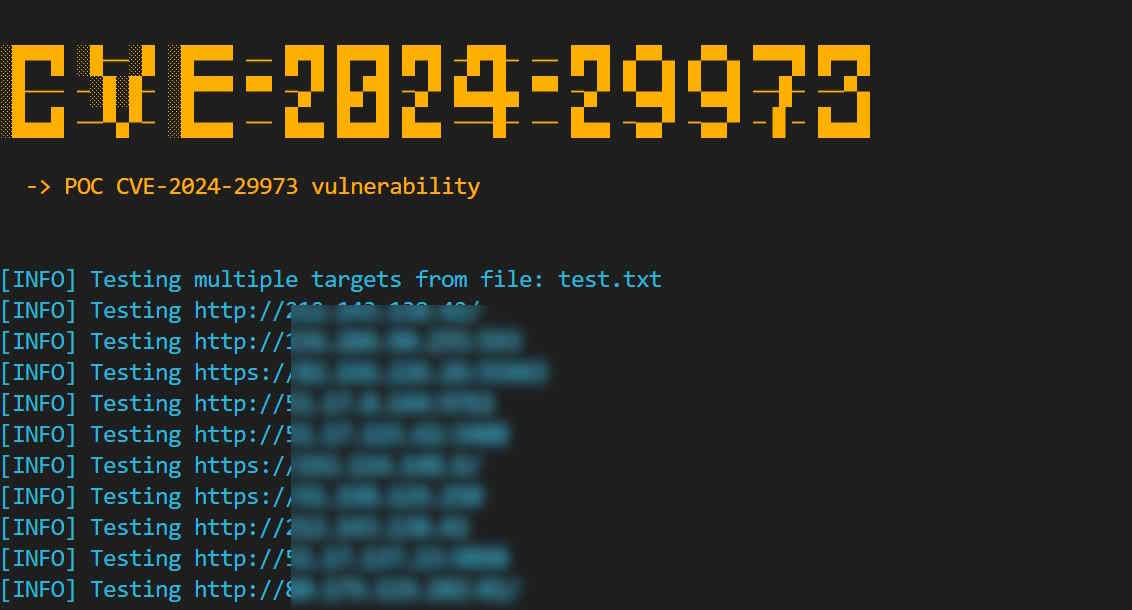
This is a proof-of-concept (PoC) and bulk scanner for CVE-2024-29973: Command injection vulnerability in Zyxel NAS326 firmware versions before V5.21(AAZF.17)C0 and NAS542 firmware versions before V5.21(ABAG.14).
- Fixed the payload mechanism. Thanks to https://github.com/p0et08/ for mentioning this.
To scan a single target:
python cve-2024-29973.py -u targetTo mass scan bulk targets IPs:
python cve-2024-29973.py -f targets.txt- Python 3.6 or higher
requestslibrary
git clone https://github.com/bigb0x/CVE-2024-29973.git; cd CVE-2024-29973Install the required packages using pip:
pip install requestsPOC was created by M Ali.
This project is licensed under the MIT License.
This provided tool is for educational purposes only. I do not encourage, condone, or support unauthorized access to any system or network. Use this tool responsibly and only on systems you have explicit permission to test. Any actions and consequences resulting from misuse of this tool are your own responsibility.