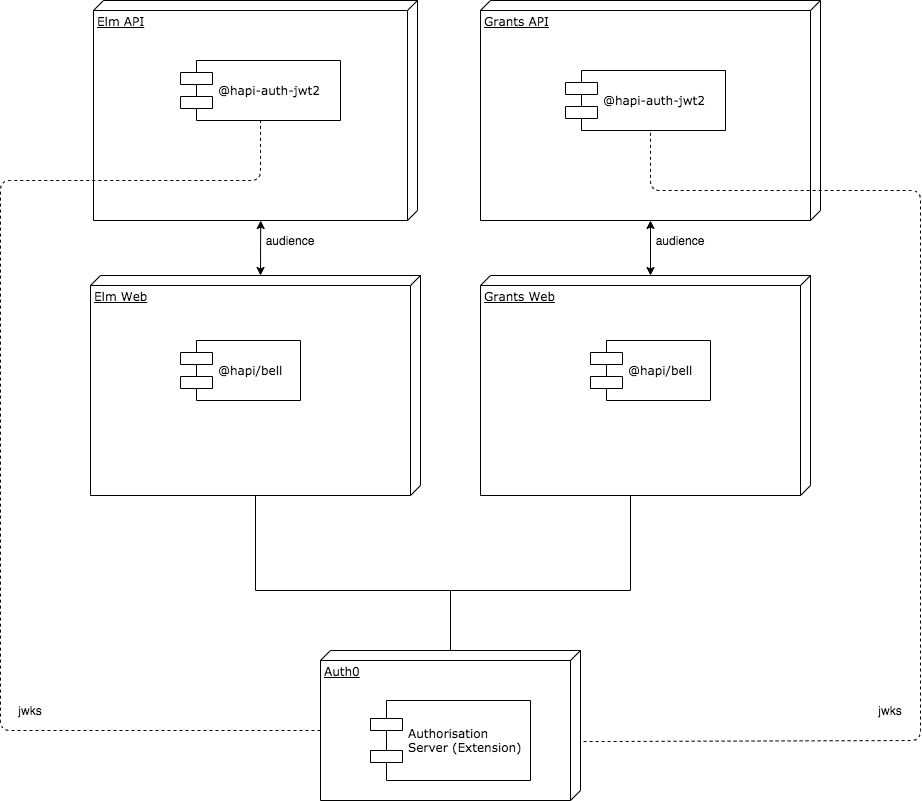
Example using auth0 and hapi to demonstrate:
- Securing two separate web applications with SSO
- Providing
access_tokenandid_tokento the application - How using the
audiencewe can use these tokens to securely call an API - How to embelish a JWT in an OpenID connect conformant way using namespaces for roles & permissions
First obtain the 4 .env files.
There are two example web servers (Elm Web and Grants Web) and two api servers (Elm API and Grants API).
$ cd web
$ npm run start:elm
$ npm run start:grants
$ cd api
$ npm run start:api
$ npm run start:grants
https://auth0.com/docs/architecture-scenarios/web-app-sso/part-1#authentication-flow
Call API Using the Authorization Code Flow
https://auth0.com/docs/flows/concepts/auth-code
Call Your API from a Regular Web App If your application executes on a server and you want to configure it to use OAuth 2.0 to access an API, read these docs.
- Overview of the flow
- Executing the flow
https://auth0.com/docs/flows/guides/auth-code/call-api-auth-code#request-tokens
- Authorize the user: Request the user's authorization and redirect back to your app with an authorization code.
- Request Tokens: Exchange your authorization code for tokens.
- Call your API: Use the retrieved Access Token to call your API.
- Refresh Tokens: Use a Refresh Token to request new tokens when the existing ones expire.
https://auth0.com/docs/api-auth/tutorials/adoption/refresh-tokens
https://auth0.com/docs/extensions/authorization-extension/v2
https://auth0.com/docs/extensions/authorization-extension/v2/rules
https://auth0.com/docs/extensions/authorization-extension/v2/implementation/configuration
https://auth0.com/docs/extensions/authorization-extension/v2#token-contents