Generic Signature Format for SIEM Systems
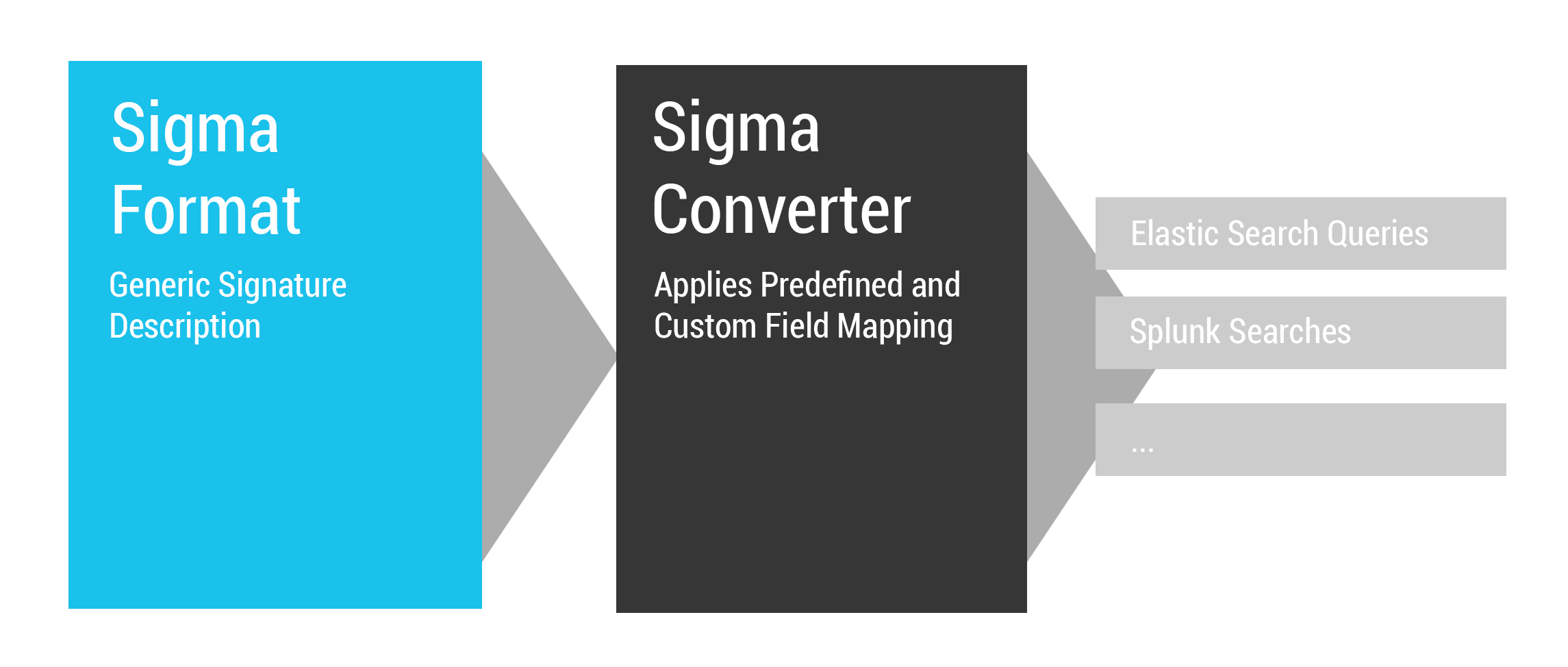
Sigma is a generic and open signature format that allows you to describe relevant log events in a straightforward manner. The rule format is very flexible, easy to write and applicable to any type of log file. The main purpose of this project is to provide a structured form in which researchers or analysts can describe their once developed detection methods and make them shareable with others.
Sigma is for log files what Snort is for network traffic and YARA is for files.
This repository contains:
- Sigma rule specification in the Sigma-Specification repository
- Open repository for sigma signatures in the
./rulessubfolder
The SANS webcast on Sigma contains a very good 20 min introduction to the project by John Hubbart from minute 39 onward. (SANS account required; registration is free)
MITRE ATT&CK® and Sigma Alerting Webcast Recording
- Describe your detection method in Sigma to make it shareable
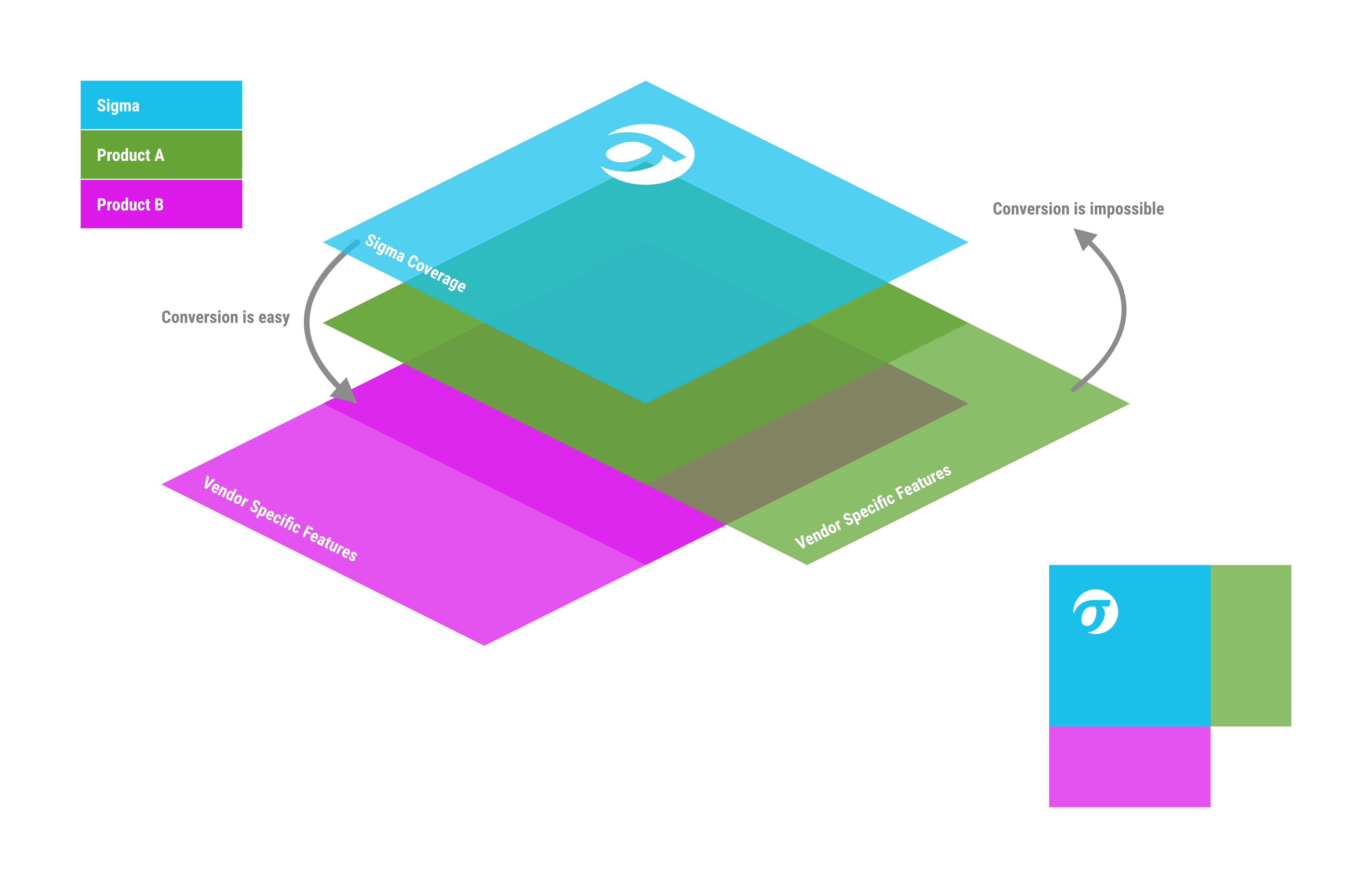
- Write your SIEM searches in Sigma to avoid a vendor lock-in
- Share the signature in the appendix of your analysis along with IOCs and YARA rules
- Share the signature in threat intel communities - e.g. via MISP
- Provide Sigma signatures for malicious behaviour in your own application
Today, everyone collects log data for analysis. People start working on their own, processing numerous white papers, blog posts and log analysis guidelines, extracting the necessary information and build their own searches and dashboard. Some of their searches and correlations are great and very useful but they lack a standardized format in which they can share their work with others.
Others provide excellent analyses, include IOCs and YARA rules to detect the malicious files and network connections, but have no way to describe a specific or generic detection method in log events. Sigma is meant to be an open standard in which such detection mechanisms can be defined, shared and collected in order to improve the detection capabilities for everyone.
See the first slide deck that I prepared for a private conference in mid January 2017.
Sigma - Make Security Monitoring Great Again
The specifications can be found in the Sigma-Specification repository.
The current specification is a proposal. Feedback is requested.
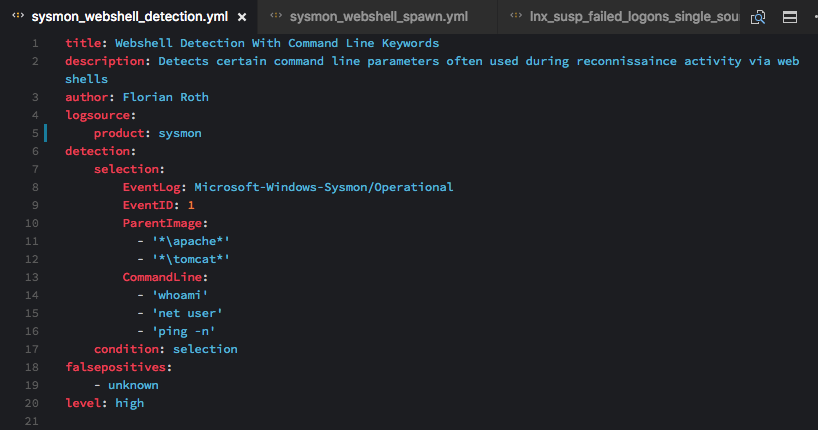
Florian wrote a short rule creation tutorial that can help you getting started. Use the Rule Creation Guide in our Wiki for a clear guidance on how to populate the various field in Sigma rules.
- Use Sigma CLI to convert your rules into queries.
- Use pySigma to integrate Sigma in your own toolchain or product.
- Check out the legacy sigmatools and sigmac if your target query language is not yet supported by the new toolchain. Please be aware that the legacy sigmatools are not maintained anymore and some of the backends don't generate correct queries.
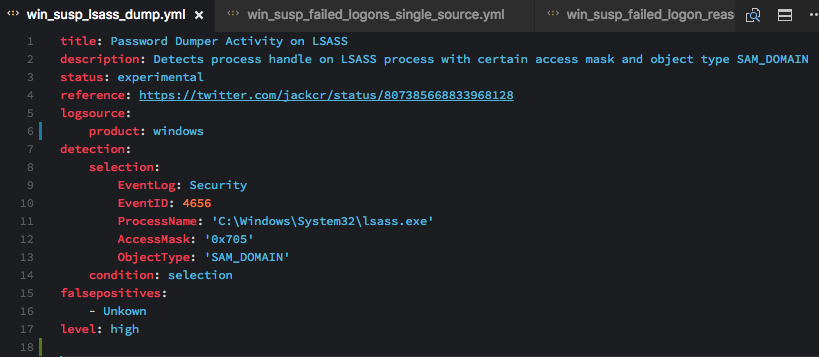
Windows 'Security' Eventlog: Access to LSASS Process with Certain Access Mask / Object Type (experimental)
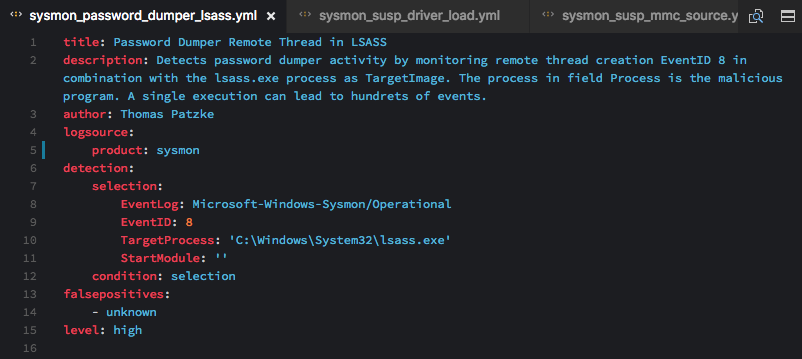
Sysmon: Remote Thread Creation in LSASS Process
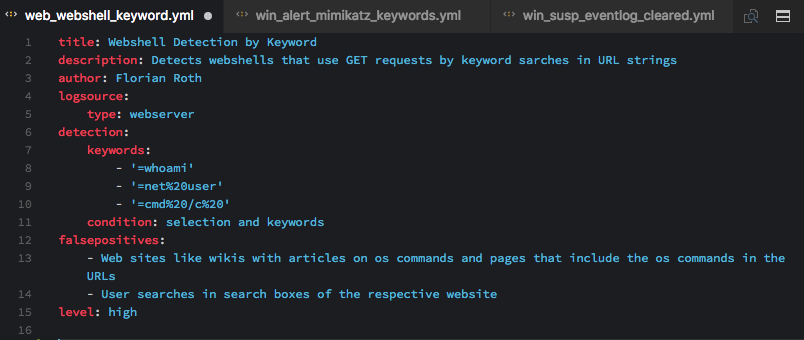
Web Server Access Logs: Web Shell Detection
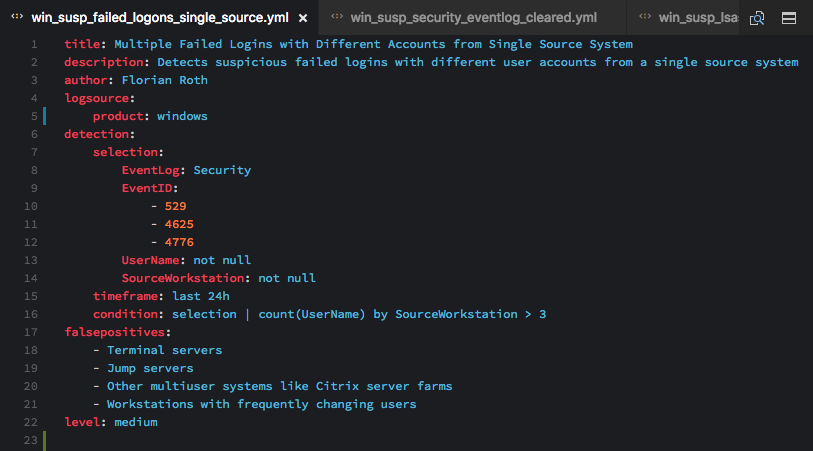
Windows 'Security' Eventlog: Suspicious Number of Failed Logons from a Single Source Workstation
- MISP (since version 2.4.70, March 2017)
- Atomic Threat Coverage (since December 2018)
- SOC Prime - Sigma Rule Editor
- uncoder.io - Online Translator for SIEM Searches
- THOR - Scan with Sigma rules on endpoints
- Joe Sandbox
- ypsilon - Automated Use Case Testing
- RANK VASA
- TA-Sigma-Searches (Splunk App)
- TimeSketch
- SIΣGMA - SIEM consumable generator that utilizes Sigma for query conversion
- Aurora Agent
- Confluent Sigma
- SEKOIA.IO - XDR supporting Sigma and Sigma Correlation rules languages
Sigma is available in some Linux distribution repositories:
If you want to contribute, you are more then welcome. There are numerous ways to help this project.
If you use it, let us know what works and what does not work.
E.g.
- Tell us about false positives (issues section)
- Try to provide an improved rule (new filter) via pull request on that rule
The github issue tracker is a good place to start tackling some issues others raised to the project. It could be as easy as a review of the documentation.
Please don't provide backends for the old code base (sigmac) anymore. Please use the new pySigma. We are working on a documentation on how to write new backends for that new code base. An example backend for Splunk can be found here.
Last but not least, the more people use Sigma, the better, so help promote it by sharing it via social media. If you are using it, consider giving a talk about your journey and tell us about it.
The content of this repository is released under the following licenses:
- The Sigma Specification and the Sigma logo are public domain
- The rules contained in the SigmaHQ repository are released under the Detection Rule License (DRL) 1.1
This is a private project mainly developed by Florian Roth and Thomas Patzke with feedback from many fellow analysts and friends. Rules are our own or have been drived from blog posts, tweets or other public sources that are referenced in the rules.