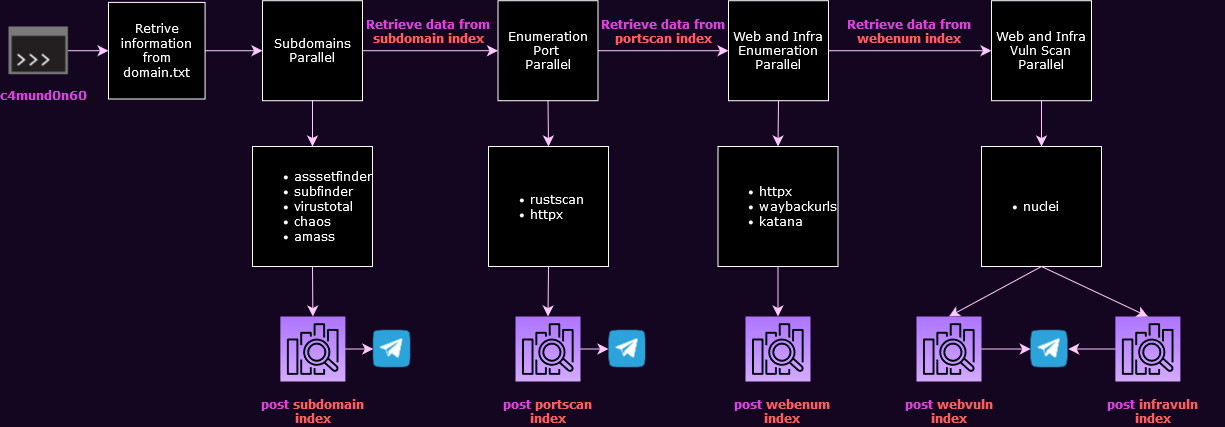
- c4mund0n60 is a tool that use output of known tools for generate smart information about a uniq or multiple domains;
- c4mund0n60 is integrate with Telegram and notify new subdomains finded , open ports and vulnerabilitys automatic.
**Follow this instructions : ** #attachments
git clone https://github.com/CircuitSoul/c4mund0n60
cd c4mund0n60
docker image build -t c4mund0n60-tools:1.0 .
if you want use a pre-deploy Elasticsearch instance, insert: url, user and pass in ./configuration/config.txt
# ELASTIC
ELASTIC_URLBASE: "https://localhost:9200/"
ELASTIC_USER: "user"
ELASTIC_PASS: "pass"
In c4mund0n60 tool folder
docker run -p 9200:9200 -p 9600:9600 -v $(pwd)/configuration/opensearch/data:/usr/share/opensearch/data -e "discovery.type=single-node" --name opensearch-node -d opensearchproject/opensearch:latest
sudo apt install python3 python3-pip parallel
pip3 install -r requirements.txt
# TELEGRAM BOT
TELEGRAM_ApiToken: "<apitoken-key>"
TELEGRAM_chatID: "<chatID-key>"
# ELASTIC
ELASTIC_URLBASE: "https://localhost:9200/"
ELASTIC_USER: "user"
ELASTIC_PASS: "pass"
#VIRUS TOTAL API KEY
VTAPIKEY: "<vtapi-key>"
#CHAOS API KEY
CHAOSKEY: "<chaos-key>"
- To create a telegram bot and get apitoken and chatID, this video is very useful (https://youtu.be/6xfUG8bghCw)
- The default creds for self manage OpenSearch instance is admin:admin (Change is recommended, if you use an VPS)
- Get VTAPIKEY for free: https://www.virustotal.com/gui/join-us
- Get CHAOSAPIKEY for free: https://chaos.projectdiscovery.io
Obs: Grants that your current user can do exec command docker (check your permissions), else exec with sudo
sh initProject.sh <project-name>
sh initProject.sh <project-name> <domains.txt>
python3 main.py <project-name>
python3 main.py <project-name> --delete
Setup Docker Engine (Native Docker) in WSL 2 - Ubuntu
Install need packages
sudo apt update && sudo apt upgrade
sudo apt remove docker docker-engine docker.io containerd runc
sudo apt-get install \
apt-transport-https \
ca-certificates \
curl \
gnupg \
lsb-release
Input docker repository in Ubuntu source list
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo gpg --dearmor -o /usr/share/keyrings/docker-archive-keyring.gpg
echo \
"deb [arch=amd64 signed-by=/usr/share/keyrings/docker-archive-keyring.gpg] https://download.docker.com/linux/ubuntu \
$(lsb_release -cs) stable" | sudo tee /etc/apt/sources.list.d/docker.list > /dev/null
Install docker engine
sudo apt-get update
sudo apt-get install docker-ce docker-ce-cli containerd.io docker-compose-plugin
Give permission for current user
sudo usermod -aG docker $USER
Initialize docker service
sudo service docker start
sudo /etc/init.d/docker start
Setup docker service when WSL initialize insert the follow content in /etc/wsl.conf
[boot]
command="service docker start"
docker command line for view the complete table ‘COMMAND’ of all running containers
for i in $(docker ps --format "table {{.ID}}" | grep -v "CONTAINER ID");do docker inspect $i; done | jq --arg separator $'********' '$separator + .[].Config.WorkingDir, .[].Config.Cmd, .[].Config.Entrypoint' | grep '********'
How to change default password of Opensearch instance
in progress
How to install firewalld and filter all inbound traffic in elasticsearch ports
in progress
- Desec Security (For excelent smart recon course and inspiration for this tool)
- All the contributors of the following repositories
- https://github.com/projectdiscovery/subfinder
- https://github.com/tomnomnom/assetfinder
- https://github.com/chris408/virustotal-subdomain-scraper/
- https://github.com/projectdiscovery/chaos-client
- https://github.com/RustScan/RustScan
- https://github.com/projectdiscovery/httpx
- https://github.com/tomnomnom/waybackurls
- https://github.com/projectdiscovery/katana
- https://github.com/projectdiscovery/nuclei
- https://github.com/0xPugazh/One-Liners
- Implement quick subdomain takeover verification
cat subs.txt | xargs -P 50 -I % bash -c "dig % | grep CNAME" | awk '{print $1}' | sed 's/.$//g' | httpx -silent -status-code -cdn -csp-probe -tls-probe - Implement cariddi tool (https://github.com/edoardottt/cariddi).
- Implement a mecanism that get a list of root domains from a CIDR block (https://twitter.com/hakluke/status/1665931596631875584).
- Implement regex analysis in JS files for search users, passwords and secrets things (https://adityashende17.medium.com/how-to-js-for-bug-bounties-edition-2023-7108b56d9db6).
- Implement crackmapexec for brute force services and another things.
- Implement https://community.riskiq.com/ for more enumeration subdomains.
- Implement enumeration from BufferOver.run
curl -s https://dns.bufferover.run/dns?q=.target.com | jq -r .FDNS_A[] | cut -d',' -f2 | sort -u - Implement enumeration from Riddler.io
curl -s "https://riddler.io/search/exportcsv?q=pld:target.com" | grep -Po "(([\w.-]*)\.([\w]*)\.([A-z]))\w+" | sort -u - Implement enumeration from CertSpotter
curl -s "https://certspotter.com/api/v1/issuances?domain=target.com&include_subdomains=true&expand=dns_names" | jq .[].dns_names | grep -Po "(([\w.-]*)\.([\w]*)\.([A-z]))\w+" | sort -u - Implement enumeration from AlienVault
curl -s "https://otx.alienvault.com/api/v1/indicators/domain/tesla.com/url_list?limit=100&page=1" | grep -o '"hostname": *"[^"]*' | sed 's/"hostname": "//' | sort -u - Create OSINT index and implement mecanism/tools that retrieve infos like emails, usernames, buckets, social midia profiles, github repos, files: docx, pdf, mp4, etc.
- Implement dork google search with Google CSE (Custom Search Engine) (https://github.com/AssassinUKG/googleSearcher).
- Implement Linkedint (https://github.com/vysecurity/LinkedInt) MAYBE
- Implement urlscan.io.
- Implement search.censys.io or use tools like sublist3r/amass for this.
- Implement SSL Certificates extration and DNS Names from ASN. (https://twitter.com/pdnuclei/status/1676184515021029377).
- Implement nrich tool (https://asciinema.org/a/468923).
- Implement BucketLoot (https://github.com/redhuntlabs/BucketLoot)
- Reasearch a way for smaller execution time of amass
- Use of the -passive and -timeout argument
- Implement support a config files for the known tools used in c4mund0n60. e.g.
amass subcommand -config config.yaml. This config.yaml can be found in ./configuration/tools/ folder. - Create a mecanism that identify and ignore (don't do any enumeration) of IP's , Netblocks and CIDR from CloudFlare, Akamai, CDN's , etc.
- Add tutorial How to change default password of Opensearch instance
- Add tutorial How to install firewalld and filter all inbound traffic in elasticsearch ports
- Decrease the size of the docker image