OWASP Juice Shop is an intentionally insecure web app for security trainings written entirely in Javascript which encompasses the entire OWASP Top Ten and other severe security flaws.
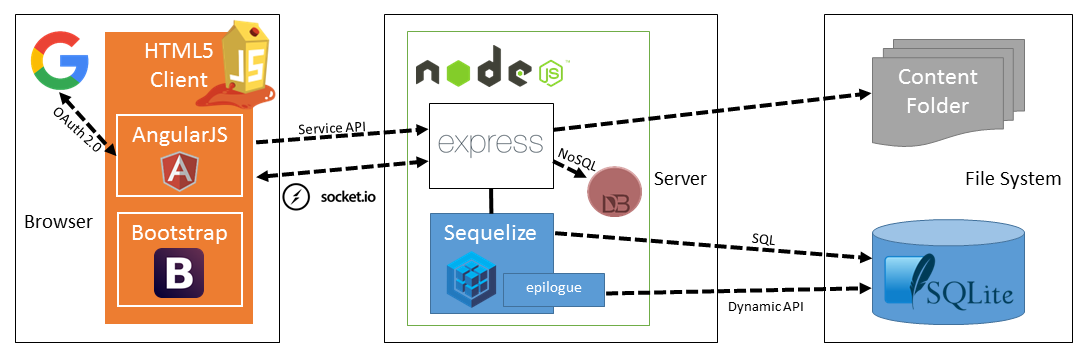
Juice Shop is written in Node.js, Express and AngularJS. It was the first application written entirely in JavaScript listed in the OWASP VWA Directory.
The application contains over 30 challenges of varying difficulty where the user is supposed to exploit the underlying vulnerabilities. The hacking progress is tracked on a score board. Finding this score board is actually one of the (easy) challenges!
Apart from the hacker and awareness training use case, pentesting proxies or security scanners can use Juice Shop as a "guinea pig"-application to check how well their tools cope with Javascript-heavy application frontends and REST APIs.
Translating "dump" or "useless outfit" into German yields "Saftladen" which can be reverse-translated word by word into "juice shop". Hence the project name. That the initials "JS" match with those of "Javascript" was purely coincidental!
- Easy-to-install: Choose between node.js, Docker and Vagrant to run on Windows/Mac/Linux
- Self-contained: Additional dependencies are pre-packaged or will be resolved and downloaded automatically
- Self-healing: The simple SQLite database is wiped and regenerated from scratch on every server startup
- Gamification: The application notifies you on solved challenges and keeps track of successfully exploited vulnerabilities on a Score Board
- CTF-support: Challenge notifications optionally show a flag code for your own Capture-The-Flag events
- Re-branding: Fully customizable business context and look & feel
- Free and Open source: Licensed under the MIT license with no hidden costs or caveats
Feel free to have a look at the latest version of OWASP Juice Shop: https://juice-shop.herokuapp.com
This is a deployment-test and sneak-peek instance only! You are not supposed to use this instance for your own hacking endeavours! No guaranteed uptime! Guaranteed stern looks if you break it!
- Click the button below and follow the instructions
This is the quickest way to get a running instance of Juice Shop! If you have forked this repository, the deploy button will automatically pick up your fork for deployment! As long as you do not perform any DDoS attacks you are free to use any tools or scripts to hack your Juice Shop instance on Heroku!
- Install node.js
- Run
git clone https://github.com/bkimminich/juice-shop.git(or clone your own fork of the repository) - Go into the cloned folder with
cd juice-shop - Run
npm install(only has to be done before first start or when you change the source code) - Run
npm start - Browse to http://localhost:3000
- Install Docker
- Run
docker pull bkimminich/juice-shop - Run
docker run -d -p 3000:3000 bkimminich/juice-shop - Browse to http://localhost:3000 (on macOS browse to http://192.168.99.100:3000 instead)
- Install and launch Docker Toolbox
- Search for
juice-shopand click Create to download image and run container - Click on the Open icon next to Web Preview to browse to OWASP Juice Shop
- Install a 64bit node.js on your Windows (or Linux) machine
- Download
juice-shop-<version>_<node-version>_<os>_x64.zip(or.tgz) attached to latest release - Unpack and run
npm startin unpacked folder - Browse to http://localhost:3000
Each packaged distribution includes some binaries for SQLite bound to the OS and node.js version which
npm installwas executed on.
- Setup an Amazon Linux AMI instance
- In Step 3: Configure Instance Details unfold Advanced Details and copy the script below into User Data
- In Step 6: Configure Security Group add a Rule that opens port 80 for HTTP
- Launch instance
- Browse to your instance's public DNS
#!/bin/bash
yum update -y
yum install -y docker
service docker start
docker pull bkimminich/juice-shop
docker run -d -p 80:3000 bkimminich/juice-shop
Technically Amazon could view hacking activity on any EC2 instance as an attack on their AWS infrastructure! We highly discourage aggressive scanning or automated brute force attacks! You have been warned!
- Install Vagrant and Virtualbox
- Run
git clone https://github.com/bkimminich/juice-shop.git(or clone your own fork of the repository) - Run
cd vagrant && vagrant up - Browse to http://juice.sh
Via a YAML configuration file in /config, the OWASP Juice Shop can be
customized in its content and look & feel. Please refer to
CUSTOMIZATION.md for detailed instructions and
examples.
OWASP Juice Shop officially supports the following versions of node.js and offers Docker images and packaged distributions accordingly:
| node.js | Docker images | Docker snapshots | Packaged distributions |
|---|---|---|---|
| 4.x | node4 |
node4-snapshot, node4-develop |
juice-shop-<version>_node4_windows_x64.zip, juice-shop-<version>_node4_linux_x64.tgz |
| 6.x | latest, node6 |
snapshot, develop, node6-snapshot, node6-develop |
juice-shop-<version>_node6_windows_x64.zip, juice-shop-<version>_node6_linux_x64.tgz |
| 7.x | node7 |
node7-snapshot, node7-develop |
juice-shop-<version>_node7_windows_x64.zip, juice-shop-<version>_node7_linux_x64.tgz |
The stable Docker images are built from
masterwhile the snapshot images are built fromdevelopbranch. The latter contain unreleased features but cannot be considered stable.
This is the official companion guide to the OWASP Juice Shop. It will give you a complete overview of the vulnerabilities found in the application including hints how to spot and exploit them. In the appendix you will even find complete step-by-step solutions to every challenge. Pwning OWASP Juice Shop is published with GitBook under CC BY-NC-ND 4.0 and is available for free in HTML, PDF, Kindle and ePub format.
- Introduction Slide Deck in HTML5
- PDF of the Intro Slide Deck on Slideshare
If you need help with the application setup please check the TROUBLESHOOTING.md or post your specific problem or question in the official Gitter Chat.
Found a bug? Crashed the app? Broken challenge? Found a vulnerability that is not on the Score Board?
Feel free to create an issue or post your ideas in the chat! Pull requests are also highly welcome - please refer to CONTRIBUTING.md for details.
Did you write a blog post, magazine article or do a podcast about or mentioning OWASP Juice Shop? Or maybe you held or joined a conference talk or meetup session, a hacking workshop or public training where this project was mentioned?
Add it to our ever-growing list of REFERENCES.md by forking and opening a Pull Request!
- On Spreadshirt.com and Spreadshirt.de you can get some swag (Shirts, Hoodies, Mugs) with the official OWASP Juice Shop logo
- On Stickermule.com you can get four variants of the OWASP Juice Shop logo to decorate your laptop
An alternative way to get stickers (and maybe even a pin-back button) is to somehow contribute to the project by fixing an issue, finding a serious bug or submitting a good idea for a new challenge! We're also happy to send some stickers your way if you organize a meetup or conference talk where you use or mention OWASP Juice Shop! Just contact the project leader to discuss your plans: bjoern.kimminich@owasp.org!
PayPal donations via above button go to the OWASP Foundations and are earmarked for "Juice Shop". This is the preferred way to support the project.
- Inspired by the "classic" BodgeIt Store by @psiinon
- Revised OWASP Juice Shop and Juice Shop CTF logo artworks by Emily Gundry (courtesy of @SecureState)
Ordered by date of first contribution. Auto-generated on Wed, 19 Apr 2017 08:32:58 GMT.
- Björn Kimminich aka
bkimminich - Bitdeli Chef aka
bitdeli-chef - The Gitter Badger aka
gitter-badger - Aaron Edwards aka
aaron-m-edwards - Alec Brooks aka
alecbrooks - Dinis Cruz aka
DinisCruz - Timo Pagel aka
wurstbrot - Gorka Vicente aka
gorkavicente - Alvaro Viebrantz aka
alvarowolfx - Johanna A aka
yuhama - Stephen OBrien aka
stephenobrien - Joe Butler aka
joelicious - Abhishek bundela aka
abhishekbundela - ninoseki
- Jannik Hollenbach aka
J12934
This program is free software: you can redistribute it and/or modify it under the terms of the MIT license. OWASP Juice Shop and any contributions are Copyright © by Bjoern Kimminich 2014-2017.