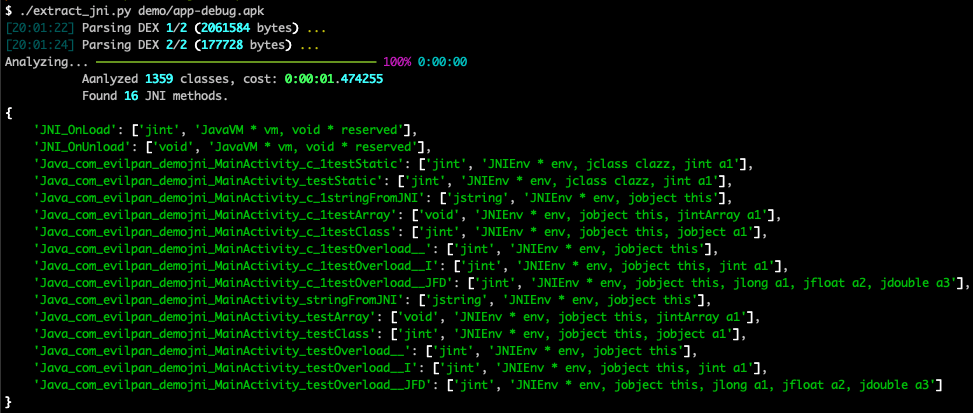
Find JNI function signatures in APK and apply to reverse tools.
- Use extract_jni.py to generate signature.json
- Load signature.json into Ghidra/IDA/Radare2
Install dependences:
pip3 install -r requirements.txt
Usage:
$ ./extract_jni.py -h
usage: extract_jni.py [-h] [-j WORKERS] [-o OUTFILE] apk
positional arguments:
apk /path/to/apk
optional arguments:
-h, --help show this help message and exit
-j WORKERS parse apk with multiple workers(processes) (default: 8)
-o OUTFILE save JNI methods as formatted json file (default: stdout)See Ghidra.
| Before | After |
|---|---|
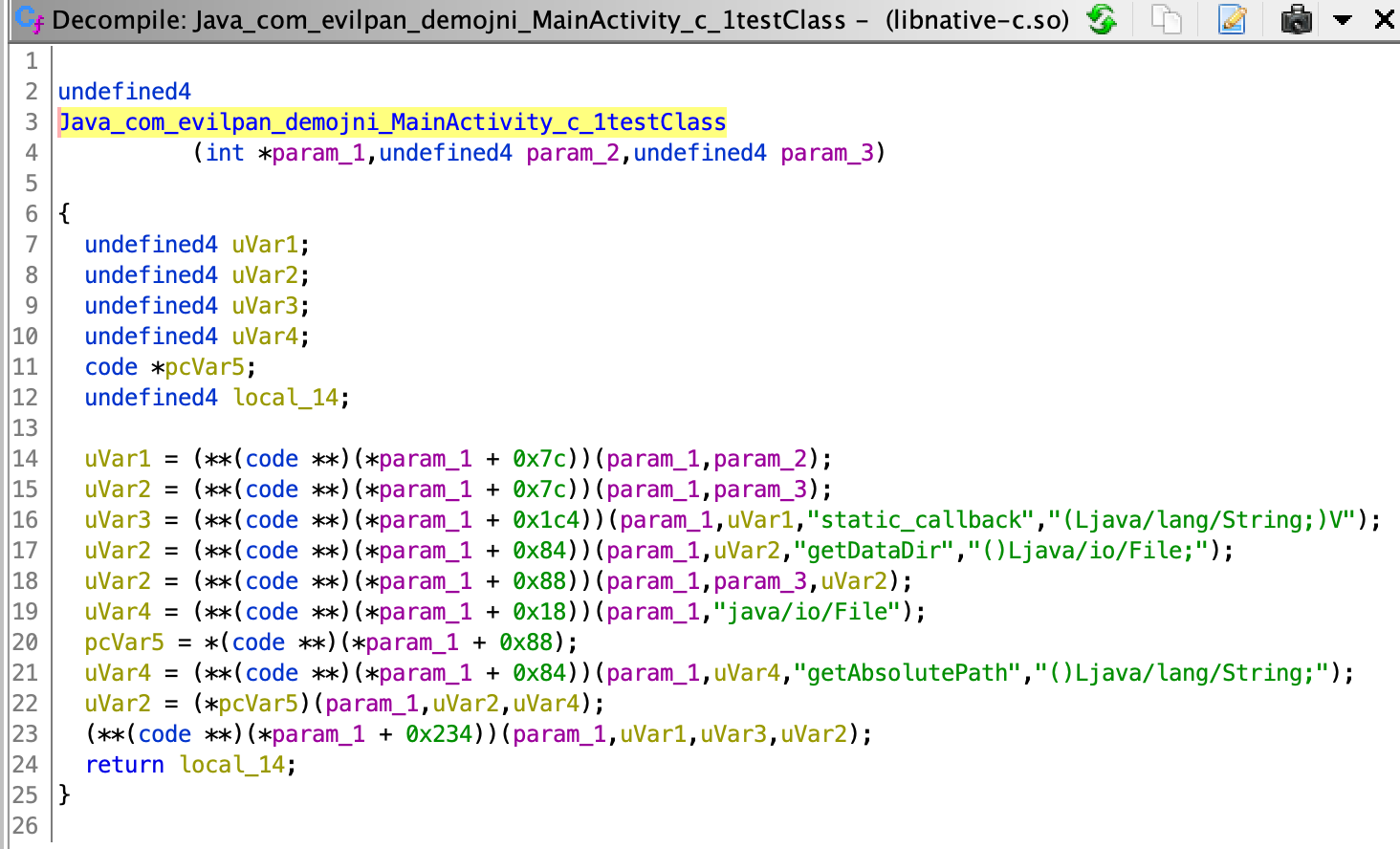 |
 |
See IDA.
| Before | After |
|---|---|
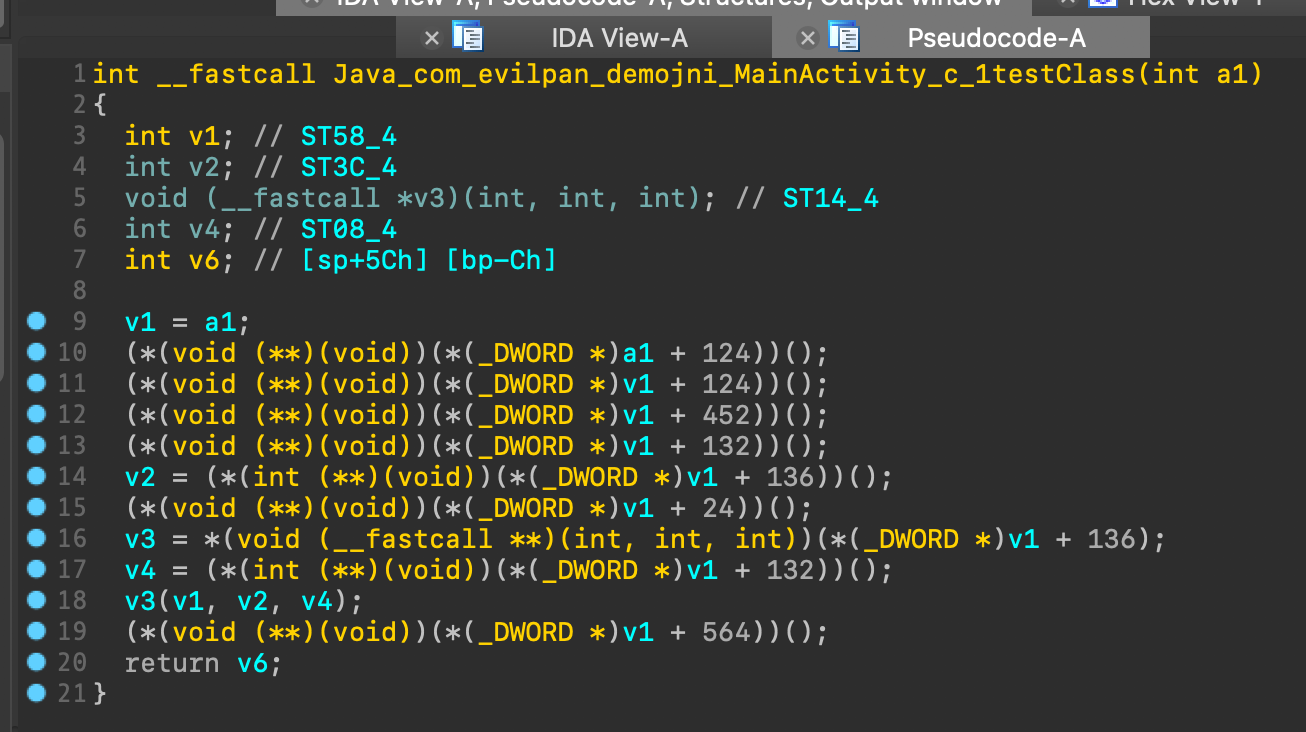 |
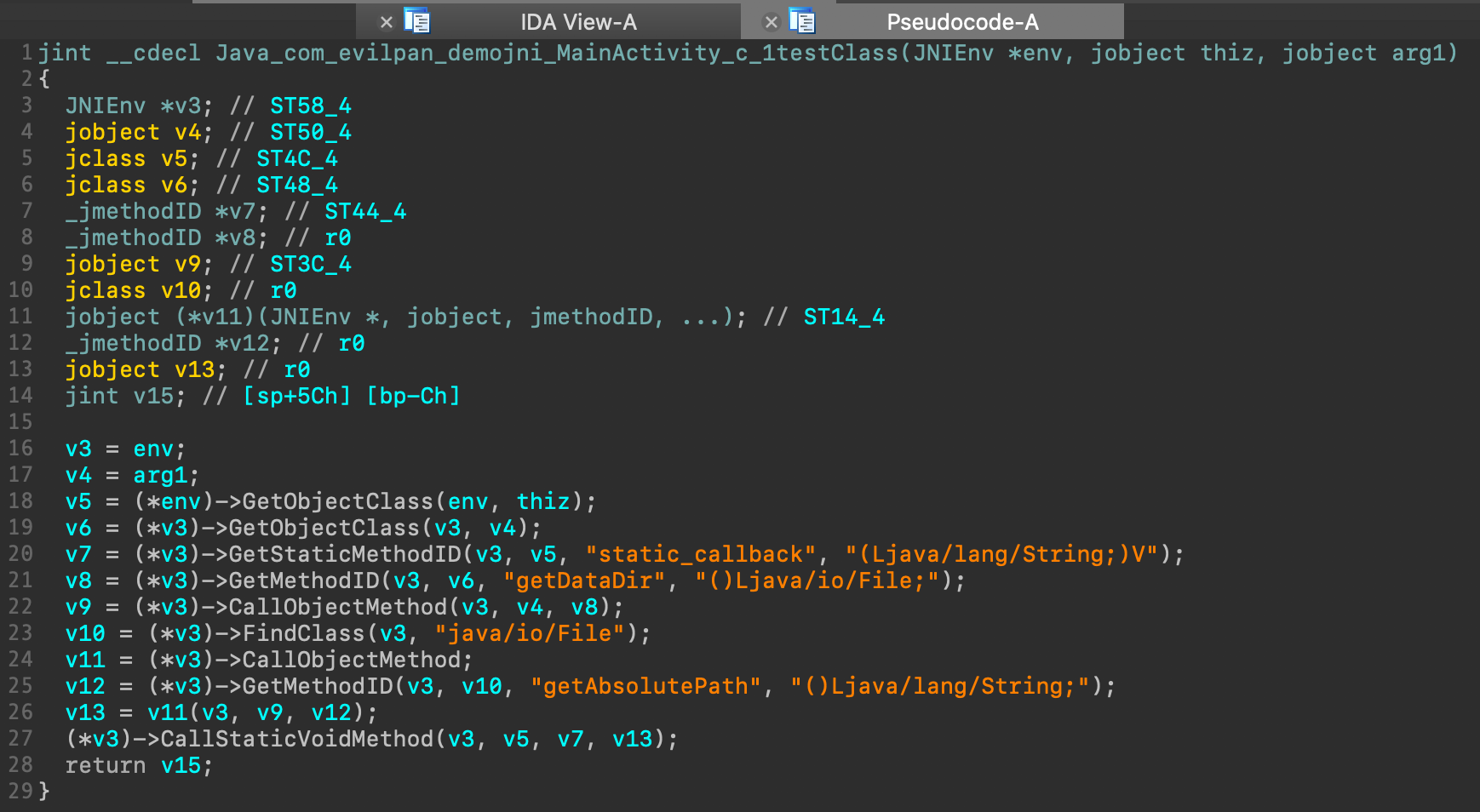 |
WIP, see Radare2
Tested with demo APK: app-debug.apk
- support both C/C++ JNI functions
- support overloaded JNI functions
- remove Jadx dependence, all in Python
- support env->RegisterNatives JNI functions