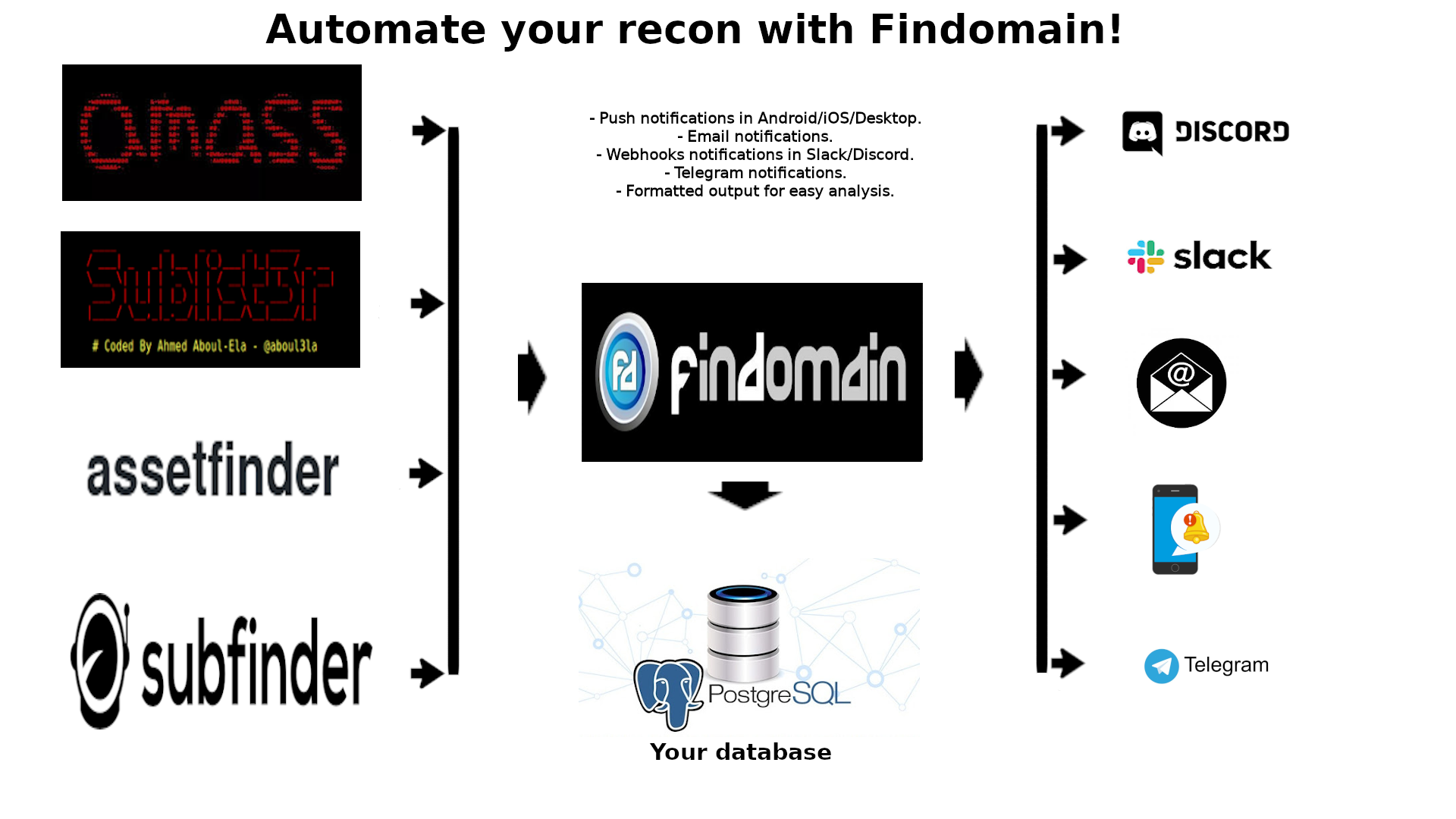
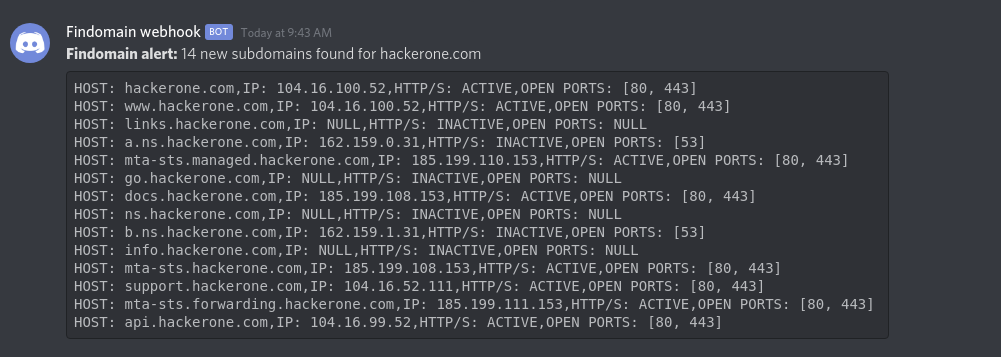
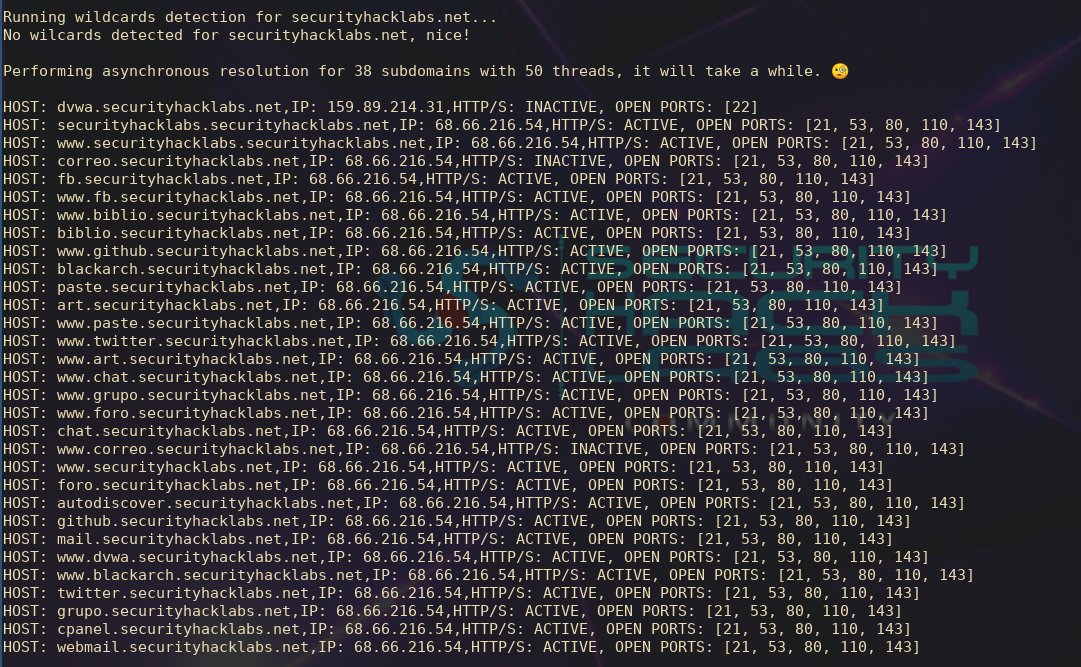
If you don't want to deal with servers and complex configurations for doing recon, Findomain offers a dedicated monitoring service hosted in Amazon, that allow you to monitor your target domains with multiple top tools (OWASP Amass, Sublist3r, Assetfinder and Subfinder) and send alerts to Discord, Slack, Telegram, Email or Push Notifications (Android/iOS/Smart Watch/Desktop) when new subdomains are found. The only you need to do is configure a file with your email address (if applicable) or/and webhooks/Telegram chat information and put your domains in another file, once you have done that you have a full automated subdomains monitoring service that keep you up to date with new subdomains discovered, Host IP, HTTP Status, Screenshots of the HTTP websites, Open Ports, Subdomains CNAME and more. All your data is securely saved in a relational database and you can request a dump of your data whenever you want.
When you finish your paypment, you will receive an email with the server credentials and documentation about how to fill the configuration file and other details.
Learn more about the monitoring server following this link.
Demos:
Screenshots:
The fastest and cross-platform subdomain enumerator.
The next table offers you the comparison about what is in Plus version that is not in free version (current repo).
Implemented features:
| Feature | Plus Version Support | Free Version Support |
|---|---|---|
| Core features | Yes | Yes |
| Check subdomains HTTP/S status | Yes | No |
| Check subdomains open ports | Yes | No |
| Support for posting HOST, IP, HTTP status and open ports to webhook notifications | Yes | No |
| Support for "light monitoring" mode | Yes | No |
| Support for automatic detection/read of default configuration file | Yes | No |
| Save Host, IP, HTTP Status and Open Ports to database | Yes | No |
| Option to exclude sources | Yes | No |
| Filter or exclude subdomains containing specific keywords. | Yes | No |
| Maximum number of threads 1000 | Yes | No |
| Force all targets to be lowercase | Yes | No |
| Port scanner | Yes | No |
| Save root domain to database | Yes | No |
| Custom user agent configuration | Yes | No |
| Rate limit user configuration | Yes | No |
| Output files written in real-time | Yes | No |
| Output to unique file while monitoring | Yes | No |
| Option to save subdomains data to database without setting up monitoring | Yes | No |
| Option to save data in your database if the webhook timeout | Yes | No |
Custom DNS IP addresses for fast subdomains resolving (more than 60 per second by default, up to 200 with --threads 200) Note: if you are going to use Findomain for bruteforce, I highly recommend the Plus version because the free one uses the same DNS resolver for all queries and that leads to requests blocked by DNS provider but also slow results. |
Yes | No |
| Built-in top faster DNS IP addresses | Yes | No |
| Subdomains screenshots of HTTP server support (requires Chrome/Chromium to run in headless mode) | Yes | No |
| Use job names to identify targets (see this tweet) | Yes | No |
| Update the existing data in the database | Yes | No |
| Email notifications. | Yes | No |
| Push notifications through Pushover. | Yes | No |
Planned features:
| Feature | Plus Version Plans | Free Version Plans |
|---|---|---|
| Project Sonar integration | Yes | No |
| Shodan source support | Yes | No |
| Elastic search support | Yes | No |
| SQLite output | Yes | No |
| Track CNAME for subdomains | Yes | No |
It table gives you a idea why you should use findomain and what it can do for you. The domain used for the test was aol.com in the following BlackArch virtual machine:
Host: KVM/QEMU (Standard PC (i440FX + PIIX, 1996) pc-i440fx-3.1)
Kernel: 5.2.6-arch1-1-ARCH
CPU: Intel (Skylake, IBRS) (4) @ 2.904GHz
Memory: 139MiB / 3943MiB
The tool used to calculate the time, is the time command in Linux.
| Enumeration Tool | Search Time | Total Subdomains Found | CPU Usage | RAM Usage |
|---|---|---|---|---|
| Findomain | real 0m5.515s | 84110 | Very Low | Very Low |
Summary: 84110 subdomains in 5.5 seconds.
- Subdomains monitoring: put data to Discord, Slack or Telegram webhooks. See Subdomains Monitoring for more information.
- Multi-thread support for API querying, it makes that the maximun time that Findomain will take to search subdomains for any target is 15 seconds (in case of API's timeout).
- Parallel support for subdomains resolution, in good network conditions can resolv about 3.5k of subdomains per minute.
- DNS over TLS support.
- Specific IPv4 or IPv6 query support.
- Discover subdomains without brute-force, it tool uses Certificate Transparency Logs and APIs.
- Discover only resolved subdomains.
- Discover subdomains IP for data analisis.
- Read target from user argument (-t) or file (-f).
- Write to one unique output file specified by the user all or only resolved subdomains.
- Write results to automatically named TXT output file(s).
- Hability to query directly the Findomain database created with Subdomains Monitoring for previous discovered subdomains.
- Hability to import and work data discovered by other tools.
- Quiet mode to run it silently.
- Cross platform support: Any platform, it's written in Rust and Rust is multiplatform. See the documentation for instructions.
- Multiple API support.
- Possibility to use as subdomain resolver.
- Subdomain wildcard detection for accurate results.
- Support for subdomain discover using bruteforce method.
- Support for configuration file in TOML, JSON, HJSON, INI or YAML format.
See Subdomains Enumeration: what is, how to do it, monitoring automation using webhooks and centralizing your findings for a detailed guide including real world examples of how you get the most out of the tool.
It tool doesn't use the common methods for sub(domains) discover, the tool uses Certificate Transparency logs and specific well tested APIs to find subdomains. It method make it tool the most faster and reliable. The tool make use of multiple public available APIs to perform the search. If you want to know more about Certificate Transparency logs, read https://www.certificate-transparency.org/
APIs that we are using at the moment:
- Certspotter
- Crt.sh Database (favorite) or Crt.sh HTTP API
- Virustotal
- Sublist3r
- Facebook
** - Spyse (CertDB)
* - Bufferover
- Threatcrowd
- Virustotal with apikey
** - AnubisDB
- Urlscan.io
- SecurityTrails
** - Threatminer
Notes
APIs marked with **, require an access token to work. Search in the Findomain documentation how to configure and use it.
APIs marked with * can optionally be used with an access token, create one if you start experiencing problems with that APIs. Search in the Findomain documentation how to configure and use it.
More APIs?
If you know other APIs that should be added, comment here.
In order to make sure Findomain will not be broken on some commit I have created the develop branch where new features and improvements are pushed before they go to master branch. In resume the difference is: develop branch and beta releases aren't ready for production purposes but testing or development purposes and master branch and non-beta releases are ready for production purposes. If you are a developer or want to be a beta tester of the new features that are added to Findomain then use the develop branch, otherwise always use the master branch. Every new feature is tested before it goes to master by the Findomain beta testers that are only (@sumgr0) at the moment, I will appreciate if you join to the testing process, just send me a DM in Twitter (@edu4rdshl).
If you are a packager of Findomain for X system distribution always go for the master branch if using git or non-beta releases if using releases model.
Build the development version:
You need to have rust, make and perl installed in your system first.
$ git clone https://github.com/Edu4rdSHL/findomain.git -b develop # Only the develop branch is needed
$ cd findomain
$ cargo build --release
$ ./target/release/findomainTo update the repository when new commits are added, just go to the folder where Findomain's develop branch was cloned and excute:
$ git pull
$ cargo build --release
$ ./target/release/findomain
We offer binarys ready to use for the following platforms (all are for 64 bits only):
If you need to run Findomain in another platform, continue reading the documentation.
If you want to build the tool for your 32 bits system or another platform, follow it steps:
Note: You need to have rust, make and perl installed in your system first.
Using the crate:
cargo install findomain- Execute the tool from
$HOME/.cargo/bin. See the cargo-install documentation.
Using the Github source code:
- Clone the repository or download the release source code.
- Extract the release source code (only needed if you downloaded the compressed file).
- Go to the folder where the source code is.
- Execute
cargo build --release - Now your binary is in
target/release/findomainand you can use it.
Install the Termux package, open it and follow it commands:
$ pkg install rust make perl
$ cargo install findomain
$ cd $HOME/.cargo/bin
$ ./findomain
If you want to install it, you can do that manually compiling the source or using the precompiled binary.
Manually: You need to have rust, make and perl installed in your system first.
$ git clone https://github.com/Edu4rdSHL/findomain.git
$ cd findomain
$ cargo build --release
$ sudo cp target/release/findomain /usr/bin/
$ findomain$ wget https://github.com/Edu4rdSHL/findomain/releases/latest/download/findomain-linux
$ chmod +x findomain-linux
$ ./findomain-linux
If you are using the ArchLinux distribution or any ArchLinux-based distro, you just need to use:
$ pacman -S findomain
If you are using the Pentoo distribution, you just need to use:
$ emerge -a findomain
$ wget https://github.com/Edu4rdSHL/findomain/releases/latest/download/findomain-aarch64
$ chmod +x findomain-aarch64
$ ./findomain-aarch64
Download the binary from https://github.com/Edu4rdSHL/findomain/releases/latest/download/findomain-windows.exe
Open a CMD shell and go to the dir where findomain-windows.exe was downloaded.
Exec: findomain-windows in the CMD shell.
You have two options to install Findomain in MacOS.
Using Homebrew:
$ brew install findomain
$ findomain
Manually from the repo:
$ wget https://github.com/Edu4rdSHL/findomain/releases/latest/download/findomain-osx
$ chmod +x findomain-osx.dms
$ ./findomain-osx.dms
$ nix-env -i findomain
$ findomain
You have two options to install Findomain in a docker container.
Using Dockerhub:
$ docker pull edu4rdshl/findomain:latest
$ docker run -it edu4rdshl/findomain:latest /bin/bash
$ findomain
Building the docker image:
Please see the documentation.
To update Findomain to latest version, you can be in some scenarios:
- You downloaded a precompiled binary: If you are using a precompiled binary, then you need to download the new binary.
- You are using it in ArchLinux or any Arch-based distro: Just run
pacman -Syu - You have cloned the repo and compiled it from source: You just need to go to the folder where the repo is cloned and run:
git pull && cargo build --release, when finish, you have your executable intarget/release/findomain. - You downloaded a source code release and compiled it: You need to download the new source code release and compile it again.
- I used cargo install findomain: then just run
cargo install findomain.
In in section you can found the steps about how to configure APIs that need or can be used with access tokens.
History
When I added the Facebook CT API in the beginning I was providing a Webhook token to search in the API, as consequence when a lot of users were using the same token the limit was reached and user can't search in the Facebook API anymore until Facebook unlocked it again. Since Findomain version 0.2.2, users can set their own Facebook Access Token for the webook and pass it to findomain setting the findomain_fb_token system variable. The change was introduced here. Also since 23/08/2019 I have removed the webhook that was providing that API token and it will not work anymore, if you're using findomain < 0.2.2 you are affected, please use a version >= 0.2.2.
Since Findomain 0.2.4 you don't need to explicity set the findomain_fb_token variable in your system, if you don't set that variable then Findomain will use one of our provided access tokens for the Facebook CT API, otherwise, if you set the environment variable then Findomain will use your token. See it commit. Please, if you can create your own token, do it. The usage limit of access tokens is reached when a lot of people use it and then the tool will fail.
Getting the Webhook token
The first step is get your Facebook application token. You need to create a Webhook, follow the next steps:
- Open https://developers.facebook.com/apps/
- Clic in "Create App", put the name that you want and send the information.
- In the next screen, select "Configure" in the Webhooks option.
- Go to "Configuration" -> "Basic" and clic on "Show" in the "App secret key" option.
- Now open in your browser the following URL: https://graph.facebook.com/oauth/access_token?client_id=your-app-id&client_secret=your-secret-key&grant_type=client_credentials
Note: replace your-app-id by the number of your webhook identifier and your-secret-key for the key that you got in the 4th step.
- You should have a JSON like:
{
"access_token": "xxxxxxxxxx|yyyyyyyyyyyyyyyyyyyyyyy",
"token_type": "bearer"
}- Save the
access_tokenvalue.
Now you can use that value to set the access token as following:
Unix based systems (Linux, BSD, MacOS, Android with Termux, etc):
Put in your terminal:
$ findomain_fb_token="YourAccessToken" findomain -(options)
Windows systems:
Put in the CMD command prompt:
> set findomain_fb_token=YourAccessToken && findomain -(options)
Note: In Windows you need to scape special characters like |, add ^ before the special character to scape it and don't quote the token. Example: set findomain_fb_token=xxxxxxx^|yyyyyyyy && findomain -(options)
Tip: If you don't want to write the access token everytime that you run findomain, export the findomain_fb_token in Unix based systems like putting export findomain_fb_token="YourAccessToken" into your .bashrc and set the findomain_fb_token variable in your Windows system as described here.
- Open https://account.spyse.com/register and make the registration process (include email verification).
- Log in into your spyse account and go to https://account.spyse.com/user
- Search for the "API token" section and clic in "Show".
- Save that access token.
Now you can use that value to set the access token as following:
Unix based systems (Linux, BSD, MacOS, Android with Termux, etc):
Put in your terminal:
$ findomain_spyse_token="YourAccessToken" findomain -(options)
Windows systems:
Put in the CMD command prompt:
> set findomain_spyse_token=YourAccessToken && findomain -(options)
Note: In Windows you need to scape special characters like |, add ^ before the special character to scape it and don't quote the token. Example: set findomain_spyse_token=xxxxxxx^|yyyyyyyy && findomain -(options)
Tip: If you don't want to write the access token everytime that you run findomain, export the findomain_spyse_token in Unix based systems like putting export findomain_spyse_token="YourAccessToken" into your .bashrc and set the findomain_spyse_token variable in your Windows system as described here.
- Open https://www.virustotal.com/gui/join-us and make the registration process (include email verification).
- Log in into your spyse account and go to https://www.virustotal.com/gui/user/YourUsername/apikey
- Search for the "API key" section.
- Save that API key.
Now you can use that value to set the access token as following:
Unix based systems (Linux, BSD, MacOS, Android with Termux, etc):
Put in your terminal:
$ findomain_virustotal_token="YourAccessToken" findomain -(options)
Windows systems:
Put in the CMD command prompt:
> set findomain_virustotal_token=YourAccessToken && findomain -(options)
Note: In Windows you need to scape special characters like |, add ^ before the special character to scape it and don't quote the token. Example: set findomain_virustotal_token=xxxxxxx^|yyyyyyyy && findomain -(options)
Tip: If you don't want to write the access token everytime that you run findomain, export the respective system variable in your OS. For Unix based systems it can be done putting export findomain_virustotal_token=YourAccessToken into your .bashrc. For Windows system it can be done as described here or here.
Getting the API key
The first step is get your SecurityTrails token.Follow the next steps:
- Open https://securitytrails.com/
- Clic in "SIGNUP FOR FREE" (right corner).
- Fill the requested fields, you need to put a valid email address, it's needed for verification..
- Select the API Pricing plan of your preference, there's a free plan limited to 50 queries per month. Clic in "Get started".
- Confirm email address.
- Select "Credentials" in the left panel, there's the API Key.
Now you can use that value to set the access token as following:
Unix based systems (Linux, BSD, MacOS, Android with Termux, etc):
Put in your terminal:
$ findomain_securitytrails_token="YourAccessToken" findomain -(options)
Windows systems:
Put in the CMD command prompt:
> set findomain_securitytrails_token=YourAccessToken && findomain -(options)
Note: In Windows you need to scape special characters like |, add ^ before the special character to scape it and don't quote the token. Example: set findomain_securitytrails_token=xxxxxxx^|yyyyyyyy && findomain -(options)
Tip: If you don't want to write the access token everytime that you run findomain, export the findomain_fb_token in Unix based systems like putting export findomain_securitytrails_token="YourAccessToken" into your .bashrc and set the findomain_fb_token variable in your Windows system as described here.
Findomain is capable of monitor a specific domain or a list of domains for new subdomains and send the data to Slack, Discord or Telegram webhooks. All what you need is a server or your computer with PostgreSQL database server installed. Have in mind that you can have only a central server/computer with PostgreSQL installed and connect to it from anywhere to perform the monitoring tasks.
IMPORTANT NOTE: Findomain is a subdomains enumeration and monitor tool, not a job scheduler. If you want to run findomain automatically then you need to configure a job scheduler like systemd-timers or the well known CRON in *NIX systems, Termux in Android or MAC and the Windows Task Scheduler in Windows.
Here's an article that covers the process of monitoring your domains with scheduled CRON jobs for *NIX systems - Automated subdomain scanning with findomain, PostgreSQL and Webhooks
Options
You can set the following command line options when using the subdomains monitoring feature:
--postgres-database <postgres-database> Postgresql database.
--postgres-host <postgres-host> Postgresql host.
--postgres-password <postgres-password> Postgresql password.
--postgres-port <postgres-port> Postgresql port.
--postgres-user <postgres-user> Postgresql username.
System variables that can be configured
Findomain reads system variables to make use of webhooks. Currently Findomain support the following webhooks (click on them to see how to setup the webhooks):
The available system variables that you have are:
findomain_discord_webhook: Discord webhook URL.
findomain_slack_webhook: Slack webhook URL.
findomain_telegrambot_token: Telegram bot autentication token.
findomain_telegrambot_chat_id: Unique identifier for the target chat or username of the target channel.
Tip: If you don't want to write the webhook parameters everytime that you run findomain, export the respective system variable in your OS. For Unix based systems it can be done putting export VariableName="VariableValue" into your .bashrc. For Windows system it can be done as described here or here.
Default values while connecting to database server
Findomain have some default values that are used when they are not set. They are listed below:
- If you only specify the
-mflag without more arguments or don't specify one of the options Findomain sets:
- Database host: localhost
- Database username: postgres
- Database password: postgres
- Database port: 5432
- Database: Default PostgreSQL database cluster
Subdomains monitoring examples
- Connect to local computer and local PostgreSQL server with specific username, password and database and push the data to both Discord and Slack webhooks
$ findomain_discord_webhook='https://discordapp.com/api/webhooks/XXXXXXXXXXXXXXX' findomain_slack_webhook='https://hooks.slack.com/services/T00000000/B00000000/XXXXXXXXXXXXXXXXXXXXXXXX' findomain -m -t example.com --postgres-database findomain --postgres-user findomain --postgres-host localhost --postgres-port 5432
- Connect to remote computer/server and remote PostgreSQL server with specific username, password and database and push the data to both Discord and Slack webhooks
$ findomain_discord_webhook='https://discordapp.com/api/webhooks/XXXXXXXXXXXXXXX' findomain_slack_webhook='https://hooks.slack.com/services/T00000000/B00000000/XXXXXXXXXXXXXXXXXXXXXXXX' findomain -m -t example.com --postgres-user postgres --postgres-password psql --postgres-host 192.168.122.130 --postgres-port 5432
- Connect to remote computer/server and remote PostgreSQL server with specific username, password and database and push the data to Telegram webhook
$ findomain_telegrambot_token="Your_Bot_Token_Here" findomain_telegrambot_chat_id="Your_Chat_ID_Here" findomain -m -t example.com --postgres-user postgres --postgres-password psql --postgres-host 192.168.122.130 --postgres-port 5432
- Connect to local computer using the default values
$ findomain_discord_webhook='https://discordapp.com/api/webhooks/XXXXXXXXXXXXXXX' findomain_slack_webhook='https://hooks.slack.com/services/T00000000/B00000000/XXXXXXXXXXXXXXXXXXXXXXXX' findomain -m -t example.com
See findomain -h/--help to see all the options.
For subdomains monitoring examples Subdomains Monitoring for more information.
You can use the tool in two ways, only discovering the domain name or discovering the domain + the IP address.
- Make a search of subdomains and print the info in the screen:
findomain -t example.com
- Make a search of subdomains and export the data to a output file (the output file name in it case is example.com.txt):
findomain -t example.com -o
- Make a search of subdomains and export the data to a custom output file name:
findomain -t example.com -u example.txt
- Make a search of only resolvable subdomains:
findomain -t example.com -r
- Make a search of only resolvable subdomains, exporting the data to a custom output file.
findomain -t example.com -r -u example.txt
- Search subdomains from a list of domains passed using a file (you need to put a domain in every line into the file):
findomain -f file_with_domains.txt
- Search subdomains from a list of domains passed using a file (you need to put a domain in every line into the file) and save all the resolved domains into a custom file name:
findomain -f file_with_domains.txt -r -u multiple_domains.txt
- Query the Findomain database created with Subdomains Monitoring.
findomain -t example.com --query-database
- Query the Findomain database created with Subdomains Monitoring and save results to a custom filename.
findomain -t example.com --query-database -u subdomains.txt
- Import subdomains from several files and work with they in the Subdomains Monitoring process:
findomain --import-subdomains file1.txt file2.txt file3.txt -m -t example.com
If you have a problem or a feature request, open an issue.
This project exists thanks to all the people who contribute. See the contributors list.