An AWS tags checking tool that can be used to look for untagged resources, missing tags, resources with too many tags, and more.
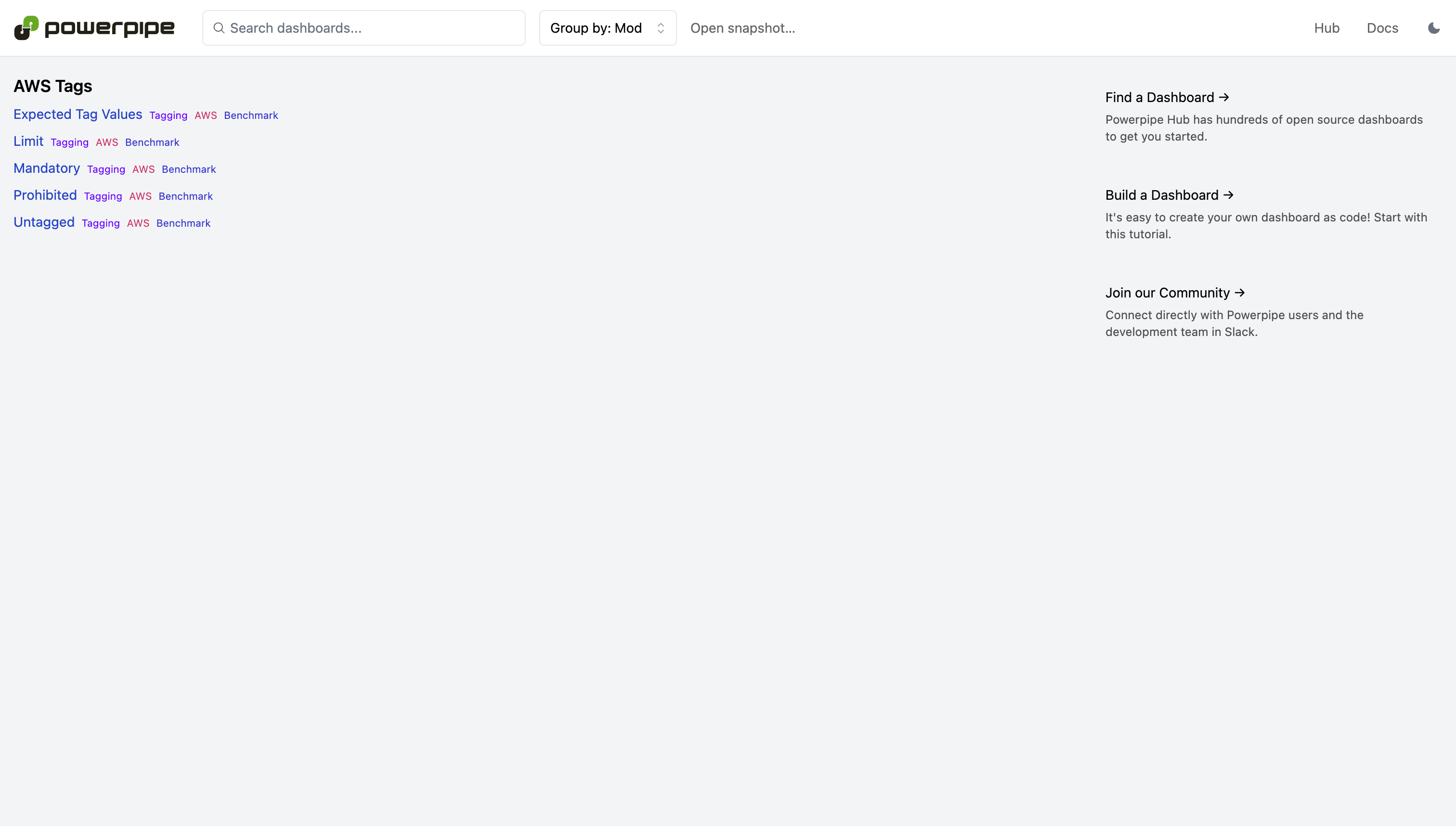
Run checks in a dashboard:
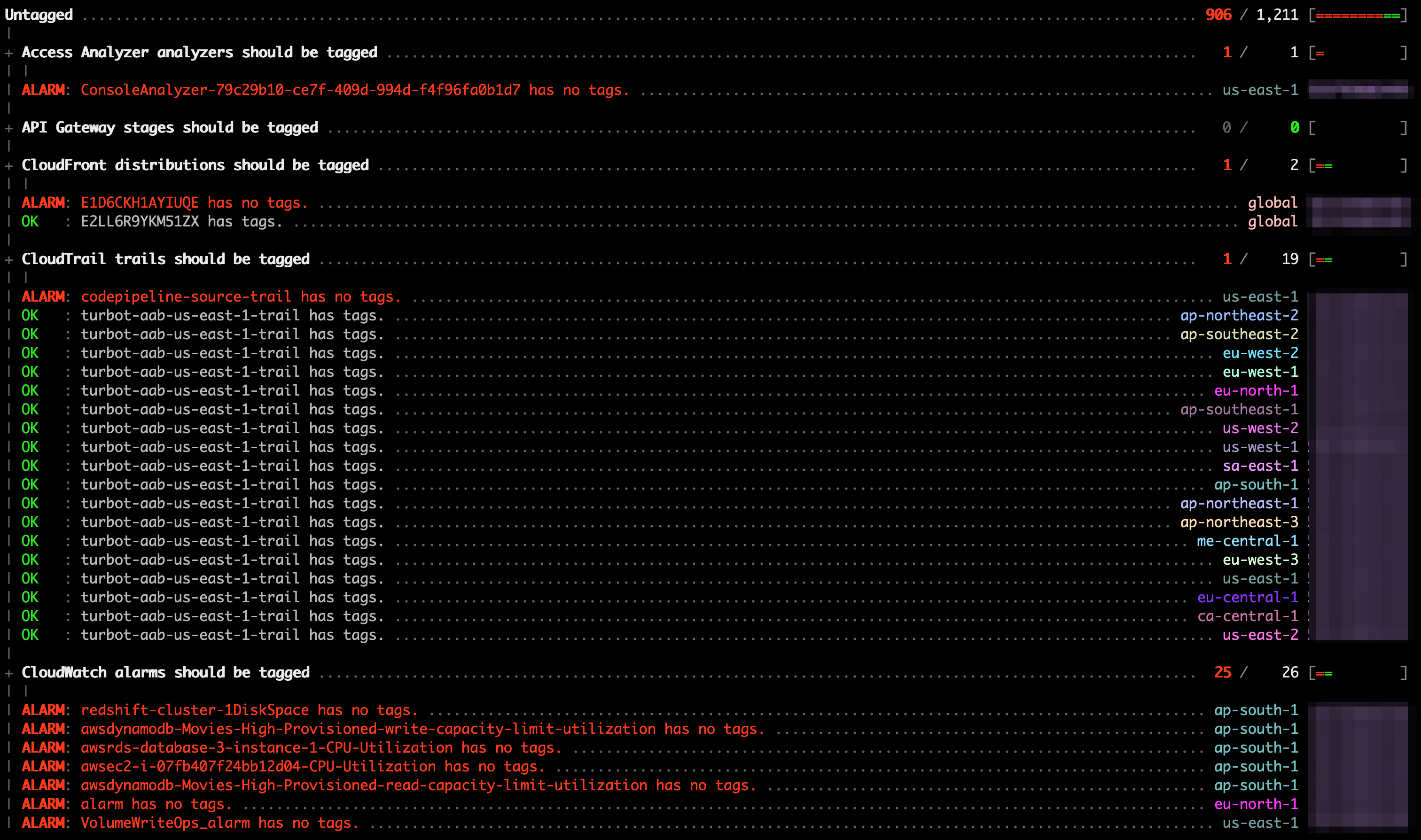
Or in a terminal:
Download and install Steampipe (https://steampipe.io/downloads). Or use Brew:
brew tap turbot/tap
brew install steampipeInstall the AWS plugin with Steampipe:
steampipe plugin install awsClone:
git clone https://github.com/turbot/steampipe-mod-aws-tags.git
cd steampipe-mod-aws-tagsStart your dashboard server to get started:
steampipe dashboardBy default, the dashboard interface will then be launched in a new browser window at https://localhost:9194. From here, you can run benchmarks by selecting one or searching for a specific one.
Instead of running benchmarks in a dashboard, you can also run them within your
terminal with the steampipe check command:
Run all benchmarks:
steampipe check allRun a single benchmark:
steampipe check benchmark.untaggedRun a specific control:
steampipe check control.s3_bucket_untaggedDifferent output formats are also available, for more information please see Output Formats.
This mod uses the credentials configured in the Steampipe AWS plugin.
Several benchmarks have input variables that can be configured to better match your environment and requirements. Each variable has a default defined in its source file, e.g., controls/limit.sp, but these can be overriden in several ways:
- Copy and rename the
steampipe.spvars.examplefile tosteampipe.spvars, and then modify the variable values inside that file - Pass in a value on the command line:
steampipe check benchmark.mandatory --var 'mandatory_tags=["Application", "Environment", "Department", "Owner"]' - Set an environment variable:
SP_VAR_mandatory_tags='["Application", "Environment", "Department", "Owner"]' steampipe check control.ec2_instance_mandatory- Note: When using environment variables, if the variable is defined in
steampipe.spvarsor passed in through the command line, either of those will take precedence over the environment variable value. For more information on variable definition precedence, please see the link below.
- Note: When using environment variables, if the variable is defined in
These are only some of the ways you can set variables. For a full list, please see Passing Input Variables.
Using the control output and the AWS CLI, you can remediate various tagging issues.
For instance, with the results of the ec2_instance_mandatory control, you can add missing tags with the AWS CLI:
#!/bin/bash
OLDIFS=$IFS
IFS='#'
INPUT=$(steampipe check control.ec2_instance_mandatory --var 'mandatory_tags=["Application"]' --output csv --header=false --separator '#' | grep 'alarm')
[ -z "$INPUT" ] && { echo "No instances in alarm, aborting"; exit 0; }
while read -r group_id title description control_id control_title control_description reason resource status account_id region
do
aws resourcegroupstaggingapi tag-resources --region ${region} --resource-arn-list ${resource} --tags Application=MyApplication
done <<< "$INPUT"
IFS=$OLDIFSTo remove prohibited tags from EC2 instances:
#!/bin/bash
OLDIFS=$IFS
IFS='#'
INPUT=$(steampipe check control.ec2_instance_prohibited --var 'prohibited_tags=["Password"]' --output csv --header=false --separator '#' | grep 'alarm')
[ -z "$INPUT" ] && { echo "No instances in alarm, aborting"; exit 0; }
while read -r group_id title description control_id control_title control_description reason resource status account_id region
do
aws resourcegroupstaggingapi untag-resources --region ${region} --resource-arn-list ${resource} --tag-keys Password
done <<< "$INPUT"
IFS=$OLDIFSIf you have an idea for additional controls or just want to help maintain and extend this mod (or others) we would love you to join the community and start contributing.
- Join our Slack community → and hang out with other Mod developers.
Please see the contribution guidelines and our code of conduct. All contributions are subject to the Apache 2.0 open source license.
Want to help but not sure where to start? Pick up one of the help wanted issues: