This project is an e-commerce experimental platform for the Software Security course.
These instructions will get you a copy of the project up and running on your local machine for development and testing purposes.
Make sure you have the following software installed:
- Python 3.11.2
- PostgreSQL 13+
- pgAdmin 8.6
-
Clone the repository:
git clone https://github.com/ChrisDaskalos/e-shop_softsec.gitcd e-shop_softsec -
Set up a virtual environment:
python -m venv venvsource venv/bin/activateOn Windows use:
venv\Scripts\activate -
Install the required Python packages:
pip install -r requirements.txt -
Set up the database:
- Ensure PostgreSQL is running and create a database named
eshopdb. - Create a user named
eshopuserwith password1234and grant all privileges on the database.
- Ensure PostgreSQL is running and create a database named
-
Apply migrations:
python manage.py makemigrationspython manage.py migrate -
Run the SSL server:
Before running the SSL server, make sure you have SSL certificates placed in the
ssldirectory of your project.python manage.py runsslserver
Below is a list of all the available pages in the e-shop project:
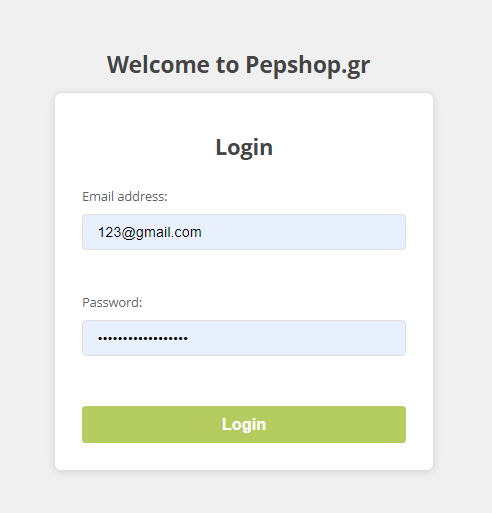
URL: /
Description: This is the landing page where users can log in to their accounts.
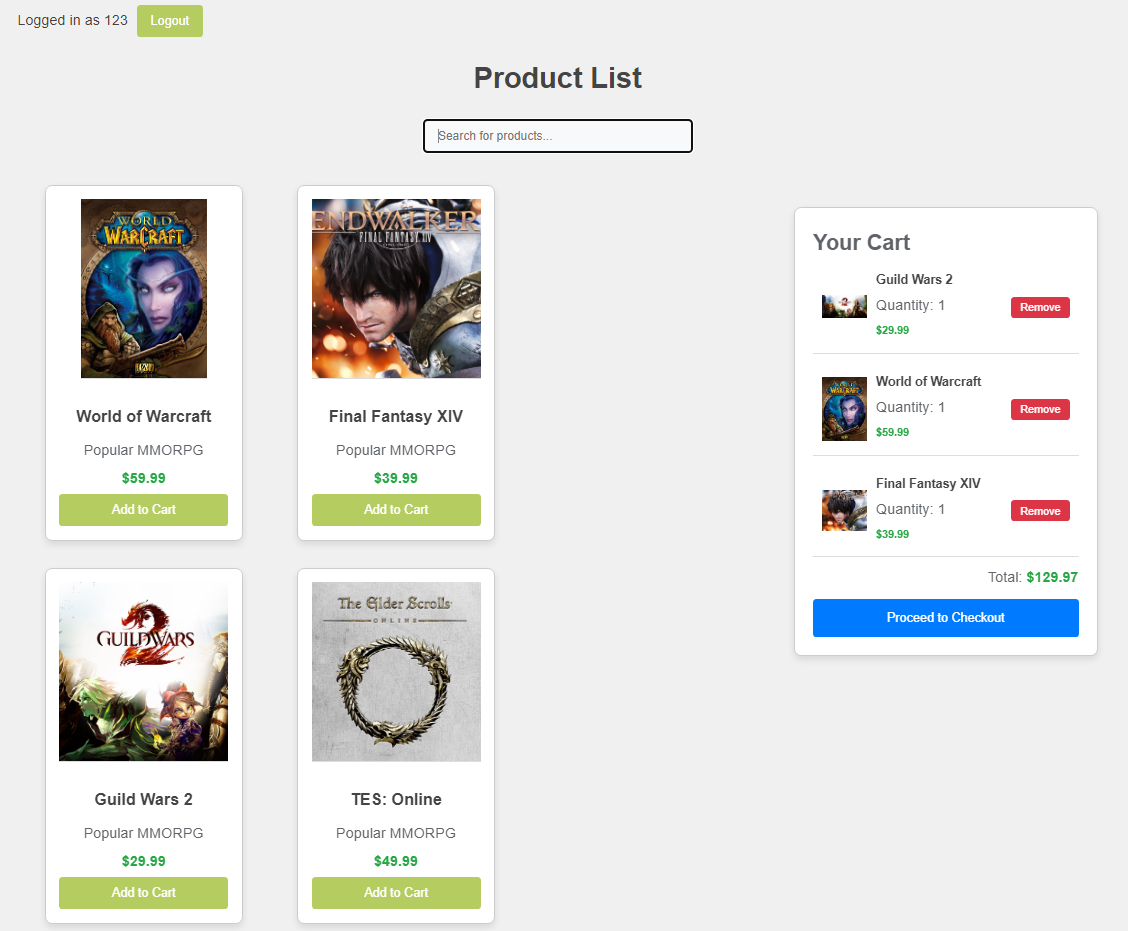
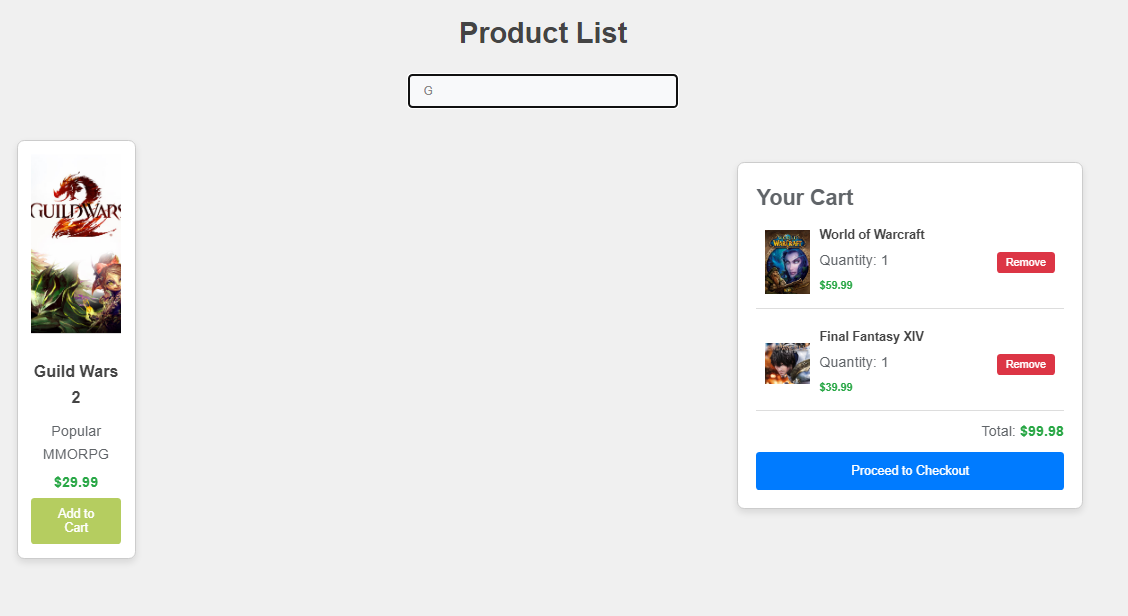
URL: /products/
Description: Displays the product catalogue available to authenticated users. Users can search for products and add them to their cart.
URL: /add_to_cart/<product_id>/
Description: Adds a selected product to the user's shopping cart.
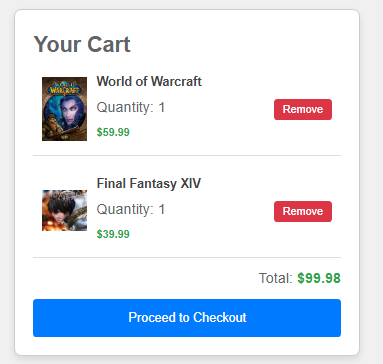
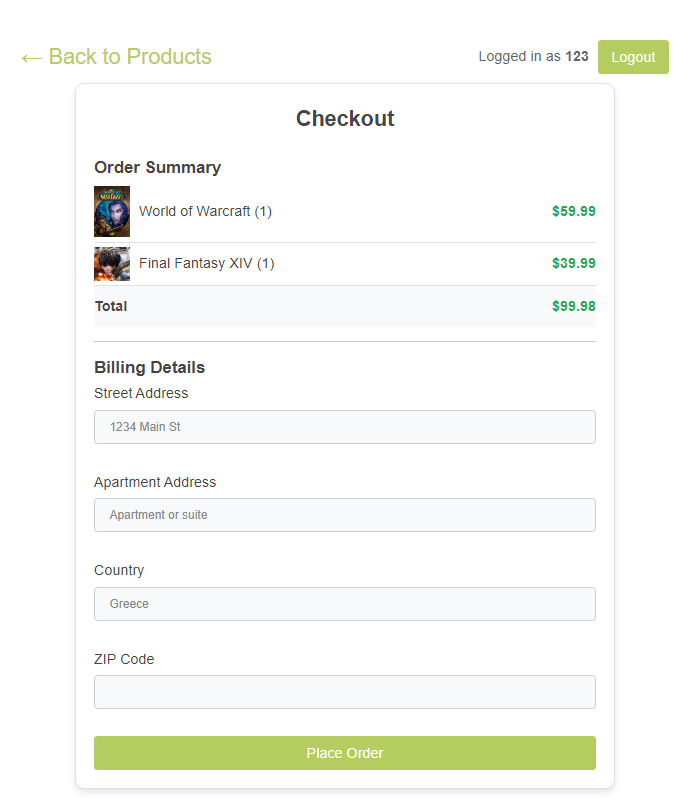
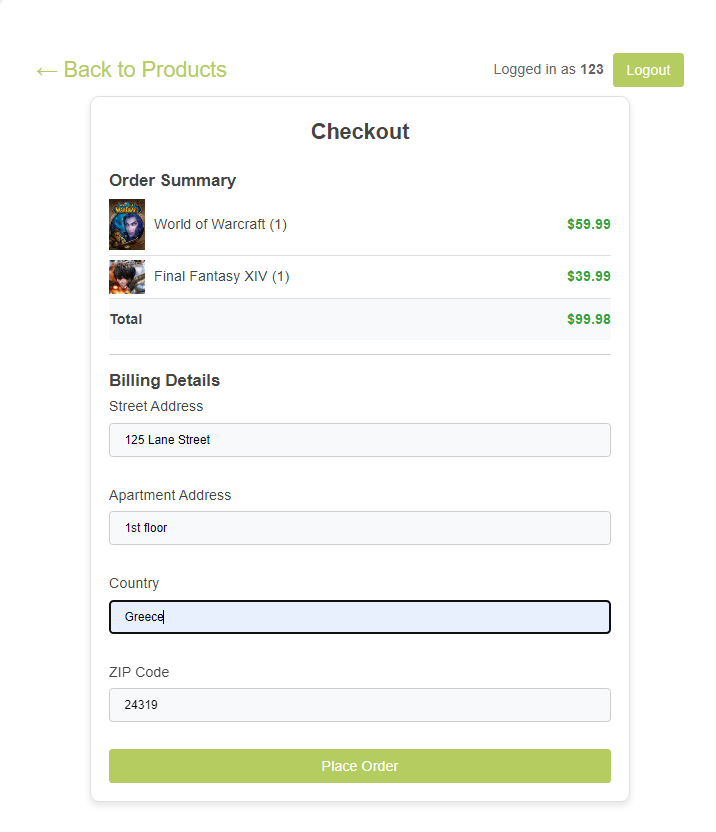
URL: /checkout/
Description: Shows the items in the user's cart and allows them to enter their shipping information. Users can review their order details and submit the order.
URL: /order_summary/
Description: Provides a summary of the user's order before final submission.
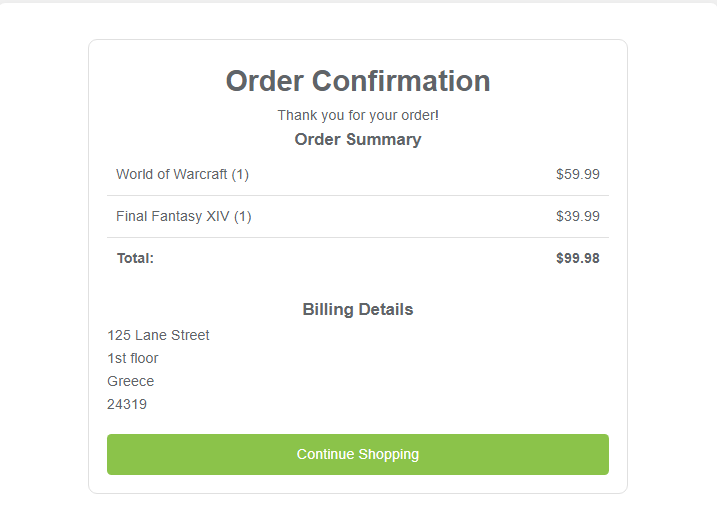
URL: /order_confirmation/
Description: Displays the confirmation of the user's order once it has been successfully placed.
URL: /logout/
Description: Logs the user out and redirects them to the login page.
The e-shop project implements several security features:
- HTTPS Only: All content is available only via HTTPS.
- Secure Cookies: Session and CSRF cookies are configured to be secure.
- CSRF Protection: Cross-Site Request Forgery protection is enabled.
- Rate Limiting: Rate limiting is implemented on login attempts.
- Content Security Policy (CSP): The application has a Content Security Policy to mitigate XSS attacks.
- HSTS: HTTP Strict Transport Security is enforced to ensure all communication is over HTTPS.
- SQL Injection Prevention Mechanisms: Django ORM query operations and other integrated security measures prevent SQL injection.
- HTML Escaping: HTML content is escaped to prevent XSS attacks.
- SameSite Cookies: The SameSite attribute is applied to cookies to prevent CSRF attacks.
- Django Integrated Security Measures: Additional security measures provided by Django to tackle various threats.