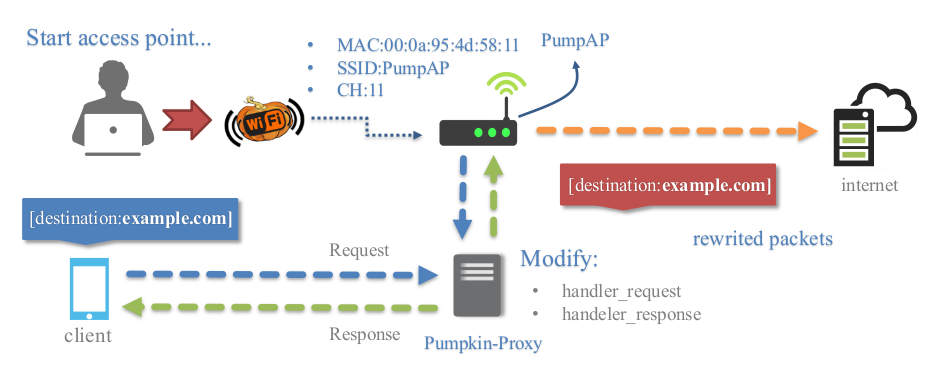
Framework for Rogue Wi-Fi Access Point Attack
WiFi-Pumpkin is an open source security tool that provides the Rogue access point to Man-In-The-Middle and network attacks.
- Python 2.7
git clone https://github.com/P0cL4bs/WiFi-Pumpkin.git
cd WiFi-Pumpkin
./installer.sh --installor download .deb file to install
sudo dpkg -i wifi-pumpkin-0.8.4-all.deb
refer to the wiki for Installation
- Rogue Wi-Fi Access Point
- Deauth Attack Clients AP
- Probe Request Monitor
- DHCP Starvation Attack
- Credentials Monitor
- Transparent Proxy
- Windows Update Attack
- Phishing Manager
- Partial Bypass HSTS protocol
- Support beef hook
- ARP Poison
- DNS Spoof
- Patch Binaries via MITM
- Karma Attacks (support hostapd-mana)
- LLMNR, NBT-NS and MDNS poisoner (Responder)
- Pumpkin-Proxy (ProxyServer (mitmproxy API))
| Plugin | Description |
|---|---|
| net-creds | Sniff passwords and hashes from an interface or pcap file |
| dns2proxy | This tools offer a different features for post-explotation once you change the DNS server to a Victim. |
| sslstrip2 | Sslstrip is a MITM tool that implements Moxie Marlinspike's SSL stripping attacks based version fork @LeonardoNve/@xtr4nge. |
| sergio-proxy | Sergio Proxy (a Super Effective Recorder of Gathered Inputs and Outputs) is an HTTP proxy that was written in Python for the Twisted framework. |
| BDFProxy-ng | Patch Binaries via MITM: BackdoorFactory + mitmProxy, bdfproxy-ng is a fork and review of the original BDFProxy @secretsquirrel. |
| Responder | Responder an LLMNR, NBT-NS and MDNS poisoner. Author: Laurent Gaffie |
Transparent proxies(mitmproxy) that you can use to intercept and manipulate HTTP traffic modifying requests and responses, that allow to inject javascripts into the targets visited. You can easily implement a module to inject data into pages creating a python file in directory "plugins/extension/" automatically will be listed on Pumpkin-Proxy tab.
from mitmproxy.models import decoded # for decode content html
from plugins.extension.plugin import PluginTemplate
class Nameplugin(PluginTemplate):
meta = {
'Name' : 'Nameplugin',
'Version' : '1.0',
'Description' : 'Brief description of the new plugin',
'Author' : 'by dev'
}
def __init__(self):
for key,value in self.meta.items():
self.__dict__[key] = value
# if you want set arguments check refer wiki more info.
self.ConfigParser = False # No require arguments
def request(self, flow):
print flow.__dict__
print flow.request.__dict__
print flow.request.headers.__dict__ # request headers
host = flow.request.pretty_host # get domain on the fly requests
versionH = flow.request.http_version # get http version
# get redirect domains example
# pretty_host takes the "Host" header of the request into account,
if flow.request.pretty_host == "example.org":
flow.request.host = "mitmproxy.org"
# get all request Header example
self.send_output.emit("\n[{}][HTTP REQUEST HEADERS]".format(self.Name))
for name, valur in flow.request.headers.iteritems():
self.send_output.emit('{}: {}'.format(name,valur))
print flow.request.method # show method request
# the model printer data
self.send_output.emit('[NamePlugin]:: this is model for save data logging')
def response(self, flow):
print flow.__dict__
print flow.response.__dict__
print flow.response.headers.__dict__ #convert headers for python dict
print flow.response.headers['Content-Type'] # get content type
#every HTTP response before it is returned to the client
with decoded(flow.response):
print flow.response.content # content html
flow.response.content.replace('</body>','<h1>injected</h1></body>') # replace content tag
del flow.response.headers["X-XSS-Protection"] # remove protection Header
flow.response.headers["newheader"] = "foo" # adds a new header
#and the new header will be added to all responses passing through the proxyplugins on the wiki
Screenshot on the wiki
FAQ on the wiki
Whether you want to report a bug, send a patch or give some suggestions on this project, drop us or open pull requests
Via BTC: 1HBXz6XX3LcHqUnaca5HRqq6rPUmA3pf6f
Happy MITM!