The TL;DR for the learnings of Windows Vulnerability CVE-2023-28252
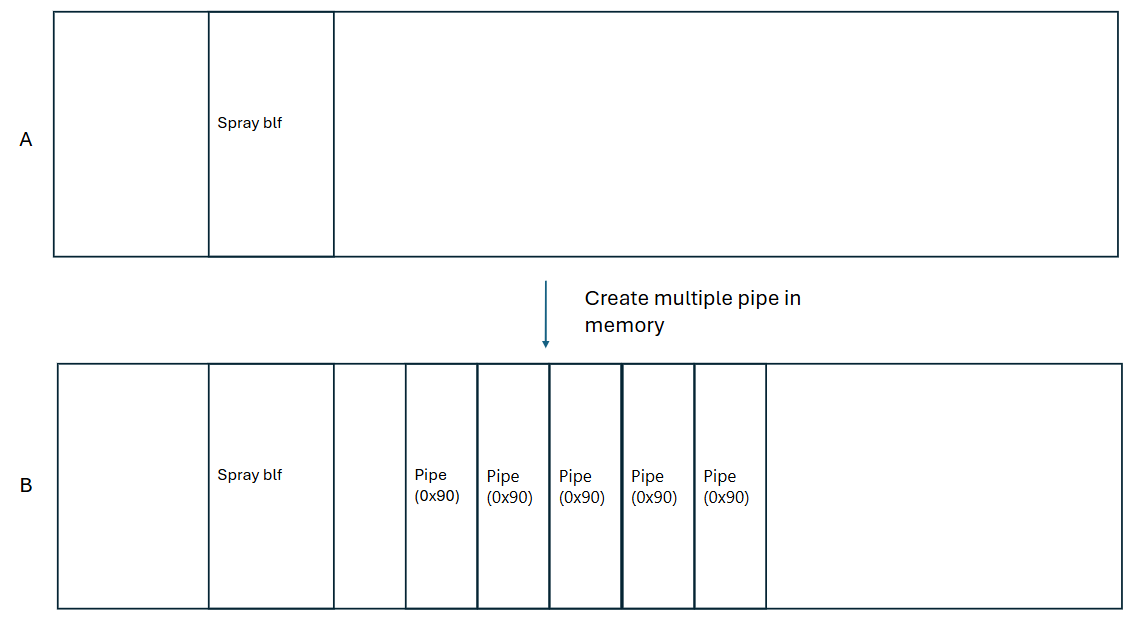
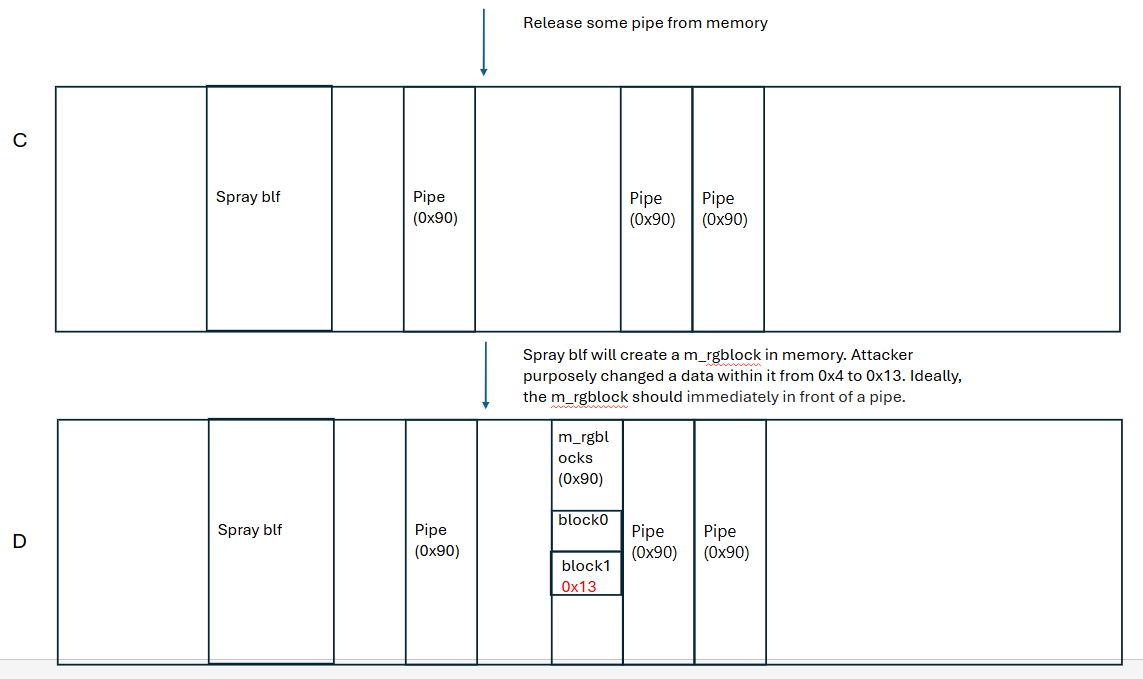
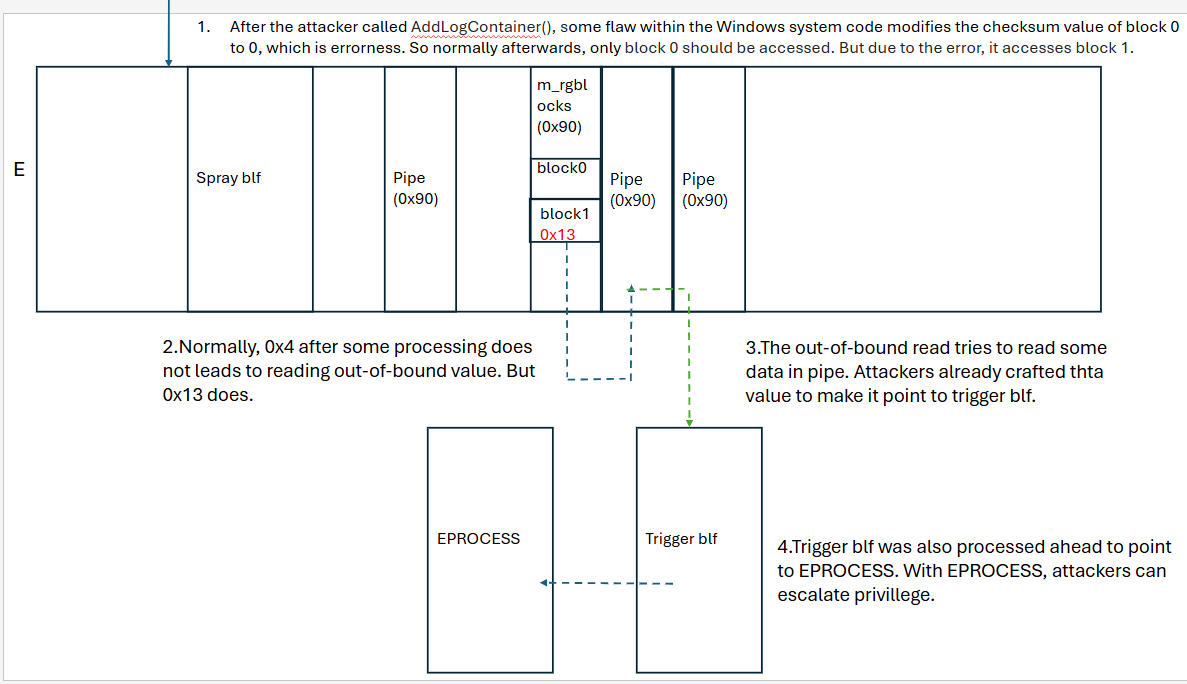
So this weekend I was practising the Aero machine on Hack The Box. The box is so much fun playing it when you can mimic a real-world attack to a Windows 11 machine. After completing it, I was very curious and wanting to know how the privilage-escalation exploit works. So I mainly read the article written by the exploit author [1]. The description is very detailed, well-explained. But going through the whole process takes a lot of time. To better demonstrate the exploit workflow, I want to visualize the process here. A big solute to the exploit authors Ricardo narvaja and Esteban kazimirow, as well as the authors from Qianxin[2].