(Sumerian) Nisaba was the Sumerian goddess of writing, learning, and the harvest
Lambda functions for verifying phone numbers
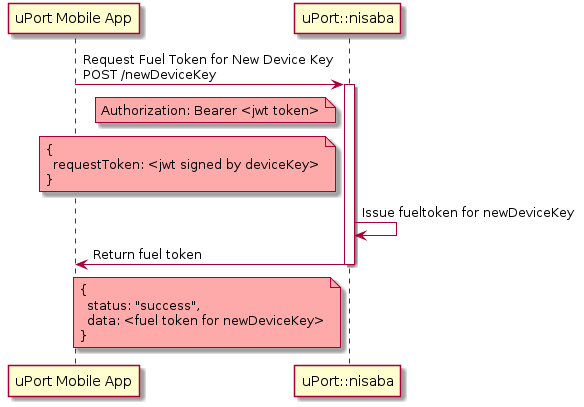
Nisaba provides user verification for the uPort ecosystem.
A verified user can request a new fuel token for a new deviceKey.
POST /newDeviceKey
Authorization: Bearer <nisaba token/fuel token>
{
requestToken: <jwt signed by deviceKey>
}
The payload of the requestToken should be:
{
newDeviceKey: <address of the new device key>
}
| Status | Message | |
|---|---|---|
| 200 | Ok | Fuel Token |
| 403 | Forbidden | JWT token missing or invalid |
| 500 | Internal Error | Internal error |
Token stored in code is deleted after JWT expiration date
{
'status': 'success',
'data': <fuel token for new deviceKey>
}
Starts a verification for a deviceKey and a phoneNumber. Sends a code thru SMS or Call
POST /verify
{
deviceKey: <device key>,
phoneNumber: <phone number>
}
| Status | Message | |
|---|---|---|
| 200 | Ok. | Verificaition started |
| 400 | Bad request | Bad or missing parameter |
| 500 | Internal Error | Internal Error |
Process continues by passing the deviceKey to the verification service.
GET /next/{device_key}
| Status | Message | |
|---|---|---|
| 200 | Ok. | Verificaition started |
| 400 | Bad request | Bad or missing parameter |
| 500 | Internal Error | Internal Error |
With the code (which was sent thru SMS) the app can verify it and request the pseudo-attestation token
POST /check
{
deviceKey: <device key>,
code: <code>
}
| Status | Message | |
|---|---|---|
| 201 | Ok | JWT token |
| 404 | Not found | Bad code |
| 500 | Internal Error | Internal Error |
{
'status': 'success',
'data': <jwt>
}
This is not a proper uPort Attestation because the sub is not a uportId is just the deviceKey
{
iss: "api.uport.me/nisaba",
exp: <token expiration date>,
iat: <token issued date>,
sub: <device key>,
aud: [
"api.uport.me/nisaba",
"api.uport.me/unnu",
"api.uport.me/sensui"
],
phoneNumber: <phone number>
}