Azure Virtual Machine (VM) with Just-in-Time access.
You'll need to enable Microsoft Defender for Servers for the Subscription.
Tip
Entra ID P2 license is also required for PIM
Make sure you enable Cloud Workload Protection (CWP) for Servers. After that, install the agents using the Portal just for completeness.
Create the .auto.tfvars file and set the required parameters:
cp config/template.tfvars .auto.tfvarsCreate the temporary keys:
mkdir .keys && ssh-keygen -f .keys/temp_rsaStart by creating the sandbox infrastructure:
terraform init
terraform apply -auto-approveTip
If you get the error 'LinuxJITPolicy' is not onboarded to Defender For Servers offering., add the server to Defender and apply again to finish the setup.
If everything goes right, the JIT policy will automatically be created to the VM by the Terraform AzApi provider.
Permissions required are:
Microsoft.Security/locations/jitNetworkAccessPolicies/initiate/actionMicrosoft.Compute/virtualMachines/read
To be able to login with Entra ID credentials, users must have one of:
Virtual Machine Administrator LoginVirtual Machine User Login
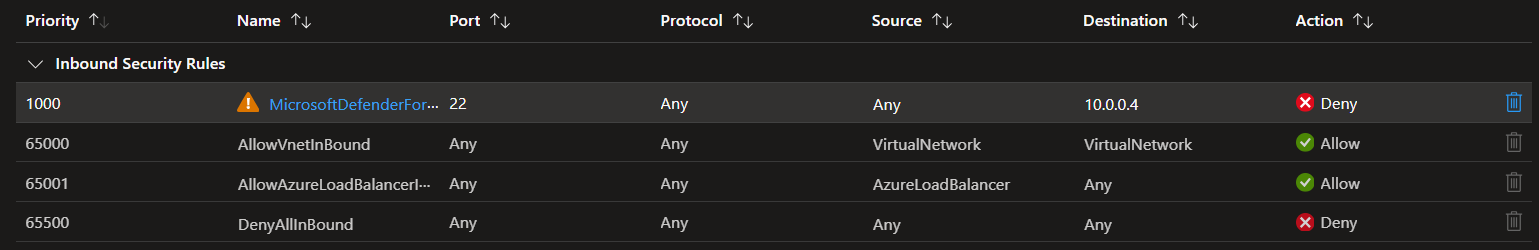
Defender should have created the following Deny rule:
Now request your JIT access.
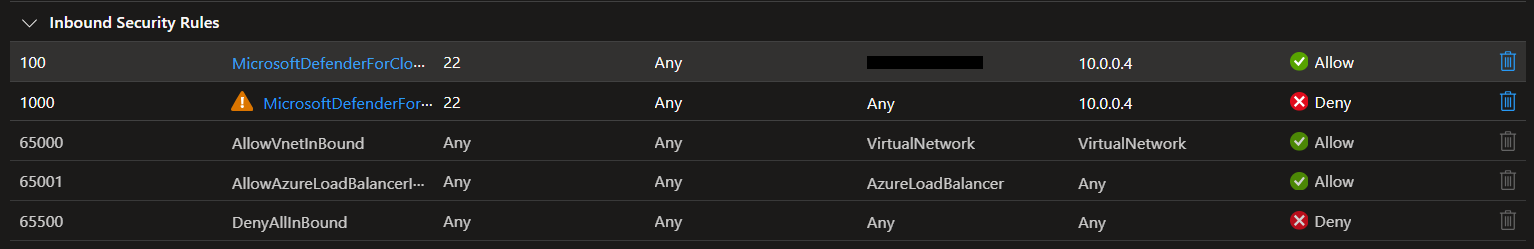
Defender should create the following Allow rule:
It is possible to extend VM management capabilities using the VMAccess extension.
To install the extension using Terraform:
# VMAccess
install_vmaccess_extension = trueTo check for deployed extensions and the installation status:
az vm extension list \
--resource-group <resource-group> \
--vm-name <vm-name> -o tableDon't forget to disable Microsoft Defender if you're only testing.
Destroy the infrastructure:
terraform destroy -auto-approve