Deploying a Metasploit Dev build and OWASP JuiceShop in less than 10 seconds ⚡
Deploying the pentest-toolbox and scanning the OWASP JuiceShop container using container subnet. This allows for very fast interactions compared to a classic offensive scenario 🚀
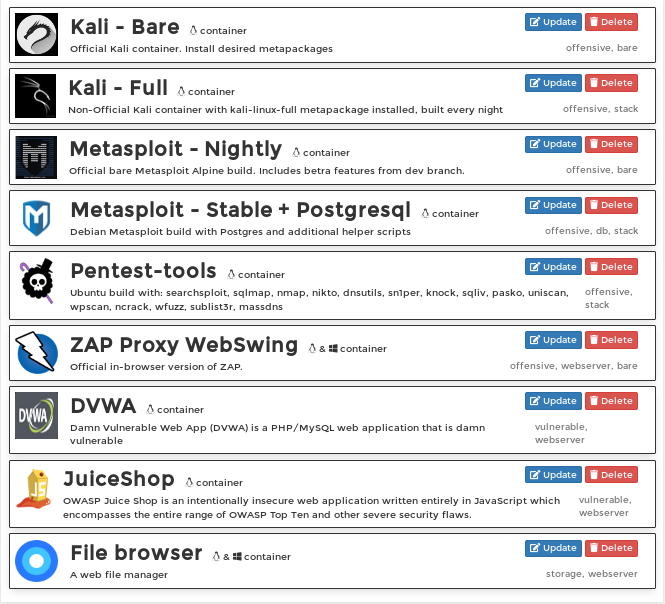
This lab is built using Portainer and custom made App Templates. The following are currently implemented:
| Name | Description | Status |
|---|---|---|
| Kali - Bare | Official Kali container. Install desired metapackages | 🆗 |
| Kali - Full | Non-Official Kali container with kali-linux-full metapackage installed, built every night | 🆗 |
| Metasploit - Nightly | Official bare Metasploit Alpine build. Includes beta features from dev branch | 🆗 |
| Metasploit - Stable + Postsgresql | Debian Metasploit build with Postgres and additional helper scripts | 🆗 |
| Pentest-tools | Ubuntu build with: searchsploit, sqlmap, nmap, nikto, dnsutils, sn1per, knock, sqliv, pasko, uniscan, wpscan, ncrack, wfuzz, sublist3r, massdns | 🆗 |
| ZAP Proxy WebSwing | Official in-browser version of ZAP | 🆗 |
| DVWA | Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is damn vulnerable | 🆗 |
| JuiceShop | OWASP Juice Shop is an intentionally insecure web application written entirely in JavaScript which encompasses the entire range of OWASP Top Ten and other severe security flaws | 🆗 |
| FileBrowser | A web file manager | 🚧 |
This lab uses Portainer to orchestrate the deployment of the various components presented above. To run the Portainer lab you will need git, docker and docker-compose.
Optionally, you can run the Lab using a docker-machine configuration to your favorite cloud provider to make it even easier.
> git clone git@gitlab.com:akka-infosec/ceh-portainer.git
> cd ceh-portainer
> docker-compose up
Once docker-compose has correctly started, direct you web browser to http://127.0.0.1/portainer, replacing the IP with Docker's.
- Set password
- Select the single endpoint presented by the interface
- Head over to
App Templates. From there, choose and deploy what you wish
Refer to the Templates documentation below for the web server ports, or attach your CLI to the target container using docker
> docker attach <container-name>Note this also supresses error messages from the docker-compose engine to stdout
> ^C
> docker-compose down # if from another tty
> docker-compose up -dFirst pull the official Portainer dedicated docker-compose repository
> git clone https://github.com/portainer/portainer-compose.gitModify the docker-compose.yml file to point to the custom App Template.
> cd ceh-portainer
> nano docker-compose.ymlReplace
command: --templates http://templates/templates.json
by
command: --templates https://raw.githubusercontent.com/khast3x/portainer-pentest-lab/master/templates.yml --host=unix:///var/run/docker.sock
In some instances, the watchtower module that is summoned by the docker-compose file can cause some problems. You can safely remove it.
You can check that your modifications did not break the configuration file by using a YAML checking tool.
> cd ceh-portainer
> docker-compose up
# Make sure everything works by viewing the stdout debug output, then stop the stack
> ^C> docker-compose up -dTo remove all portainer local data, docker images, containers, volumes and networks:
> docker system prune ; rm -rf /opt/portainer/Default values such as ports or volumes can be changed by selecting (+) Advanced Settings on the container page before deploying
| Container Name: | kali-bare |
| Source: | Link |
| Ports: | 4444:4444 |
| Image: | kalilinux/kali-linux-docker |
| Usage: | This image comes bare and requires installing your desired kali metapackages. Once deployed, you can access it through the CLI by typing docker attach kali-bare |
| Container Name: | kali-full |
| Source: | Link |
| Ports: | 4445:4444 |
| Image: | booyaabes/kali-linux-full |
| Usage: | Kali image with kali-linux-full metapackage installed, built every night. Once deployed, you can access it through the CLI by typing docker attach kali-full |
| Container Name: | msf-dev |
| Source: | Link |
| Ports: | 4446:4444 |
| Image: | metasploitframework/metasploit-framework |
| Usage: | Official bare Metasploit Alpine build. Includes beta features from the dev branch. Once deployed, you can access it through the CLI by typing docker attach kali-full. From the bash prompt you can start ./msfconsole or ./msfvenom |
| Container Name: | msf-postgresql |
| Source: | Link |
| Ports: | 4447:4444 |
| Image: | phocean/msf |
| Usage: | Non official Metasploit build on Debian. Comes with pre-configured msfdb. Remember to start it inside the container by using service postgresql start. Metasploit will recognize it automatically. Once deployed, you can access it through the CLI by typing docker attach kali-full. From the bash prompt you can start ./msfconsole or ./msfvenom. From the msfconsole, you can check the database status with db_status |
| Container Name: | pentest-tools |
| Source: | Link |
| Ports: | |
| Image: | szalek/pentest-tools |
| Usage: | Ubuntu build with: searchsploit, sqlmap, nmap, nikto, dnsutils, sn1per, knock, sqliv, pasko, uniscan, wpscan, ncrack, wfuzz, sublist3r, massdns. Once deployed, you can access it through the CLI by typing docker attach pentest-tools. All the scripts are already in the shell binary path |
| Container Name: | zap-proxy |
| Source: | Link |
| Ports: | 8081:8080, 8090:8090 |
| Image: | owasp/zap2docker-stable |
| Usage: | Official in-browser version of OWASP ZAP. Once deployed, head over to http://127.0.0.1:8081/?anonym=true&app=ZAP with the appropriate IP address. This is important, otherwise you won't have access to the app |
| Container Name: | vuln-dvwa |
| Source: | Link |
| Ports: | 8082:80 |
| Image: | vulnerables/web-dvwa |
| Usage: | Point your browser to http://127.0.0.1:8082 to access it. To start using: Generate DB from the web interface, Login using admin/password. Select DVWA Security in the left menu, set your difficulty level |
| Container Name: | vuln-juiceshop |
| Source: | Link |
| Ports: | 8084:3000 |
| Image: | bkimminich/juice-shop |
| Usage: | Point your browser to http://127.0.0.1:8084 to access it |
Copyright [2018] [TMC - AKKA]
Licensed under the Apache License, Version 2.0 (the "License"); you may not use this file except in compliance with the License. You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software distributed under the License is distributed on an "AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the License for the specific language governing permissions and limitations under the License.
Icon made by Freepik from www.flaticon.com