Compatible with node 10+ (tested with node 10 -> 14)
$ npm install -g sonar-report- See all options with:
$ sonar-report --help
SYNOPSIS
sonar-report [OPTION]...
-
Environment:
- http_proxy : the proxy to use to reach the sonarqube instance (
http://<host>:<port>) - NODE_EXTRA_CA_CERTS
- the custom certificate authority to trust (troubleshoots
Unable to verify the first certificate) - the variable holds a file name that contains the certificate in pem format (root CA or full trust chain)
- the custom certificate authority to trust (troubleshoots
- http_proxy : the proxy to use to reach the sonarqube instance (
-
Example:
# Generate report example
sonar-report \
--sonarurl="https://sonarcloud.io" \
--sonarcomponent="sopra-steria:soprasteria_sonar-report" \
--project="Sonar Report" \
--application="sonar-report" \
--release="1.0.0" \
--branch="feature/branch" \
--sinceleakperiod="false" \
--allbugs="false" > /tmp/sonar-report_sonar-report.html
# Open in browser
xdg-open /tmp/sonar-report_sonar-report.htmlThe sinceleakperiod parameter activates delta analysis. If true, sonar-report will only get the vulnerabilities that were added since a fixed date/version or for a number of days. For this it will:
- get
sonar.leak.periodvalue using sonar settings API. - filter accordingly when getting the issues using the issues API.
When sinceleakperiod is activated, the report will include an additional Reference period field that holds the leak period configured in SonarQube.
More info:
- Sonar documentation
- In sonarQube, /settings : see leak period
- "false": only vulnerabilities are exported
- "true": all bugs are exported
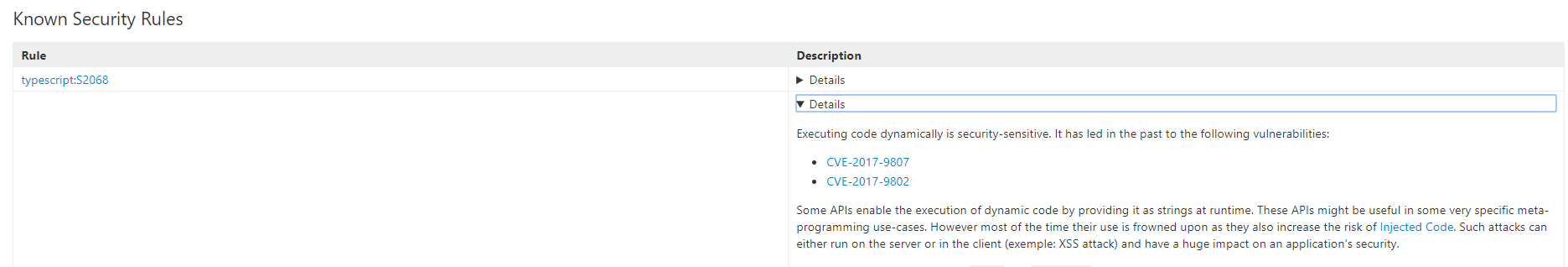
On some versions of sonar (found on 6.5), the type of issue and the type of the rule don't match (for example VULNERABILITY vs CODE_SMELL ).
In this case, when allbugs=false, it's possible that the issue is extracted but not it's rule. What will happen is that the issue has / in the description (because the description is the name of the rule).
To circumvent this issue, the fixMissingRule will extract all rules without any filter on the type.
Beware that, with this parameter activated, all the issues linked to the rules displayed may not be displayed.
Set this flag to true if using a sonarQube version that doesn't support security hotspots (<7.3?)
Get the dependencies:
npm installRun with the same command as Use but use node index.js instead of sonar-report
- The description is "/"
Set fixMissingRule to true
- Error "Value of parameter 'types' (SECURITY_HOTSPOT) must be one of: [CODE_SMELL, BUG, VULNERABILITY]"}]}
Your version of sonarQube doesn't support security hotspots. Set noSecurityHotspot to true.
- {"errors":[{"msg":"Can return only the first 10000 results. 10500th result asked."}]}
This is a limitation in sonarQube API. There is no way around it to date apart from adding limiting filters
Try removing --allbugs=true or tune the query in index.js (see /web_api/api/issues under your sonarQube instance)
See also this discussion https://community.sonarsource.com/t/cannot-get-more-than-10000-results-through-web-api/3662/4