Weave Ignite is an open source Virtual Machine (VM) manager with a container UX and built-in GitOps management.
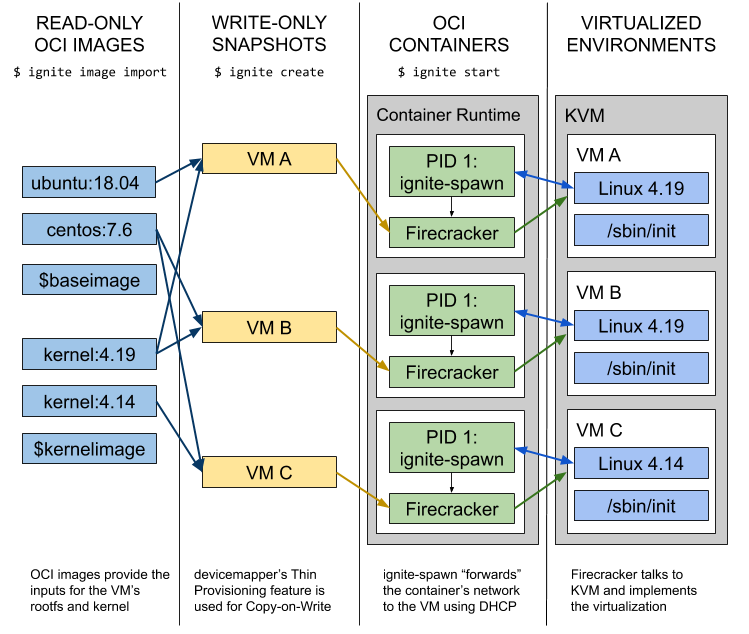
- Combines Firecracker MicroVMs with Docker / OCI images to unify containers and VMs.
- Works in a GitOps fashion and can manage VMs declaratively and automatically like Kubernetes and Terraform.
Ignite is fast and secure because of Firecracker. This is an open source KVM implementation from AWS that is optimised for high security, isolation, speed and low resource consumption. AWS uses it as the foundation for their serverless offerings (AWS Lambda and Fargate) that need to load nearly instantly while also keeping users isolated (multitenancy). Firecracker has proven to be able to run 4000 micro-VMs on the same host!
Ignite makes Firecracker easy to use by adopting its developer experience from containers.
With Ignite, you pick an OCI-compliant image (Docker image) that you want to run as a VM, and then just
execute ignite run instead of docker run. There’s no need to use VM-specific tools to build
.vdi, .vmdk, or .qcow2 images, just do a docker build from any base image you want
(e.g. ubuntu:18.04 from Docker Hub), and add your preferred contents.
When you run your OCI image using ignite run, Firecracker will boot a new VM in c.125 milliseconds (!) for you, using a default 4.19 linux kernel. If you want to use some other kernel, just specify the --kernel flag, pointing to another OCI image containing a kernel at /boot/vmlinux, and optionally your preferred modules. Next, the kernel executes /sbin/init in the VM, and it all starts up. After this, Ignite connects the VMs to any CNI network, integrating with e.g. Weave Net.
Ignite is a declarative Firecracker microVM administration tool, like Docker manages runC containers. Ignite runs VM from OCI images, spins VMs up/down in lightning speed, and can manage fleets of VMs efficiently using GitOps.
The idea is that Ignite makes Firecracker VMs look like Docker containers.
Now we can deploy and manage full-blown VM systems just like e.g. Kubernetes workloads.
The images used are OCI/Docker images, but instead of running them as containers, it executes
as a real VM with a dedicated kernel and /sbin/init as PID 1.
Networking is set up automatically, the VM gets the same IP as any docker container on the host would.
And Firecracker is fast! Building and starting VMs takes just some fraction of a second, or at most some seconds. With Ignite you can get started with Firecracker in no time!
With Ignite, Firecracker is now much more accessible for end users, which means the ecosystem can achieve the next level of momentum due to the easy onboarding path thanks to a docker-like UX.
Although Firecracker was designed with serverless workloads in mind, it can equally well boot a
normal Linux OS, like Ubuntu, Debian or CentOS, running an init system like systemd.
Having a super-fast way of spinning up a new VM, with a kernel of choice, running an init system
like systemd allows to run system-level applications like the kubelet, which needs to “own” the full system.
Example use-cases:
- Set up many secure VMs lightning fast. It's great for testing, CI and ephemeral workloads
- Launch and manage entire “app ready” stacks from Git because Ignite supports GitOps!
- Run even legacy or special apps in lightweight VMs (eg for multi-tenancy, or using weird/edge kernels)
And - potentially - we can run a cloud of VMs ‘anywhere’ using Kubernetes for orchestration, Ignite for virtualization, GitOps for management, and supporting cloud native tools and APIs.
Ignite is different from Kata Containers or gVisor. They don’t let you run real VMs, but only wrap a container in new layer providing some kind of security boundary (or sandbox).
Ignite on the other hand lets you run a full-blown VM, easily and super-fast, but with the familiar container UX. This means you can “move down one layer” and start managing your fleet of VMs powering e.g. a Kubernetes cluster, but still package your VMs like containers.
Please check out the Releases Page.
How to install Ignite is covered in docs/installation.md.
WARNING: In it's v0.X series, Ignite is in alpha, which means that it might change in backwards-incompatible ways.
Note: At the moment ignite needs root privileges on the host to operate,
for certain specific operations (e.g. mount). This will change in the future.
# Let's run the weaveworks/ignite-ubuntu docker image as a VM
# Use 2 vCPUs and 1GB of RAM, enable automatic SSH access and name it my-vm
ignite run weaveworks/ignite-ubuntu \
--cpus 2 \
--memory 1GB \
--ssh \
--name my-vm
# List running VMs
ignite ps
# List Docker (OCI) and kernel images imported into Ignite
ignite images
ignite kernels
# Get the boot logs of the VM
ignite logs my-vm
# SSH into the VM
ignite ssh my-vm
# Inside the VM you can check that the kernel version is different, and the IP address came from the Docker bridge
# Also the memory is limited to what you specify, as well as the vCPUs
> uname -a
> ip addr
> free -m
> cat /proc/cpuinfo
# Rebooting the VM tells Firecracker to shut it down
> reboot
# Cleanup
ignite rm my-vmFor a walkthrough of how to use Ignite, go to [docs/usage.md](docs/usage.md).
In Git you declaratively store the desired state of a set of VMs you want to manage.
ignite gitops reconciles the state from Git, and applies the desired changes as state is updated in the repo.
This can then be automated, tracked for correctness, and managed at scale - just some of the benefits of GitOps.
The workflow is simply this:
- Run
ignite gitops [repo], where repo points to your Git repo - Create a file with the VM specification, specifying how much vCPUs, RAM, disk, etc. you’d like from the VM
- Run
git pushand see your VM start on the host
See it in action!
Please refer to the following documents:
- Documentation Page
- Installing Ignite
- Scope and Dependencies
- Getting Started Walkthrough
- Declaratively Controlling Ignite
- CLI Reference
- API Reference
A base image is an OCI-compliant image containing some operating system (e.g. Ubuntu).
You can follow normal docker build patterns for customizing your VM's rootfs.
A kernel image is an OCI-compliant image containing a /boot/vmlinux (an uncompressed kernel)
executable (can be a symlink). You can also put supporting kernel modules in /lib/modules
if needed. You can match and mix any kernel and any base image.
As the upstream centos:7 and ubuntu:18.04 images from Docker Hub doesn't
have all the utilities and packages you'd expect in a VM (e.g. an init system), we have packaged some
reference base images and a sample kernel image to get started quickly.
You can use the following pre-built images with Ignite. They are built on the normal Docker Hub images,
but add systemd, openssh, and similar utilities.
- Ubuntu 18.04 Dockerfile (
weaveworks/ignite-ubuntu) - CentOS 7 Dockerfile (
weaveworks/ignite-centos) - Amazon Linux 2 Dockerfile (
weaveworks/ignite-amazonlinux) - The Firecracker Team's Alpine Image (
weaveworks/ignite-alpine)
- Default Kernel Image (
weaveworks/ignite-kernel) - The Firecracker Team's Kernel (
weaveworks/ignite-amazon-kernel)
- Guide: Run a HA Kubernetes cluster with Ignite and kubeadm (
weaveworks/ignite-kubeadm)
These prebuilt images can be given to ignite run directly.
Please see CONTRIBUTING.md and our Code Of Conduct.
Other interesting resources include:
If you have any questions about, feedback for or problems with ignite:
- Invite yourself to the Weave Users Slack.
- Ask a question on the #ignite slack channel.
- File an issue.
Your feedback is always welcome!