Sharing Bug Bounty tips and tricks with the community including but not limited to automation, one liners and useful thoughts
Cyllabus
- Github local recon - usage: gitsecrets “word” | gf pattern
gitsecrets(){
{ find .git/objects/pack/ -name "*.idx"|while read i;do git show-index < "$i"|awk '{print $2}';done;find .git/objects/ -type f|grep -v '/pack/'|awk -F'/' '{print $(NF-1)$NF}'; }|while read o;do git cat-file -p $o;done|grep -E "$1"
}
- ffuf on many files
ffuf -u URL/FUZZ -w allipstoffuf:URL -w ~/.config/wordlists/envpath:FUZZ -maxtime 300 -t 500 -c -v
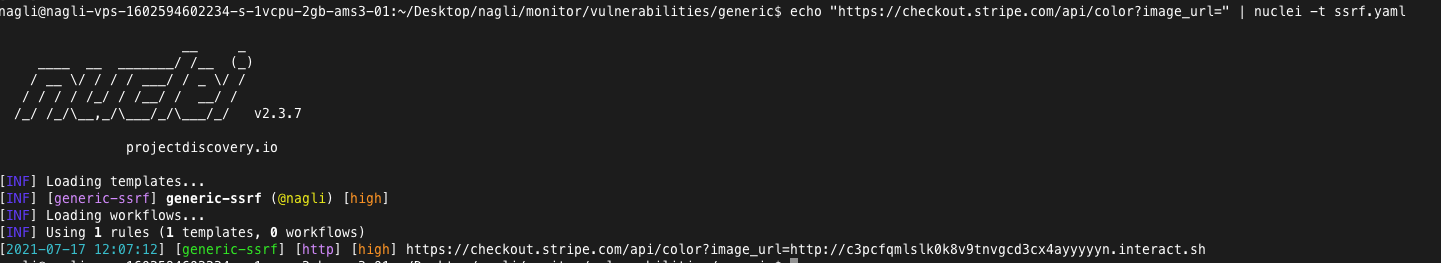
- SSRF nuclei template - Feed endpoints to probe for SSRF interaction automatically, the module tries to fetch simple interaction on the provided input, and later appends common SSRF query params to the original request.
Sample:
echo "https://checkout.stripe.com/api/color?image_url=" | nuclei -t ssrf.yaml
- WAF bypass by changing scheme:
http://web.com/?XSSendpoint ===> no WAF
https://web.com/?XSSendpoint ===> WAF implemented
- Google Dorks:
Root Domains - "org" subsidiaries
intext: credit company
- Amass
1. Get company's ASN numbers - amass intel -org DoD
2. Turn ASN numbers into CIDR - whois -h whois.radb.net -- "-i origin $asn" | grep -Eo "([0-9.]+){4}/[0-9]+" | sort -u >> $recondir/cidr
3. Get TLDS from ASN - amass intel -asn $asn
4. Get TLDS from whois data - amass intel -whois -d TLD (facebook.com)
5. Get TLDS from CIDR - amass intel -cidr xxxxxx/23
- CIDR to hostnames
prips 144.160.32.0/19 | hakrevdns -d | httpx -title -status-code -follow-redirects
- ReDoS on GraphQL API endpoint - Regex BOMB to shutter the server CPU.
Takeaway : FUZZ with certain characters such as \u0000 to try and trigger ReGeX verbose errors
- Ticket Trick - was able to register with noreply@github.com, system created support tickets by emailing to support@company.com, the email verification landed to his account.
Takeaway: If a company won't require email address verification and will automatically generate support tickets, try and sign up with noreply@github.com
- CSRF due to authenticity_token not being validated - The authenticity_token had a fixed value which wasn't validated, leads to being vulnerable to CSRF -> Org takeover on shopify.
Takeaway: whenever authenticity_token is presented on requests validate if the value is being processed in the back-end.
- Application level DOS with crafted payload - "name" parameter on POST request crashed upon supplying (((((()0))))) as input.
Takeaway: try (((((()0))))) when fuzzing post requests.
- IDOR on steam id cookie - Utilizing a POST request with the victim steamid cookie value performed the action as the victims behalf
Takeaway: Swap identifyable cookie values between lateral accounts.
Takeaway: Look through org's public repos for Bitbucket content
- Java RCE via POST request "month" parameter - The month parameter was vulnerable to code injection with the following payload: 1${T(java.lang.System).getenv()}
Takeaway: When Fuzzing java application to try and insert code injection queries like ${T(java.lang.System).getenv()}
- SSO takeover while adding trailing space - Adding trailing space to the organisation name would trim it whenever user tried to authenticate
Takeaway: When supplying org name check what is the behaviour with adding " " (space) on it's name
Takeaway: Tampering with the host header with situations who involve caching, can append port to the host to cause DOS
Takeaway: Go through the "main.slug.js" files and look for API Keys, this one looks like the google maps one (AI....)
Takeaway: Look for websites who has bucket like https://s3.amazonaws.com/BUCKETNAME and try to run aws s3 ls BUCKETNAME
Takeaway: Check each step of reset password phase who might not be protected with rate limiting, this could even be a third step after clicking an email, allowing to skip phase 2.
Takeaway: on Admin / custom made login panels check the source code to determine if there are some leaks including password.
Takeaway: %27||/**/(case%20when(/*%c3*/length/*%c3*/(user)=5)then/**/(1)else(1/0)end)||%27
Takeaway: Change the scope parameter to arbitrary file and see if the redirect_url will redirect to external domain
Some of the one liners or data presented might be taken from other repos and was tampered by me, I only share here stuff I use regulary or encountered in the last year, if you find here anything that was originally crafted by you lemme know and I'll credit you.