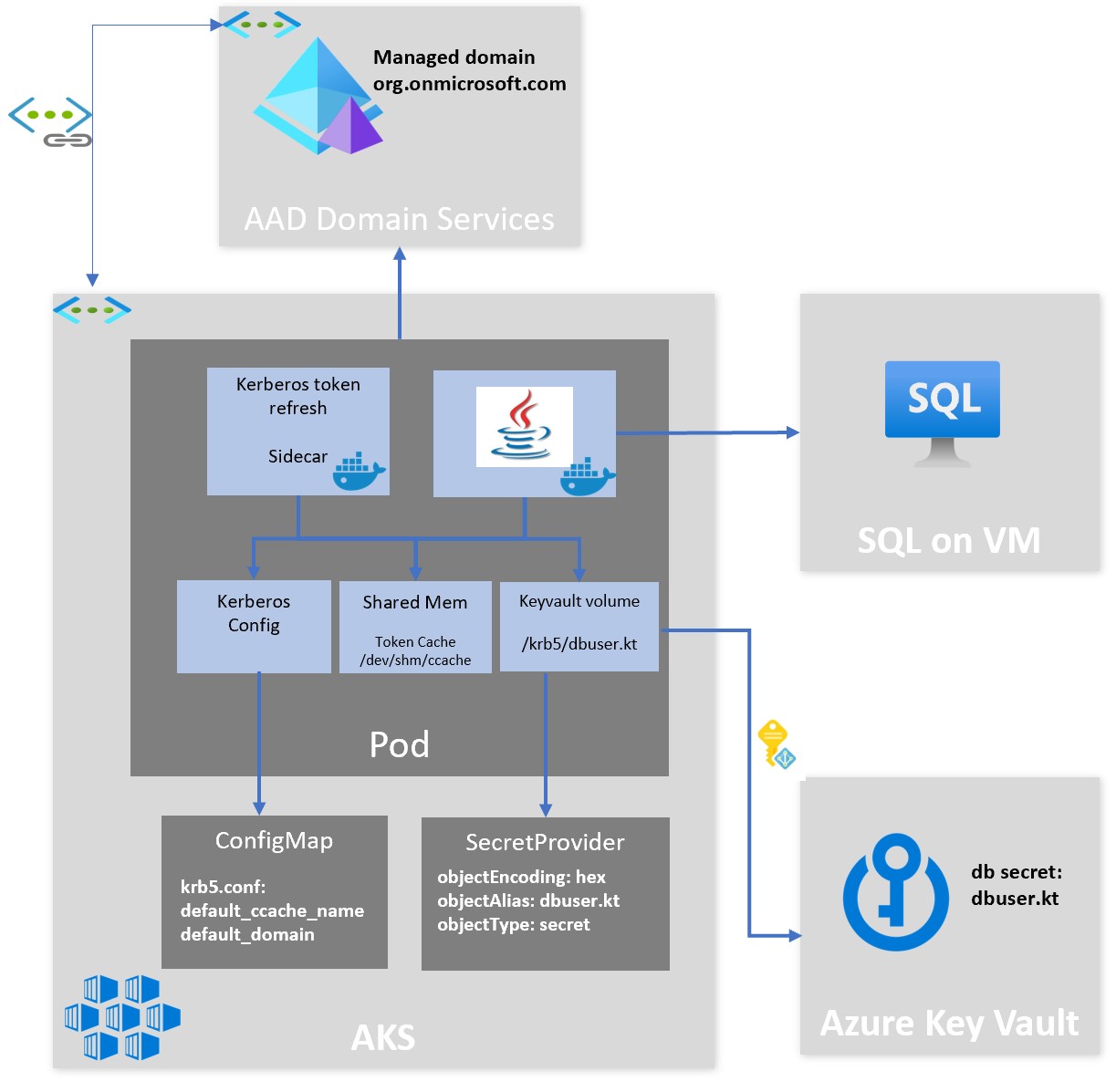
Setup for the following Architecture
- create user in Azure AD for Managed Domain tenant
- Grant access to user in
testdb
CREATE LOGIN [ENEROSORG\dbuser] FROM WINDOWS
CREATE USER [ENEROSORG\dbuser] FOR LOGIN [ENEROSORG\dbuser];
ALTER ROLE db_owner ADD MEMBER [ENEROSORG\dbuser];
kinit -V eneros@ENEROSORG.ONMICROSOFT.COM
----------------------------------------------------------------------------------
Using default cache: /tmp/krb5cc_1000
Using principal: dbuser@ENEROSORG.ONMICROSOFT.COM
Password for dbuser@ENEROSORG.ONMICROSOFT.COM:
Authenticated to Kerberos v5
- Run SQL command
sqlcmd -E -S SQLIAASEN.ENEROSORG.ONMICROSOFT.COM -d testdb -Q "SELECT SUSER_SNAME();"
----------------------------------------------------------------------------------
ENEROSORG\dbuser
sudo apt-get update
sudo apt-get install krb5-user samba sssd sssd-tools libnss-sss libpam-sss ntp ntpdate realmd adcli
ktutil: addent -password -p dbuser@ENEROSORG.ONMICROSOFT.COM -k 2 -e aes128-cts-hmac-sha1-96
ktutil: wkt dbuser.keytabsudo kinit -V -kt dbuser.keytab dbuser
Using default cache: /tmp/krb5cc_1000
Using principal: dbuser@ENEROSORG.ONMICROSOFT.COM
Using keytab: dbuser.keytab
Authenticated to Kerberos v5
sqlcmd -E -S SQLIAASEN.ENEROSORG.ONMICROSOFT.COM -d testdb -Q "SELECT SUSER_SNAME();"
---------------------------------------------------------------------------------------
ENEROSORG\dbuser Our example uses JDBS driver java implemetation for integrated authentication with the Java Krb5LoginModule.
we specify integratedSecurity=true and authenticationScheme=JavaKerberos connection properties.
mvn clean compile assembly:single
export KRB5CCNAME=/tmp/krb5cc_1000 sudo java -jar target/sql-kerberos-jar-with-dependencies.jar
- build docker images
docker build -t sql-kerberos:1.0 .
docker tag sql-kerberos:1.0 acraccess.azurecr.io/sql-kerberos:1.0
docker push acraccess.azurecr.io/sql-kerberos:1.0
or
az acr build -r acraccess --image sql-kerberos:1.0 -f containers/dbapp/Dockerfile .
cd containers/sidecar
az acr build -r acraccess --image kinit-sidecar:1.0 .
- create secret with keytab data
kubectl create secret generic keytab --from-file=./dbuser.keytab
- create configmap with kerberos config
kubectl create cm krb5config --from-file=./containers/krb5.conf
- create pod with two containers - sidecar running kinit to refresh ticket and application
kubectl apply -f containers/k8s-manifest.yaml
- verify logs
k logs kinit-dbapp -c kinit --tail=20
*** Waiting for 10 seconds
*** kinit at +2021-12-24 + kinit -V -k dbuser@ENEROSORG.ONMICROSOFT.COM
Using default cache: /dev/shm/ccache
Using principal: dbuser@ENEROSORG.ONMICROSOFT.COM
Authenticated to Kerberos v5
Ticket cache: FILE:/dev/shm/ccache
Default principal: dbuser@ENEROSORG.ONMICROSOFT.COM
Valid starting Expires Service principal
12/24/21 05:36:25 12/24/21 15:36:25 krbtgt/ENEROSORG.ONMICROSOFT.COM@ENEROSORG.ONMICROSOFT.COM
renew until 12/31/21 05:36:25
*** Waiting for 10 seconds
k logs kinit-dbapp -c dbapp --tail=10
Authenticated User: ENEROSORG\dbuser
Authenticated User: ENEROSORG\dbuser
Authenticated User: ENEROSORG\dbuser
Authenticated User: ENEROSORG\dbuser
az keyvault secret set --name dbuserkt --vault-name kvforkeytab --file dbuser.keytab --encoding hex
k create configmap dbconfig --from-literal=SQL-SERVER=SQLIAASEN.ENEROSORG.ONMICROSOFT.COM --from-literal=DB-NAME=testdb
Join an Ubuntu Linux virtual machine to an Azure Active Directory Domain Services managed domain
Connecting a SQL Server client on Linux using Active Directory authentication
Linux to Windows Authentication Linux to Windows Authentication GitHub
Kerberos Sidecar Container Kerberos Sidecar Container Github
Using Kerberos integrated authentication to connect to SQL Server
Register a Service Principal Name for Kerberos Connections
AD(Active Directory) authentication for SQL Containers on Azure Kubernetes Service (AKS)