This project contains an reference implementation for a CI/CD pipeline for Apigee using the Apigee Deploy Maven Plugin.
The CICD pipeline consists of:
- Git branch dependent Apigee environment selection and proxy naming to allow deployment of feature branches as separate proxies in the same environment
- Static code analysis using eslint
- Unit testing using mocha
- Integration testing of the deployed proxy using apickli
- Packaging and deployment of the API proxy bundle using Apigee Deploy Maven Plugin
-
Install dependencies:
npm install
-
Unit testing:
npm run unit-test
-
Integration testing against host
$APIGEE_ORG-$APIGEE_ENV.apigee.netand default basepathairports-cicd/v1:TEST_HOST=$APIGEE_ORG-$APIGEE_ENV.apigee.net npm run integration-test
-
Integration testing against feature branch deployment on
airports-cicd-feature-ABC/v1:TEST_HOST=$APIGEE_ORG-$APIGEE_ENV.apigee.net TEST_BASE_PATH='/ airports-cicd-feature-ABC/v1' npm run integration-test
The instructions below explain how to trigger an Apigee CI/CD pipeline manually via the gcloud command. You can obviously also configure Cloud Build triggers on your SCM tool to automatically trigger a deployment.
Requires the Cloud Build API to be enabled and a Service Account with the following roles (or a custom role with all required permissions):
- Apigee API Admin
- Apigee Environment Admin
gcloud services enable cloudbuild.googleapis.com
PROJECT_ID=$(gcloud config get-value project)
PROJECT_NUMBER=$(gcloud projects describe $PROJECT_ID --format="value(projectNumber)")
CLOUD_BUILD_SA="$PROJECT_NUMBER@cloudbuild.gserviceaccount.com"
gcloud projects add-iam-policy-binding "$PROJECT_ID" \
--member="serviceAccount:$CLOUD_BUILD_SA" \
--role="roles/apigee.environmentAdmin"
gcloud projects add-iam-policy-binding "$PROJECT_ID" \
--member="serviceAccount:$CLOUD_BUILD_SA" \
--role="roles/apigee.apiAdmin"Run the following command to trigger a cloud build manually:
gcloud builds submit --config=./ci-config/cloudbuild/cloudbuild.yaml \
--substitutions=_API_VERSION=google,_DEPLOYMENT_ORG=$PROJECT_ID,_INT_TEST_HOST=api.my-host.example.com,_INT_TEST_BASE_PATH=/airports-cicd-experiment/v1,BRANCH_NAME=experimentRequires the Cloud Build API to be enabled and a Service Account with the following role:
- Secret Manager Secret Accessor
gcloud services enable secretmanager.googleapis.com cloudbuild.googleapis.com
PROJECT_ID=$(gcloud config get-value project)
PROJECT_NUMBER=$(gcloud projects describe $PROJECT_ID --format="value(projectNumber)")
CLOUD_BUILD_SA="$PROJECT_NUMBER@cloudbuild.gserviceaccount.com"
gcloud projects add-iam-policy-binding "$PROJECT_ID" \
--member="serviceAccount:$CLOUD_BUILD_SA" \
--role="roles/secretmanager.secretAccessor"To pass the Apigee user and password securely into the Cloud Build pipeline you have to add these two secrets to the cloud secret manager:
devrel_apigee_userthat holds the user to use for the CI/CD accountdevrel_apigee_passthat holds the password for the CI/CD account
echo "$APIGEE_USER" | gcloud secrets create devrel_apigee_user --data-file=-
echo "$APIGEE_PASS" | gcloud secrets create devrel_apigee_pass --data-file=-Run the deployment (with a simulated git branch name)
gcloud builds submit --config=./ci-config/cloudbuild/cloudbuild.yaml --substitutions=_API_VERSION=apigee,_INT_TEST_HOST=$APIGEE_ORG-$APIGEE_ENV.apigee.net,_INT_TEST_BASE_PATH=/airports-cicd-experiment/v1,_DEPLOYMENT_ORG=$APIGEE_ORG,BRANCH_NAME=experimentYou can either use the included instructions to configure a new Jenkins server
or use your existing infrastructure. The jenkins-build folder contains instructions
on how to set up a dockerized Jenkins environment with all the necessary
tooling and plugins required.
See the instructions in ./jenkins-build/README.md.
If you already have a current (version 2.200+) Jenkins instance you can also use that one.
You are responsible to ensure you have the following plugins enabled:
Start or configure your Jenkins server as described above.
Create a Git repository to hold your API Proxy. To use the cicd-pipeline
in a Github repository github.com/my-user/my-api-proxy-repo follow these
steps:
cd devrel/references/cicd-pipeline
git init
git remote add origin git@github.com:my-user/my-api-proxy.git
git checkout -b feature/cicd-pipeline
git add .
git commit -m "initial commit"
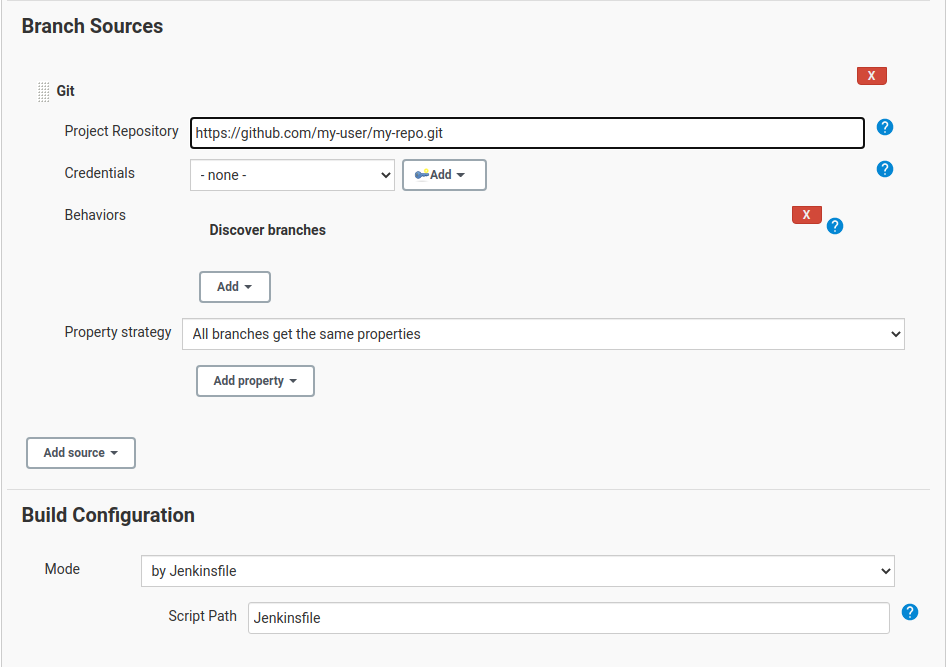
git push -u origin feature/cicd-pipelineUse the UI to configure the Jenkins Job for multibranch pipelines:
- Set the Git repo e.g.
https://github.com/my-user/my-api-proxy-repo - Path to the Jenkinsfile e.g.
ci-config/jenkins/Jenkinsfile - (Optional) Set the build trigger / polling frequency
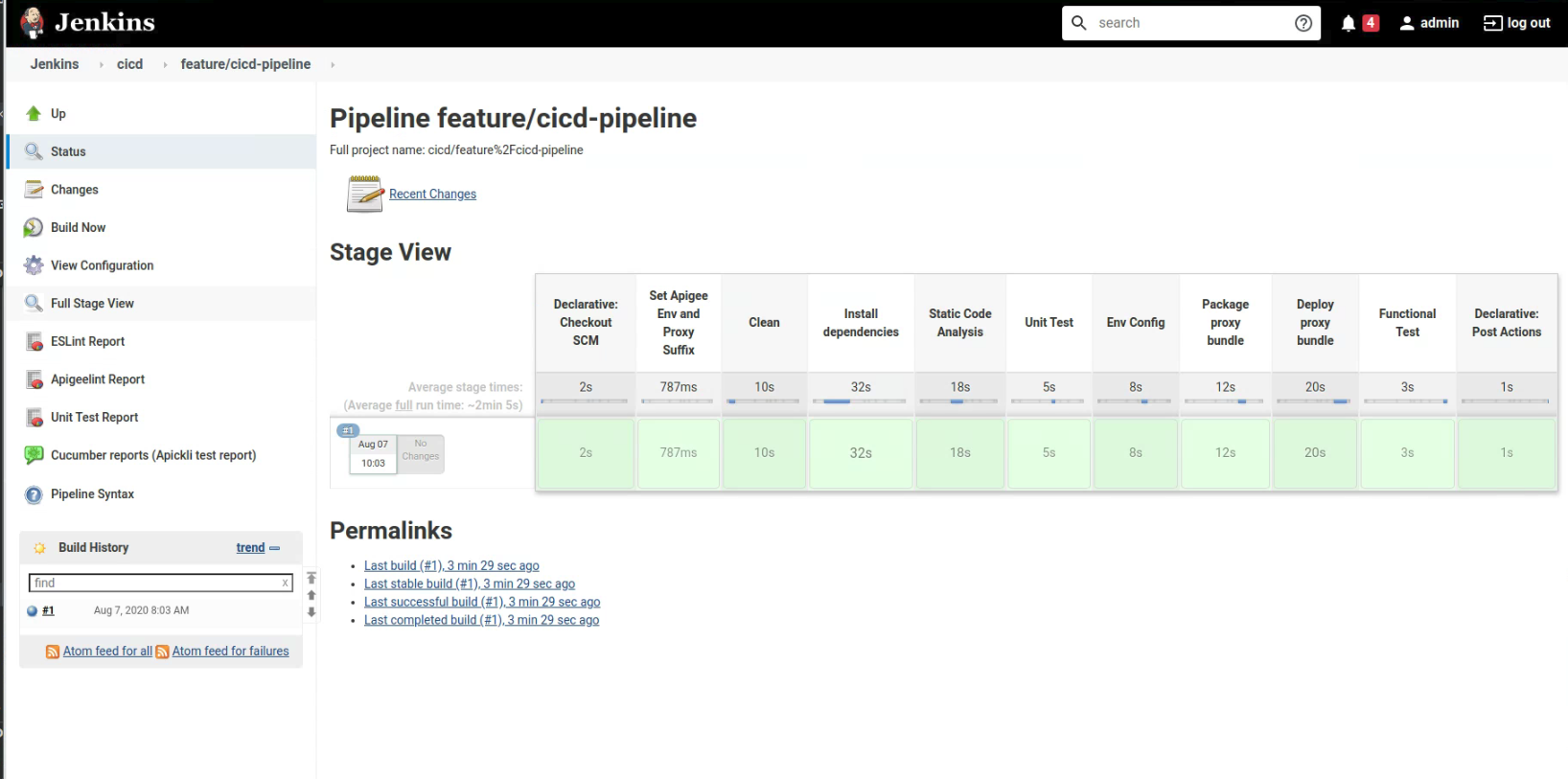
- Open the multi-branch pipeline you just created.
- Click
Scan Multibranch Pipeline Nowto detect branches with a Jenkinsfile. - Explore the build(s) that get triggered.
- Explore the final build success.
- Explore the newly created api-proxy in the test environment that corresponds to the feature branch
- Merge the feature branch into
mainbranch and explore the promotion into the Apigee test environment - Merge the
mainbranch into theprodbranch and explore the promotion into the Apigee prod environment
- The authentication to the Apigee management API is done using OAuth2. If you require MFA, please see the documentation for the Maven deploy plugin for how to configure MFA.