This repo seeks to provide an example that demonstrates how to protect sensitive data using HashiCorp Vault.
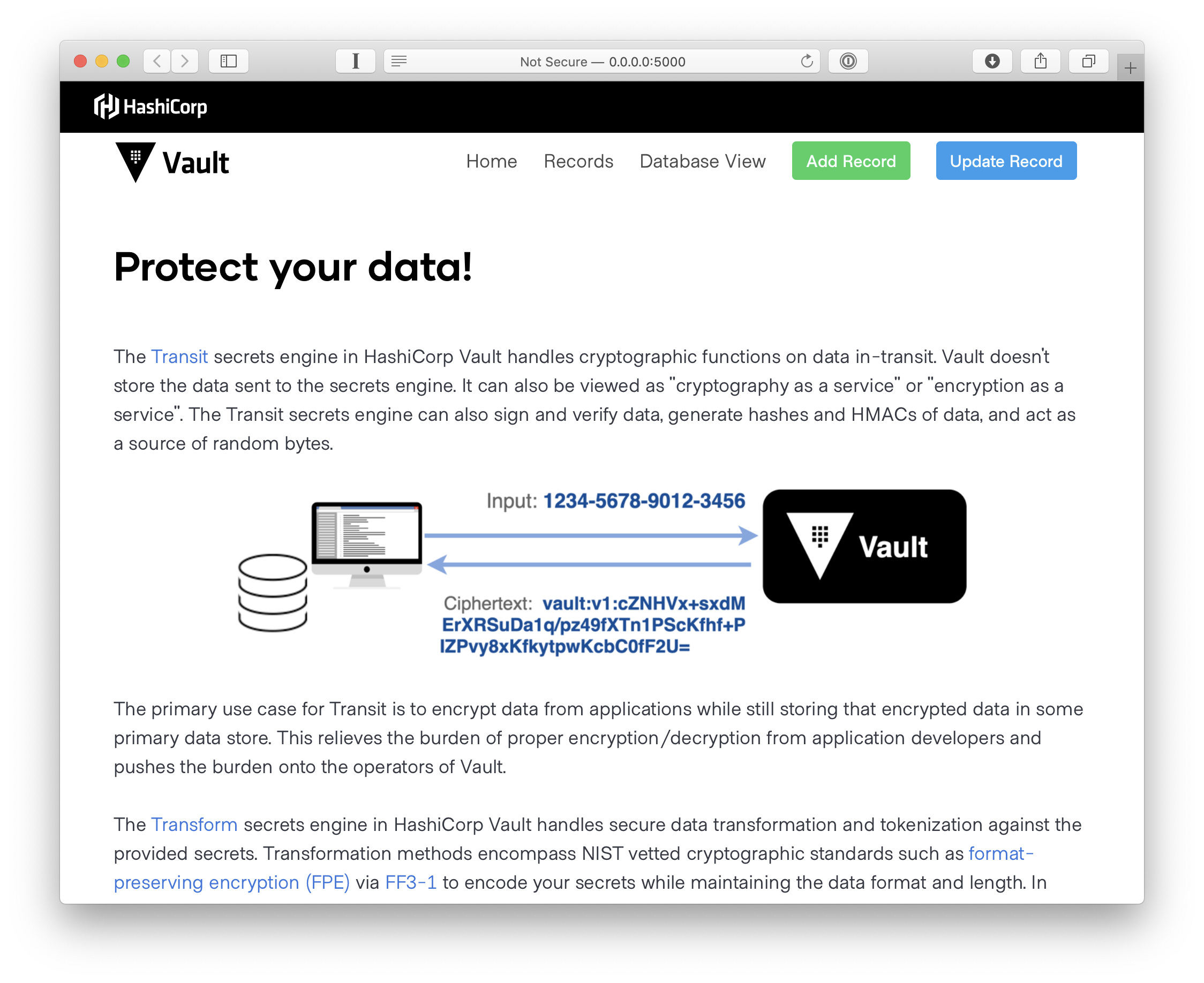
The Transit secrets engine in HashiCorp Vault provides an API that can be used to perform a variety of cryptographic operations, such as encryption, decryption, signing, hashing, and HMAC. It can also be used for secure key generation, or providing a unified method for random number generation.
The Transform secrets engine in HashiCorp Vault provides an API that can be used to perform secure data transformation and tokenization against a provided input value. This can be used to implement format preserving encryption as well as masking of sensitive data.
This repo launches a simple CRUD app that can integrate with Vault to protect customer records. Database dynamic credentials are also used.
Please note that the Transform secrets engine is an Enterprise only feature. If you wish to use Transform in this demo, please make sure you are using Vault Enterprise. The Vault Enterprise binary is available at releases.hashicorp.com/vault, and will be denoted by +ent in the name. It will run for 30 minutes without a license before shutting down.
This application reads the following required configuration parameters from environment variables at startup:
VAULT_ADDR- Vault cluster or server addressVAULT_DATABASE_CREDS_PATH- Vault MySQL database dynamic credentials pathVAULT_NAMESPACE- Vault namespaceVAULT_TRANSFORM_PATH- Vault Transform engine pathVAULT_TRANSFORM_MASKING_PATH- Vault Transform engine path for maskingVAULT_TRANSIT_PATH- Vault Transit engine pathMYSQL_ADDR- MySQL database address (omit port as it is currently hardcoded to 3306)
Optional:
VAULT_TOKEN- Provide if Vault token auth is desired
This application currently supports two Vault authentication methods: token auth or JWT auth with an Azure identity token. If a VAULT_TOKEN is provided it will be used. Otherwise the app will try retrieving an access token from Azure MSI and logging into Vault using the JWT auth method. The JWT auth method must be configured at the default path of jwt with a role of webapp-role.
docker run --name transit-app-example \
-p 5000:5000 \
-e VAULT_ADDR=http://192.168.100.2:8200 \
-e VAULT_DATABASE_CREDS_PATH=database/creds/transit-app-example \
-e VAULT_NAMESPACE=development \
-e VAULT_TOKEN=s.AvYZaHT7DAUyP6dDbj7S4ESu \
-e VAULT_TRANSFORM_PATH=transform \
-e VAULT_TRANSFORM_MASKING_PATH=masking/transform \
-e VAULT_TRANSIT_PATH=transit \
-e MYSQL_ADDR=192.168.100.2 \
-d assareh/transit-app-example:latest
- Browser window must be greater than 1100 or so pixels wide due to a CSS issue
Fork the code on GitHub.