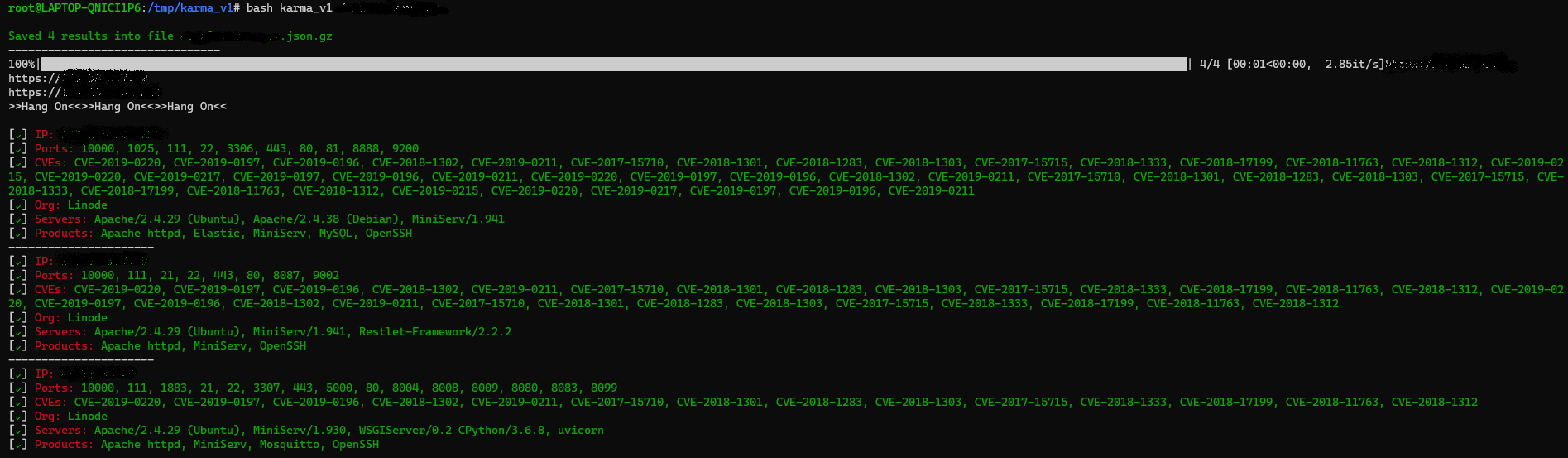
KARMA_v1 is a simple bash script automation that can talk to Shodan Premium API and find active IPs, ASN, Common Vulnerabilities, CVEs & Open Ports, Products, Hostname, Server Details.
- Powerful and flexible results via Shodan Dorks
- SSL SHA1 checksum/fingerprint Search
- Only hit In-Scope IPs
- Verify each IP with SSL/TLS certificate issuer match RegEx
- Find out all ports including well known/uncommon
- Grab all targets vulnerabilities related to CVEs
- Banner grab for each IP & Product
Its (karma_v1) a bit slow due to shodan API rate limit.
# git clone https://github.com/Dheerajmadhukar/karma_v1.git# pip3 install shodan# apt install jq -y4. Install httpx @pdiscoveryio to probe the requests
# GO111MODULE=on go get -v github.com/projectdiscovery/httpx/cmd/httpx5. Install Interlace @codingo to multithread [Follow the codingo interlace repo instructions]
Clone https://github.com/codingo/Interlace.git & install accordingly. # cat > .token
SHODAN_PREMIUM_API_HERE# bash karma_v1 target.tld
Output will be saved in output/target.tld-YYY-MM-DD directorySome example usage:
# bash karma_v1 target.tld- shodan python module [ pip3 install shodan ]
- anew @tomnomnom
- jq [ apt install jq -y ]
- httpx @pdiscoveryio
- Interlace @codingo