Make exploiting race conditions in web applications highly efficient and ease-of-use.
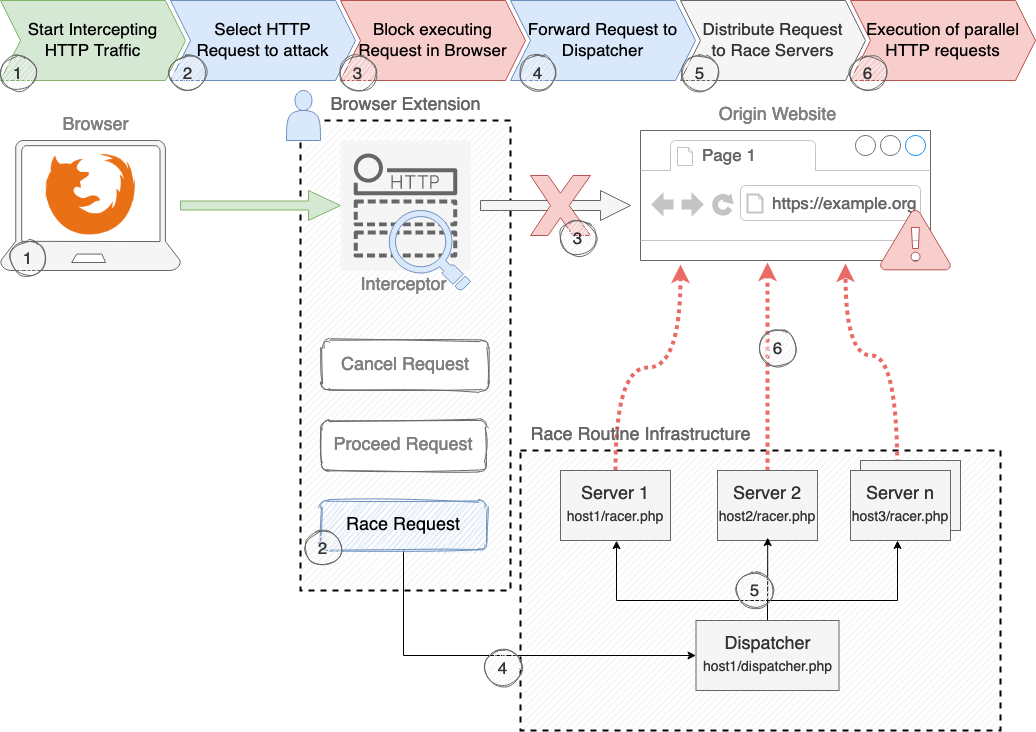
Firefox browser extension for live request monitoring and intercepting the desired request which will be forwarded to the Race Dispatcher.
Race Dispatcher and Race Script to execute parallel requests against any given endpoint.
ZAP Extensions to test for Race Conditions.
A web application with typical vulnerable use cases such as withdrawing money or excessive poll votes.
A demo of the tool and a introduction to race condition vulnerabililties can be watched in this video, which got recorded at Hack in the Box Conference (HITBSecConf) 2022 Singapore:
In addition a PDF of the research can be found here (in German).
The following action items are considered to be implemented in a future version (happy for any contributions!):
- Improve timing (by using ntp, a websocket push, or anything else) of the race server to decrease the time gap between dispatching to multiple race servers OR allow a scheduled timing option
- Allow downloading of the HTTP-Responses to analyse the success of the attack
- Allow multiple, different parameters/content of the HTTP-Request to allow improved exploitation of load balancers with sticky sessions and other attack szenarios that require custom parameters
Code of Raceocat is licensed under the Apache License 2.0.
Feel free to open issues / pull requests if you want to contribute to this project.
You can reach me on Twitter @javanrasokat.