A GitHub Action for running the ZAP Baseline scan to find vulnerabilities in your web application.
The ZAP baseline action scans a target URL for vulnerabilities and maintains an issue in GitHub repository for the identified alerts. Read the following blog post for additional information.
Required The URL of the web application to be scanned. This can be either a publicly available web application or a locally accessible URL.
Optional The name of the docker file to be executed. By default the action runs the stable version of ZAP. But you can configure the parameter to use the weekly builds.
Optional You can also specify a relative path to the rules file to ignore any alerts from the ZAP scan. Make sure to create the rules file inside the relevant repository. The following shows a sample rules file configuration. Make sure to checkout the repository (actions/checkout@v2) to provide the ZAP rules to the scan action.
10011 IGNORE (Cookie Without Secure Flag)
10015 IGNORE (Incomplete or No Cache-control and Pragma HTTP Header Set)Optional Additional command lines options for the baseline script
Optional By default the baseline action will file the report to the GitHub issue using the issue_title input.
Set this to false if you don't want the issue to be created or updated.
Optional The title for the GitHub issue to be created
Optional ZAP action uses the default action token provided by GitHub to create and update the issue for the baseline scan.
You do not have to create a dedicated token. Make sure to use the GitHub's default action token when running the action(secrets.GITHUB_TOKEN).
Optional By default ZAP Docker container will fail with an exit code,
if it identifies any alerts. Set this option to true if you want to fail the status of the GitHub Scan if ZAP identifies any alerts during the scan.
Optional By default the baseline action will attach the report to the build with the name zap_scan. Set this to a different string to name it something else. Consult GitHub's documentation for which artifact names are allowed.
If set, the following ZAP authentication environment variables will be copied into the docker container:
ZAP_AUTH_HEADER_VALUEZAP_AUTH_HEADERZAP_AUTH_HEADER_SITE
** Basic **
steps:
- name: ZAP Scan
uses: zaproxy/action-baseline@v0.12.0
with:
target: 'https://www.zaproxy.org'
** Advanced **
on: [push]
jobs:
zap_scan:
runs-on: ubuntu-latest
name: Scan the webapplication
steps:
- name: Checkout
uses: actions/checkout@v2
with:
ref: master
- name: ZAP Scan
uses: zaproxy/action-baseline@v0.12.0
with:
token: ${{ secrets.GITHUB_TOKEN }}
docker_name: 'ghcr.io/zaproxy/zaproxy:stable'
target: 'https://www.zaproxy.org'
rules_file_name: '.zap/rules.tsv'
cmd_options: '-a'
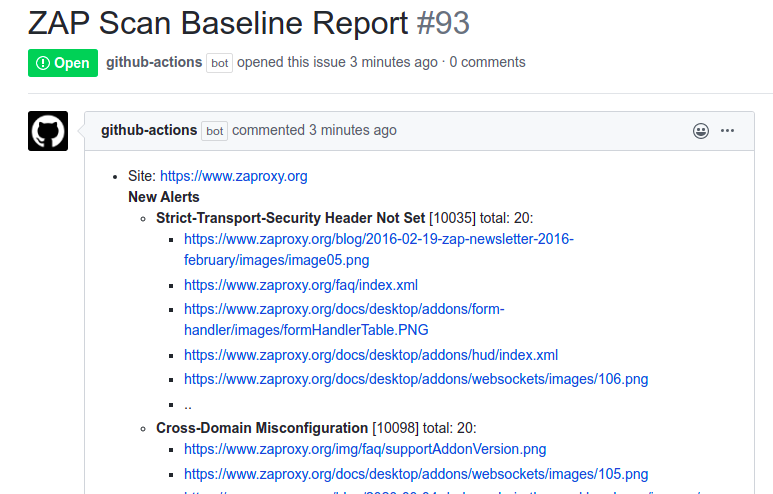
The following issue shows how the GitHub Baseline Action scans the https://www.zaproxy.org/ website and notifies the users via opening an issue in the ZAP website repository. The issue will be created by the GitHub Actions bot and will list the alerts as issue comments.
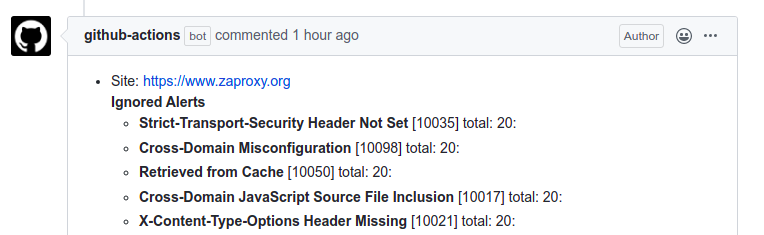
To demonstrate the workflow of the action; we are ignoring the alerts as they are not relevant, but this has the same effect as fixing them.
Therefore during the second scan we are ignoring few alerts via ZAP rules and the action bot updates the issue with the newly ignored/resolved alerts.
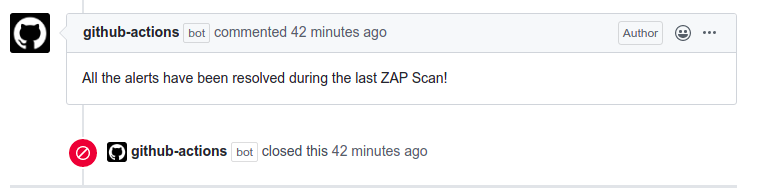
During the last scan we are ignoring all the alerts, thus resulting in finding zero alerts. Based on the scan results
the actions bot will close the ongoing open issue.
ZAP is internationalised and alert information is available in many languages.
You can change the language used by this action by changing the locale via the cmd_options e.g.: -z "-config view.locale=fr_FR"
See https://github.com/zaproxy/zaproxy/tree/main/zap/src/main/dist/lang for the full set of locales currently supported.
You can help improve ZAP translations via https://crowdin.com/project/zaproxy.