GitHub uses your commit email address to associate commits with your GitHub account. When a user makes commits to a public repository, their email address is pushed with the commit.
If you'd like to keep your personal email address private, you can use a GitHub-provided no-reply email address as your commit email address. GitHub provides some instructions on keeping your personal email address private, but it seems that GitHub users either don't know or don't care that their email address may be exposed.
However, any commits you made before changing your commit email address are still associated with your previous email address. This is why this repository exists. The script will clone all accessible repositories, change the committer email from all commits and push it back to GitHub.
- This
email_fix.pyscript is meant to run on Linux. If you're using Windows 10 and above, I recommend running Ubuntu via WSL. You can follow the documentation from Microsoft to install WSL. What things you need to run the program: - Python3 and PIP can be installed using
APT package managerby running:sudo apt install python3 python3-pip
- Install the following Packages from PyPi by using the following commands:
pip3 install -r requirements.txt
- First, we need to generate a personal access token that will allow us to authenticate against the API. We can get one at https://github.com/settings/tokens and by clicking on Generate new token. Select
RepoandUserscopes for the token. - Rename
.env.sampleto.envand populate the appropriate values. - Run
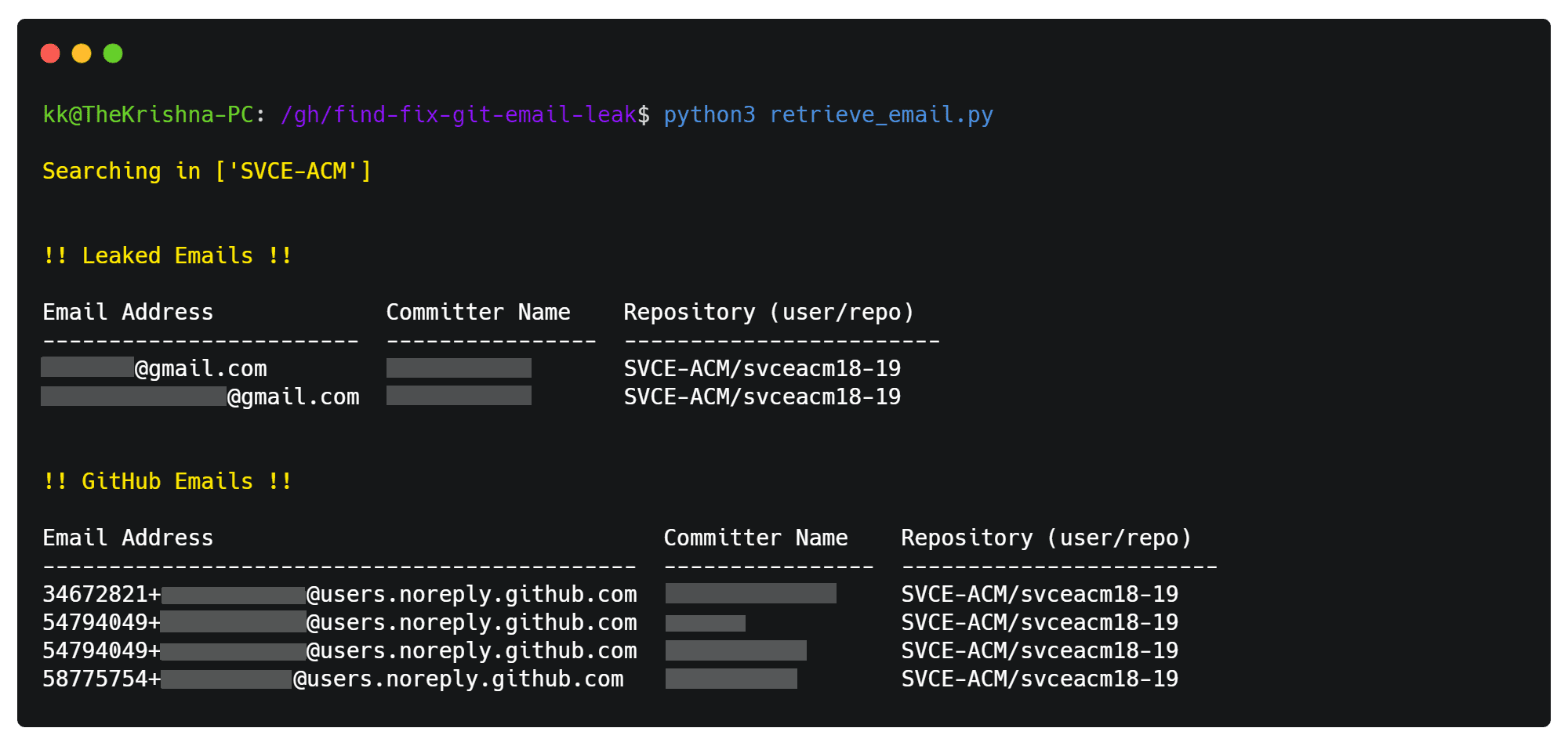
retrieve_email.pyto check for all leaked email addresses. This script uses recent events via the GitHub API to find the leaked email addresses. An example screenshot is attached: - Once you identified the leaked email addresses, populate them back to the
.envfile. - Now, run
email_fix.pyto replace the committer email addresses with theCORRECT_EMAILfrom.env(preferably the GitHub-providedno-replyemail address). Changes might take up to 90 days to reflect in the GitHub Events API. - Repeat the process if you have multiple leaked email addresses.
- GitHub Docs: Block commits you push from the command line that expose your personal email address
- The script does not preserve the
SHA1s for previous tags, versions and objects. - The
retrieve_email.pyuses GitHub Events API to scan for leaked email(s) which limits scanning upto 100 recent results per page TODOEach Git commits needs to be scanned for email(s). This will also increase coverage for git repositories outside GitHub.TODOCurrently, works only on theHEADor parent branch (master,main, etc). Will increase the scope to other branches if I have the time.
- Hat tip to anyone whose code was used.
I shall not be liable for any consequential, incidental, direct, indirect, special, or other damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss). Run this at your own risk.
Made with ❤️ by Krishnakanth Alagiri