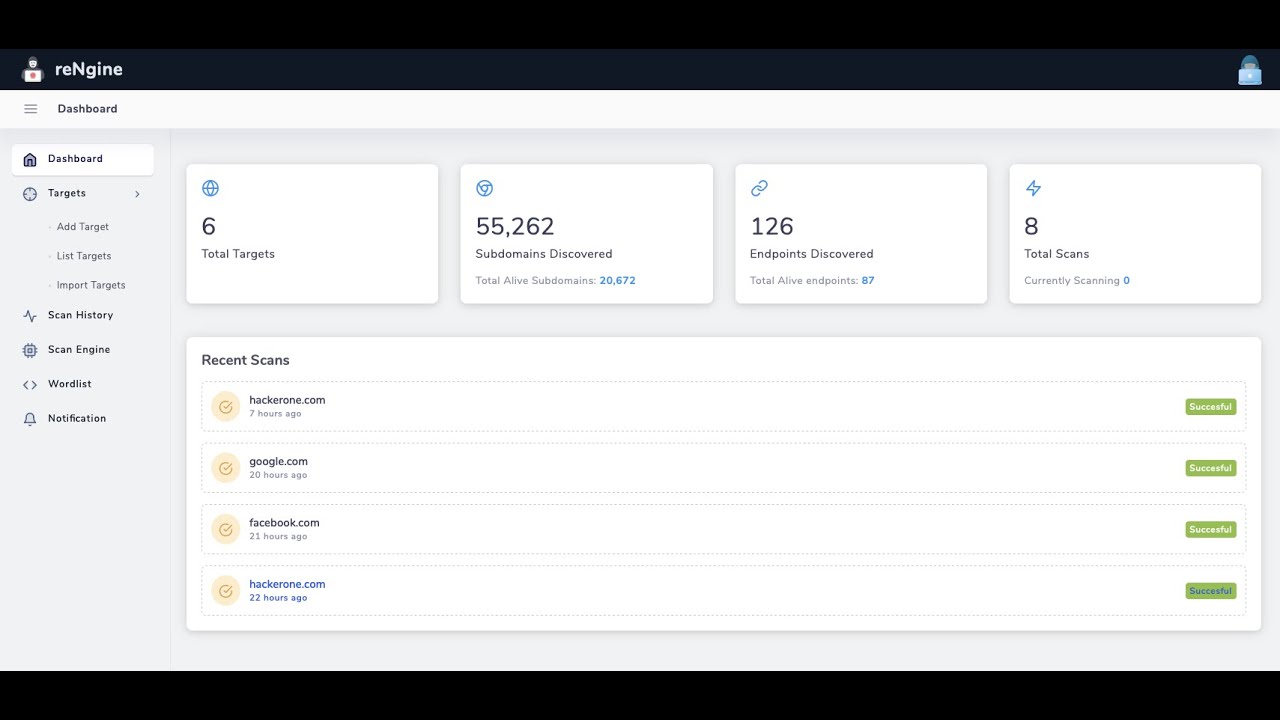
An automated recon framework for web applications
reNgine Documentation
.
What's new
·
Contribute
·
Report Bug
·
Request Feature
reNgine official documentation has been released. All the installation instructions and other information regarding reNgine has been documented at https://rengine.wiki
reNgine is an automated reconnaissance framework meant for information gathering during penetration testing of web applications. reNgine has customizable scan engines, which can be used to scan the domains, endpoints, or gather information. The beauty of reNgine is that it gathers everything in one place. It has a pipeline of reconnaissance, which is highly customizable.
reNgine can be very useful when you want to perform the reconnaissance, gather endpoints, directory and file search, grab screenshots, and gather all the results in one place.
Suppose, if you have a domain hackerone.com, reNgine can perform the scan based on your scan engines, gather all the results in one place. reNgine makes it possible for use cases like, "I want to search the subdomain which has page title "Dashboard" and has page status as 200, and I quickly want to have a look at the screenshot".
Another use-case could be, "I want to list all subdomains that use PHP, and the HTTP status is 200!"
On the endpoints part, reNgine is capable of gathering the URL endpoints using tools like gau, hakrawler which gathers URL from many sources like common crawl, Wayback engine, etc.
reNgine also makes it possible for the use case like, "search the URLs that have extension .php and HTTP status is 200!"
Assume that, you are looking for open redirection, you can quickly search for =http and look for HTTP status 30X, this will give high accuracy of open redirection with minimal efforts.
Click below to watch the demo
- Vulnerability Scan using Nuclei, Subdomain Discovery, Ports Discovery, Endpoints Discovery, Directory Bruteforce, Visual Reconnaissance (Screenshot the targets)
- IP Discovery, CNAME discovery, Subdomain Takeover Scan
- Highly configurable scan engines
- Run multiple scans in parallel
- Run Clocked Scans (Run reconnaissance exactly at X Hours and Y minutes)
- Run Periodic Scans (Runs reconnaissance every X minutes/hours/days/week)
- Advanced lookup in Recon Results
reNgine is not a:
- Reconnaissance with high accuracy (No! reNgine, uses other open-source tools, to make this pipeline possible. The accuracy and capability of reNgine is also dependent on those tools)
- Speed oriented recon framework with immediate results
Of course, at this point, reNgine does not give the best of the best result compared to other tools, but reNgine has certainly minimal efforts. Also, I am continuously adding new features. You may help me on this journey by creating a PR filled with new features and bug fixes. Please have a look at the Contributing section before doing so.
All the installation instructions have been moved to wiki documentation. Find the wiki documentation here https://rengine.wiki
Contributions are what make the open-source community such an amazing place to learn, inspire, and create. Any contributions you make are greatly appreciated. Your contributions could be as simple as fixing the indentations or fixing UI to as complex as bringing new modules and features.
See contributing guide to get started.
Please note that reNgine is beginner-friendly. If you have never done any open-source yet, we encourage you to do so. We will be happy and proud of your first PR ever.
You can begin with resolving any open issues.
It is distributed under the GNU GPL v3 license License. See LICENSE for more information.
reNgine is just a pipeline of recon. reNgine would not have been possible without the following individuals/organizations.
- Amass: OWASP
- httpx, subfinder, naabu: ProjectDiscovery
- Sublist3r: Ahmed Aboul-Ela
- assetfinder: Tom Hudson
- gau: Corben Leo
- hakrawler : Luke Stephens
- dirsearch: maurosoria
- subjack haccer
Also, some of the icons and images used herein reNgine are from Freepik and Flaticon.