Discover, assess and mitigate known vulnerabilities in your Java and Python projects.
The open-source vulnerability assessment tool supports software development organizations in regards to the secure use of open-source components during application development. The tool analyzes Java and Python applications in order to
- detect whether they depend on open-source components with known vulnerabilities,
- collect evidence regarding the execution of vulnerable code in a given application context (through the combination of static and dynamic analysis techniques), and
- support developers in the mitigation of such dependencies.
As such, it addresses the OWASP Top 10 security risk A9, Using Components with Known Vulnerabilities, which is often the root cause of data breaches [1].
In comparison to other tools, the detection is code-centric and usage-based, which allows for more accurate detection and assessment than tools relying on meta-data. It is a collection of client-side scan tools, RESTful microservices and rich OpenUI5 Web frontends.
Read more in our Docs
Originally developed by SAP Security Research [2][3], the tool has become the officially recommended open-source scan tool for Java applications at SAP. Since the beginning of 2017, it has been used to perform 20K+ scans of more than 600+ Java development projects.
The tool approach is best described in the following scientific papers, please cite these if you use the tool for your research work:
- Serena Ponta, Henrik Plate, Antonino Sabetta, Beyond Metadata: Code-centric and Usage-based Analysis of Known Vulnerabilities in Open-source Software, 34th International Conference on Software Maintenance and Evolution (ICSME), 2018
- Henrik Plate, Serena Ponta, Antonino Sabetta, Impact Assessment for Vulnerabilities in Open-Source Software Libraries, 31st International Conference on Software Maintenance and Evolution (ICSME), 2015
In the following a couple of example features:
- Detection of vulnerable code is realized by discovering method signatures in Java archives and comparing their source and byte code with the vulnerable and fixed version (as known from the fix commit). As such, the detection is more accurate than for approaches based on meta-data (less false-positives and false-negatives). In particular, it is robust against rebundling, a very common practice in the Java ecosystem.
- Assessment of vulnerable dependencies by application developers and security experts is supported by information about the potential and actual execution of vulnerable code. This information is based on call graph analysis and trace information collected during JUnit and integration tests. Going down to the granularity of single methods, application developers are presented with the potential and actual call stack from application code till vulnerable code.
- The addition of new vulnerabilities to the knowledge base does not require the re-scan of applications. In other words, right after an addition to the knowledge base, it is immediately known whether previously scanned applications are affected or not.
- Mitigation proposals consider the reachable share of dependencies, i.e., the set of methods that can be potentially reached from application code union the actual executions observed during tests. This information is used to compute several metrics aiming to let developers chose the best non-vulnerable replacement of a vulnerable dependency (best in regards to non-breaking and with least regression likelihood).
- Individual findings can be exempted if developers come to the conclusion that a vulnerability cannot be exploited in a given application-context. This information can be maintained in an auditable fashion (incl. timestamp and author information) and typically prevents build exceptions during CI/CD pipelines.
- Organization-internal CERTs can query for all applications affected by a given vulnerability. This feature supports, for instance, larger development organizations with many software applications developed by distributed and de-central development units.
Visit the Wiki in order to get a better understanding of the various features and the Web frontends.
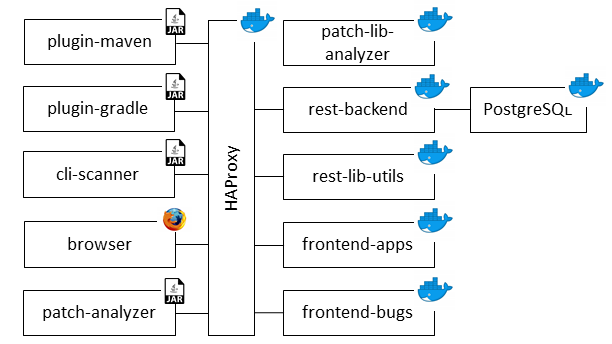
The open-source vulnerability assessment tool has a distributed architecture composed of a couple of Spring Boot microservices, two Web frontends and a number of client-side scanners/plugins, which perform the actual analysis of application and dependency code on build systems or developer workstations.
You need Docker
- to build all artifacts and
- operate the various server-side components.
You need the Java 8 JRE and the following to run the various client-side scanners/plugins:
- Maven 3.3+ for the analysis of Maven projects using the
plugin-maven, - Python 3 as well as the packages pip, virtualenv and setuptools (
pip install <name>) for the analysis of Python applications using thecli-scanner, and - Gradle 4 for the analysis of Gradle projects using the
plugin-gradle.
For your convenience, you can use Docker to build and run the open-source vulnerability assessment tool on your own in a few easy steps. Detailed instructions are available here.
Even though the default configuration works out of the box, you may want to configure the various components to adapt the tool to your needs and organization. See below for a some examples and refer to the Wiki for detailed configuration instructions.
The client-side scan tools (plugin-maven, plugin-gradle, cli-scanner) can be configured to integrate and align with organization-specific development and security policies. For instance, it is configurable whether build exceptions are thrown as soon as dependencies with vulnerable code exist, or only if the execution of such vulnerable code is observed during JUnit or integration tests.
The microservices and Web frontends can be configured to integrate with an organization-specific build and development infrastructure. For instance, private Nexus or PyPI repositories can be configured to provide information about non-public components.
The tool was originally built to manage publicly known vulnerabilities in open-source components, however, the knowledge base can also (in parallel) comprise non-public vulnerabilities. This possibility is particularly useful for larger development organizations with many internal re-use components. As for open-source components, thanks to the integration with private Nexus and PyPI repositories, the tool can suggest the latest non-vulnerable version of such internal re-use components.
Important: Due to the current lack of an authentication and authorization mechanism, it is NOT recommended to run the Web frontends and server-side microservices on systems accessible from the Internet.
Other limitations:
- Static and dynamic analyses are not implemented for Python
- Static analysis for Java is only supported until Java 8
- Java 9 multi-release archives are not supported (classes below
META-INF/versionsare simply ignored)
The list of current issues is available here
Use the following link to Stack Overflow to search for FAQs or to request help.
Bug reports shall be submitted as GitHub issues, please refer to the next section for more details.
Our aim is to build a lively community, hence, we welcome any exchange and collaboration with individuals and organizations interested in the use, support and extension of the open-source vulnerability assessment tool.
Please read this document to read more about your options:
- Help Others on Stack Overflow
- Report Bugs as GitHub issues
- Analyze Bugs
- Contribute Code (fixes and features)
- Contribute to the Knowledge Base: The fuel driving the open-source vulnerability assessment tool is its vulnerability database with information about fix commits for publicly known open source vulnerabilities. The so-called vulnerability assessment knowledge base is a dedicated GitHub repository to organize the sharing and joint maintenance of this information.
The following is a subset of pending feature requests:
- Static and dynamic analysis for Python
- Support of JavaScript (client- and server-side)
- UI dashboards for workspaces
Copyright (c) 2018 SAP SE or an SAP affiliate company. All rights reserved.
This project is licensed under the Apache Software License, v.2 except as noted otherwise in the LICENSE file.
[1] https://snyk.io/blog/owasp-top-10-breaches/
[2] https://www.sap.com/documents/2017/08/f2895a6e-ca7c-0010-82c7-eda71af511fa.html
[3] https://scholar.google.com/citations?user=FOEVZyYAAAAJ&hl=en