The latest update to owlsector.bungie.net includes a link that proceeds to give you a data transmission.
A very crafty reddit user beat me to the punch, and managed to decrypt the base64 encoded data of some of the messages, by matching the forwarding protocols to find a full message chunck. (See: Message Decoded for the new ARG)
- reddit is currently under the impression that the images are a map
- I believe the images are only part of the message, like a QR code, there is text data embedded in the unprocessed information
The clues I describe below have largely been unidentified, missed, or dismissed by the community. This is partially my fault, as I have been throwing comments at reddit after staying up for 20 hours straight, and my ramblings seem like nonsense.
I believe detailing the clues in this manner will help to rectify my ramblings, and together help the community unlock the next step:
- Nodes have names consisting of 4 different UTF-8 characters:
- Each character is actually an 8-bit hex code:
- Each node name, when translated to Hex, is a 32 bit Hex
- 32 bit hex happens to be the base block size factor for Rijndael (pronounced Rine-dahl) encryption keys
- Rijndael-AES-CBC is a symmetric encryption algorithm that uses the same key to both encrypt and decrypt a message
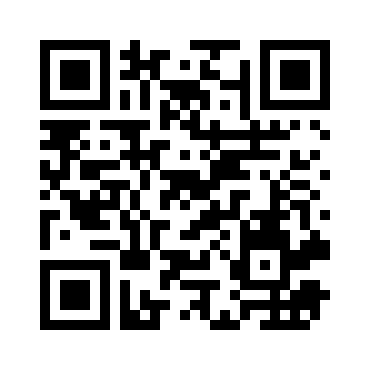
- text can be embedded in images. For an excellent example of this, just take a photo of this QR code from any QR reader on your mobile device, or upload the QR code below here: ZXing Decoder Online
- I've noticed a pattern in the HEX-formatted names of the nodes... many Nodes have the same 32 bit block, even though their names are different
- cyptographic keys contain randomart images used to easily identify various keys by the naked eye
Example Image with Data embedded (QR code)
reddit user /r/thegrayfox89 unknowingly (IMHO) gave us a few hints of hist own in his post Message Decoded for the new ARG:
- He mentions that he specifically looked to output JPEG data, and mentioned that there was other data that was either "garbage data", or data in a format he couldn't recognize
- He mentions self-referencing nodes. If this was purely image data, it wouldn't make sense for a base64 decryption of a JPEG to have any matching buffers... especially buffers of such an immense size
- it does make sense however, if some of the data within is text, and the message has non-unique words or phrases, or repeating patterns.
The Images Together contain embedded data (It's a QR code) This theory stipulates that the node names (once translated to hex)and the key sequences used together show you how to assemble the 8 images. On e assembled, the images actually are a QR code.
This theory is that the images are just verification keys for the message that is embedded in the data. The node names (again translated to hex) are the public keys for the text data, and the images are the private keys. Used together you can decrypt the text contained within. The processing key is either a salt, a filtering mechanism for filtering image data from text data, or is a partial initilization vector that must be pieced together using the forwarding protocol
Using the info below I've begun to write code to translate node names into hex key's, using the google-spreadsheets npm package, by consuming the data houseed in this spreadsheet , which is entered using this form
| Character | Character Name | 8-BIT Hex Code |
|---|---|---|
| ▼ | BLACK DOWN POINTING TRIANGLE | e296bc |
| ♦ | BLACK DIAMOND SUIT | e299a6 |
| ■ | BLACK SQUARE | e296a0 |
| ● | BLACK CIRCLE | e2978f |
All coders, of any expertise, are welcome to particpate or contribute PR's. To help code, make sure you have latest npm, and then:
git clone git@github.com:LongLiveCHIEF/fifth-monitor.git
npm install
