This tool allows you to statically analyze Windows, Linux, OSX executables and APK files.
You can get:
- What DLL files are used.
- Functions and APIs.
- Sections and segments.
- URLs, IP addresses and emails.
- Android permissions.
- File extensions and their names.
And so on...
Qu1cksc0pe aims to get even more information about suspicious files and helps user realize what that file is capable of.
python3 qu1cksc0pe.py --file suspicious_file --analyze25/04/2022
- You can also use Qu1cksc0pe from
Windows Subsystem Linuxin Windows 10.
Necessary python modules:
puremagic=> Analyzing target OS and magic numbers.androguard=> Analyzing APK files.apkid=> Check for Obfuscators, Anti-Disassembly, Anti-VM and Anti-Debug.rich=> Pretty outputs and TUI.tqdm=> Progressbar animation.colorama=> Colored outputs.oletools=> Analyzing VBA Macros.pefile=> Gathering all information from PE files.quark-engine=> Extracting IP addresses and URLs from APK files.pyaxmlparser=> Gathering informations from target APK files.yara-python=> Android library scanning with Yara rules.prompt_toolkit=> Interactive shell.frida=> Performing dynamic analysis against android applications.lief=> ELF binary parsing and analysis.zepu1chr3=> Analyzing binaries via radare2.
Installation of python modules: pip3 install -r requirements.txt
Gathering other dependencies:
- VirusTotal API Key:
https://virustotal.com - Strings:
sudo apt-get install strings - PyExifTool:
git clone git://github.com/smarnach/pyexiftool.gitthencd pyexiftool && sudo python3 setup.py install
Alert
You must specify jadx binary path in Systems/Android/libScanner.conf
[Rule_PATH]
rulepath = /Systems/Android/YaraRules/
[Decompiler]
decompiler = JADX_BINARY_PATH <-- You must specify this.- You can install Qu1cksc0pe easily on your system. Just execute the following commands.
Command 0:sudo pip3 install -r requirements.txt
Command 1:sudo python3 qu1cksc0pe.py --install
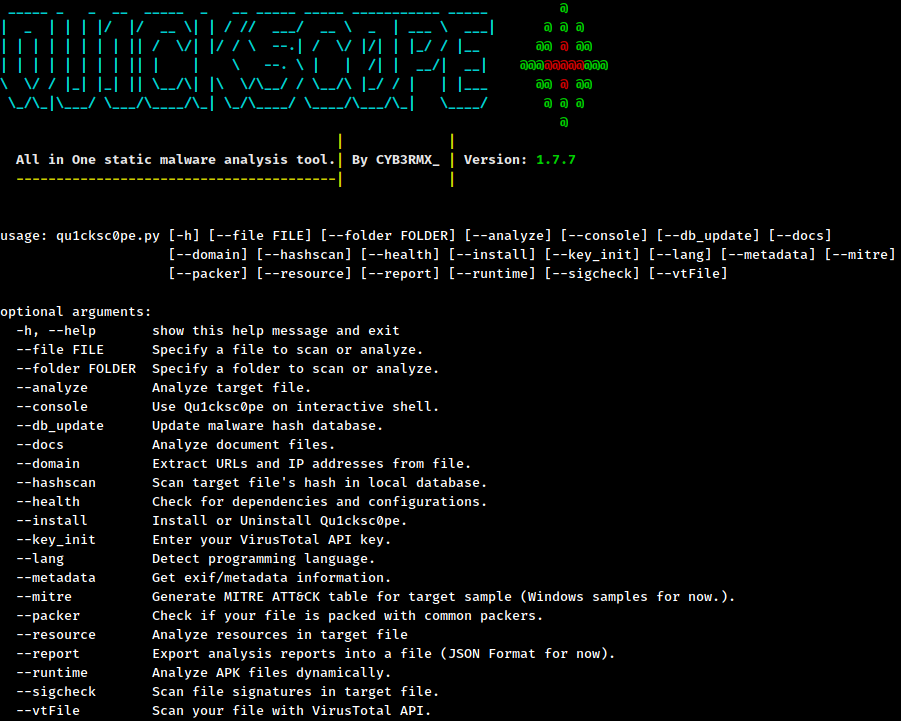
Usage: python3 qu1cksc0pe.py --file suspicious_file --analyze
Usage: python3 qu1cksc0pe.py --file suspicious_file --resource
Alert
You must connect a virtual device or physical device to your computer.
Usage: python3 qu1cksc0pe.py --runtime
Usage: python3 qu1cksc0pe.py --file suspicious_file --hashscan
Supported Arguments:
--hashscan--packer
Usage: python3 qu1cksc0pe.py --folder FOLDER --hashscan
Report Contents:
Threat CategoriesDetectionsCrowdSourced IDS Reports
Usage for --vtFile: python3 qu1cksc0pe.py --file suspicious_file --vtFile
Usage: python3 qu1cksc0pe.py --file suspicious_document --docs
Usage: python3 qu1cksc0pe.py --file suspicious_file --sigcheck
Usage: python3 qu1cksc0pe.py --file suspicious_file --mitre
Usage: python3 qu1cksc0pe.py --file suspicious_executable --lang
Usage: python3 qu1cksc0pe.py --console
Usage: python3 qu1cksc0pe.py --file suspicious_file --domain
This category contains functions and strings about:
- Creating or destroying registry keys.
- Changing registry keys and logs.
This category contains functions and strings about:
- Creating/modifying/infecting/deleting files.
- Getting information about file contents and filesystems.
This category contains functions and strings about:
- Communicating with malicious hosts.
- Downloading malicious files.
- Sending informations about infected machine and its user.
This category contains functions and strings about:
- Creating/infecting/terminating processes.
- Manipulating processes.
This category contains functions and strings about:
- Handling DLL files and another malware's resource files.
- Infecting and manipulating DLL files.
This category contains functions and strings about:
- Manipulating Windows security policies and bypassing restrictions.
- Detecting debuggers and doing evasive tricks.
This category contains functions and strings about:
- Executing system commands.
- Manipulating system files and system options to get persistence in target systems.
This category contains functions and strings about:
- Microsoft's Component Object Model system.
This category contains functions and strings about:
- Encrypting and decrypting files.
- Creating and destroying hashes.
This category contains functions and strings about:
- Gathering informations from target hosts like process states, network devices etc.
This category contains functions and strings about:
- Tracking infected machine's keyboard.
- Gathering information about targets keyboard.
- Managing input methods etc.
This category contains functions and strings about:
- Manipulating and using target machines memory.
For most of FRIDA scripts: https://github.com/Ch0pin/
Another scripts: https://codeshare.frida.re/browse