tfsec uses static analysis of your terraform templates to spot potential security issues. Now with terraform v0.12+ support.
Install with brew/linuxbrew:
brew install tfsecInstall with Chocolatey:
choco install tfsecYou can also grab the binary for your system from the releases page.
Alternatively, install with Go:
go get -u github.com/tfsec/tfsec/cmd/tfsectfsec will scan the specified directory. If no directory is specified, the current working directory will be used.
The exit status will be non-zero if tfsec finds problems, otherwise the exit status will be zero.
tfsec .As an alternative to installing and running tfsec on your system, you may run tfsec in a Docker container.
There are a number of Docker options available
| Image Name | Base | Comment |
|---|---|---|
| tfsec/tfsec | alpine | Normal tfsec image |
| tfsec/tfsec-alpine | alpine | Exactly the same as tfsec/tfsec, but for those whole like to be explicit |
| tfsec/tfsec-ci | alpine | tfsec with no entrypoint - useful for CI builds where you want to override the command |
| tfsec/tfsec-scratch | scratch | An image built on scratch - nothing frilly, just runs tfsec |
To run:
docker run --rm -it -v "$(pwd):/src" liamg/tfsec /srcIf you want to run tfsec on your repository as a GitHub Action, you can use https://github.com/triat/terraform-security-scan.
- Checks for sensitive data inclusion across all providers
- Checks for violations of AWS, Azure and GCP security best practice recommendations
- Scans modules (currently only local modules are supported)
- Evaluates expressions as well as literal values
- Evaluates Terraform functions e.g.
concat()
You may wish to ignore some warnings. If you'd like to do so, you can
simply add a comment containing tfsec:ignore:<RULE> to the offending
line in your templates. If the problem refers to a block of code, such
as a multiline string, you can add the comment on the line above the
block, by itself.
For example, to ignore an open security group rule:
resource "aws_security_group_rule" "my-rule" {
type = "ingress"
cidr_blocks = ["0.0.0.0/0"] #tfsec:ignore:AWS006
}...or...
resource "aws_security_group_rule" "my-rule" {
type = "ingress"
#tfsec:ignore:AWS006
cidr_blocks = ["0.0.0.0/0"]
}If you're not sure which line to add the comment on, just check the tfsec output for the line number of the discovered problem.
You can ignore multiple rules by concatenating the rules on a single line:
#tfsec:ignore:AWS017 tfsec:ignore:AWS002
resource "aws_s3_bucket" "my-bucket" {
bucket = "foobar"
acl = "private"
}You may wish to exclude some checks from running. If you'd like to do so, you can
simply add new argument -e CHECK1,CHECK2,etc to your cmd command
tfsec . -e GEN001,GCP001,GCP002You can include values from a tfvars file in the scan, using, for example: --tfvars-file terraform.tfvars.
Checks are currently limited to AWS/Azure/GCP resources, but there are also checks which are provider agnostic.
| Checks |
|---|
| AWS Checks |
| Azure Checks |
| GCP Checks |
| General Checks |
tfsec is designed for running in a CI pipeline. For this reason it will
exit with a non-zero exit code if a potential problem is detected.
You may wish to run tfsec as part of your build without coloured
output. You can do this using --no-colour (or --no-color for our
American friends).
You can output tfsec results as JSON, CSV, Checkstyle, Sarif, JUnit or just plain old human readable format. Use the --format flag
to specify your desired format.
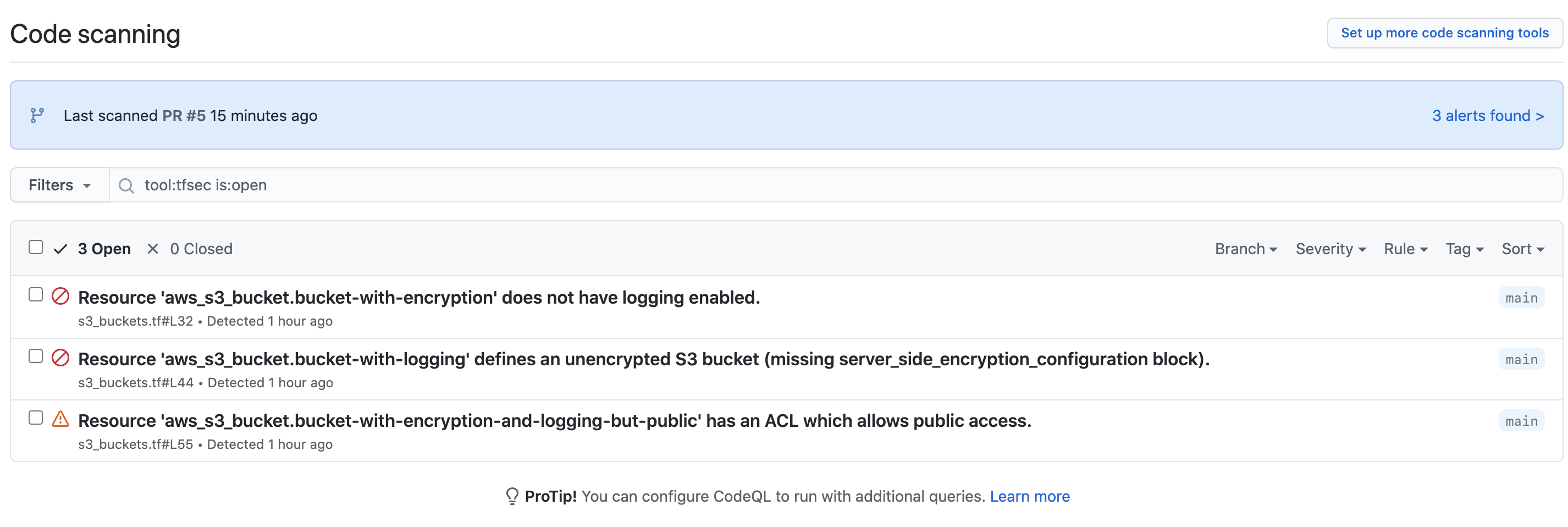
If you want to integrate with Github Security alerts and include the output of your tfsec checks you can use the tfsec-sarif-action Github action to run the static analysis then upload the results to the security alerts tab.
The alerts generated for tfsec-example-project look like this.
When you click through the alerts for the branch, you get more information about the actual issue.
For more information about adding security alerts, check
If you need to support versions of terraform which use HCL v1
(terraform <0.12), you can use v0.1.3 of tfsec, though support is
very limited and has fewer checks.