Filament Access Control
Opinionated setup for managing admin users, roles and permissions within Laravel Filament
Features
- Separate database table for filament admin users (separate model, separate guard, separate password broker)
- Uses spatie/laravel-permission for roles and permissions
- Adds the missing password reset flow to Filament
- Fully localized
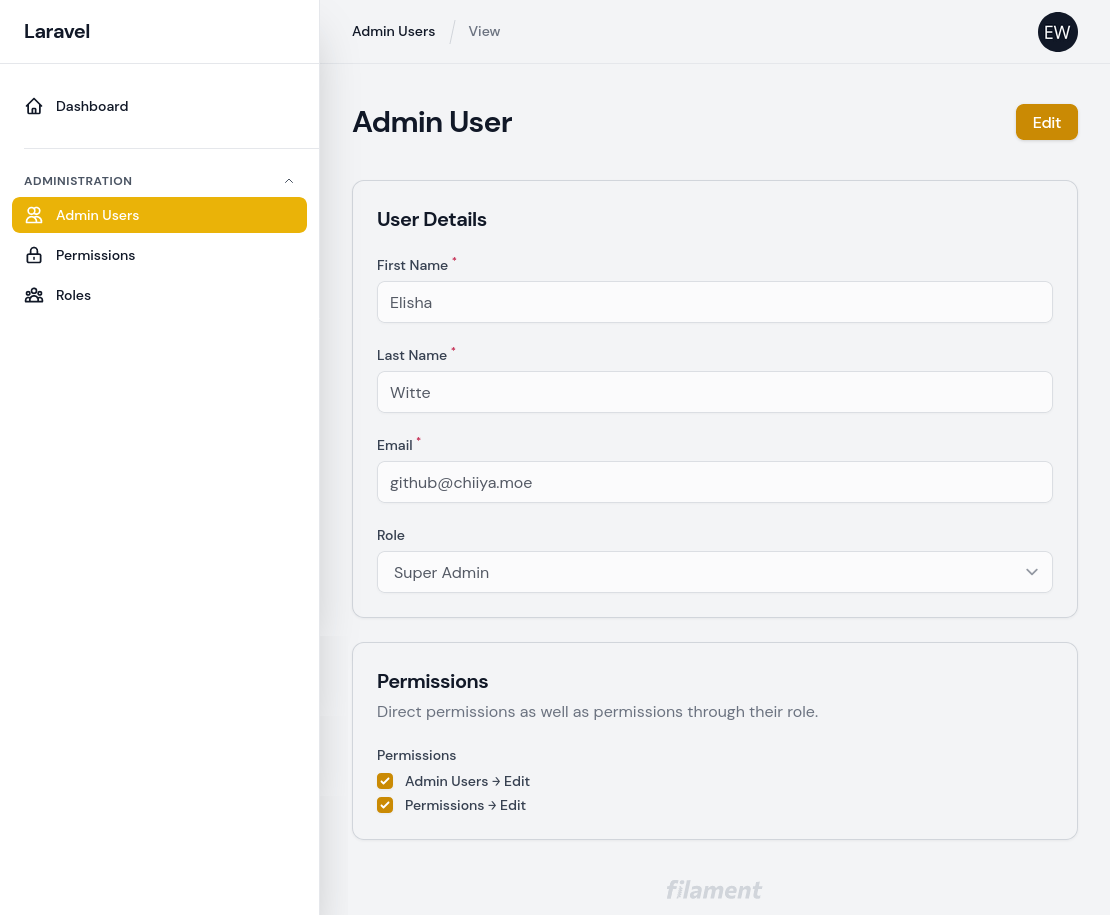
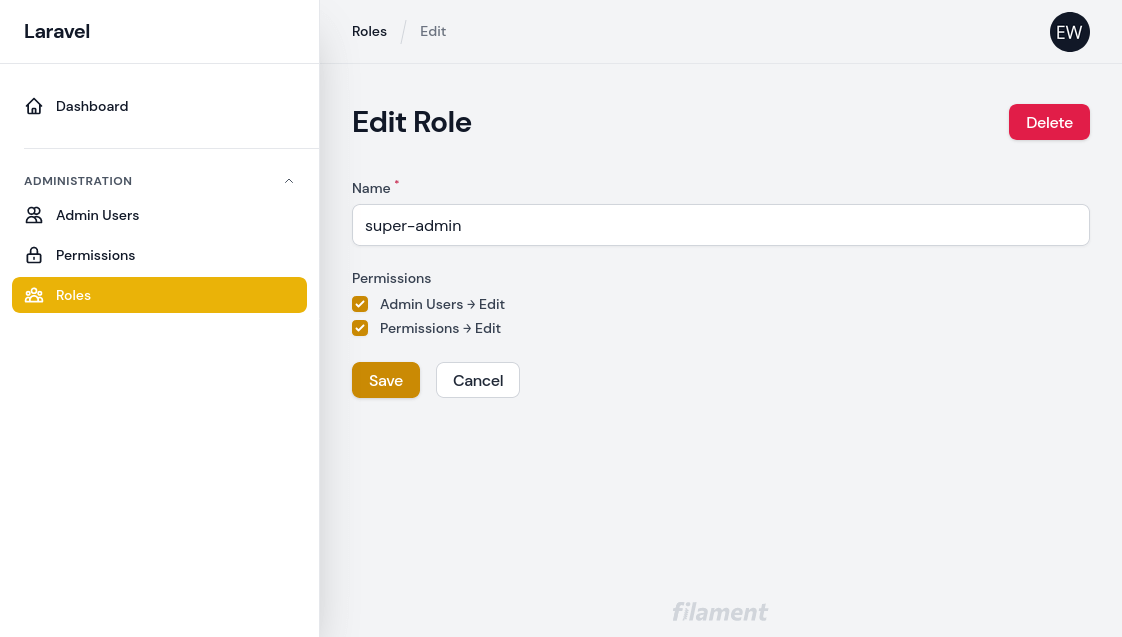
- CRUD resources for admin users, roles and permissions
- Admin users may belong to one role
- Admin users can have direct permissions or indirect permissions through their role
- When creating admin users through the admin interface, no password is specified. Instead, the user receives an email prompting them to set their password
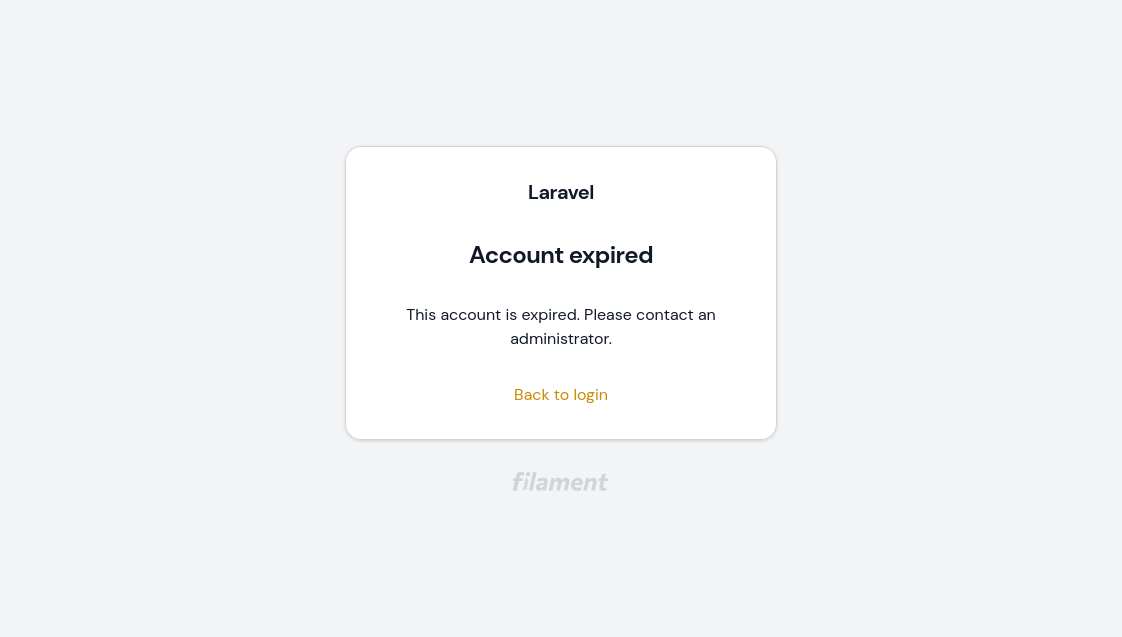
- Optional account expiry for admin users. Expired accounts are no longer able to log in
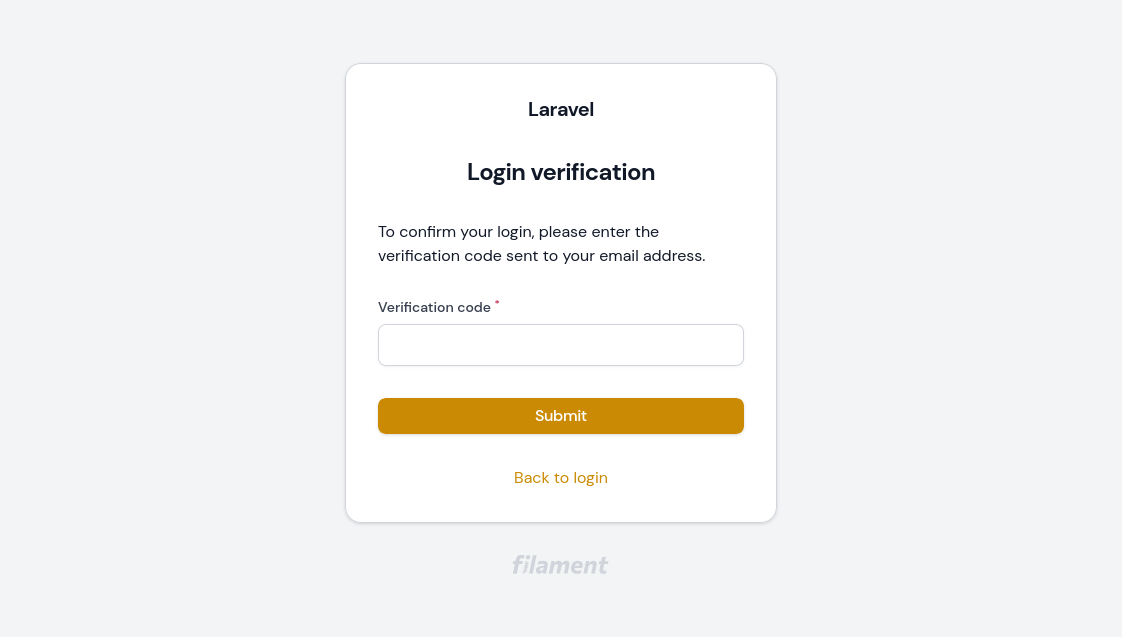
- Optional email based two-factor authentication.
Installation
- Install the package via composer:
composer require chiiya/filament-access-control- Update your
config/filament.phpfile to use the package's guard andLoginpage:
'auth' => [
'guard' => env('FILAMENT_AUTH_GUARD', 'filament'),
'pages' => [
'login' => \Chiiya\FilamentAccessControl\Http\Livewire\Login::class,
],
],- Publish the migrations and config, then run the migrations. Make sure you also publish and run the spatie/laravel-permission migrations if you haven't done so yet.
php artisan vendor:publish --tag="filament-access-control-migrations"
php artisan vendor:publish --tag="filament-access-control-config"
php artisan vendor:publish --provider="Spatie\Permission\PermissionServiceProvider"
php artisan migrate-
To seed the necessary base data (role & permissions), run
php artisan filament-access-control:installor call theChiiya\FilamentAccessControl\Database\Seeders\FilamentAccessControlSeederseeder in your database seeder. -
Create an admin user using
php artisan filament-access-control:user. If you create users programmatically (e.g. in your database seeder), make sure to assign them thesuper-adminrole if you want them to be able to access the role and user management.
Optionally, you can publish the translations with:
php artisan vendor:publish --tag="filament-access-control-translations"Optionally, you can publish the views with:
php artisan vendor:publish --tag="filament-access-control-views"Usage
Authorizing Resources, Pages & Actions
Authorizing Resources
To authorize access to resources, use policies as described in the Filament documentation.
class ProductPolicy
{
public function viewAny(FilamentUser $user): bool
{
return $user->can('products.view');
}
// ...
}Authorizing Pages
This package comes with a simple trait that you can use to authorize access to custom pages based on a permission.
use Chiiya\FilamentAccessControl\Traits\AuthorizesPageAccess;
class MyPage extends Page
{
use AuthorizesPageAccess;
public static string $permission = 'my-page.view';
public function mount(): void
{
static::authorizePageAccess();
}
}Authorizing Actions
One way to authorize actions is to use the visible() method:
ButtonAction::make('exports')
->visible(fn () => Filament::auth()->user()->can('exports.view'))Localizing Role & Permission Names
Roles and permissions should have names that make them easy to use in code (e.g. admin-users.update).
For the admin you may however wish to localize them or make them more readable. You can do so by simply
adding a JSON translation entry for the given role or permission name (e.g. lang/en.json):
{
"admin-users.update": "Admin Users → Edit"
}Feature: Account Expiry
With the optional account expiry feature, all accounts require an expiration date. When accounts are expired, they can no longer log in. To enable the account expiry feature, enable the feature flag in the config file:
'features' => [
\Chiiya\FilamentAccessControl\Enumerators\Feature::ACCOUNT_EXPIRY,
],You will also need to add the EnsureAccountIsNotExpired middleware to your filament auth middleware config:
use Chiiya\FilamentAccessControl\Http\Middleware\EnsureAccountIsNotExpired;
'middleware' => [
'auth' => [
Authenticate::class,
EnsureAccountIsNotExpired::class,
],
]Feature: Two-Factor Authentication
With the optional two-factor authentication feature, users must enter a verification code sent via email upon login. To enable the two-factor authentication feature, enable the feature flag in the config file:
'features' => [
\Chiiya\FilamentAccessControl\Enumerators\Feature::TWO_FACTOR,
],Screenshots
Changelog
Please see CHANGELOG for more information on what has changed recently.
Contributing
Please see CONTRIBUTING for details.
License
The MIT License (MIT). Please see License File for more information.