datagrip-vault-plugin
This plugin provides database credentials using Vault dynamic secrets.
Vault login is not handled by this plugin.
You should manually log in into Vault, which will, using the default Token Helper, create a Vault token file in $HOME/.vault-token.
The recommended way to use this plugin is with a Vault Agent, with Auto-Auth and cache enabled.
Installation
-
Using IDE built-in plugin system:
Settings/Preferences > Plugins > Marketplace > Search for "datagrip-vault-plugin" > Install Plugin
-
Manually:
Download the latest release and install it manually using Settings/Preferences > Plugins > ⚙️ > Install plugin from disk...
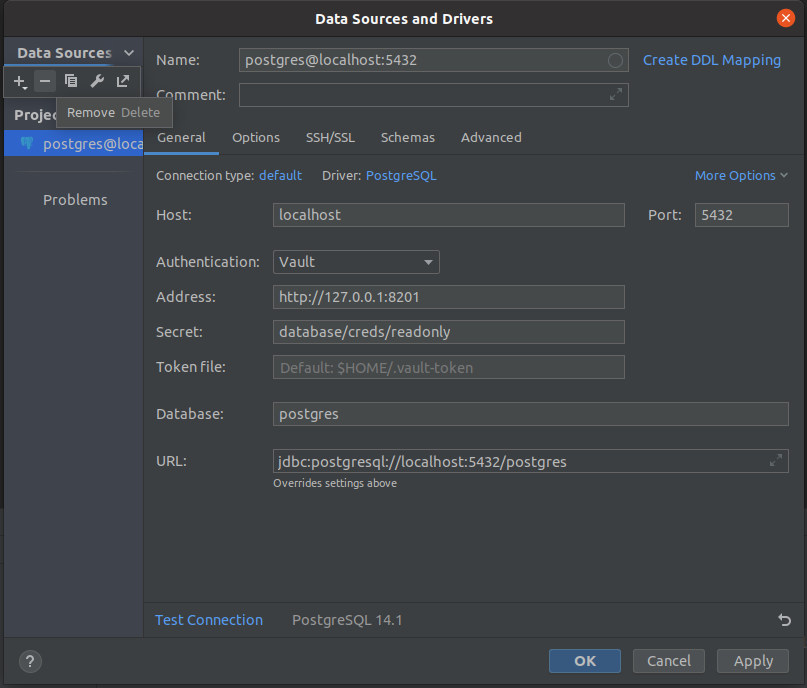
Screenshots
Vault Agent
This plugin will request new credentials everytime a connection is open to the database. To re-use already existing and valid credentials a Vault Agent is recommended.
This is an example, with AWS Authenticaton. Save it as vault-agent-datagrip.hcl and edit accordingly:
auto_auth {
method "aws" {
config = {
type = "iam"
role = "zzz"
access_key = "xxx"
secret_key = "yyy"
header_value = "https://vault.example.com"
}
}
sink "file" {
config = {
path = "/opt/vault/vault-token-datagrip"
}
}
}
vault {
address = "https://vault.example.com"
}
cache {
use_auto_auth_token = true
}
listener "tcp" {
address = "127.0.0.1:8101"
tls_disable = true
}Launch the Vault Agent with vault agent -log-level=debug -config vault-agent-datagrip.hcl.
Configure a DataGrip database connection with:
Address: 127.0.0.1:8101Token file: /opt/vault/vault-token-datagrip
Launching Vault Agent automatically
To skip launching the Vault Agent manually, you can configure your system manager to launch it on startup. For systemd create a /etc/systemd/system/vault-agent-datagrip.service with:
[Unit]
Description="Vault Agent to serve Tokens - DataGrip"
[Service]
User=froque
WorkingDirectory=/opt/vault
ExecStart=/usr/bin/vault agent -config=/opt/vault-agent-datagrip.hcl
Restart=always
[Install]
WantedBy=multi-user.targetLaunch the Vault Agent with sudo systemctl start vault-agent-datagrip.