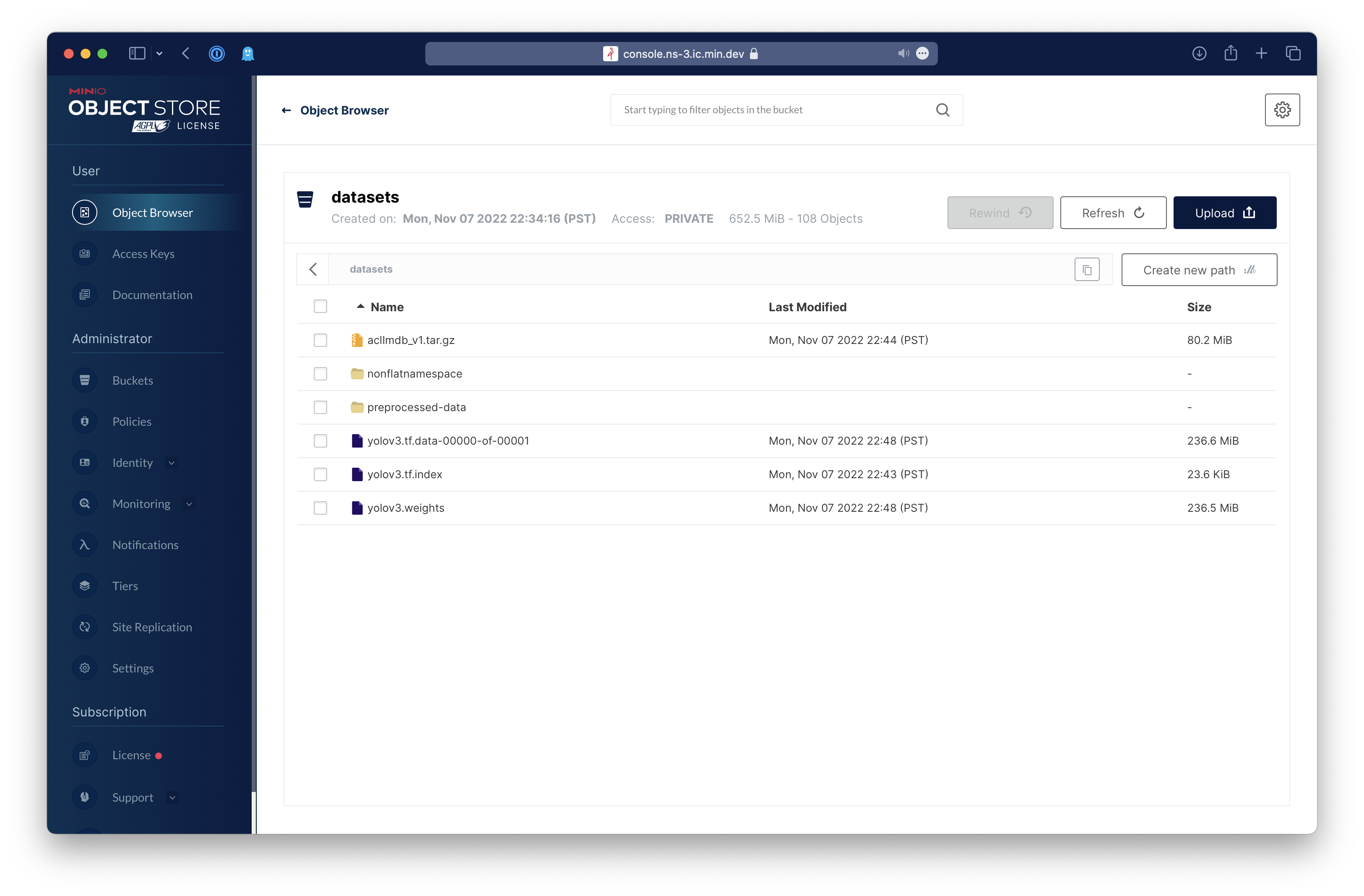
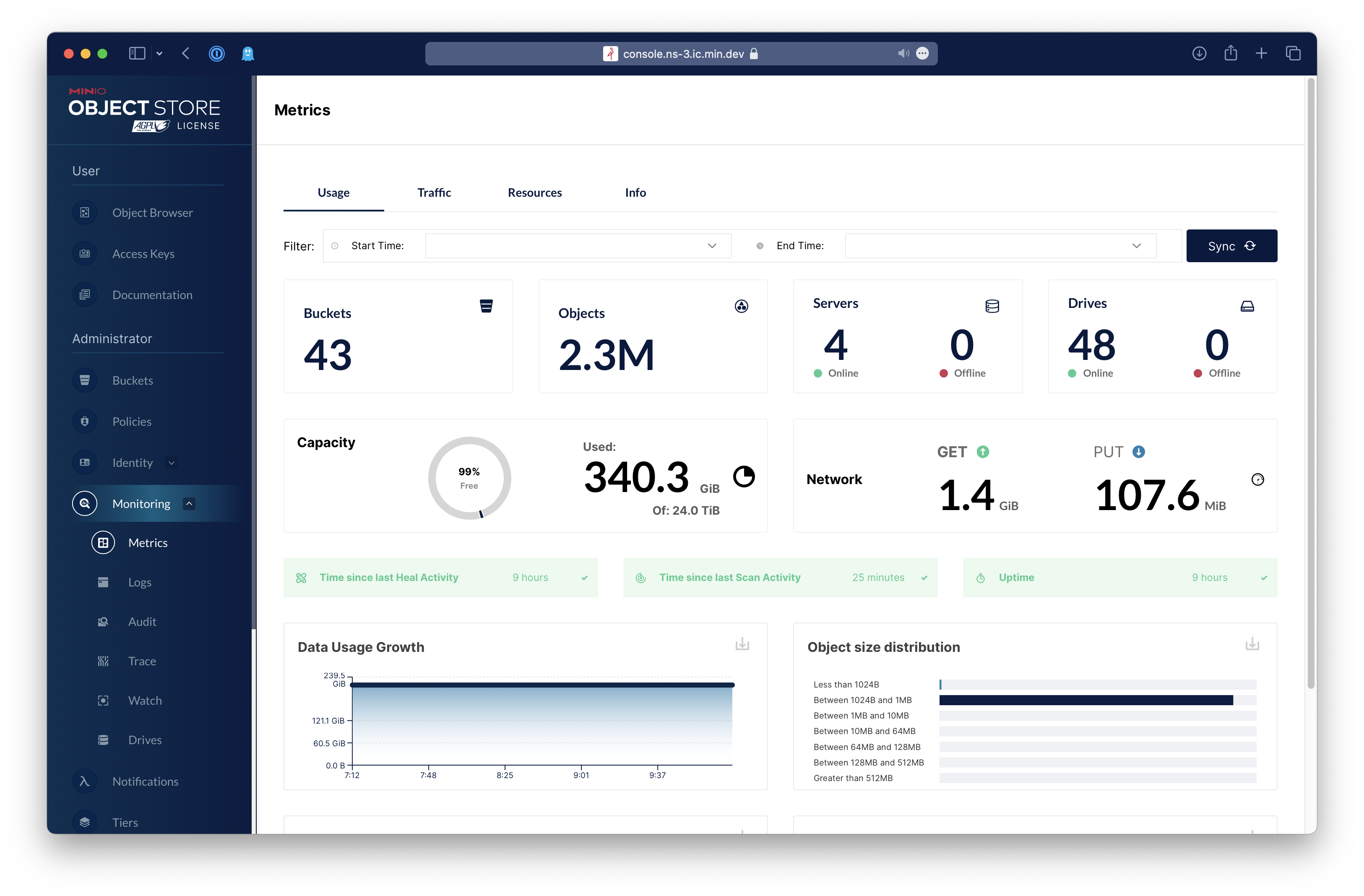
A graphical user interface for MinIO
| Object Browser | Dashboard | Creating a bucket |
|---|---|---|
 |
 |
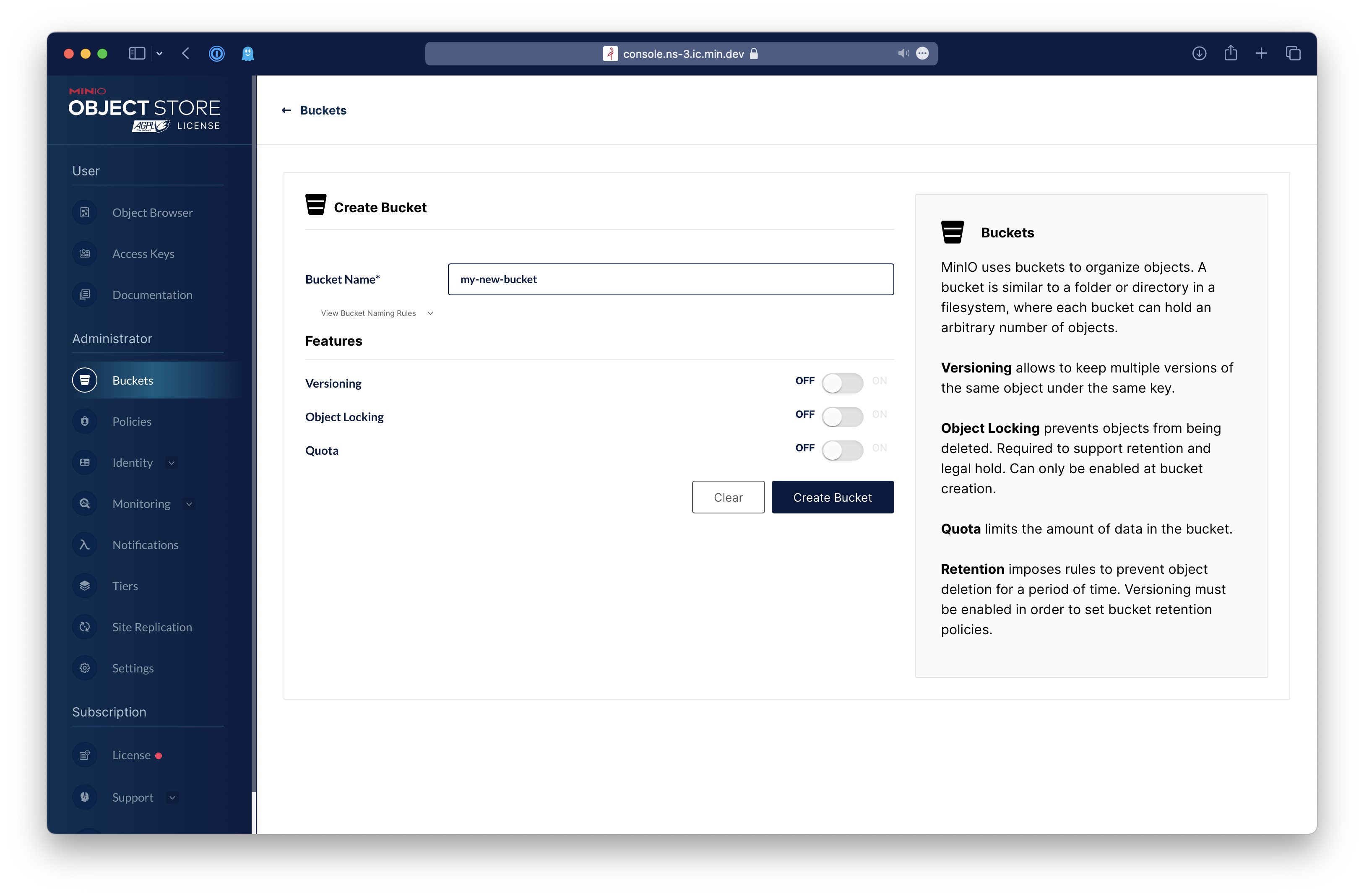 |
Table of Contents
- MinIO Console
- Contribute to console Project
MinIO Console is a library that provides a management and browser UI overlay for the MinIO Server. The standalone binary installation path has been removed.
In case a Console standalone binary is needed, it can be generated by building this package from source as follows:
You will need a working Go environment. Therefore, please follow How to install Go. Minimum version required is go1.22
go install github.com/minio/console/cmd/console@latest
All console needs is a MinIO user with admin privileges and URL pointing to your MinIO deployment.
Note: We don't recommend using MinIO's Operator Credentials
mc admin user add myminio/
Enter Access Key: console
Enter Secret Key: xxxxxxxxcat > admin.json << EOF
{
"Version": "2012-10-17",
"Statement": [{
"Action": [
"admin:*"
],
"Effect": "Allow",
"Sid": ""
},
{
"Action": [
"s3:*"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::*"
],
"Sid": ""
}
]
}
EOFmc admin policy create myminio/ consoleAdmin admin.jsonmc admin policy attach myminio consoleAdmin --user=consoleNOTE: Additionally, you can create policies to limit the privileges for other
consoleusers, for example, if you want the user to only have access to dashboard, buckets, notifications and watch page, the policy should look like this:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"admin:ServerInfo"
],
"Effect": "Allow",
"Sid": ""
},
{
"Action": [
"s3:ListenBucketNotification",
"s3:PutBucketNotification",
"s3:GetBucketNotification",
"s3:ListMultipartUploadParts",
"s3:ListBucketMultipartUploads",
"s3:ListBucket",
"s3:HeadBucket",
"s3:GetObject",
"s3:GetBucketLocation",
"s3:AbortMultipartUpload",
"s3:CreateBucket",
"s3:PutObject",
"s3:DeleteObject",
"s3:DeleteBucket",
"s3:PutBucketPolicy",
"s3:DeleteBucketPolicy",
"s3:GetBucketPolicy"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::*"
],
"Sid": ""
}
]
}Before running console service, following environment settings must be supplied
# Salt to encrypt JWT payload
export CONSOLE_PBKDF_PASSPHRASE=SECRET
# Required to encrypt JWT payload
export CONSOLE_PBKDF_SALT=SECRET
# MinIO Endpoint
export CONSOLE_MINIO_SERVER=http://localhost:9000Now start the console service.
./console server
2021-01-19 02:36:08.893735 I | 2021/01/19 02:36:08 server.go:129: Serving console at http://localhost:9090
By default console runs on port 9090 this can be changed with --port of your choice.
Copy your public.crt and private.key to ~/.console/certs, then:
./console server
2021-01-19 02:36:08.893735 I | 2021/01/19 02:36:08 server.go:129: Serving console at http://[::]:9090
2021-01-19 02:36:08.893735 I | 2021/01/19 02:36:08 server.go:129: Serving console at https://[::]:9443For advanced users, console has support for multiple certificates to service clients through multiple domains.
Following tree structure is expected for supporting multiple domains:
certs/
│
├─ public.crt
├─ private.key
│
├─ example.com/
│ │
│ ├─ public.crt
│ └─ private.key
└─ foobar.org/
│
├─ public.crt
└─ private.key
...
Copy the MinIO ca.crt under ~/.console/certs/CAs, then:
export CONSOLE_MINIO_SERVER=https://localhost:9000
./console serverYou can verify that the apis work by doing the request on localhost:9090/api/v1/...
In some cases it may be convenient to log all HTTP requests. This can be enabled by setting
the CONSOLE_DEBUG_LOGLEVEL environment variable to one of the following values:
0(default) uses no logging.1log single line per request for server-side errors (status-code 5xx).2log single line per request for client-side and server-side errors (status-code 4xx/5xx).3log single line per request for all requests (status-code 4xx/5xx).4log details per request for server-side errors (status-code 5xx).5log details per request for client-side and server-side errors (status-code 4xx/5xx).6log details per request for all requests (status-code 4xx/5xx).
A single line logging has the following information:
- Remote endpoint (IP + port) of the request. Note that reverse proxies may hide the actual remote endpoint of the client's browser.
- HTTP method and URL
- Status code of the response (websocket connections are hijacked, so no response is shown)
- Duration of the request
The detailed logging also includes all request and response headers (if any).
Please follow console Contributor's Guide
