This exercise will demonstrate deployability of resources based on subnet status.
Create the base resources:
terraform init
terraform apply -auto-approveTo enabled advanced monitoring capabilities, such as the Connection Monitor, use the Network Watcher Agent.
This project already installs the agent by default.
You can enable the Connection Monitor from the Azure Monitor Insights section for the Network blade.
The following subnets will be created within the VNET:
| Subnet | Is empty? | Service Endpoint | Subnet Delegation |
|---|---|---|---|
| Subnet001 | No | - | - |
| Subnet002 | Yes | Microsoft.Storage |
- |
| Subnet003 | Yes | - | Microsoft.Sql/managedInstances |
| Subnet004 | Yes | - | Microsoft.Web/serverFarms |
| Subnet005 | Yes | - | - |
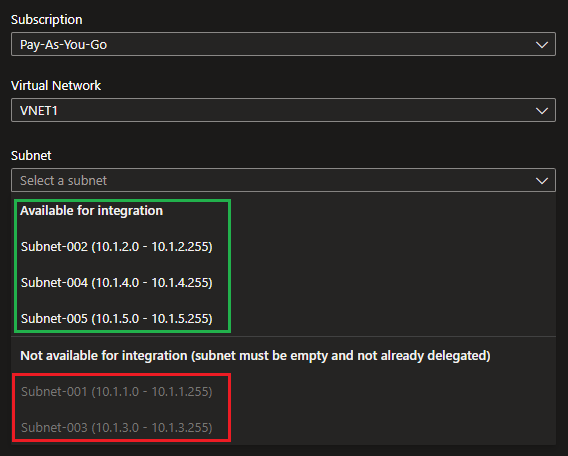
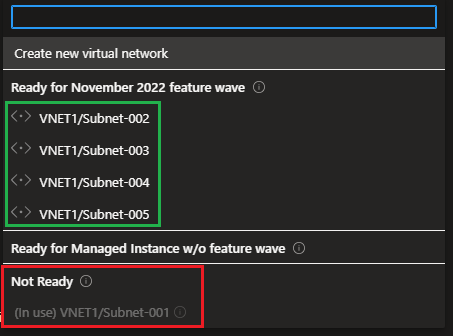
The results are interesting when looking at Subnet003.
When integrating services to subnets, we get different outputs:
| Service | Subnet 1 | Subnet 2 | Subnet 3 | Subnet 4 | Subnet 5 |
|---|---|---|---|---|---|
| App Service | ❌ | ✅ | ❌ | ✅ | ✅ |
| SQL MAnaged Instance | ❌ | ✅ | ✅ | ✅ | ✅ |
Requirements for App Service:
Requirements for SQL Managed Instance:
All network interfaces assigned to an application security group have to exist in the same virtual network that the first network interface assigned to the application security group is in. For example, if the first network interface assigned to an application security group named AsgWeb is in the virtual network named VNet1, then all subsequent network interfaces assigned to ASGWeb must exist in VNet1. You can't add network interfaces from different virtual networks to the same application security group.
Here're some commands to test ASGs.
Although not mentioned explicitly, you cannot use an ASG created in a different region.
# Creating in different regions to test compatibility
# You can add this one
az network asg create -g rg-test001 -n asg-test001-eastus2 -l eastus2
# You CANNOT add this one as it is from a different region
az network asg create -g rg-test001 -n asg-test001-brazilsouth -l brazilsouthDestroy the resources after using it:
terraform destroy -auto-approve