A Cloud-Native SIEM for the Modern Security Team
Documentation | Quick Start | Blog | Chat with us on Slack!
Panther is a cloud-native platform for detecting threats with log data, improving cloud security posture, and conducting investigations.
Security teams can use Panther for:
| Use Case | Description |
|---|---|
| Continuous Monitoring | Analyze logs in real-time and identify suspicious activity that could indicate a breach |
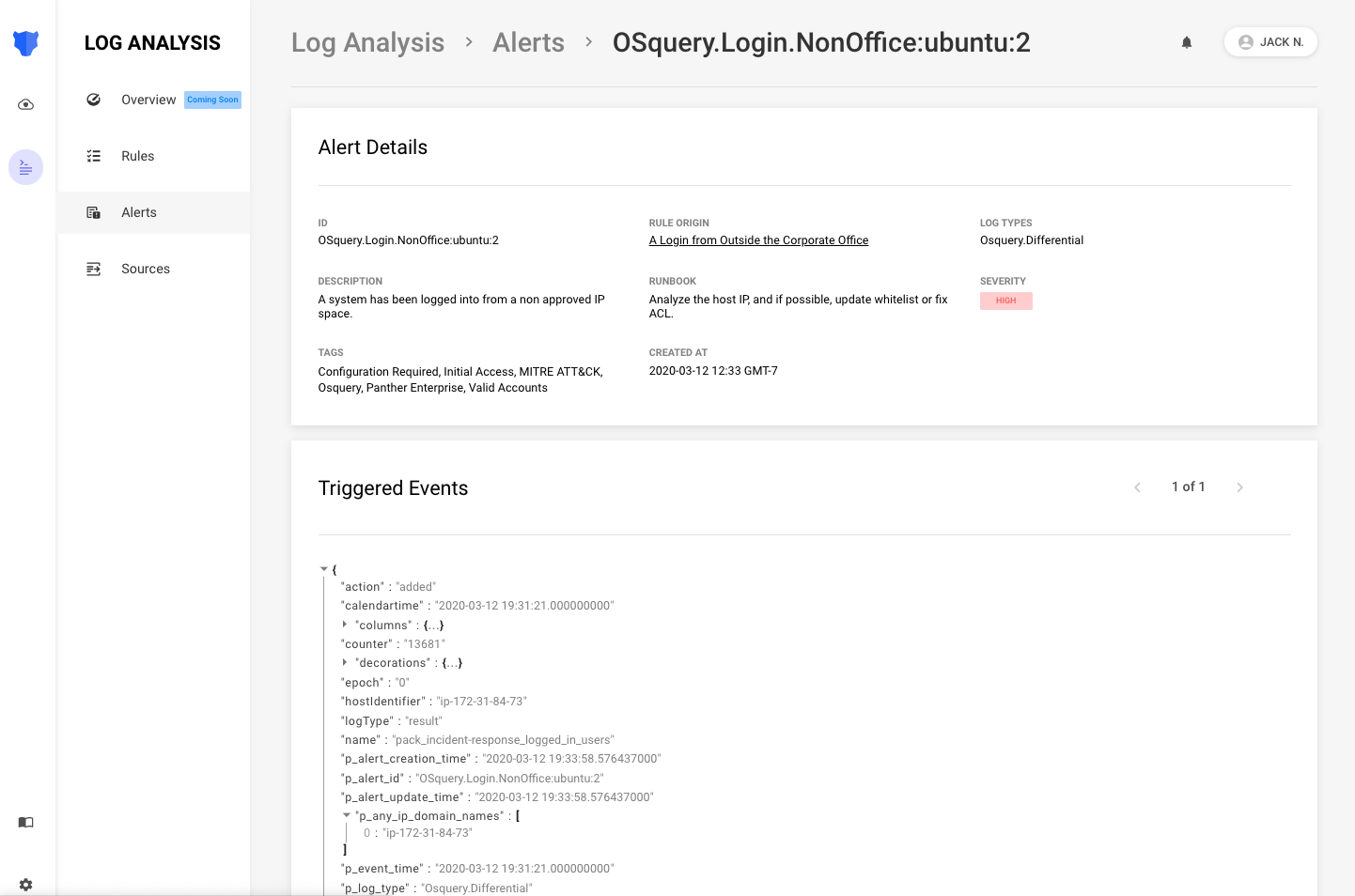
| Alert Triage | Pivot across all of your security data to understand the full context of an alert |
| Searching IOCs | Quickly search for matches against IOCs using standardized data fields |
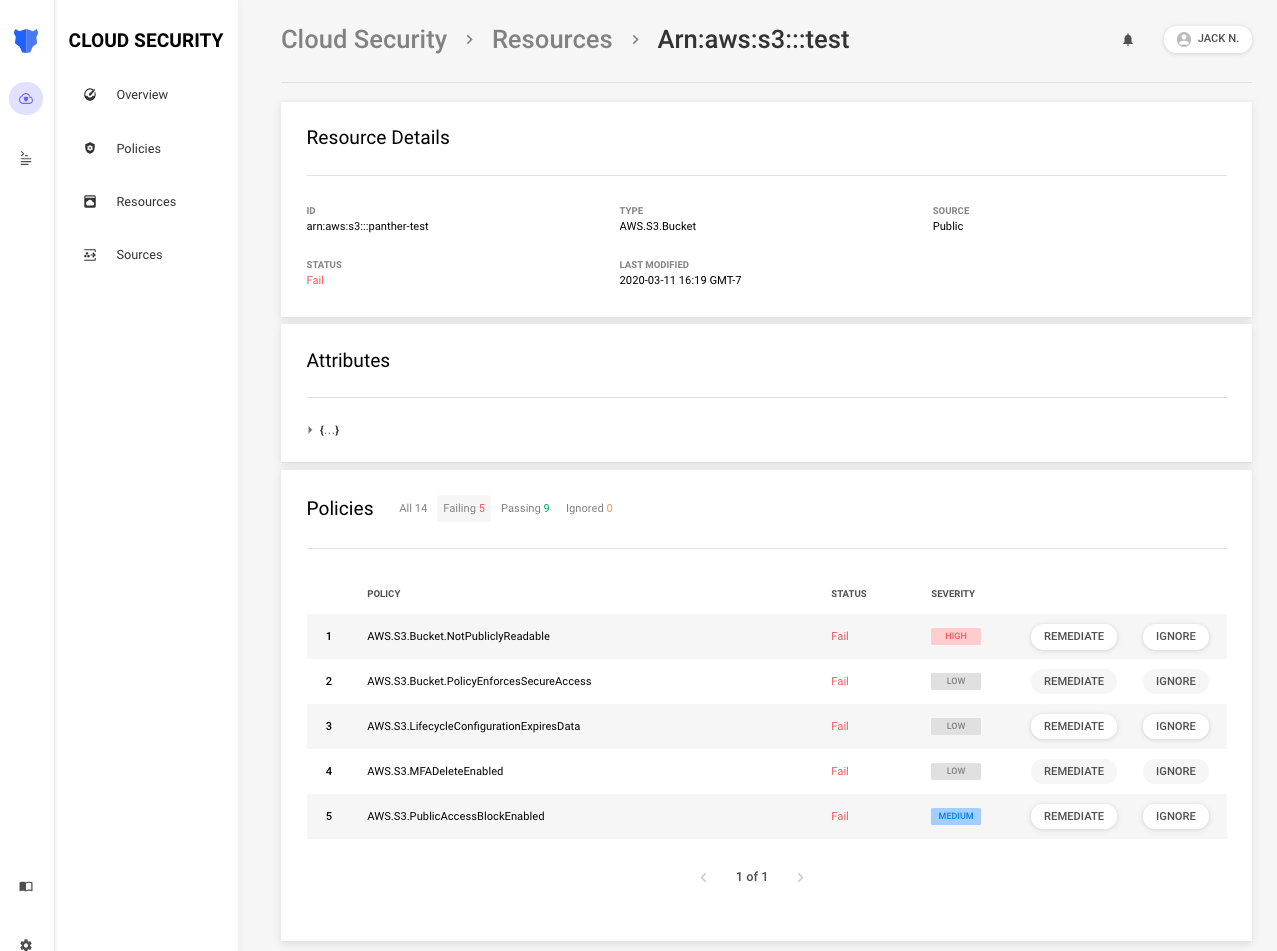
| Securing Cloud Resources | Identify misconfigurations, achieve compliance, and model security best practices in code |
Follow our Quick Start Guide to deploy Panther in your AWS account in a matter of minutes!
Use our Tutorials to learn about security logging and data ingestion.
Panther uses Python for analysis, and each deployment is pre-installed with 150+ open source detections.
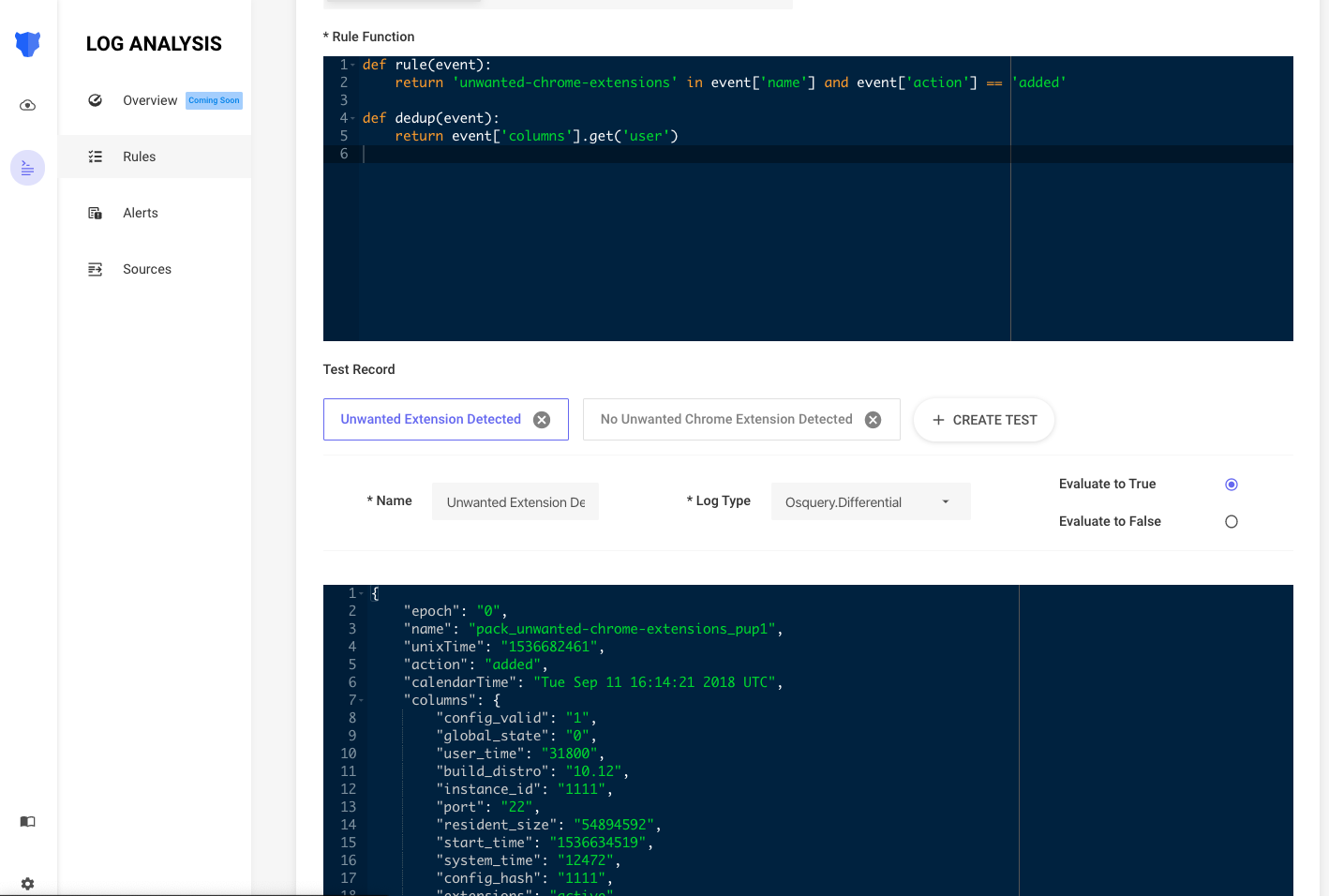
In the following example, osquery logs are analyzed to identify malware on a macOS laptop:
from fnmatch import fnmatch
APPROVED_PATHS = {'/System/*', '/usr/*', '/bin/*', '/sbin/*', '/var/*'}
def rule(event):
if 'osx-attacks' not in event.get('name'):
return False
if event.get('action') != 'added':
return False
process_path = event.get('columns', {}).get('path')
# Alert if the process is running outside any of the approved paths
return not any([fnmatch(process_path, p) for p in APPROVED_PATHS])
def title(event):
# Show the query name that caused the alert
return 'Malware [{}] detected via osquery'.format(event.get('name'))
def dedup(event):
if event.get('columns'):
# Group every similar infection in the fleet
return event.get('columns').get('path')If this rule returns True, an alert will dispatch to your team based on the defined severity.
The second analysis type is called a policy, and can be used to model security best practices on cloud resources:
REGIONS_REQUIRED = {'us-east-1'}
def policy(resource):
regions_enabled = [detector.split(':')[1] for detector in resource['Detectors']]
for region in REGIONS_REQUIRED:
if region not in regions_enabled:
return False
return TrueReturning True means that a resource is compliant, and returning False will Fail the policy and trigger an alert.
For more information on the concepts above, check out our docs:
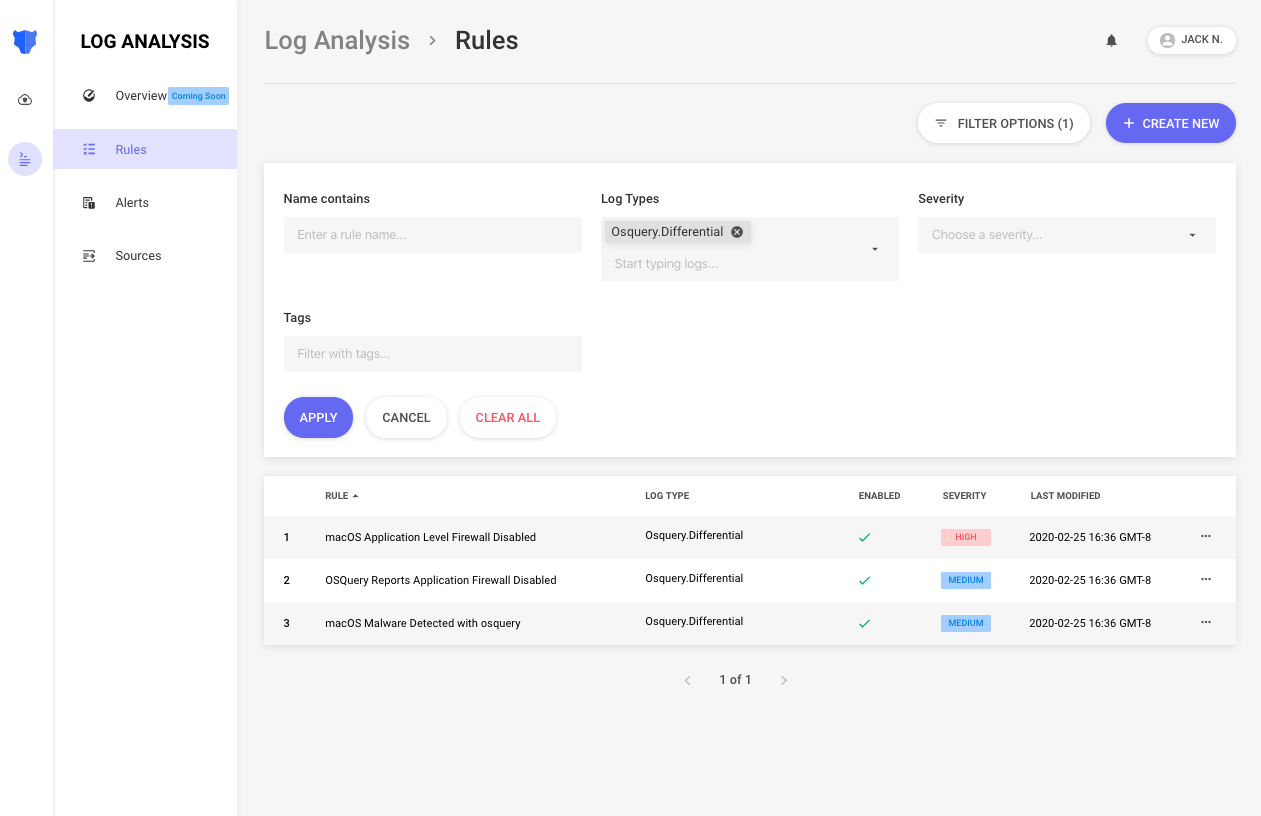
Rule Search: Show running detections
Rule Editor: Write and test Python detections in the UI
Alert Viewer: Triage generated alerts
Resource Viewer: View attributes and policy statuses
We are a San Francisco based startup comprising security practitioners who have spent years building large-scale detection and response capabilities for companies such as Amazon and Airbnb. Panther was founded by the core architect of StreamAlert, a cloud-native solution for automated log analysis open-sourced by Airbnb.
It's no longer feasible to find the needle in the security-log-haystack manually. Many teams struggle to use traditional SIEMs due to their high costs, overhead, and inability to scale. Panther was built from the ground up to leverage the elasticity of cloud services and provide a highly scalable, performant, and flexible security solution at a much lower cost.
We welcome all contributions! Please read the contributing guidelines before submitting pull requests.
Panther is dual-licensed under the AGPLv3 and Apache-2.0 licenses.
Thanks goes to these wonderful people (emoji key):
This project follows the all-contributors specification. Contributions of any kind welcome!