AWS Organization Formation is an Infrastructure as Code (IaC) tool for AWS Organizations.
AWS Organization Formation (also: org-formation) has 3 main features:
- Infrastructure as Code for AWS Organizations:
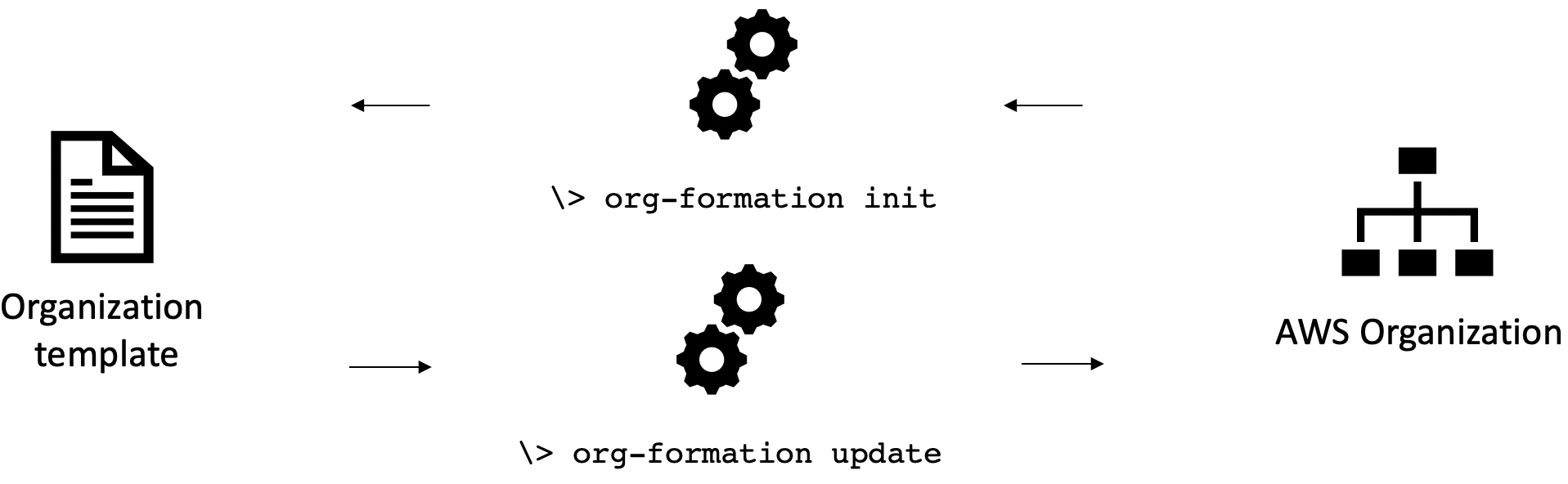 Organization resources reference | Example organization file | CLI Reference
Organization resources reference | Example organization file | CLI Reference
- CloudFormation annotations to provision resources cross account:
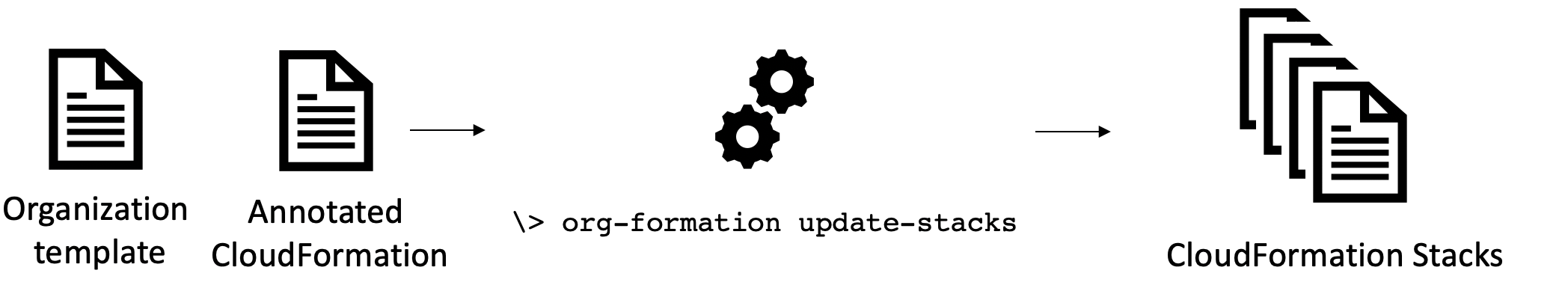 Annotated CloudFormation reference | Examples | CLI Reference
Annotated CloudFormation reference | Examples | CLI Reference
- Automation of account creation and resource provisioning:
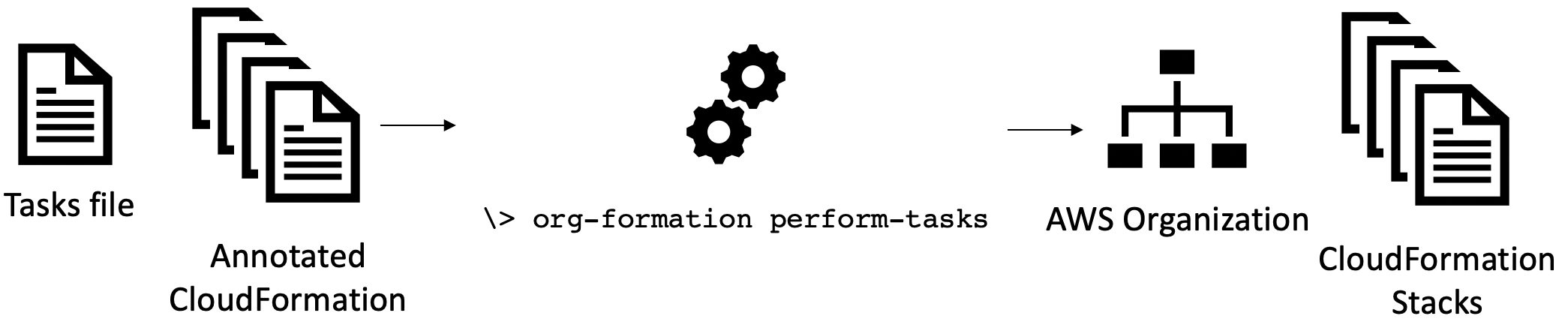 Automation task file reference | Example tasks file | CLI Reference
Automation task file reference | Example tasks file | CLI Reference
Want more? here a list of 50+ features 😎😎😎
With npm installed, run
> npm install -g aws-organization-formation
You can now execute the commandline program org-formation. try:
> org-formation --help
💡Need help getting started? Get some on slack!
To get started you first need an org-formation template that describes all your Organization resources such as Accounts, OUs and SCPs.
After Installation you can generate this file using the following command:
> org-formation init organization.yml --region us-east-1 [--profile org-master-account]
example output organization.yml file
AWSTemplateFormatVersion: '2010-09-09-OC'
Organization:
Root:
Type: OC::ORG::MasterAccount
Properties:
AccountName: My Organization Root
AccountId: '123123123123'
Tags:
budget-alarm-threshold: '2500'
account-owner-email: my@email.com
OrganizationRoot:
Type: OC::ORG::OrganizationRoot
Properties:
ServiceControlPolicies:
- !Ref RestrictUnusedRegionsSCP
ProductionAccount:
Type: OC::ORG::Account
Properties:
RootEmail: production@myorg.com
AccountName: Production Account
Tags:
budget-alarm-threshold: '2500'
account-owner-email: my@email.com
DevelopmentAccount:
Type: OC::ORG::Account
Properties:
RootEmail: development@myorg.com
AccountName: Development Account
Tags:
budget-alarm-threshold: '2500'
account-owner-email: my@email.com
DevelopmentOU:
Type: OC::ORG::OrganizationalUnit
Properties:
OrganizationalUnitName: development
Accounts:
- !Ref DevelopmentAccount
ProductionOU:
Type: OC::ORG::OrganizationalUnit
Properties:
OrganizationalUnitName: production
Accounts:
- !Ref ProductionAccount
RestrictUnusedRegionsSCP:
Type: OC::ORG::ServiceControlPolicy
Properties:
PolicyName: RestrictUnusedRegions
Description: Restrict Unused regions
PolicyDocument:
Version: '2012-10-17'
Statement:
- Sid: DenyUnsupportedRegions
Effect: Deny
NotAction:
- 'cloudfront:*'
- 'iam:*'
- 'route53:*'
- 'support:*'
Resource: '*'
Condition:
StringNotEquals:
'aws:RequestedRegion':
- eu-west-1
- us-east-1
- eu-central-1Note: If you prefer to set up CI/CD run org-formation init-pipeline instead. It will create a CodeCommit repository and CodePipeline that will update your organization upon every commit!
You can make changes to the file you generated and upate your organization using the update commmand. Alternatively you can run create-change-set and update-change-set. Read more in the cli reference
Once you got the hang of managing organization resources, use these organization resources to write smarter cloudformation that allows you to provision resources across your organization. Read more about managing resources across accounts.
Just like with the resources within your AWS Account, managing AWS Organization resources as code allows you to apply changes automatically, reducing manual work, inconsistencies and mistakes.
If you are considering to use an account vending machine (e.g. AWS Control Tower) to create and manage new accounts within your organization: Do realize that the account vending machine allows you to quickly create organization resources but only has limited facilities when it comes to updating and maintaining these resources.
My operation takes a long time to complete / is slow.
Especially if you have a lot of accounts this can happen.
An easy way to speed things up is by specifying the commandline argument --max-concurrent-stacks 10 where 10 is the number of stacks to run in concurrently.
Another way to speed things up is to run tasks in parallel this can be done with the argument --max-concurrent-tasks 10. This, however, has the side-effect that the logging might be somewhat harder to ralate to a specific task (as it might be out of order).
Is there a way around having to create new email accounts per account?
Every AWS Account needs a unique root email address, there is no way around this...
What you can do however is however is see whether your mailserver allows you to append a '+' (plus sign) and another secondary name to your account to create new unique email addresses.
Email to there addresses will end up in the mailbox assigned to the alias before the plus sign and this will still be considered a valid and unique emailaddress when creating a new AWS Account.
Example:
If your emailaddress is name@gmail.com you will receive email send to name+awsaccount1@gmail.com and name+awsaccount2@gmail.com to your inbox.
Mailservers that support this are gmail, aws workmail and hotmail.
How do i set up MFA for the account used by org-formation?
Org-formation needs high priviledge access to your master account. If you run org-formation manually it is wise to set up MFA.
I assume you have credentials set up in ~/.aws/credentials and this looks like (might well be called default):
[org-formation]
aws_access_key_id = AKIAxxxxxxxxx
aws_secret_access_key = xxxxxxxxxxxxxxxxxThis allows org-formation to assume the IAM User that corresponds to the access key and secret using the option --profile org-formation.
In order to enforce MFA you need to do the following:
- Assign a MFA device to the IAM User in the console.
- Create a role in your master account that has high priviledged access and enforces the use of MFA. We call this
MyOrgFormationRole. - Create a profile that refers to the MyOrgFormation. We call this profile
org-formation-mfa. - Test whether MFA has been setup correctly by running
org-formation describe-stacks --profile org-formation-mfa. - If step #4 was succesfull you can strip the IAM user you use from permissions other than the once it needs to assume
MyOrgFormationRole.
Code snippets below:
- Creating the
MyOrgFormationRoleRole (step #2) - execute with CloudFormation
AWSTemplateFormatVersion: '2010-09-09'
Resources:
MyOrgFormationRole:
Type: AWS::IAM::Role
Properties:
RoleName: MyOrgFormationRole
ManagedPolicyArns:
- 'arn:aws:iam::aws:policy/AdministratorAccess'
AssumeRolePolicyDocument:
Version: '2012-10-17'
Statement:
- Effect: Allow
Principal:
AWS: !Sub 'arn:aws:iam::${AWS::AccountId}:root'
Action: sts:AssumeRole
Condition:
Bool:
aws:MultiFactorAuthPresent: 'true'- Creating the profile
org-formation-mfa(step #3) put in your~/.aws/configfile. Replace000000000000with your master account id. The value formfa_serialneeds to be the value you got when setting up MFA for your user
[profile org-formation-mfa]
role_arn = arn:aws:iam::000000000000:role/MyOrgFormationRole
source_profile = org-formation
mfa_serial = arn:aws:iam::000000000000:mfa/my-user- Expected output when executing a command that requires MFA (step 4):
\> org-formation describe-stacks --profile org-formation-mfa
👋 Enter MFA code for arn:aws:iam::000000000000:mfa/my-user:
XXXXXX # here you type in the put the MFA code
{ ...regular output } # if successfull the command will execute- The minimum set of permissions for your user
Replace
000000000000with your master account id (or the complete ARN for your Role )
Sid: 'AssumeMFARole'
Action: 'sts:AssumeRole'
Effect: 'Allow'
Resource: 'arn:aws:iam::000000000000:role/MyOrgFormationRole'Hope this helps
What is the password of the root user for newly created accounts?
Accounts that are created have a root user but no password.
You can create a password using the 'Forgot password' process using the root email.
Note: Once you have created a password and used it consider to throw the password away. You are not supposed to log in using root anyway and storing your password somewhere could only lead to losing it. As we just figured out above you didnt need it in the first place.
Do bind an MFA on your root user! Find info under the IAM service section of the console
Needless to add? dont use a virtual MFA on the same device that has access to the email account used as RootEmail... this reduces your 'multi factor' authentication to a single factor 🤔🤣
What happens when I remove an account from the organization.yml?
If you remove an account from the organization it will not be deleted. Deleting accounts using api calls is not supported by AWS.
After running update the account that is removed from the organization will be not be able to be part of organization bindings.
\> org-formation update ./examples/organization.yml --profile org-formation
OC::ORG::Account | Development4Account | Forget
OC::ORG::OrganizationalUnit | DevelopmentOU | Detach Account (Development4Account)
OC::ORG::OrganizationalUnit | DevelopmentOU | CommitHash
After running update-stacks any stack that was deployed to this account using org-formation will be deleted from the target account. Stacks that have been created by other means will not be affected.
Obviously: having a task file will do both update and update-stacks in the right sequence and you're done!
If you removed and account and want to re-add it:
Just add it back to the organization.yml. Make sure you run update and update-stacks (or perform-tasks) and your account will particapate in all bindings and the stacks will be re-deployed to the account.
As long as the account was not deleted in full org-formation will identify it by the RootEmail (or AccountId) attribute in the organization.yml
What happens when I rename an account (AccountName attribute) in org-formation?
Renaming accounts is not possible using API's. You will have to log into the account as root to change the account name in AWS.
If you change the AccountName attribute in org-formation this will warn you about the above and will, when resolving references to the account, use the account name from the organization.yml file.
What happens when I rename an account (logical name) in org-formation?
The logical name, just like with CloudFormation is how you refer to the account from within your templates. The logical account is also used as an identifier within org-formation.
If you rename an account, by its logical name, org-formation will first notice that the resource by the old logical name has gone and forget it. Later it will discover the new same account by its new logical name and match it with the physical account that already exists in AWS. It will match the two thus completing the rename.
Why is XYZ not supported?
No reason other than not running into this usecase so far.
Really happy to implement this based on someone else's usecase.
- Examples
- List of 50+ features
- Managing AWS Organizations as code
- Organization Annotated CloudFormation
- Automating deployments
- Custom Account Creation Worklow
- CLI reference
- Changelog
Special thanks to the following companies:
Special thanks to the following individuals:

